Android Village
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
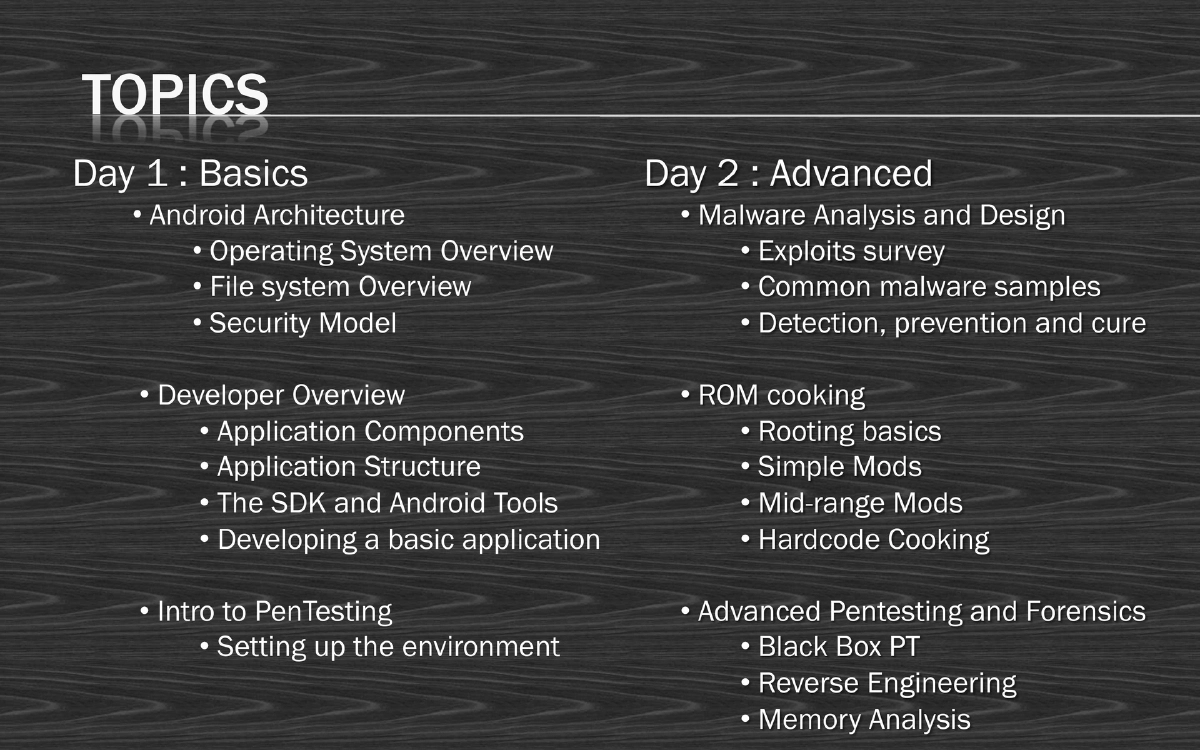
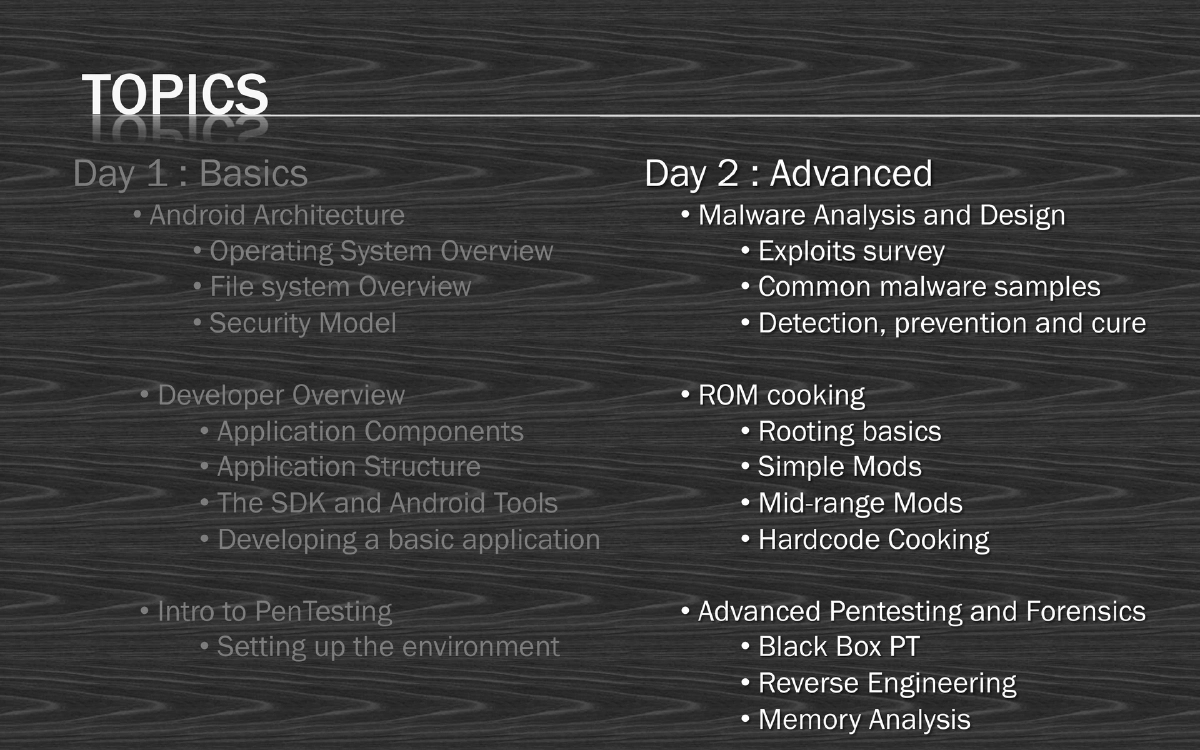
This two-day Android Hacking Village workshop provides comprehensive coverage of Android security, from architecture fundamentals and application development through malware analysis, ROM cooking, exploit techniques, and penetration testing methodologies.
Key Topics Covered
Day 1 - Fundamentals:
Android Architecture:
- Founded 2003 by Andy Rubin et al., acquired by Google 2005, Open Handset Consortium formed 2007
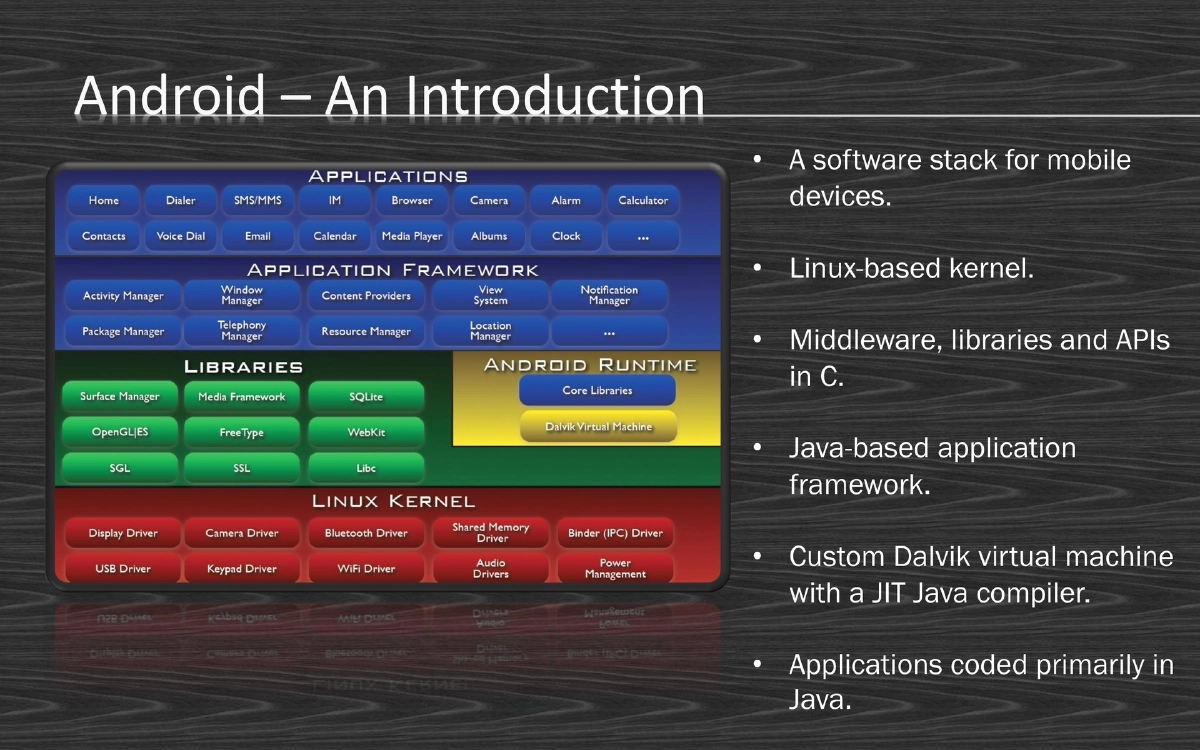
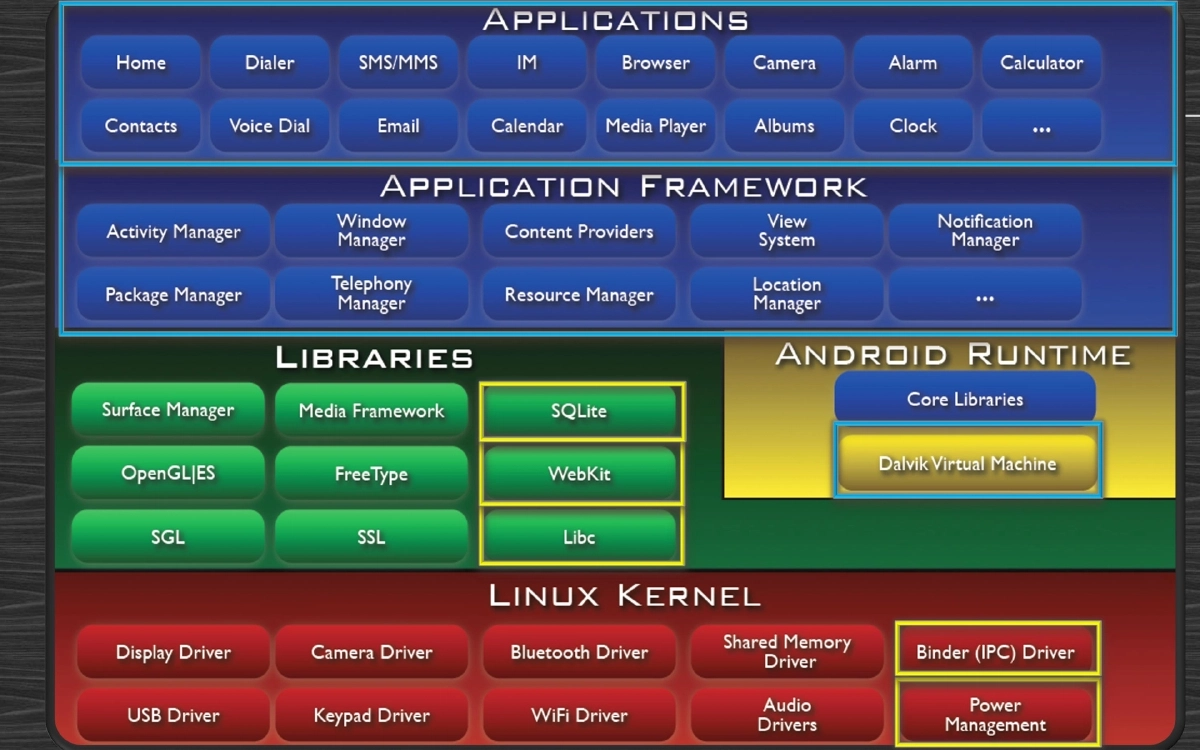
- Software stack: Linux kernel, C middleware/libraries/APIs, Java application framework, Dalvik VM with JIT compiler
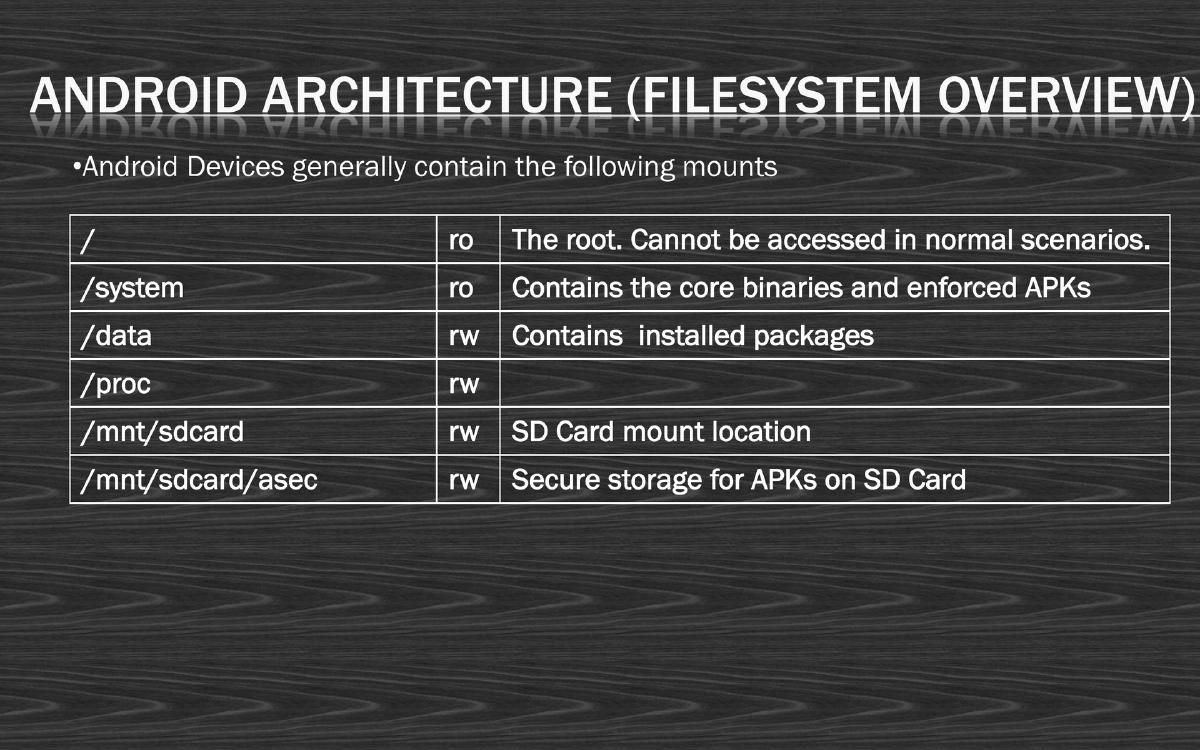
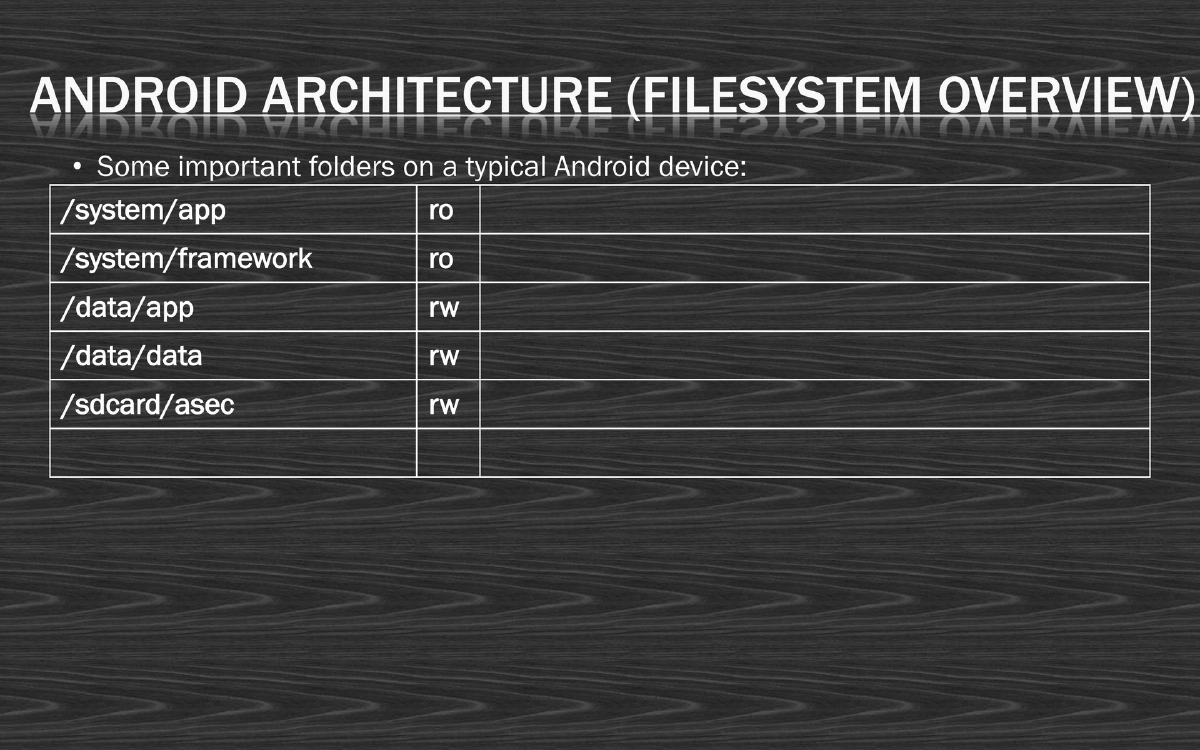
- Key filesystem mounts: / (root, read-only), /system (core binaries, read-only), /data (installed packages, read-write), /mnt/sdcard
Security Model - The Good:
- Traditional access control with idle-time locking
- Application sandboxing via unique VMs and Linux processes
- Permission-based access control (developer-configured, user-granted)
- Application provenance through X509 digital certificates
- Remote kill switch capability
Security Model - The Bad:
- No hardware-based encryption (pre-3.0), no non-executable memory areas
- Limited developer accountability, poor code obfuscation
- Applications easily trojanized, difficult anti-virus environment
- Long patch cycles, recovery/boot process vulnerabilities
- Security enforcement reliant on end-users
Application Development:
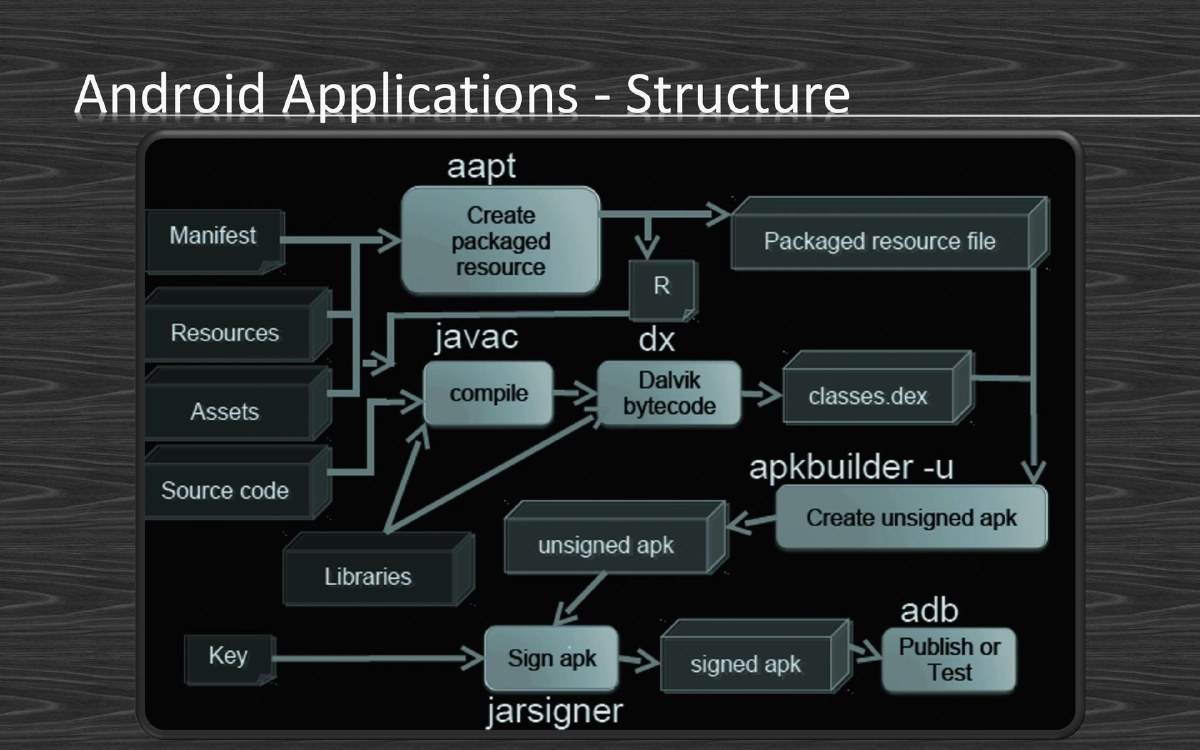
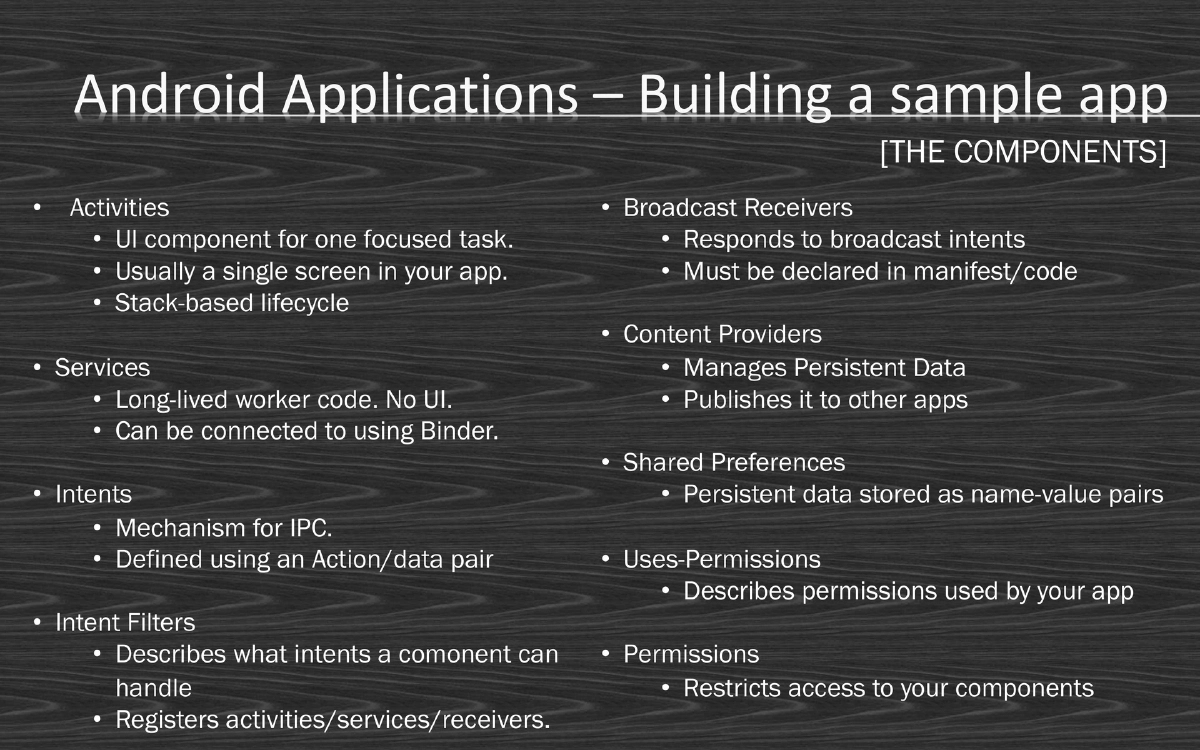
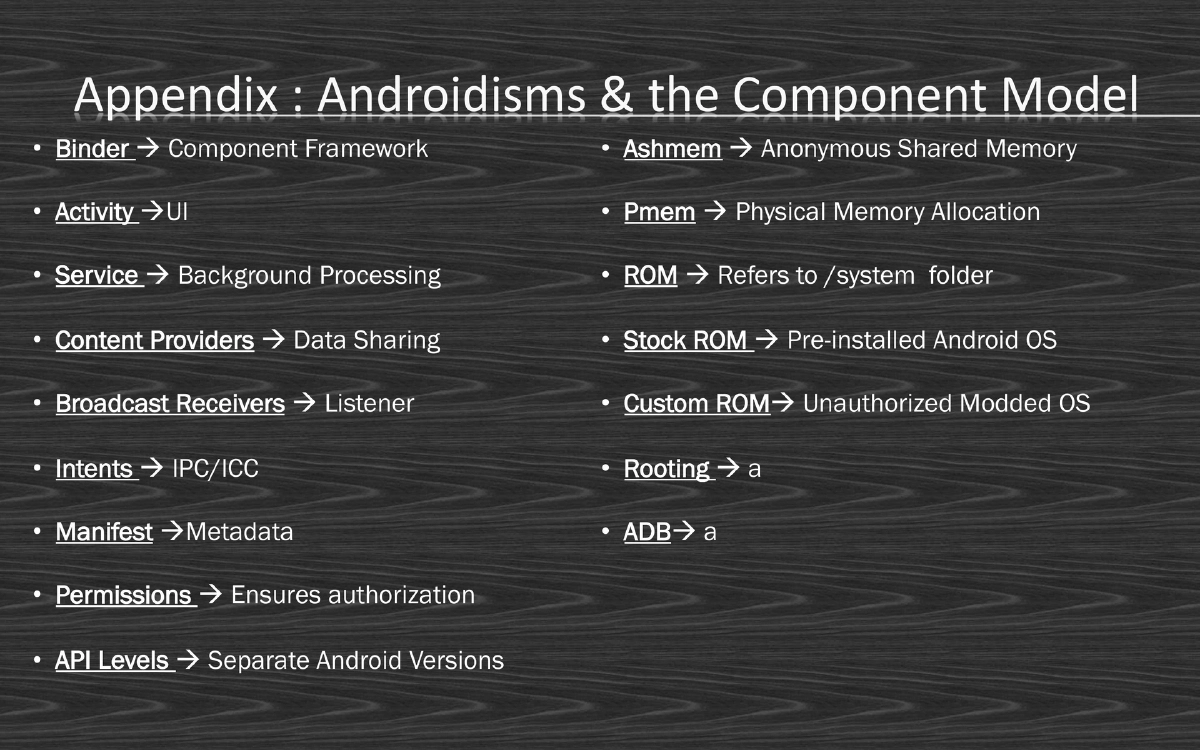
- APK structure (ZIP-formatted, JAR-based), components: Activities, Services, Intents, Broadcast Receivers, Content Providers
- GUI building with XML layouts, event listeners
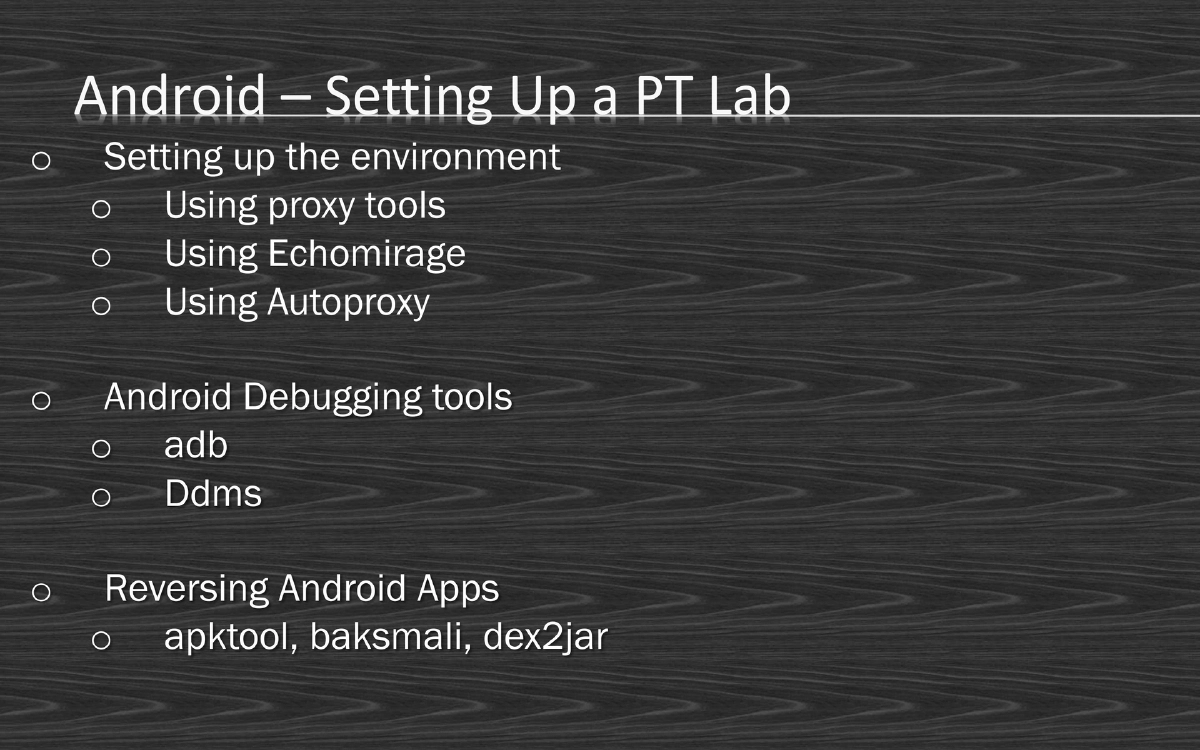
- SDK tools: adb, android manager, DDMS, emulator, logcat, ProGuard
Day 2 - Advanced Topics:
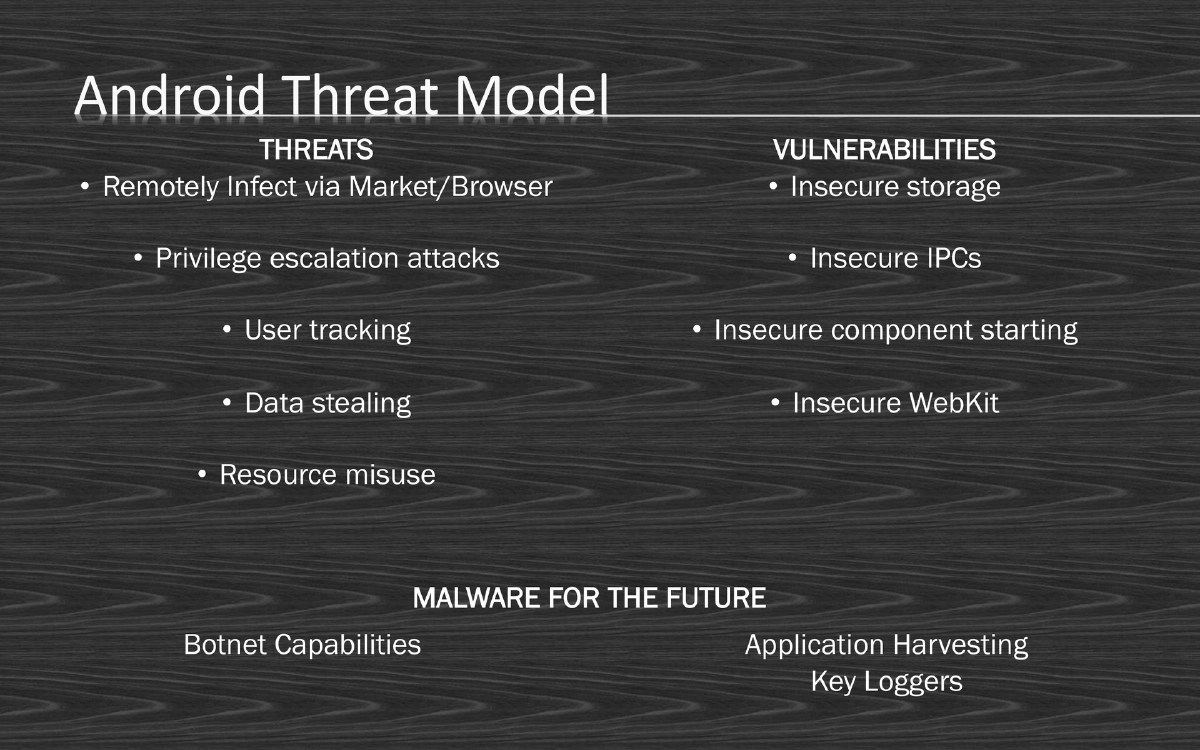
Android Threat Model:
- Threats: Remote infection via market/browser, privilege escalation, user tracking, data stealing, resource misuse
- Vulnerabilities: Insecure storage, insecure IPCs, insecure component starting, insecure WebKit
- Future malware: Botnet capabilities, application harvesting, key loggers
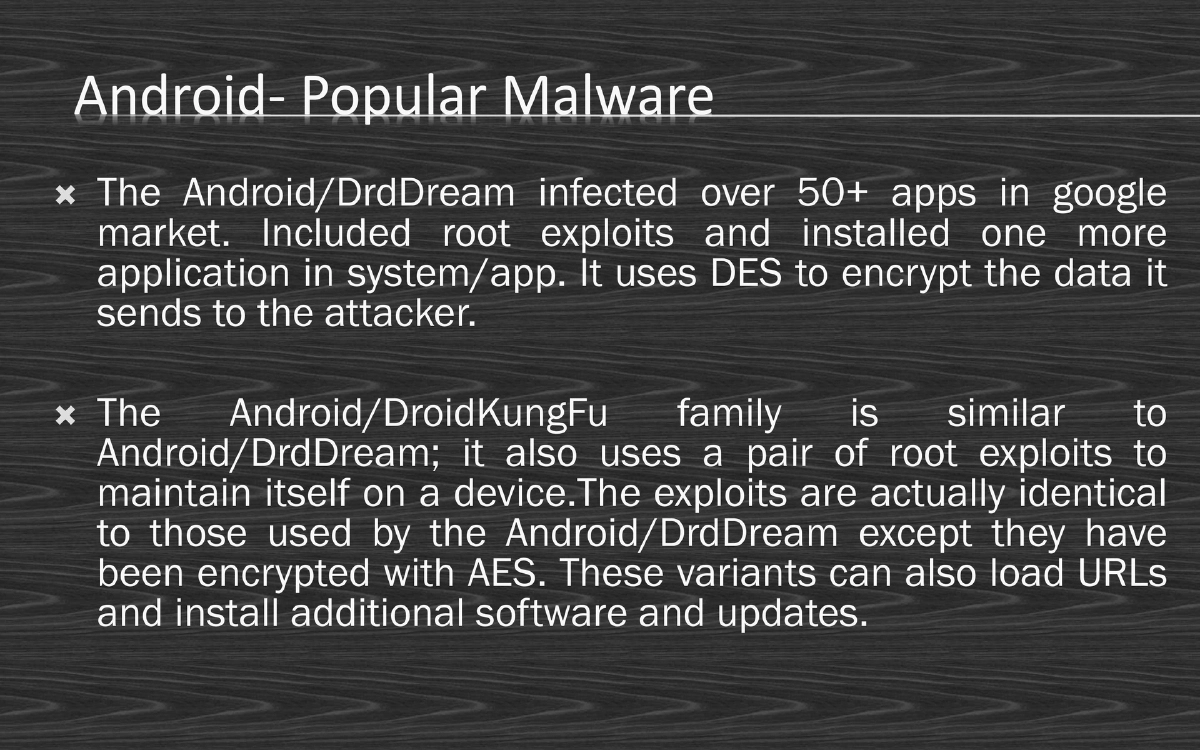
Notable Malware:
- Android/DrdDream: Infected 50+ market apps, included root exploits, used DES encryption
- Android/DroidKungFu: Similar to DrdDream, used AES-encrypted exploits, capable of loading URLs and installing updates
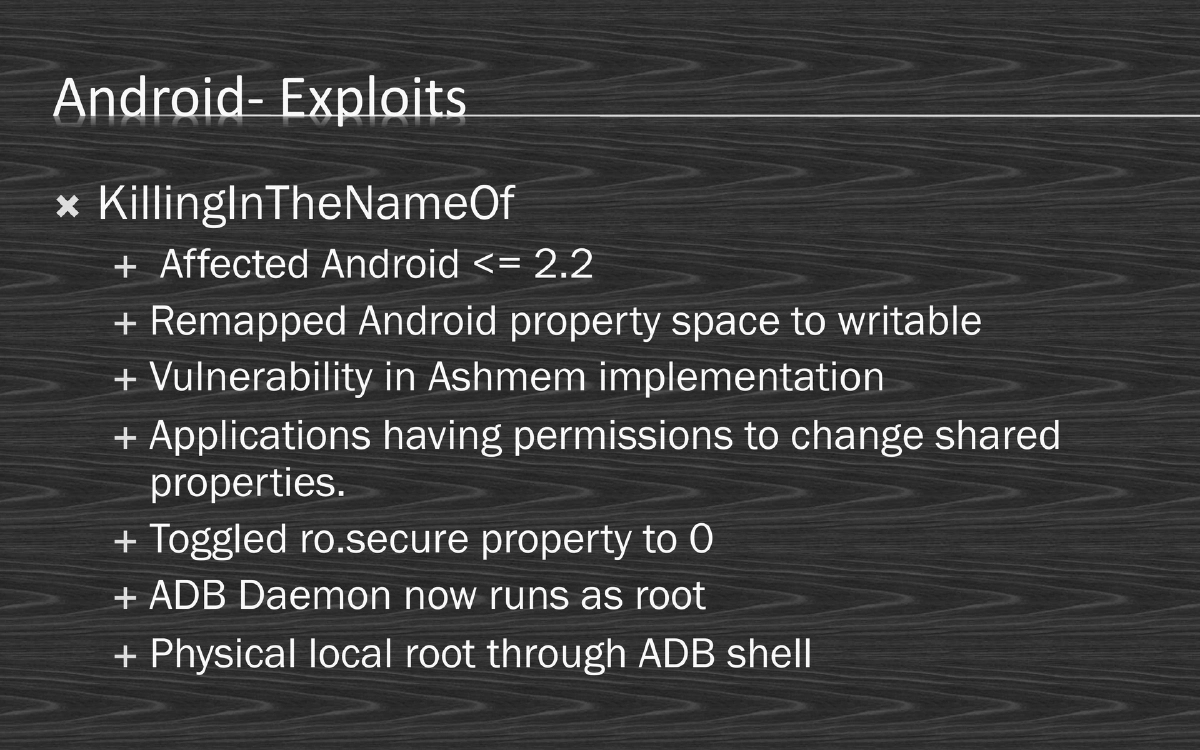
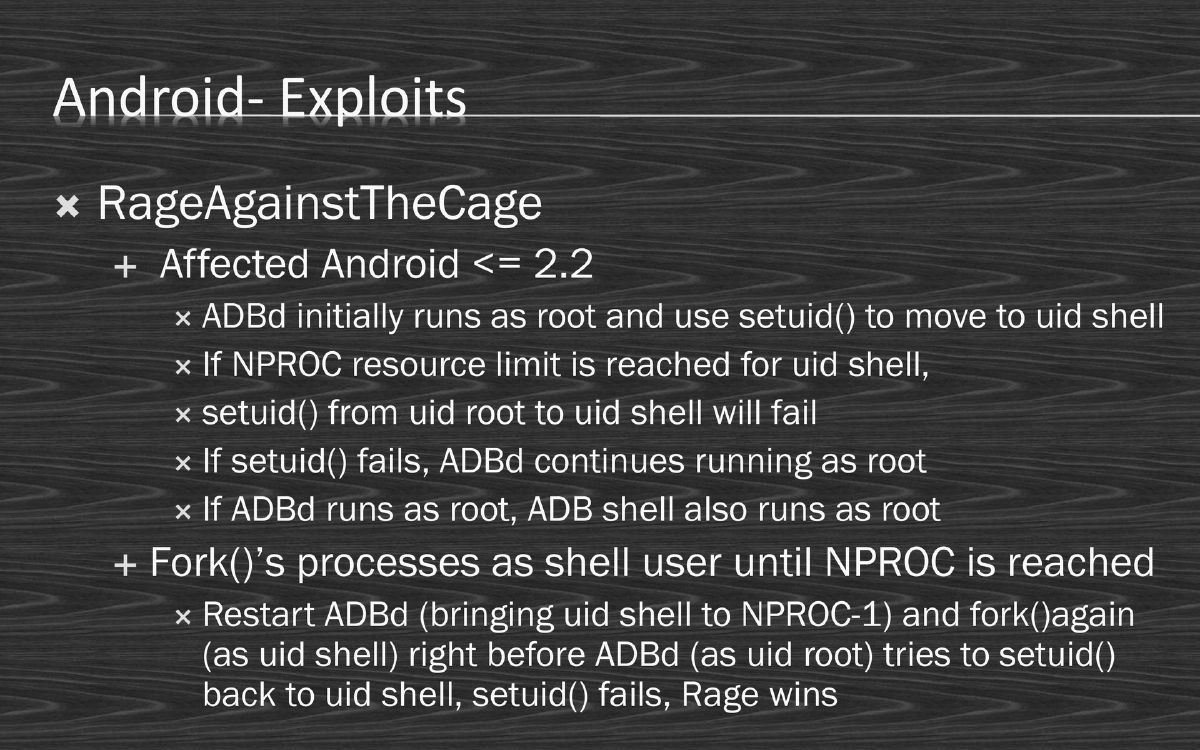
Exploit Techniques:
- KillingInTheNameOf: Affected Android <= 2.2, remapped property space to writable via Ashmem vulnerability
- RageAgainstTheCage: Exploited ADBd’s setuid() behavior when NPROC resource limit is reached, causing ADB to continue running as root
ROM and Rooting:
- Custom vs. stock ROM comparison (gaming, battery, overclocking variants)
- Three modding levels: Simple (removing/adding apps), Mid-level (decompiling/reversing), Hardcore (cross-compiling, driver modification)
- Rooting fundamentals: temporary vs. permanent root, SU and Superuser.apk
Actionable Takeaways
- Android security spans multiple layers from OS kernel to application logic
- The permission model, while useful, places too much trust in end-users
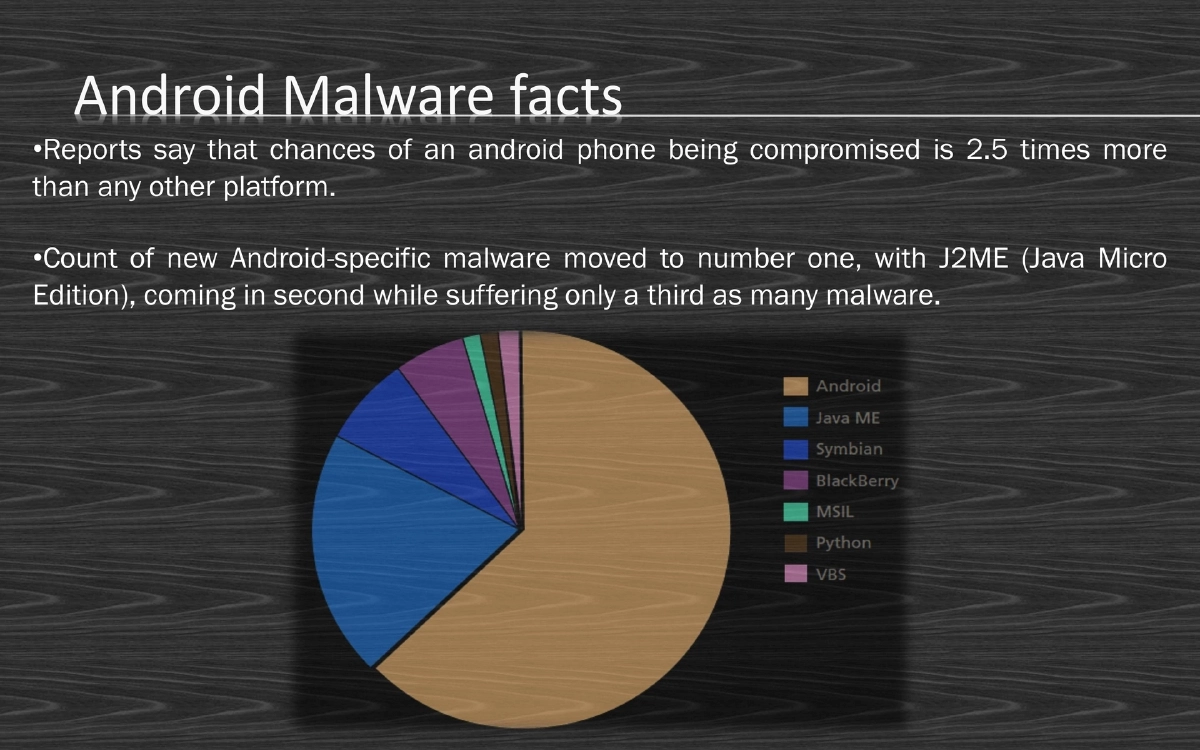
- Malware evolution on Android mirrors PC malware history
- Privilege escalation exploits target fundamental OS mechanisms (setuid, Ashmem)
- ROM security review is critical for any corporate Android deployment