(26 Mar 2026)

Security Days 2026 Spring

(24 Mar 2026)

Security Days 2026 Spring

(28 Feb 2026)

Nullcon Goa 2026

(27 Feb 2026)

Nullcon Goa 2026

(11 Dec 2025)

BlackHat Europe 2025

(01 Nov 2025)
Payment Gateway Integration Security Handbook

(23 Oct 2025)

Security Days 2025 Fall

(18 Sep 2025)

OpenSSF SBOM Everywhere SIG

(08 Aug 2025)

Adversary Village @ DefCon USA 2025

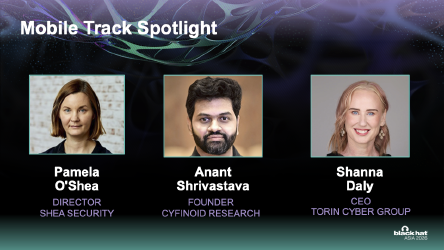
(07 Aug 2025)

BlackHat USA 2025

(07 Aug 2025)
Supply Chain Microsummit @ BlackHat USA 2025

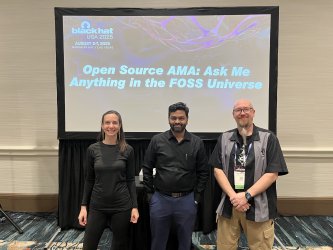
(06 Aug 2025)

BlackHat USA 2025

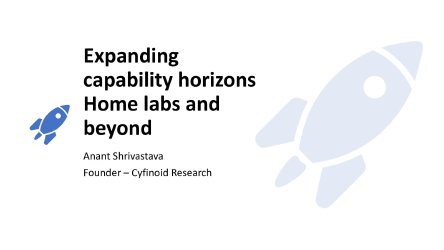
(15 Jun 2025)

Vulncon 2025

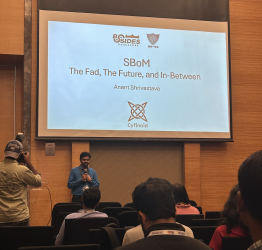
(08 Feb 2025)

Bsides Kerela 2025

(03 Aug 2024)

BlackHat USA 2024

(11 Jan 2022)
India Digital Summit 2022

(06 Aug 2021)

Adversary Village DefCon USA 2021

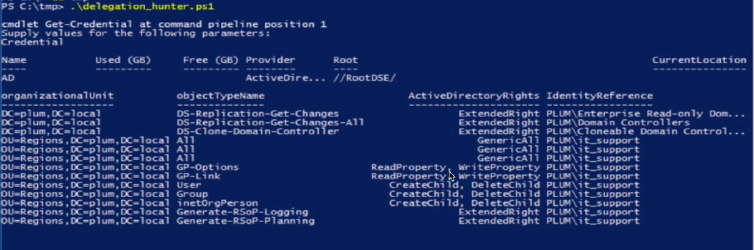
(18 Nov 2020)

HITB Cyber Week Dubai: Red Team Village

(18 Nov 2020)

HITB Cyber Week Dubai: Red Team Village

(09 Oct 2018)
Freewheeling discussion around opensource and my projects including androidtamer and null study groups

(20 Apr 2016)
techRadar
An Article discussing Android Security in context of various ROM’s in market

(20 Aug 2015)
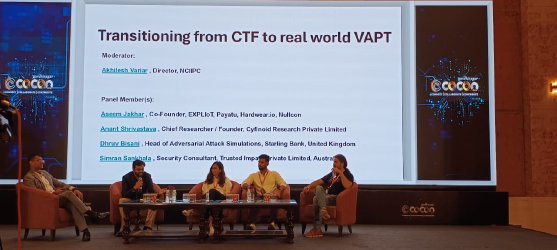
c0c0n 2015

(03 Aug 2012)

c0c0n 2012
how to use android devices for basic pentesting operations

(16 Oct 2011)
This paper focuses on custom rom’s and check for security misconfiguration’s which could yield to device compromise.