Ip Expo DevSecOps
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation by Anant Shrivastava at IPExpo Manchester 2019 delivers a focused 26-slide overview of DevSecOps — automating security within DevOps pipelines. Covering the what, why, and how of DevSecOps, the talk walks through the business case for shifting security left, the specific security controls that should be integrated at each pipeline stage, tool selection criteria, cloud security considerations, the cultural changes required for success, the Security Champions model, and real-world case studies illustrating both prevention strategies and the consequences of neglected security. The presentation frames DevSecOps through the lens of three security enablers: People, Process, and Technology.
Key Topics Covered
-
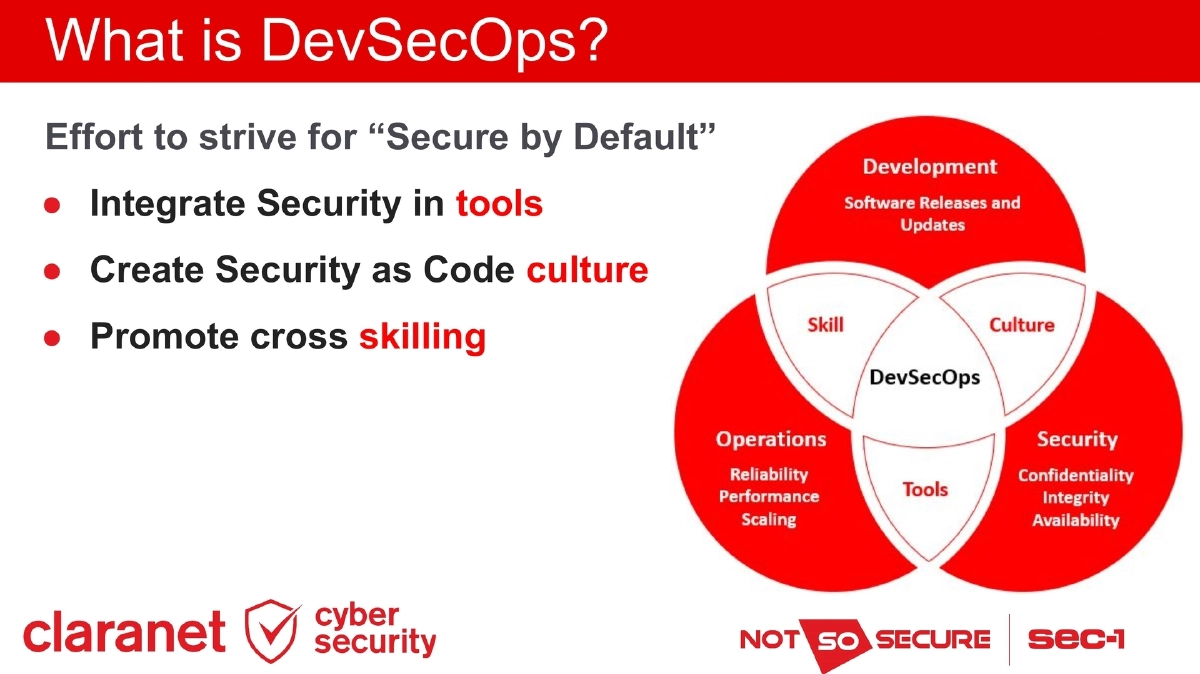
What is DevSecOps: An effort to achieve “Secure by Default” outcomes by integrating security into tools, creating a Security as Code culture, and promoting cross-skilling across development, operations, and security teams.
-
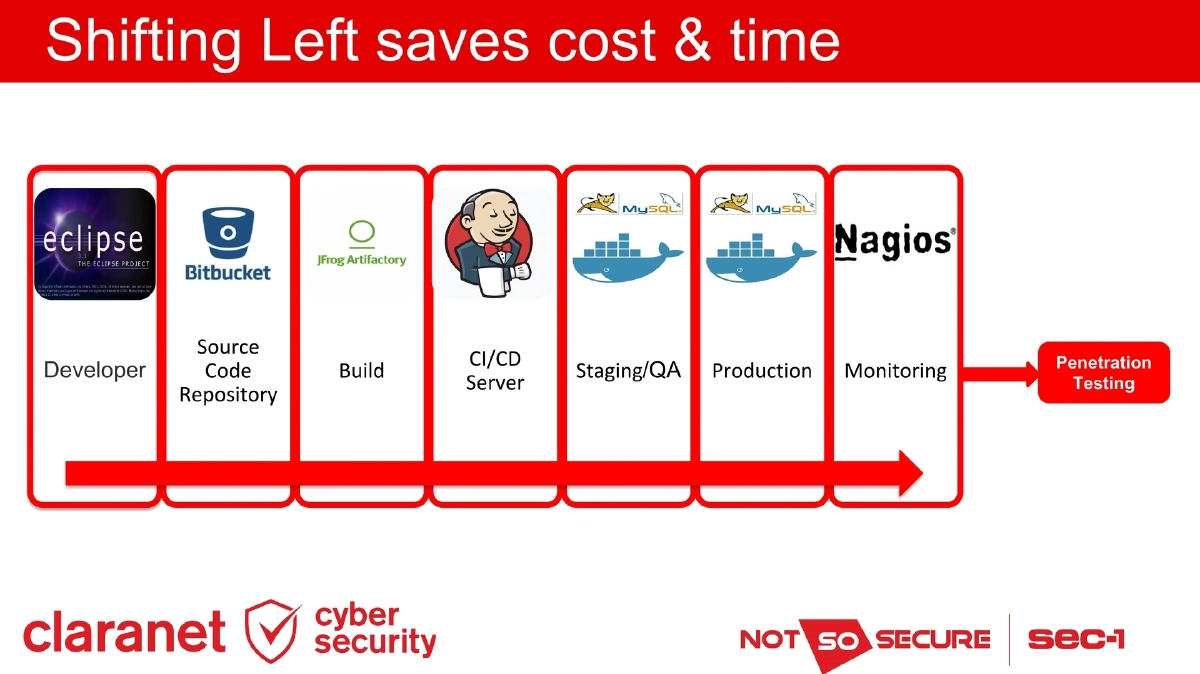
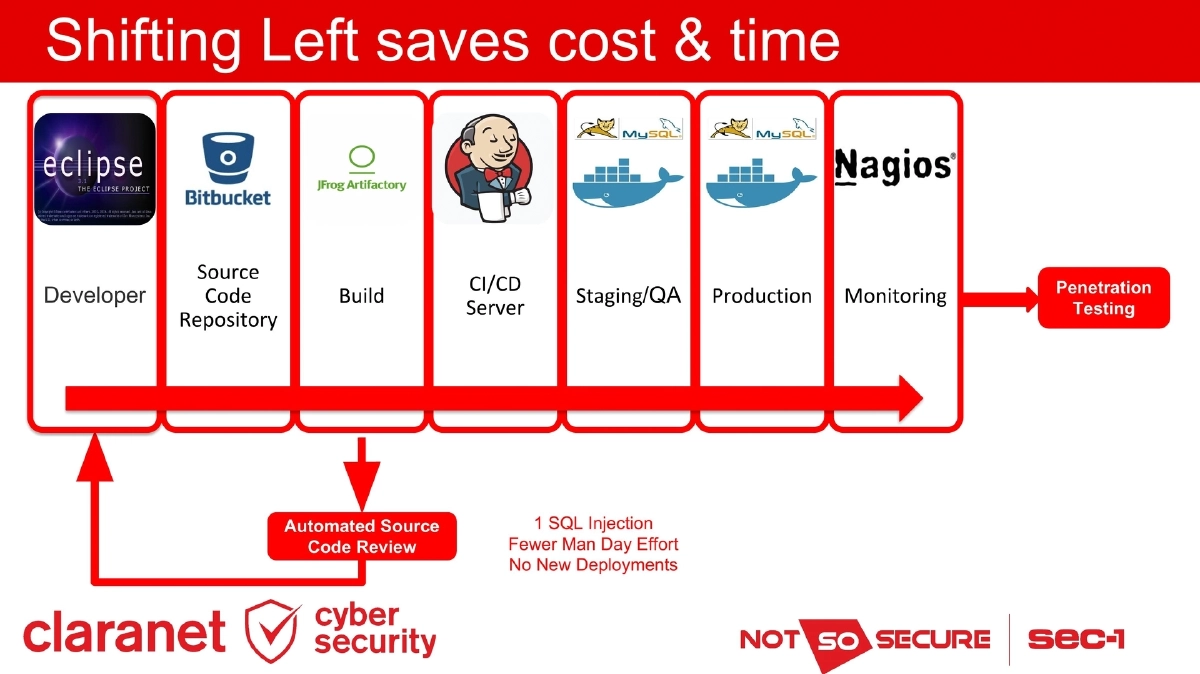
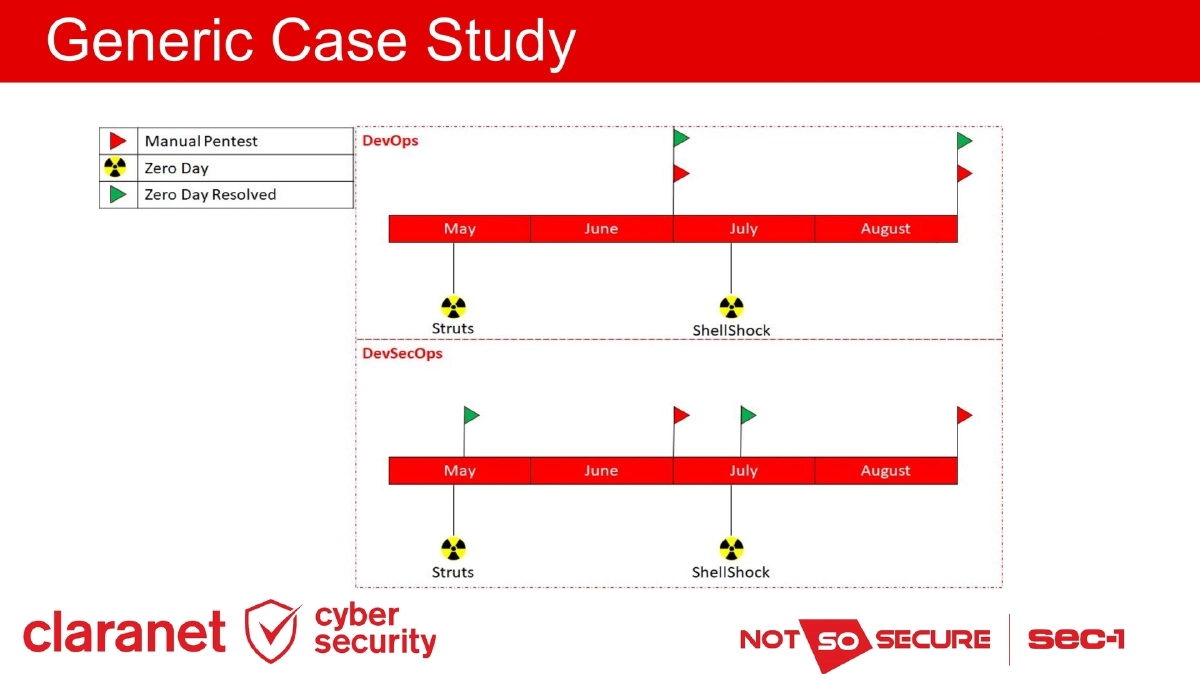
Why DevSecOps: DevOps moves at a rapid pace that traditional security cannot match. Security embedded as part of the process is the only way to ensure safety. The “shift left” principle demonstrates that catching a vulnerability (e.g., SQL injection) at the developer/source code stage requires fewer man-days of effort, eliminates new deployments, and enables automated remediation.
-
How DevSecOps Works: DevSecOps is the combination of automation and cultural changes — integrating security tools into the DevOps pipeline while enabling cultural shifts to embrace security as a shared responsibility.
-
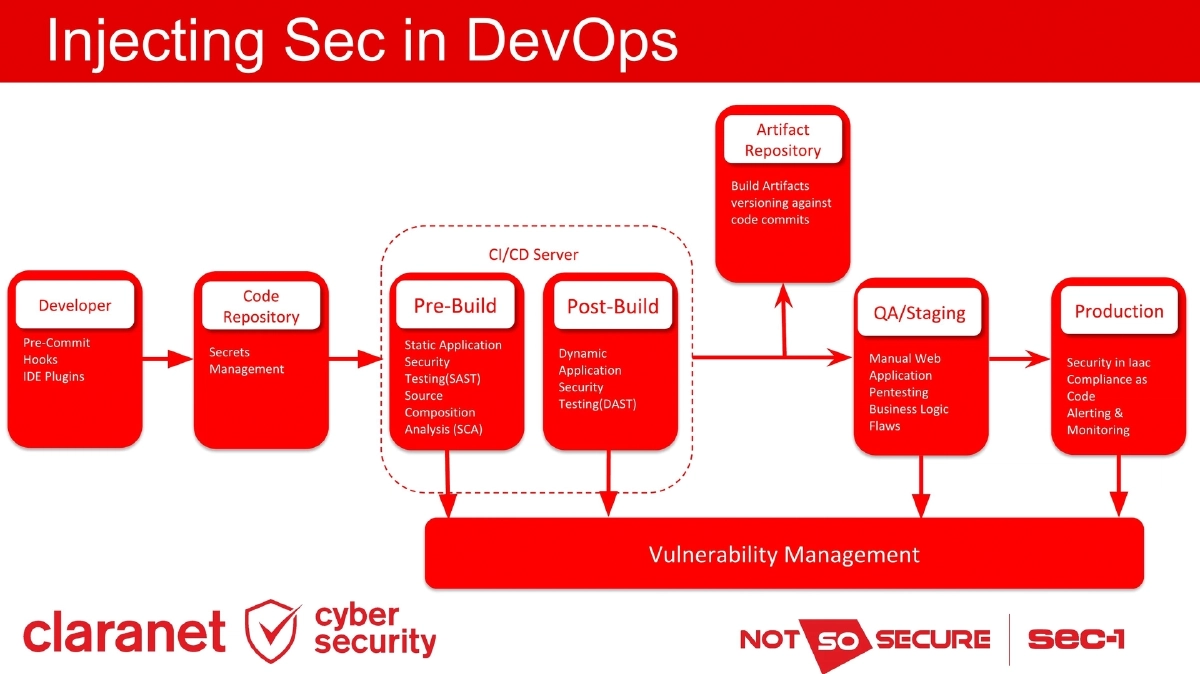
Security Integration Across the Pipeline:
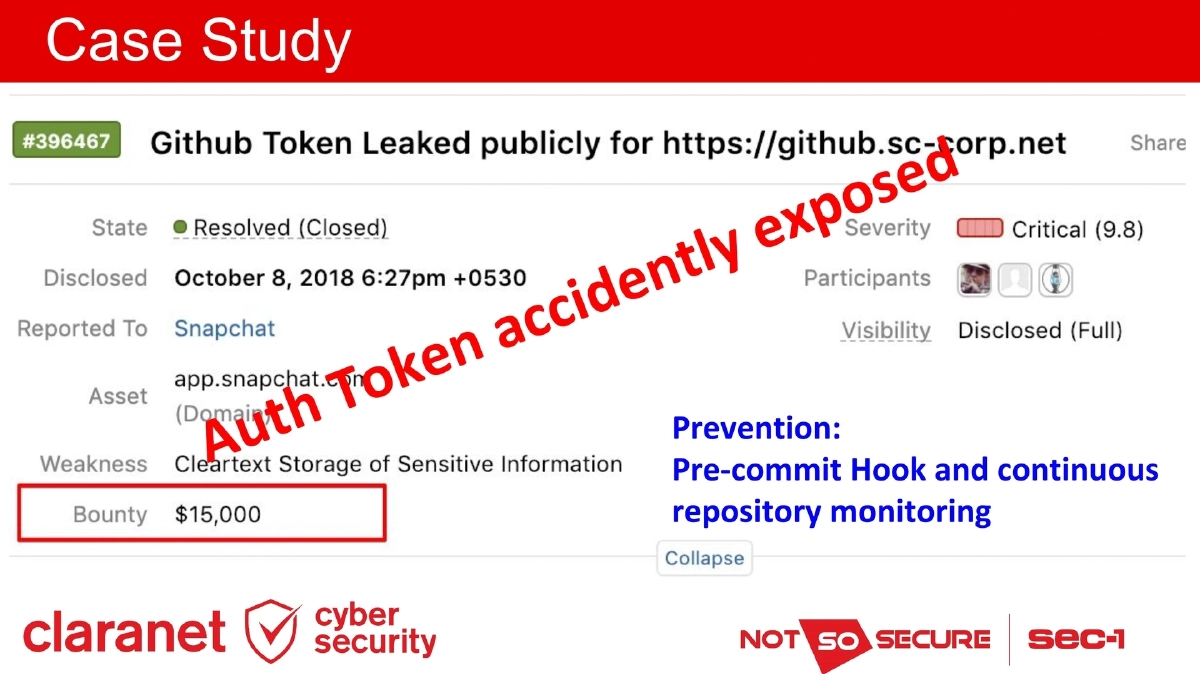
- Pre-Commit Hooks and IDE Plugins: Catching secrets and basic security issues before code enters the repository
- Secrets Management: Tokenizing credentials to prevent accidental exposure
- SAST (Static Application Security Testing): Automated white-box code analysis during CI/CD builds
- SCA (Software Composition Analysis): Identifying vulnerable third-party libraries and dependencies
- DAST (Dynamic Application Security Testing): Black/grey-box testing against deployed applications
- Manual Pentesting: Business logic flaw detection in QA/Staging
- Infrastructure as Code Security: Auditing IaC configurations
- Compliance as Code: Version-controlled compliance rules
- Alerting and Monitoring: Production security monitoring
- Vulnerability Management: Centralized tracking and remediation
-
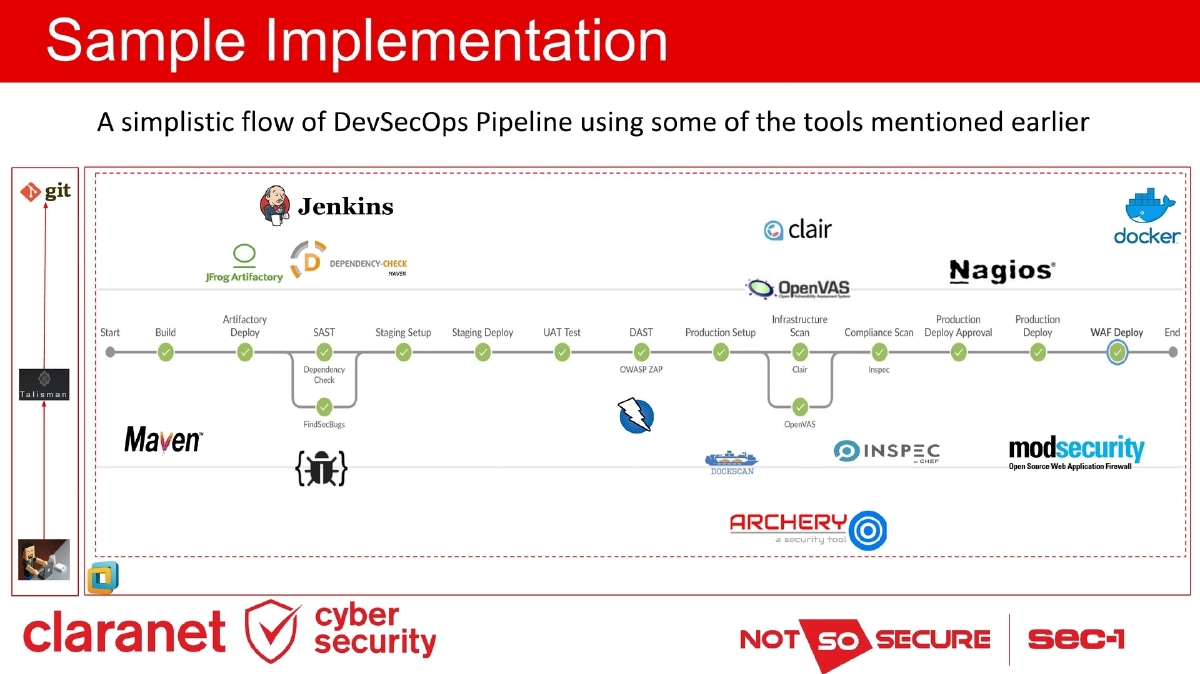
Tool Selection Criteria: Tools suitable for the pipeline must have API/command-line access, complete execution within 15 minutes maximum, be containerizable/scriptable, have minimal licensing limitations, produce machine-readable output (JSON/XML rather than stdout), and be configurable to manage false positives and false negatives.
-
Cloud Security Considerations: The threat landscape shifts in cloud environments. New focus areas include Identity and Access Management, billing attacks, security groups, permissions to resources, rogue/shadow admins, and forgotten resources that lead to compromises or unexpected costs. Infrastructure as Code enables quick auditing and linting of cloud configurations.
-
Cultural Aspect: Automation alone is insufficient. Organizations must foster collaboration and an inclusive culture, encourage a security mindset especially outside the dedicated security team, build allies in the form of security champions, and avoid the blame game.
-
Security Champions Program: A single champion per team serves as the bridge between Dev, Sec, and Ops. Organizations should provide equal cross-skilling opportunities, incentivize collaboration through internal bug bounties, sponsor team interactions and social events, and fund cross-skilling training for non-security teams.
-
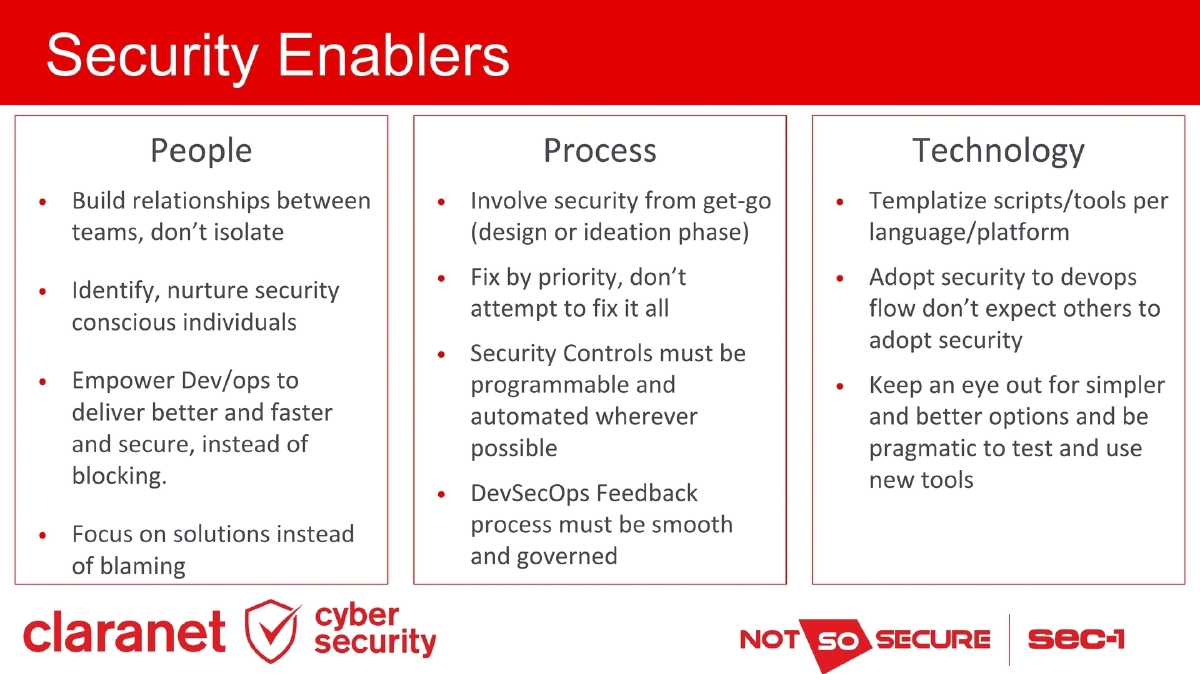
Security Enablers Framework:
- People: Build relationships between teams rather than isolating; identify and nurture security-conscious individuals; empower Dev/Ops to deliver securely; focus on solutions over blame
- Process: Involve security from the design/ideation phase; fix by priority rather than attempting everything; make security controls programmable and automated; ensure smooth DevSecOps feedback governance
- Technology: Templatize scripts and tools per language/platform; adapt security to the DevOps flow; stay pragmatic about testing and adopting new tools
-
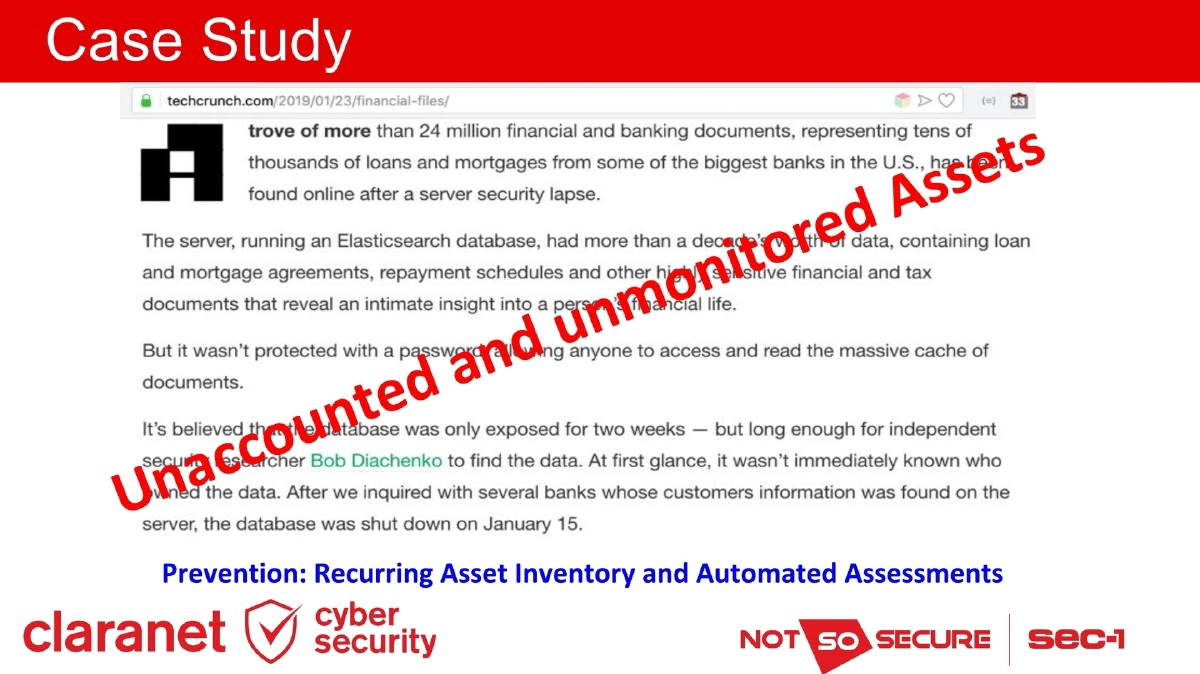
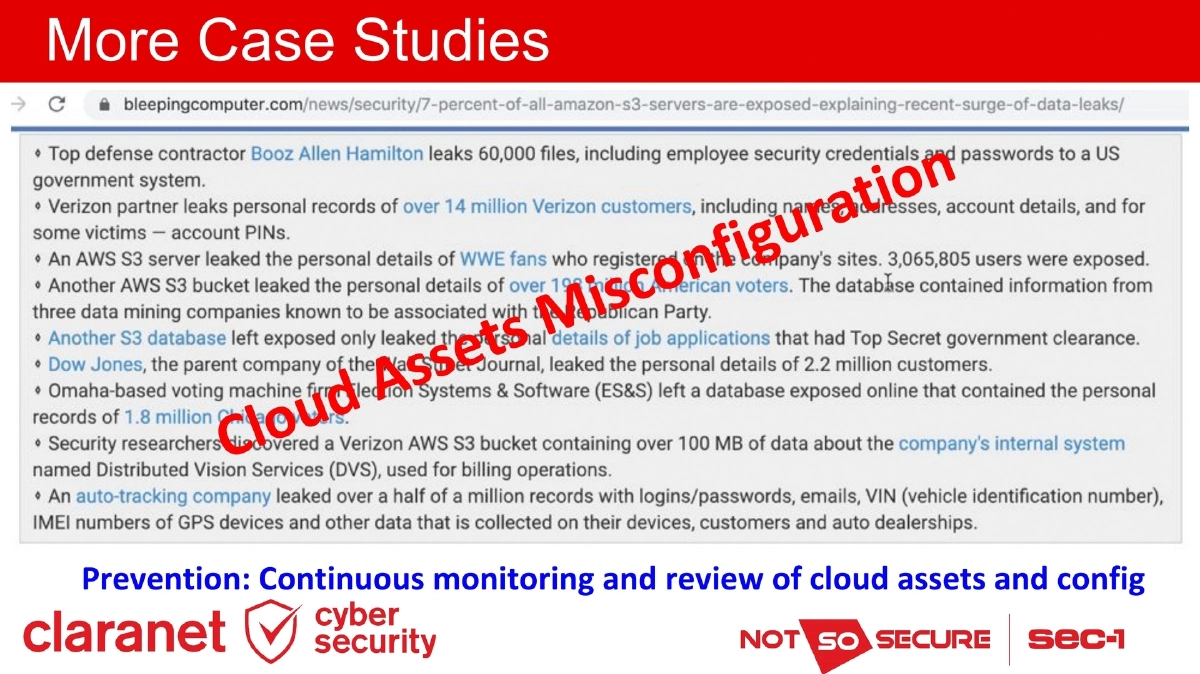
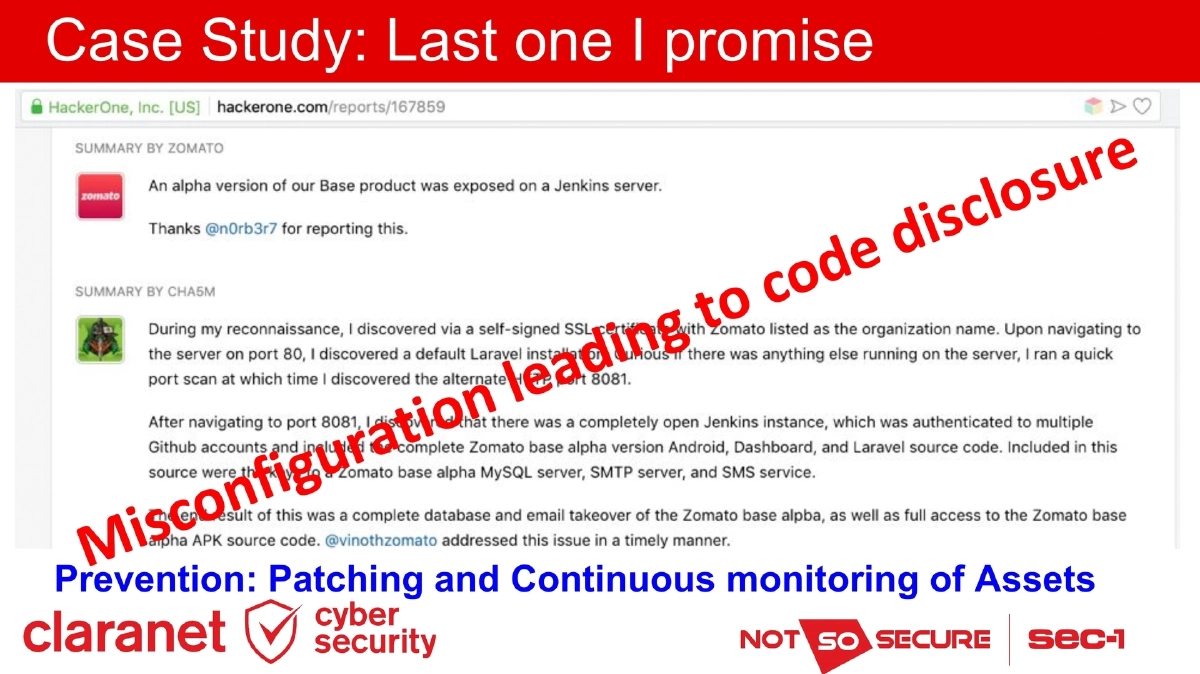
Case Studies: Multiple scenarios demonstrating security failures and their prevention:
- Unaccounted assets — prevented by recurring inventory and automated assessments
- Accidental credential exposure — prevented by pre-commit hooks and continuous repository monitoring
- Cloud misconfiguration — prevented by continuous monitoring and configuration review
- Misconfiguration leading to code disclosure — prevented by patching and continuous asset monitoring
-
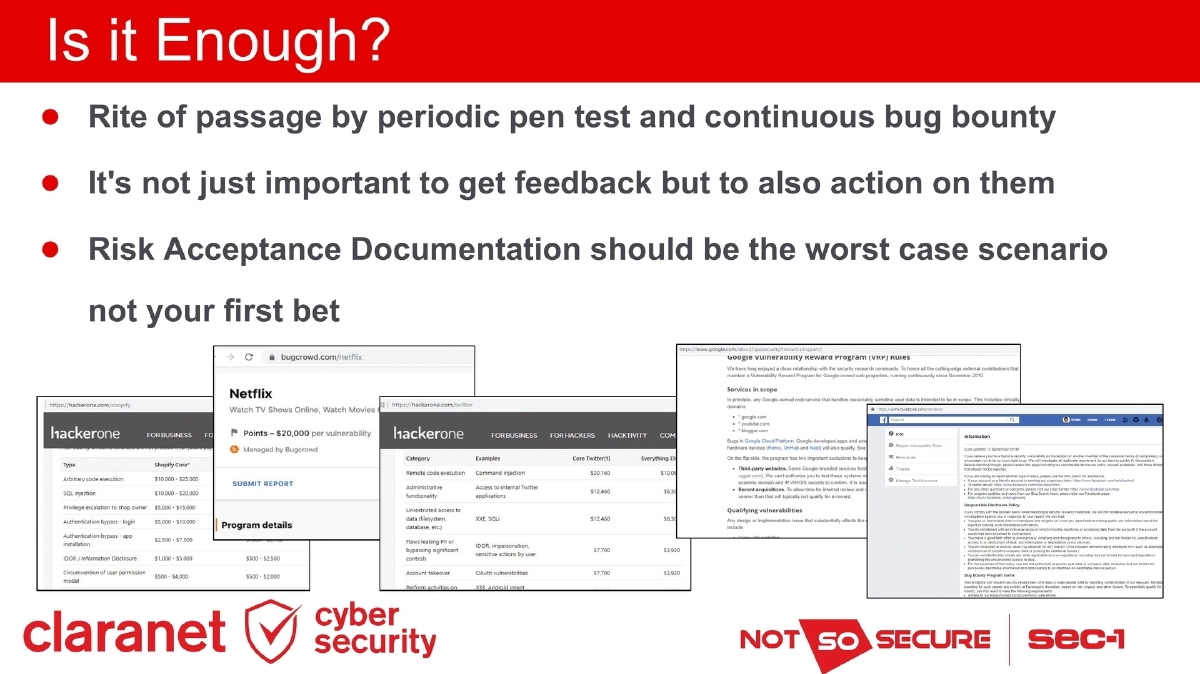
Beyond Automation: Periodic penetration testing and continuous bug bounty programs remain essential. Organizations must act on feedback rather than just collecting it, and risk acceptance documentation should represent worst-case scenarios rather than being the default response.
Actionable Takeaways
- Audit your current DevOps pipeline and identify gaps where security controls are missing — map each stage (pre-commit through production) against the DevSecOps pipeline framework presented.
- Apply the 15-minute execution rule when evaluating security tools for pipeline integration, and require machine-readable output (JSON/XML) to enable automated processing and vulnerability management.
- Implement pre-commit hooks as a first line of defense against credential leakage, but treat them as one layer in a defense-in-depth strategy since they can be bypassed.
- Establish a Security Champions program with one representative per development team, supported by internal bug bounties and cross-skilling opportunities to build a security-conscious culture organically.
- For cloud environments, expand security monitoring beyond application-level concerns to include IAM policies, billing anomalies, security group configurations, and comprehensive asset inventory.
- Adopt the People-Process-Technology enablers framework — involve security from the ideation phase, prioritize fixes by risk, and templatize security tooling per language/platform for consistency.
- Complement automated DevSecOps controls with periodic penetration testing and bug bounty programs, and establish a culture of acting on findings rather than defaulting to risk acceptance.
- Start small and iterate — DevSecOps is not one-size-fits-all, and every environment is different. Test and validate tools and processes before broad implementation.