Nessus Reporting Karma
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This interactive session covers Nessus vulnerability scanner reporting formats, custom report parsing, and building an integrated vulnerability management system with PHP and Oracle database backend.
Key Topics Covered
Nessus Reporting Formats:
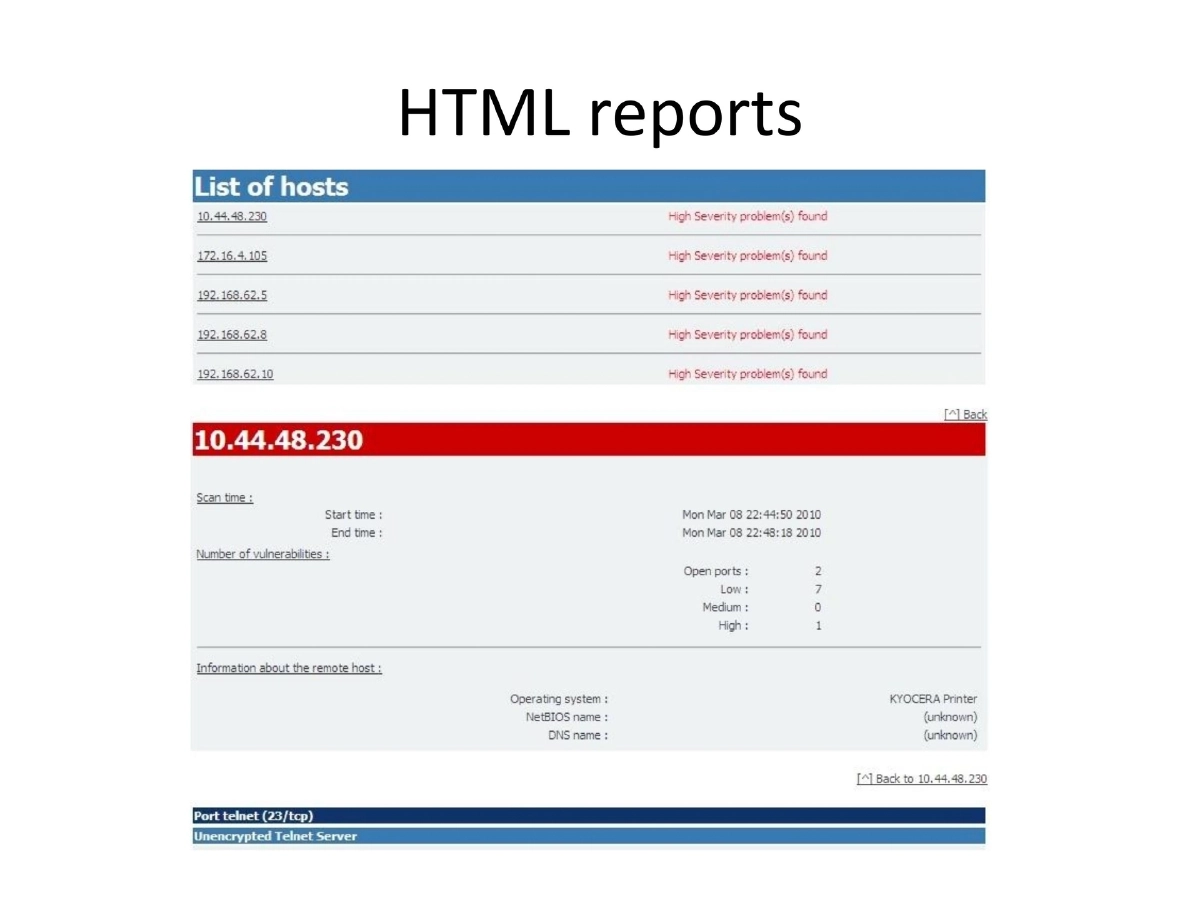
- HTML: Standard web-based reports
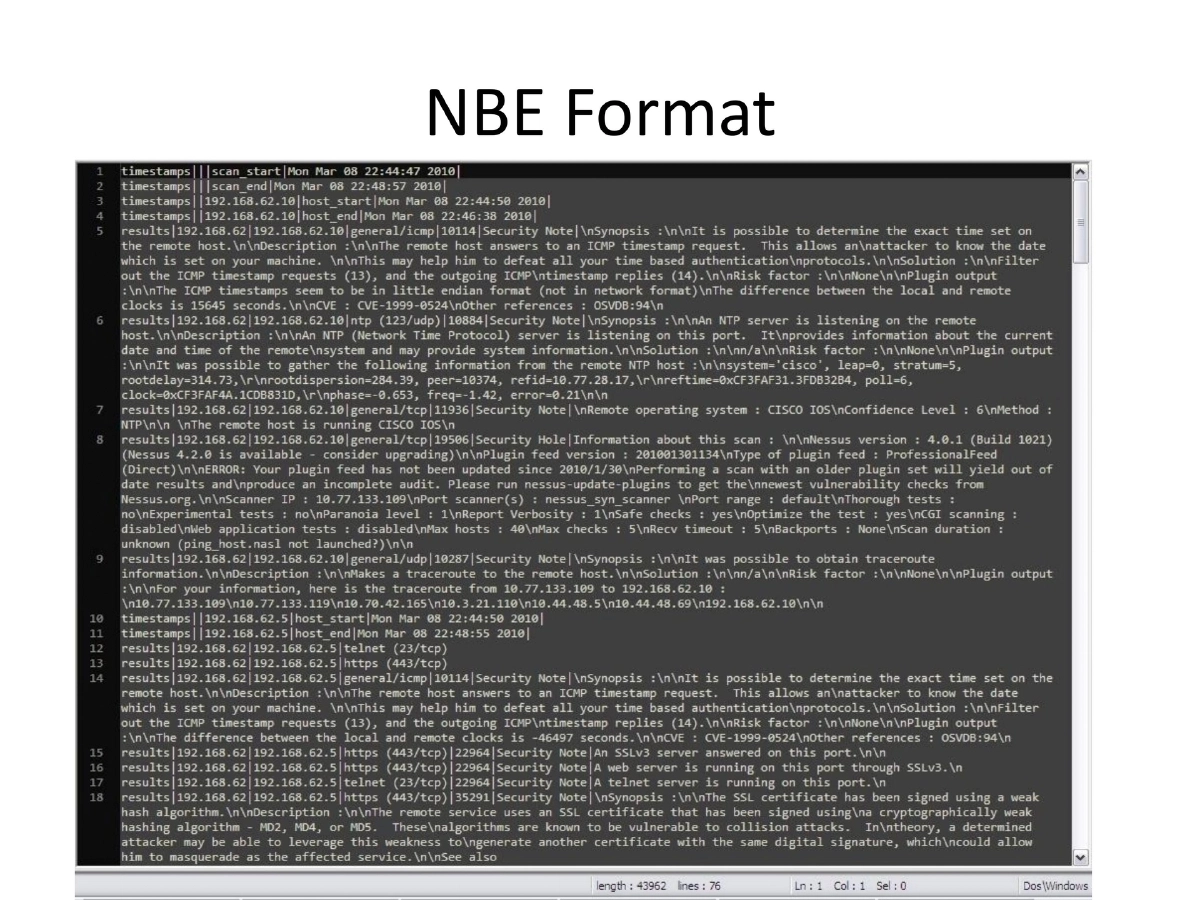
- NBE: Legacy format
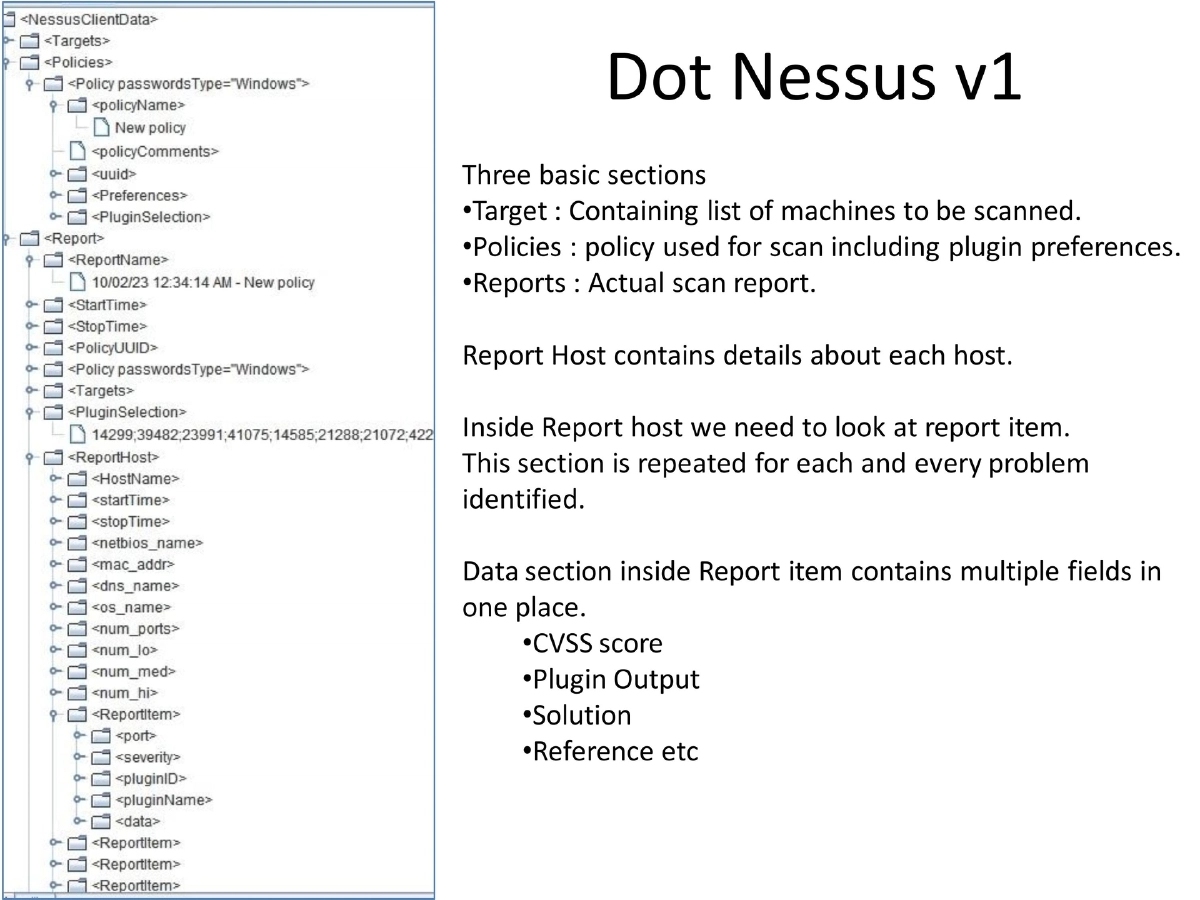
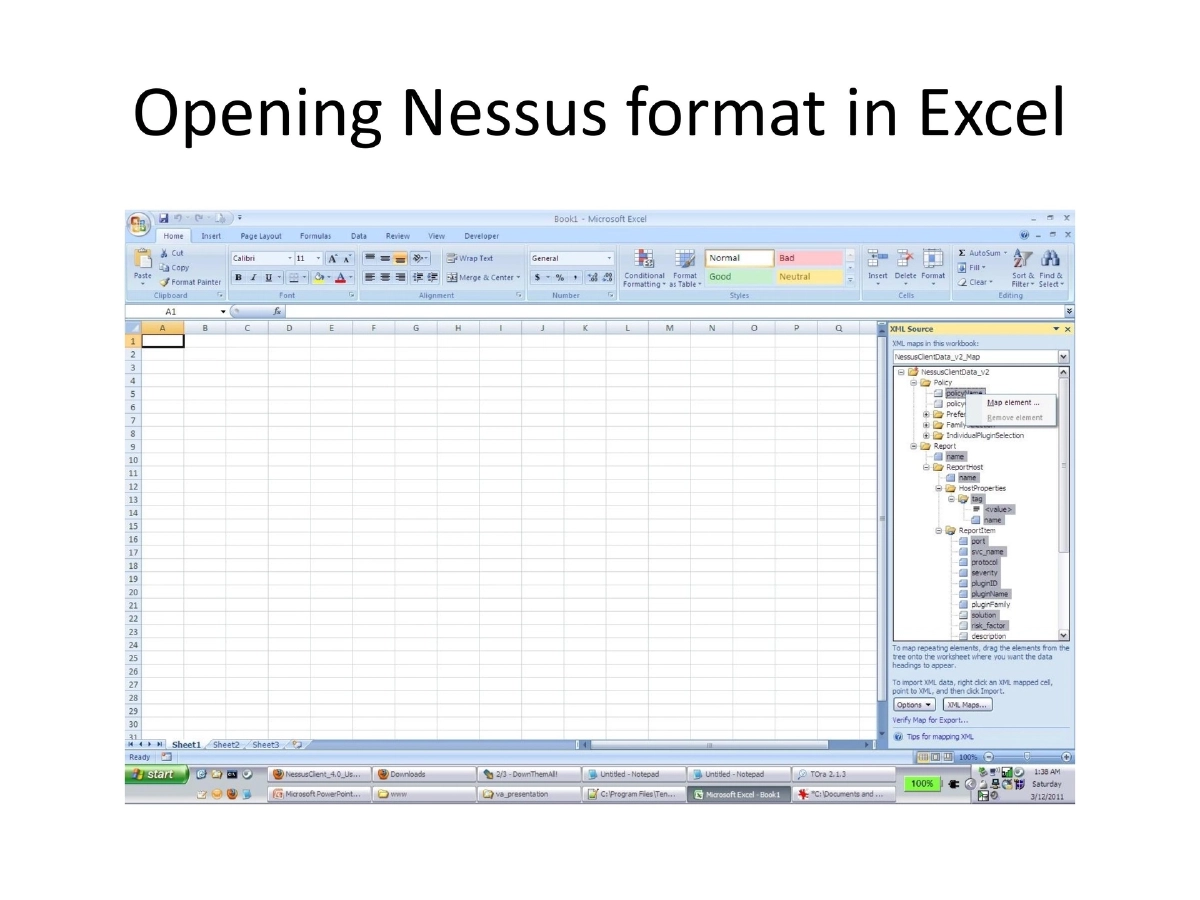
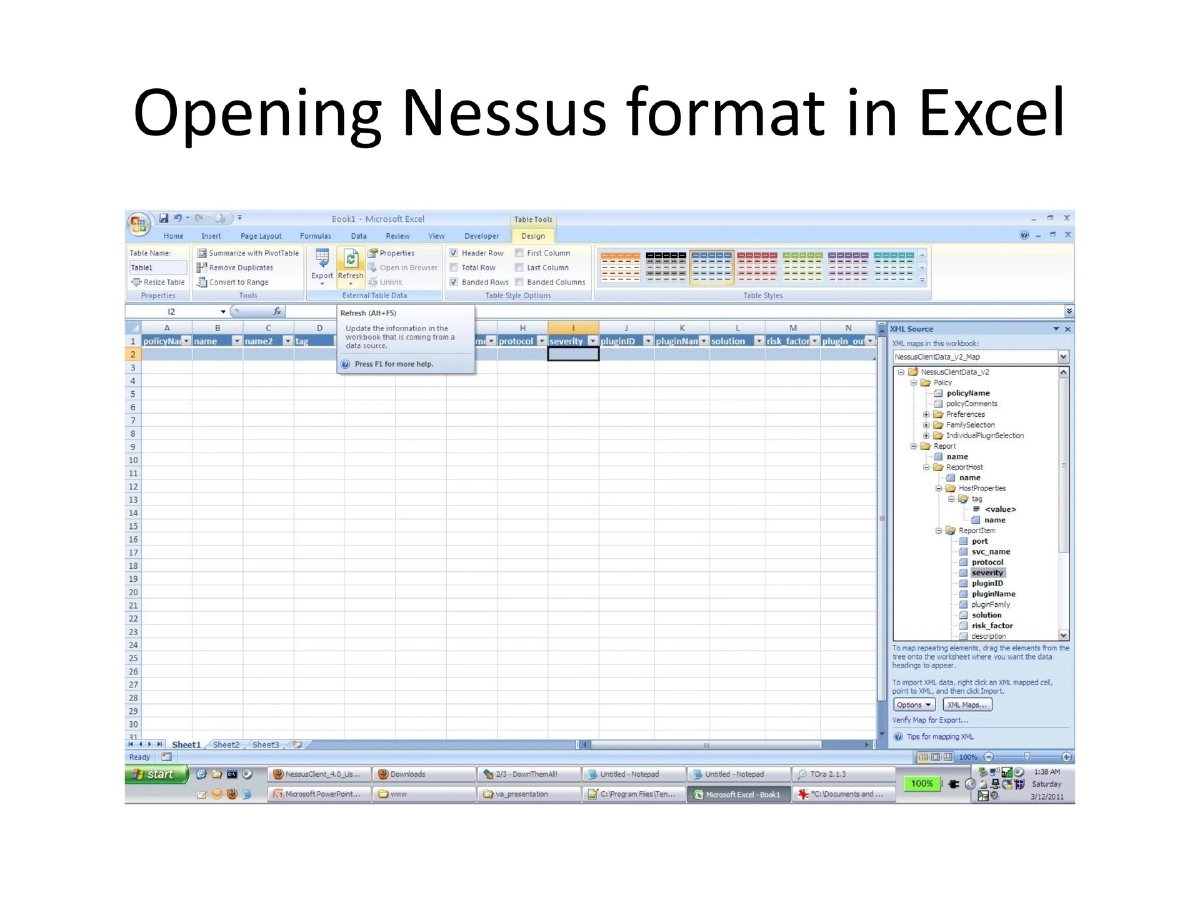
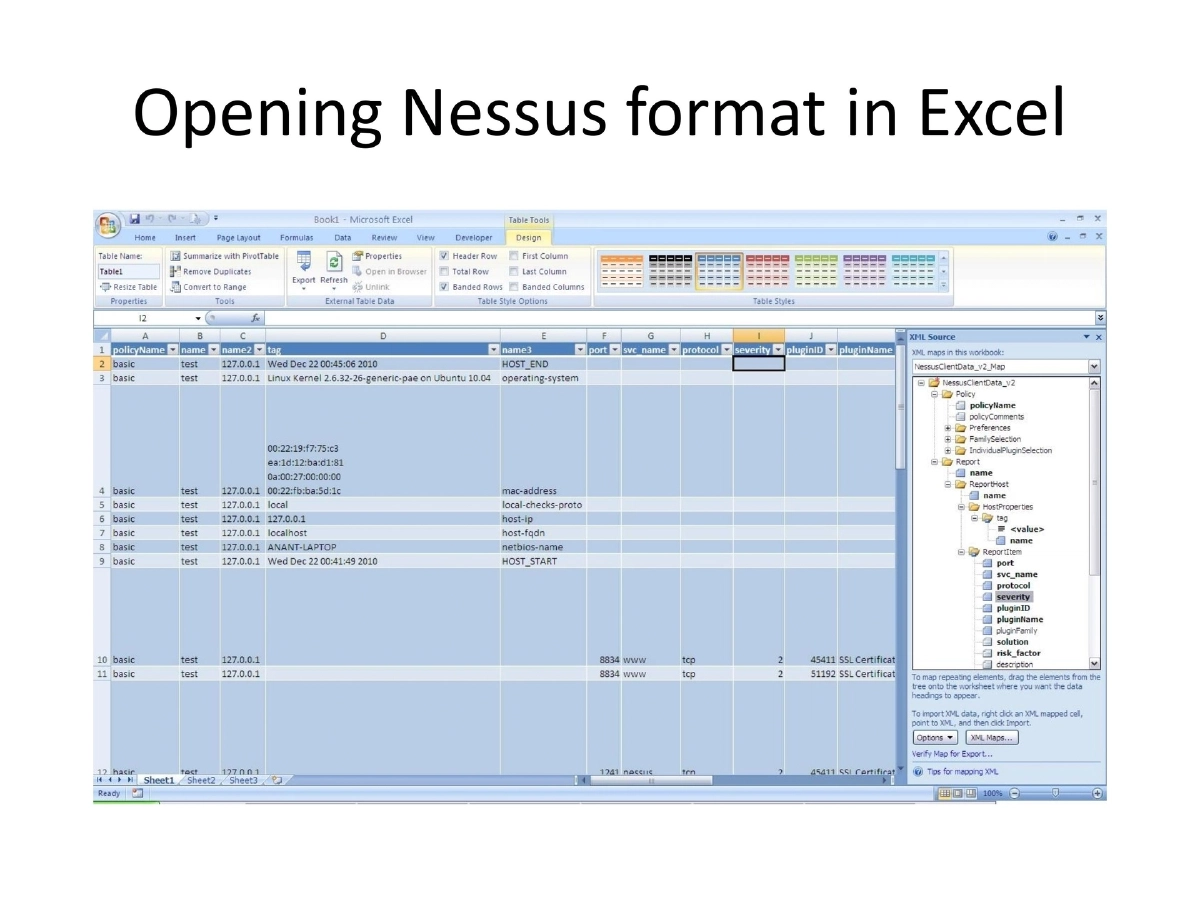
- .nessus v1: Three sections (Target, Policies, Reports) with data fields combined in a single section
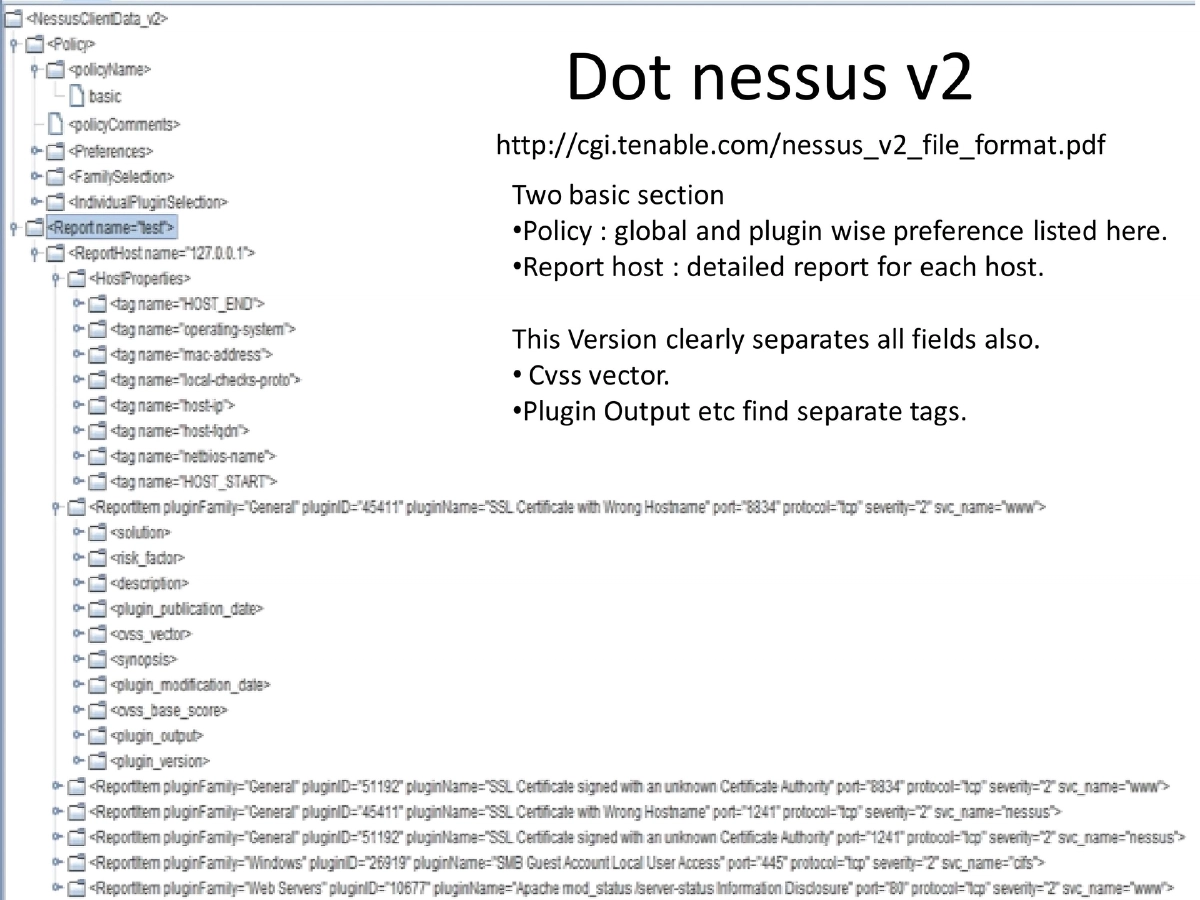
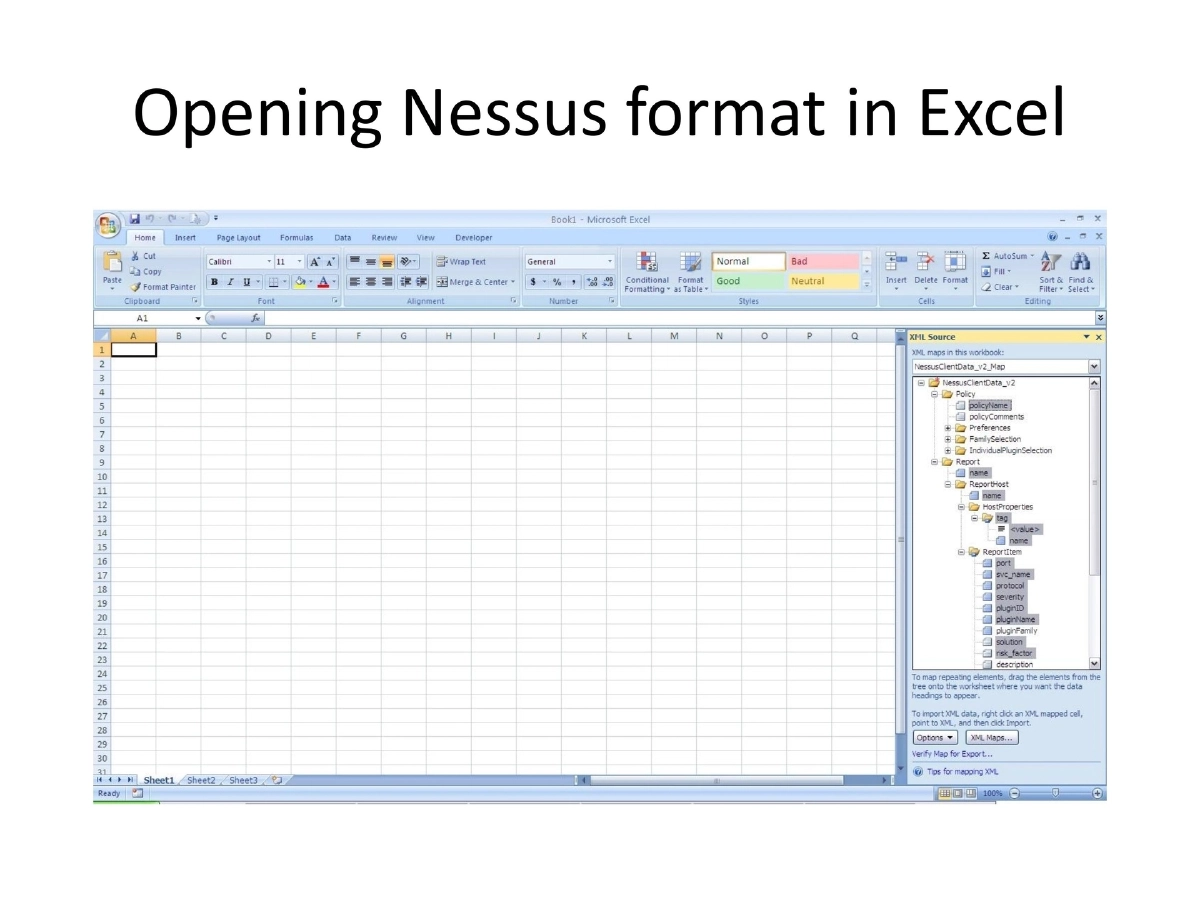
- .nessus v2: Improved format with clearly separated fields (CVSS vector, plugin output in separate tags), documented at Tenable’s specification
Format Evolution:
- The v2 format continuously evolves with new tags
- Recent additions include exploit_available, exploit_framework_canvas, canvas_package, exploit_framework_metasploit, and metasploit_name
- These fields enable automated correlation with exploitation frameworks
Custom Parsing Approaches:
- Existing options include Seccubus (periodic scan with report comparison) and various Python/Perl tools
- Custom parsing needed for: integrating with existing infrastructure tools, deeper customization, and better control over scan frequency and granularity
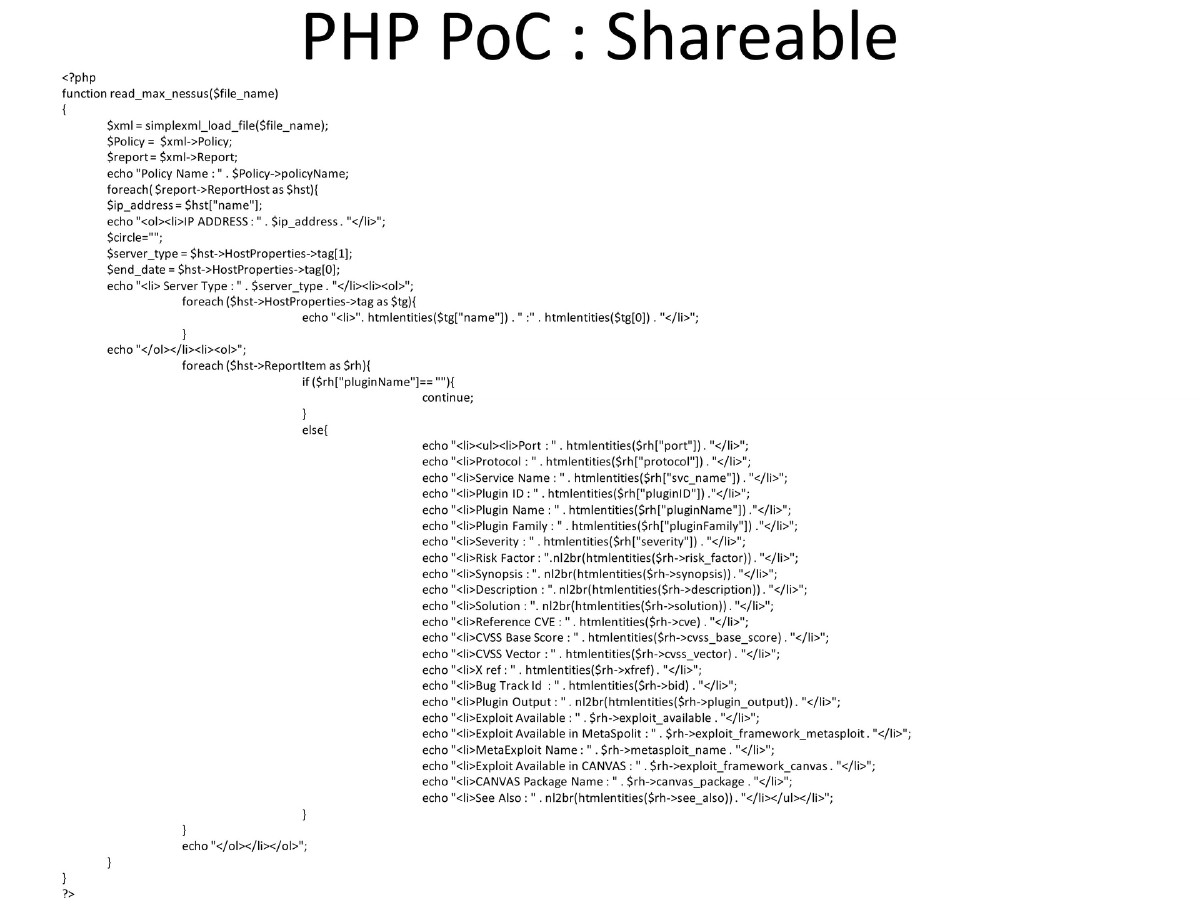
- Demonstrated a PHP proof-of-concept parser using simplexml_load_file to extract all report fields
Integrated Vulnerability Management System:
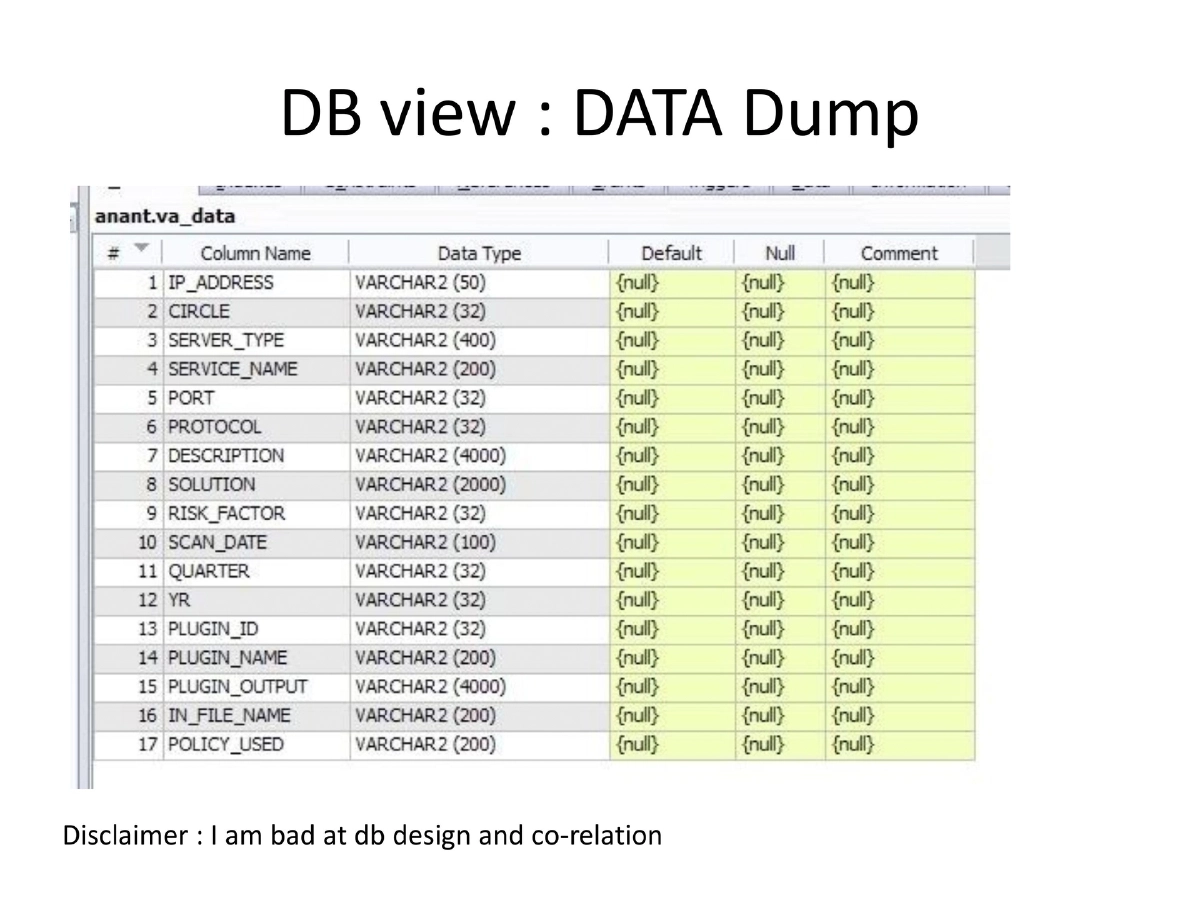
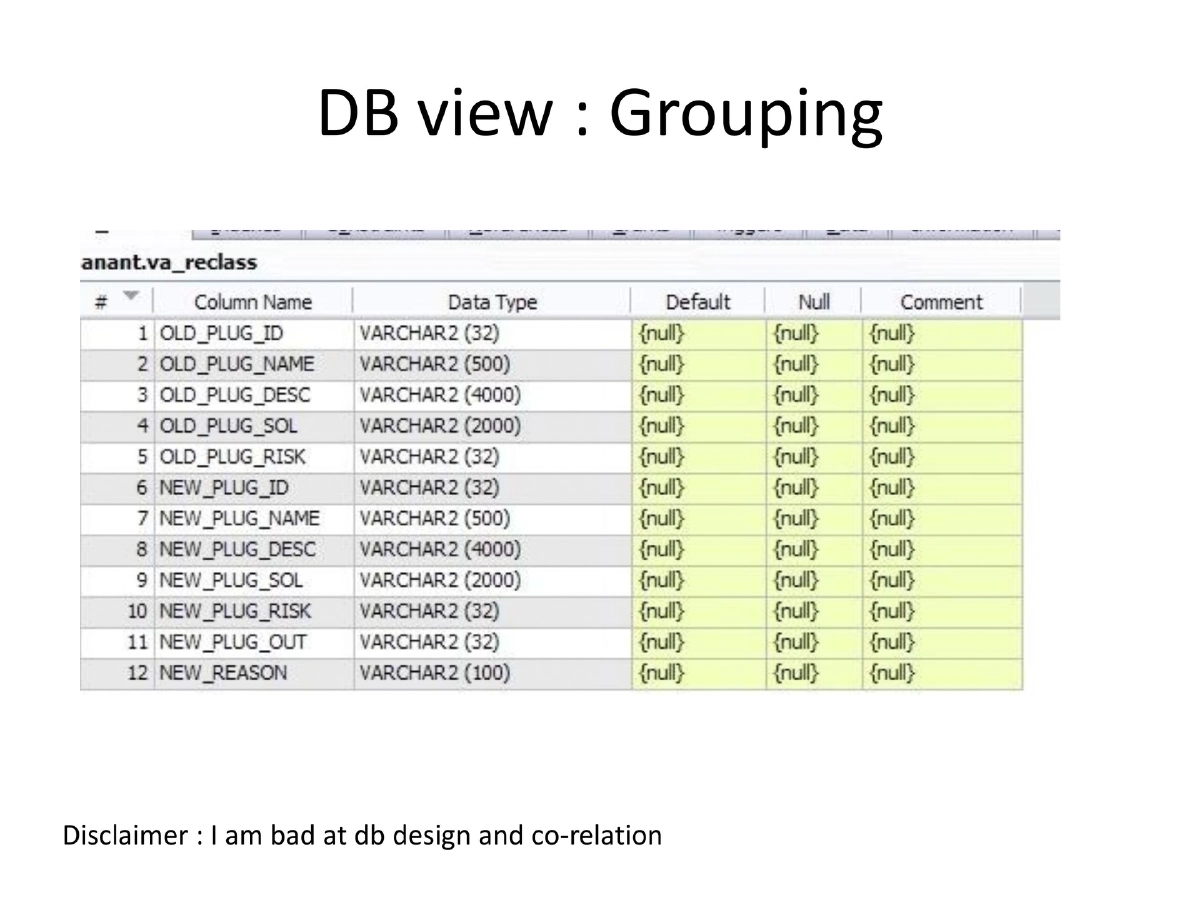
- PHP frontend for uploading reports to Oracle database
- Integration with inventory management tools
- Key analysis features:
- Known false positive identification by plugin ID
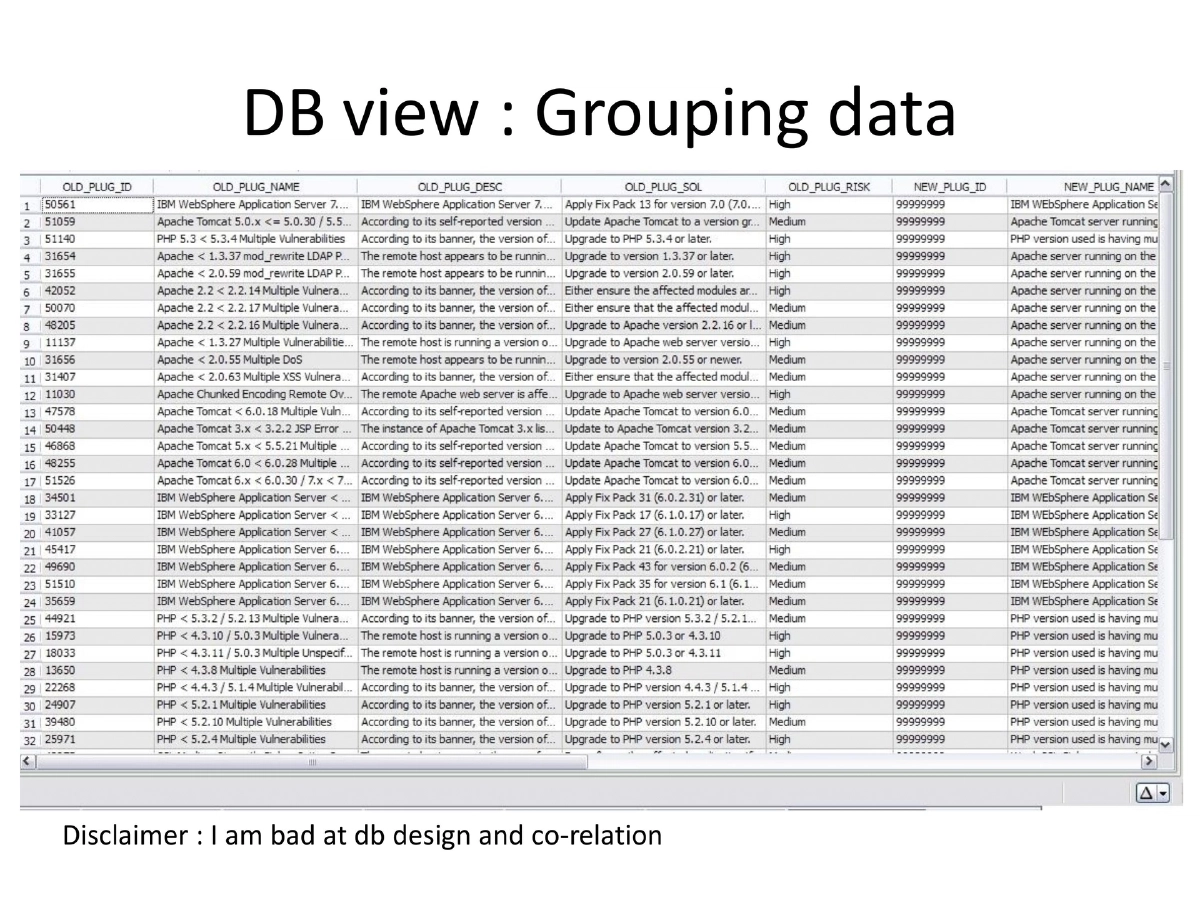
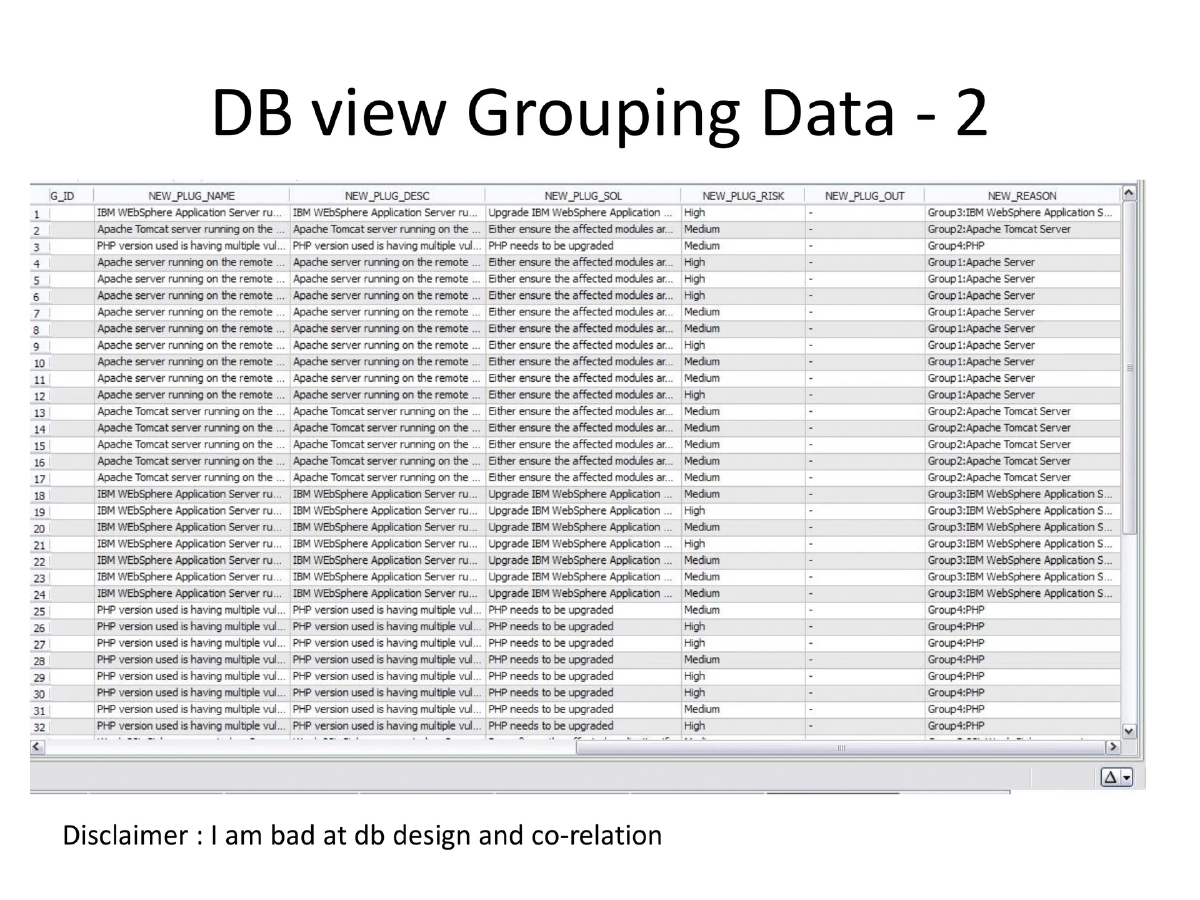
- Vulnerability grouping by common remediation
- Classification by network vs. server devices
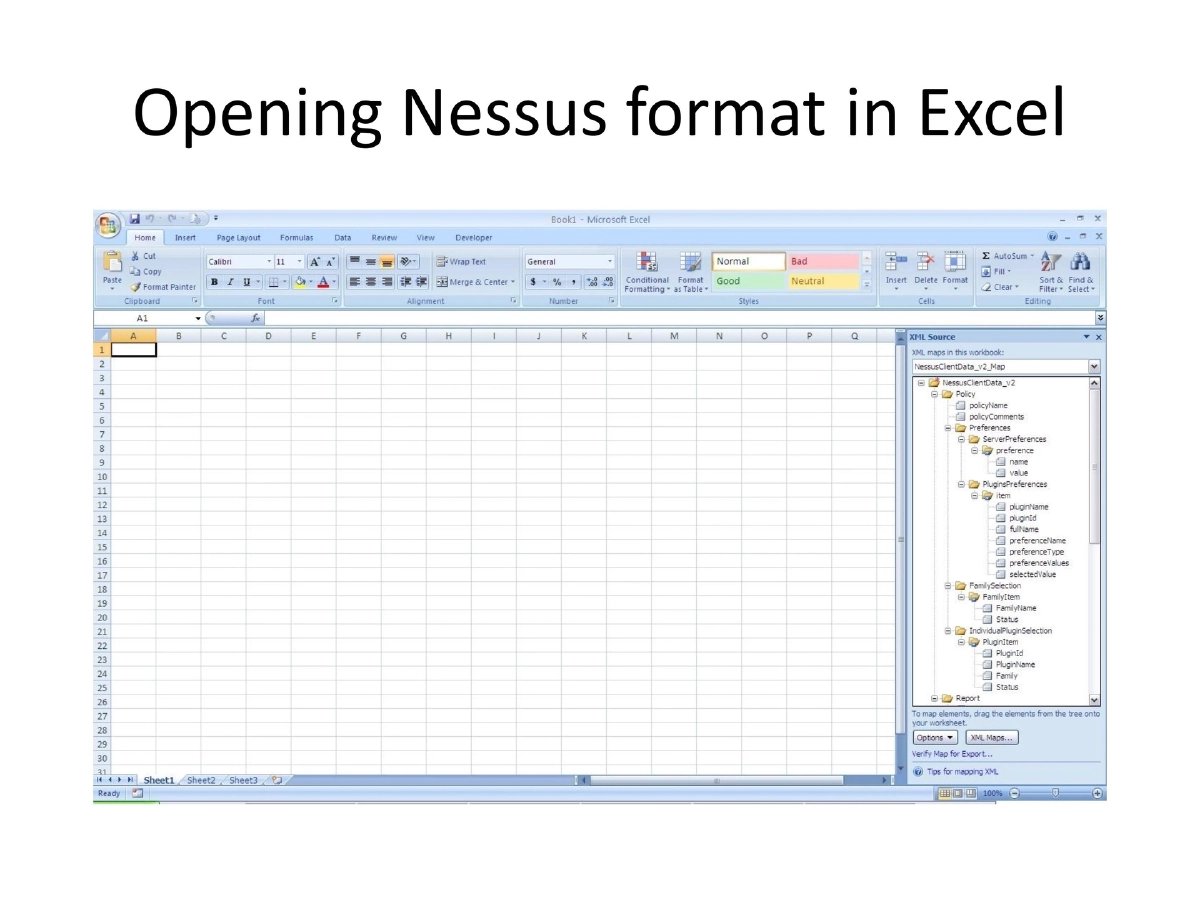
- Excel-based report extraction
- Cross-referencing with system inventory to find missing systems
- Tracking repeated vulnerabilities over time using system inventory IDs
- Detecting changes in device details between scan snapshots
Plugin Detail Extraction:
- Nessus 4.2 and below: command-line query interface
- Above 4.2: XML-RPC interface for remote initialization and control
Planned Enhancements:
- Creating similar interface for OpenVAS
- Using XML-RPC for remote initialization and control
- Adding MySQL as an alternative database option
Actionable Takeaways
- Understanding Nessus XML formats enables powerful custom reporting
- Integrating vulnerability data with asset inventory provides organizational context
- Automated false positive identification by plugin ID reduces analysis burden
- Grouping vulnerabilities by common remediation streamlines patching efforts
- Historical tracking reveals vulnerability trends and persistent issues