G0s Workshop Android
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This workshop at the Ground Zero Summit provides a comprehensive deep dive into Android security, covering platform internals, application architecture, the Android Tamer toolkit, mobile security vulnerabilities, and hands-on penetration testing techniques for both testing Android apps and using Android as a testing platform.
Key Topics Covered
Android Platform Fundamentals:
- 56% smartphone market share, open source with minimal developer license cost
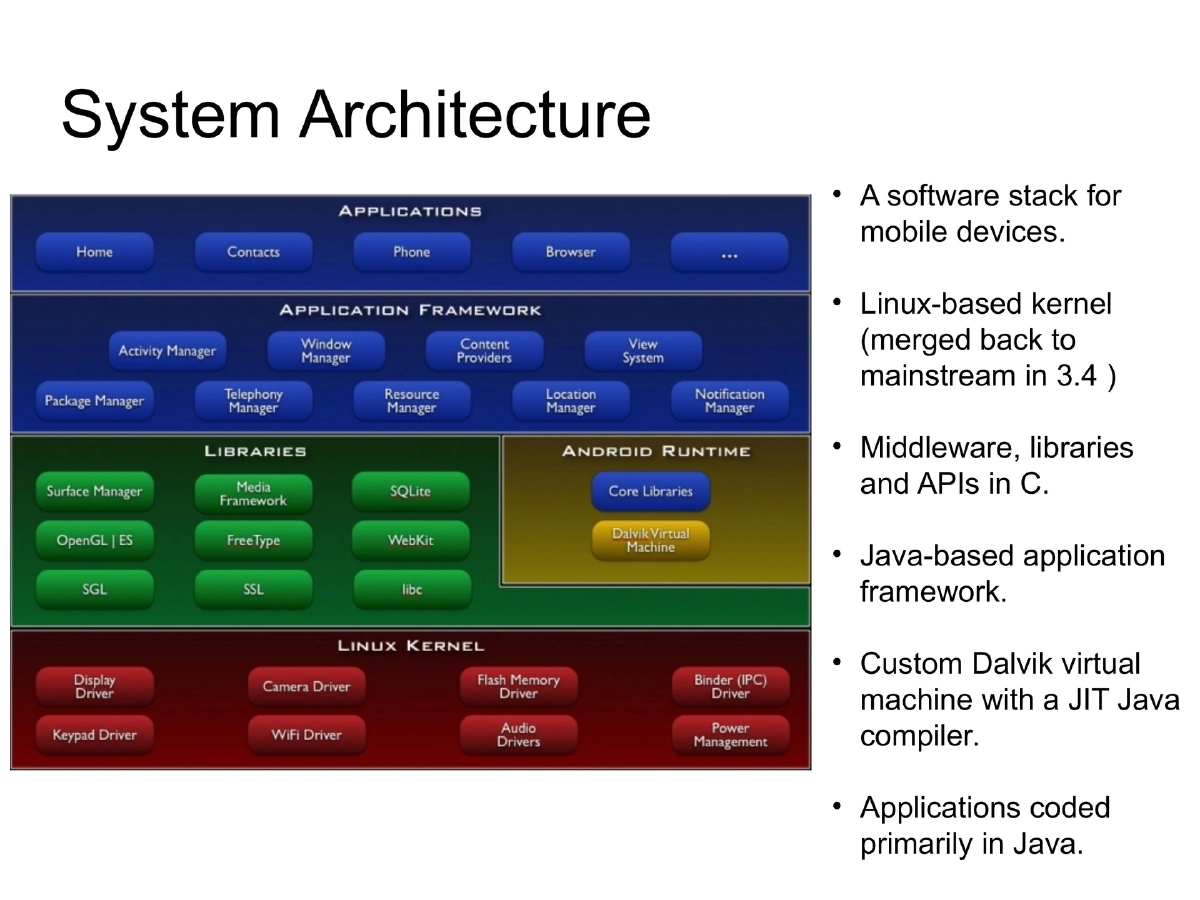
- Linux-based kernel (merged to mainstream in 3.4), Dalvik VM with JIT compiler
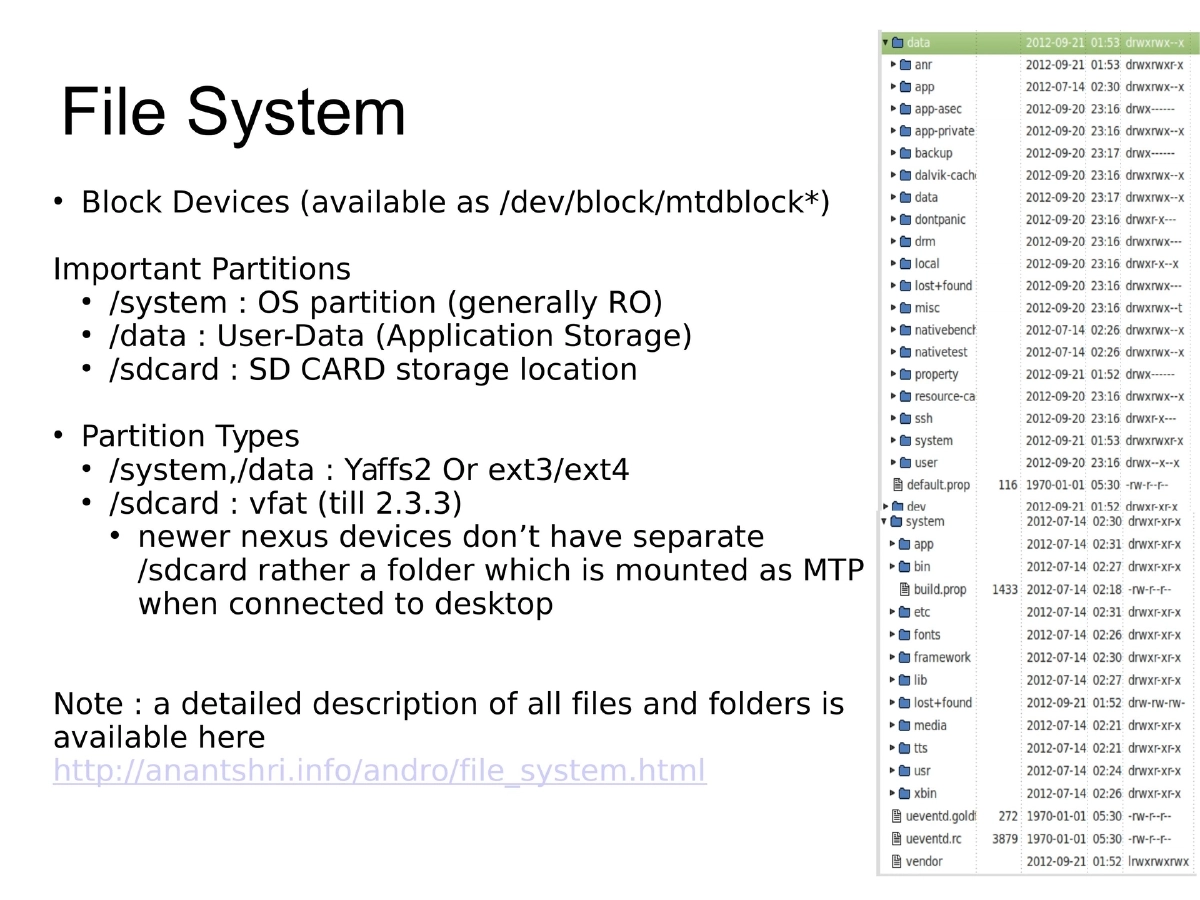
- File system: /system (OS image, yaffs2/ext), /data (user data), /sdcard (vfat)
- Security model: Unix permissions, SELinux (permissive in 4.3, enforced in 4.4), app sandboxing, permission-based access control
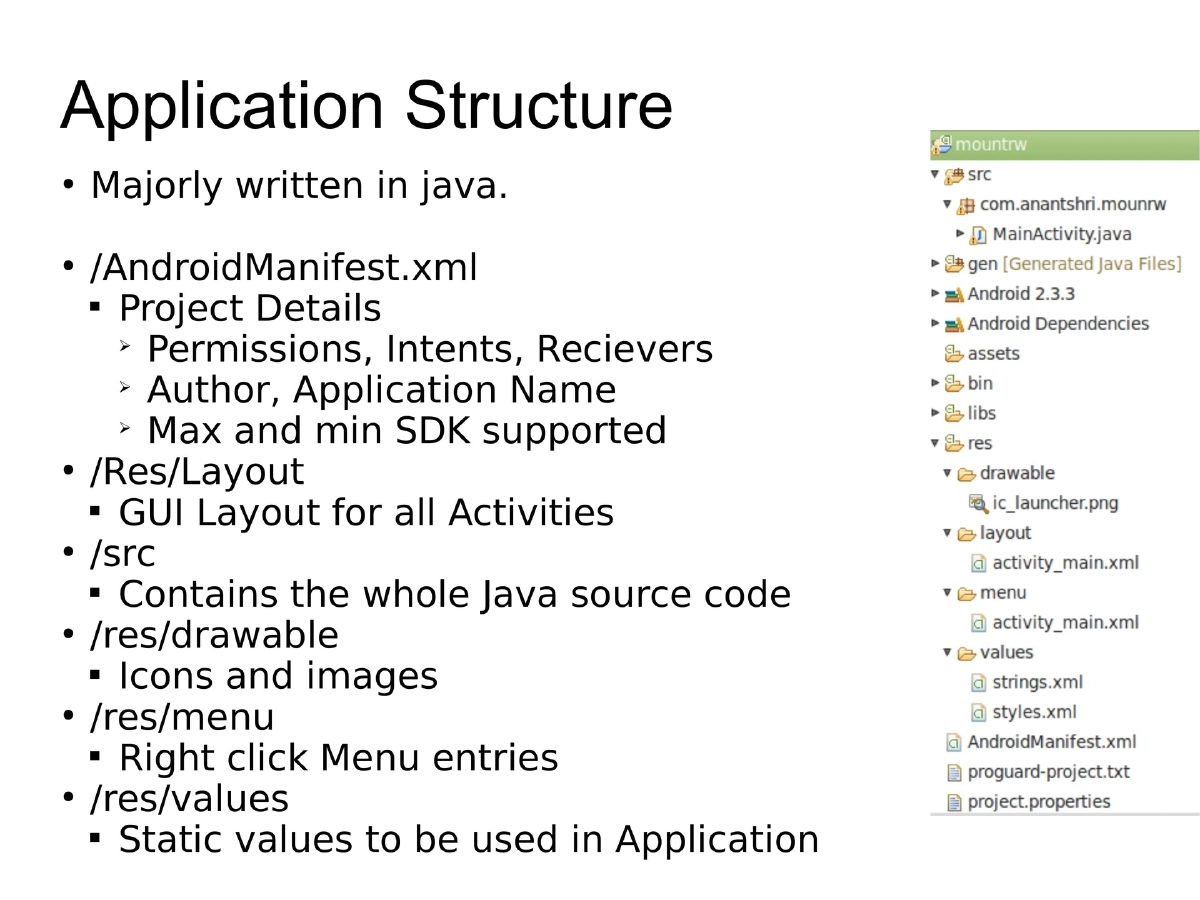
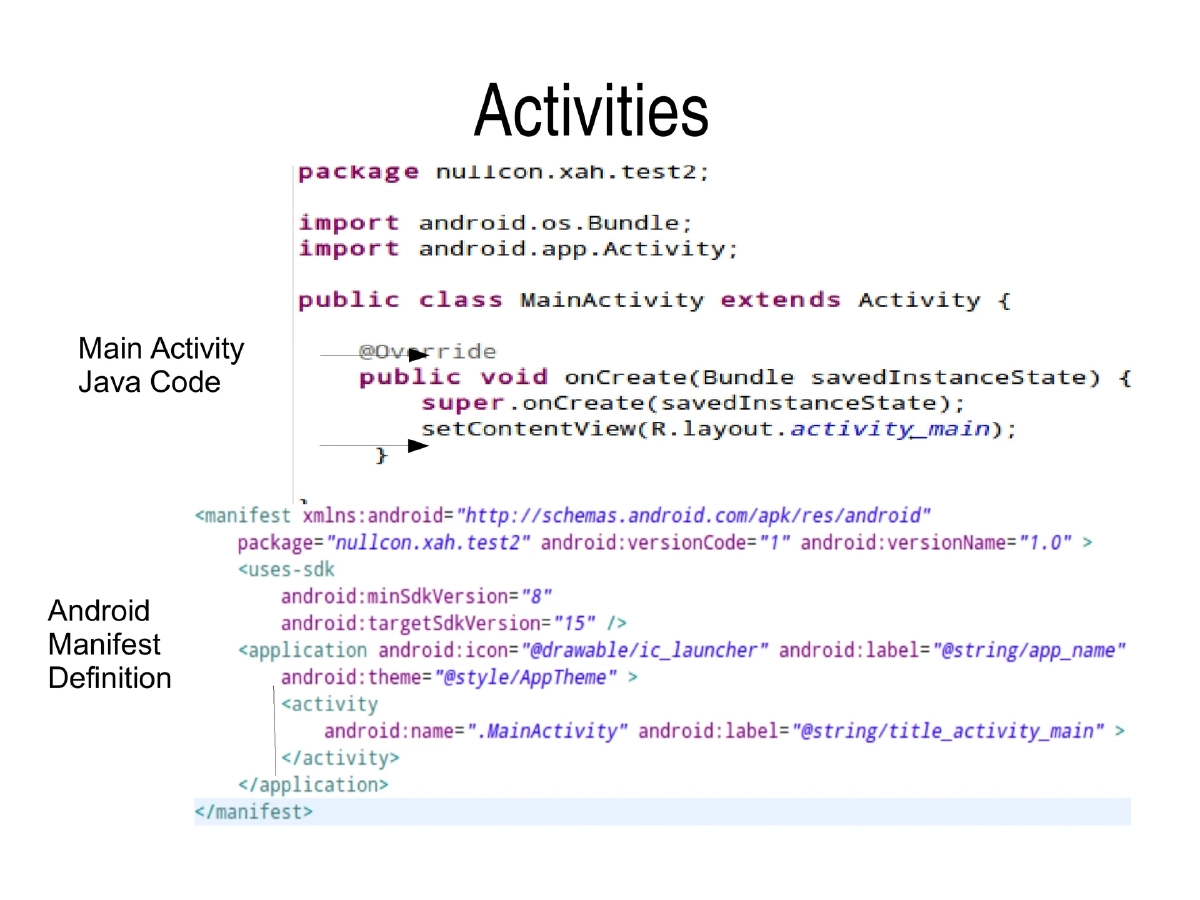
Application Architecture:
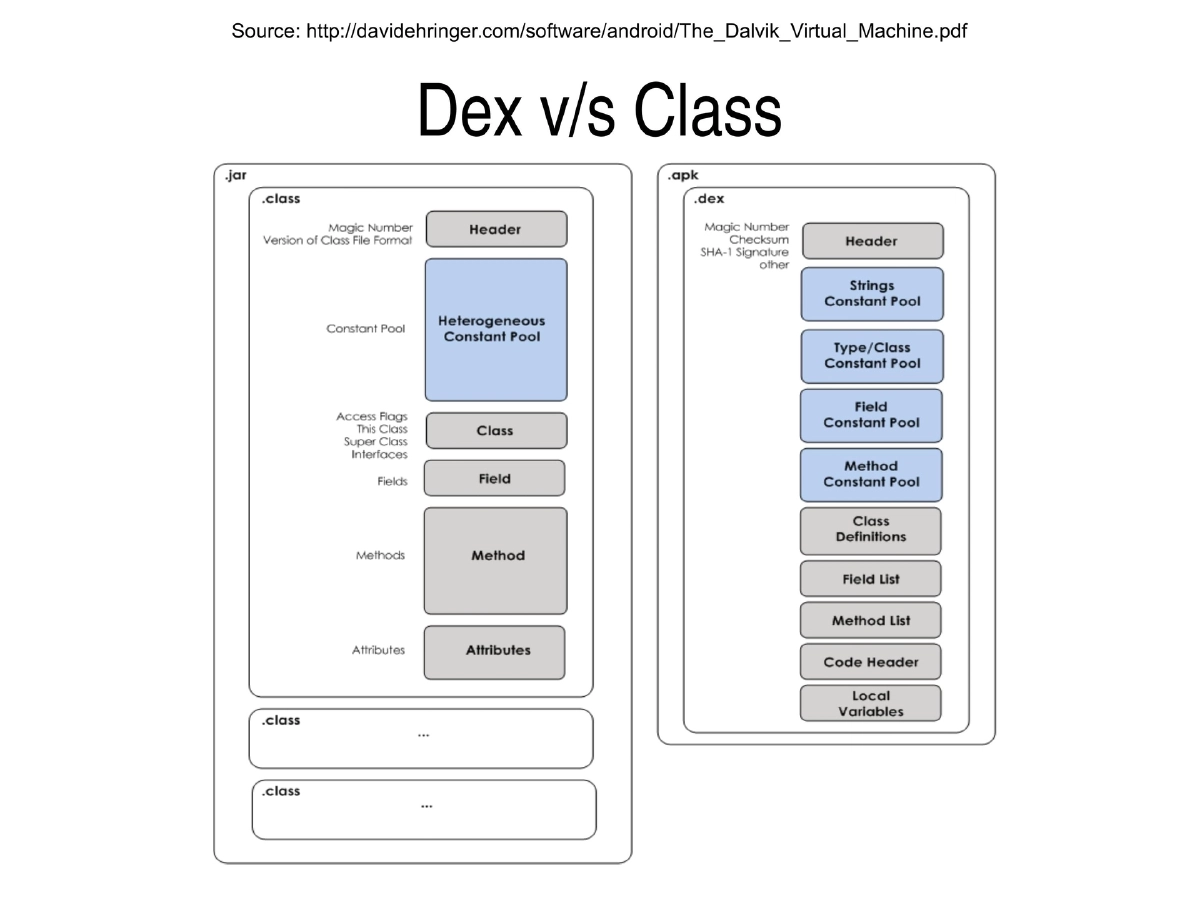
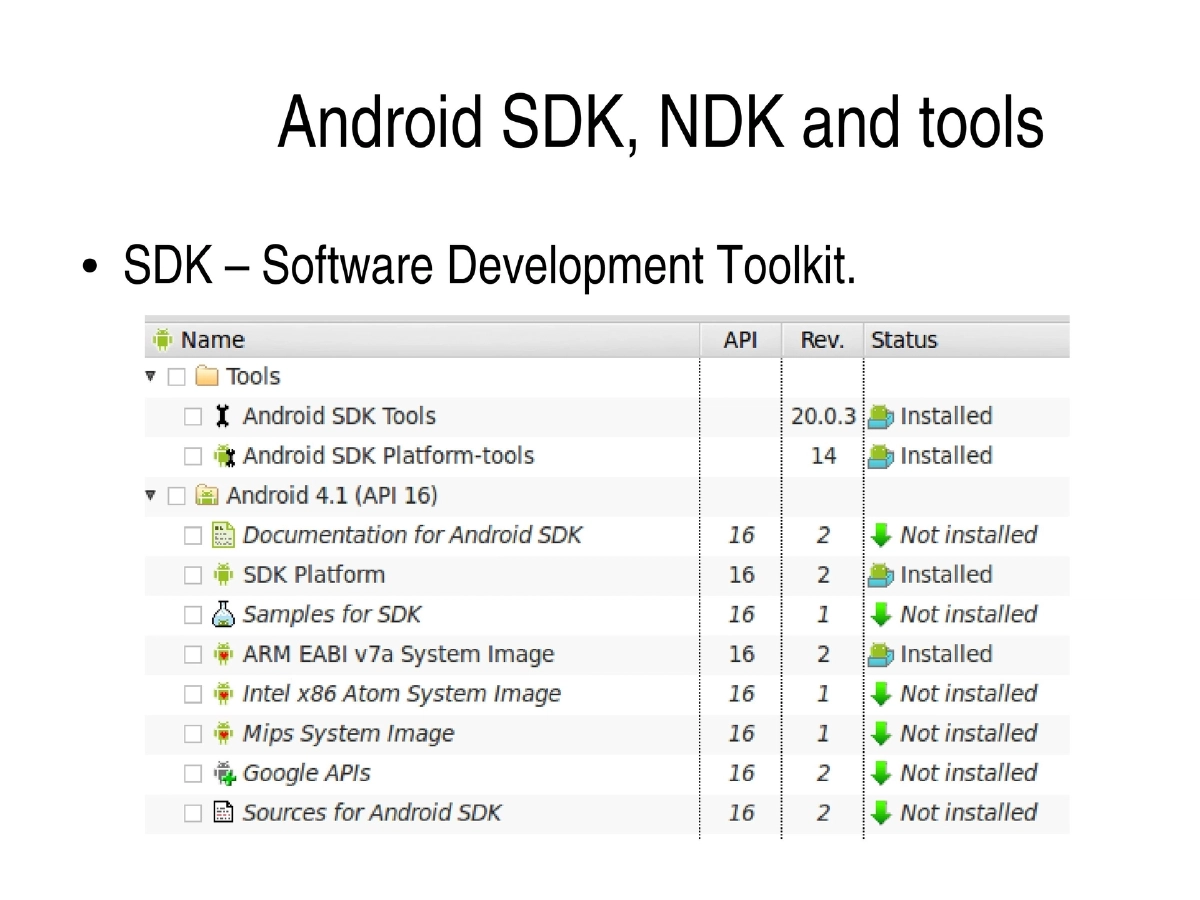
- Dalvik VM designed for memory-constrained devices; DEX format with optimized memory footprint
- Zygote process initializes core libraries at boot, forks VMs for each application
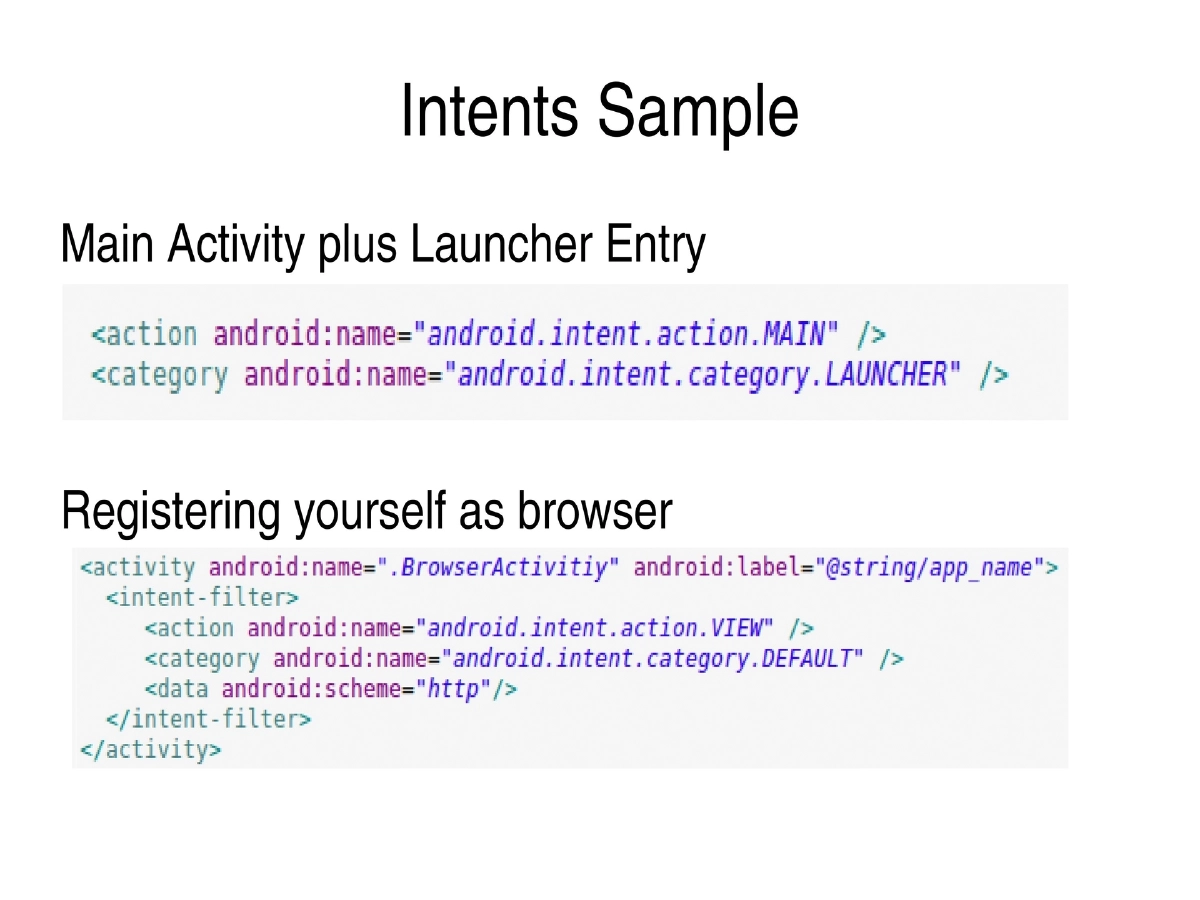
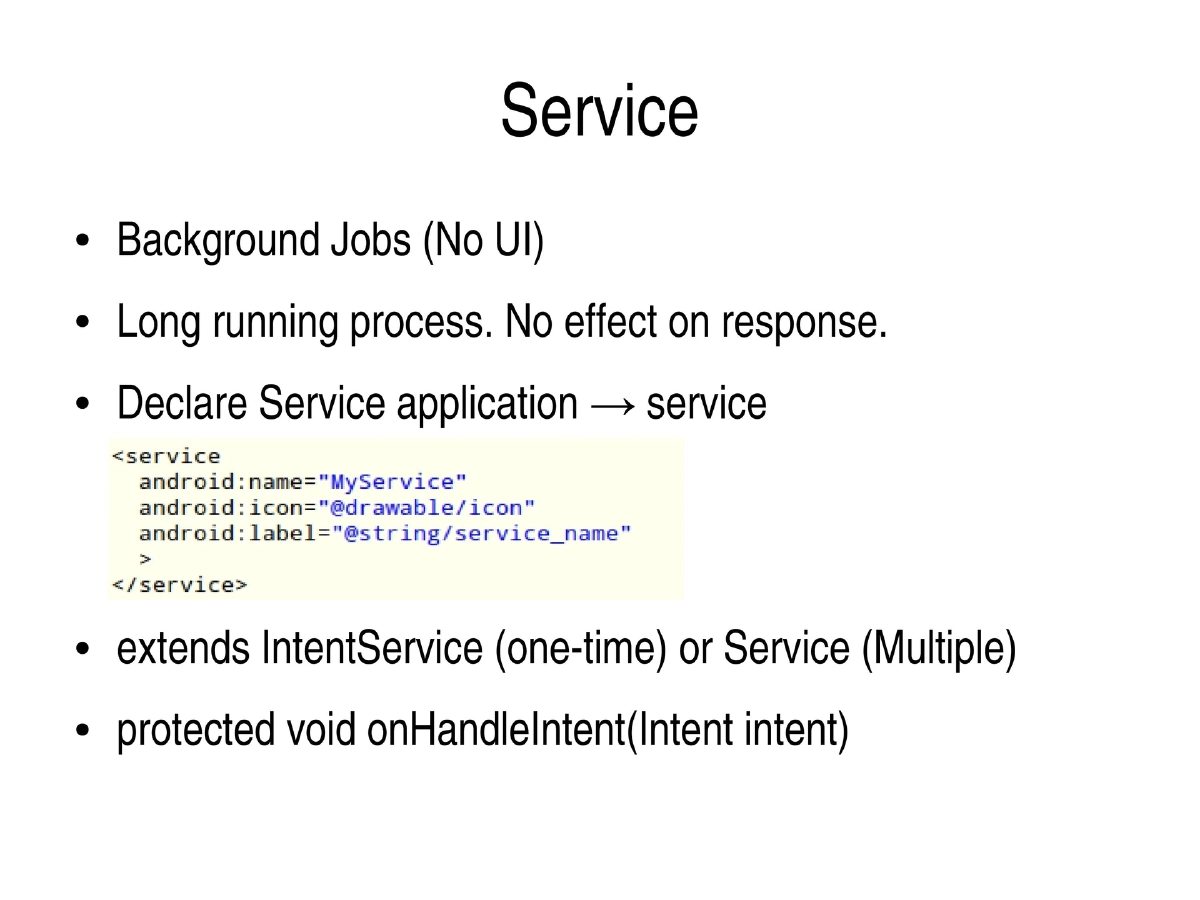
- Key components: Activities, Intents, Services, Content Providers, Broadcast Receivers
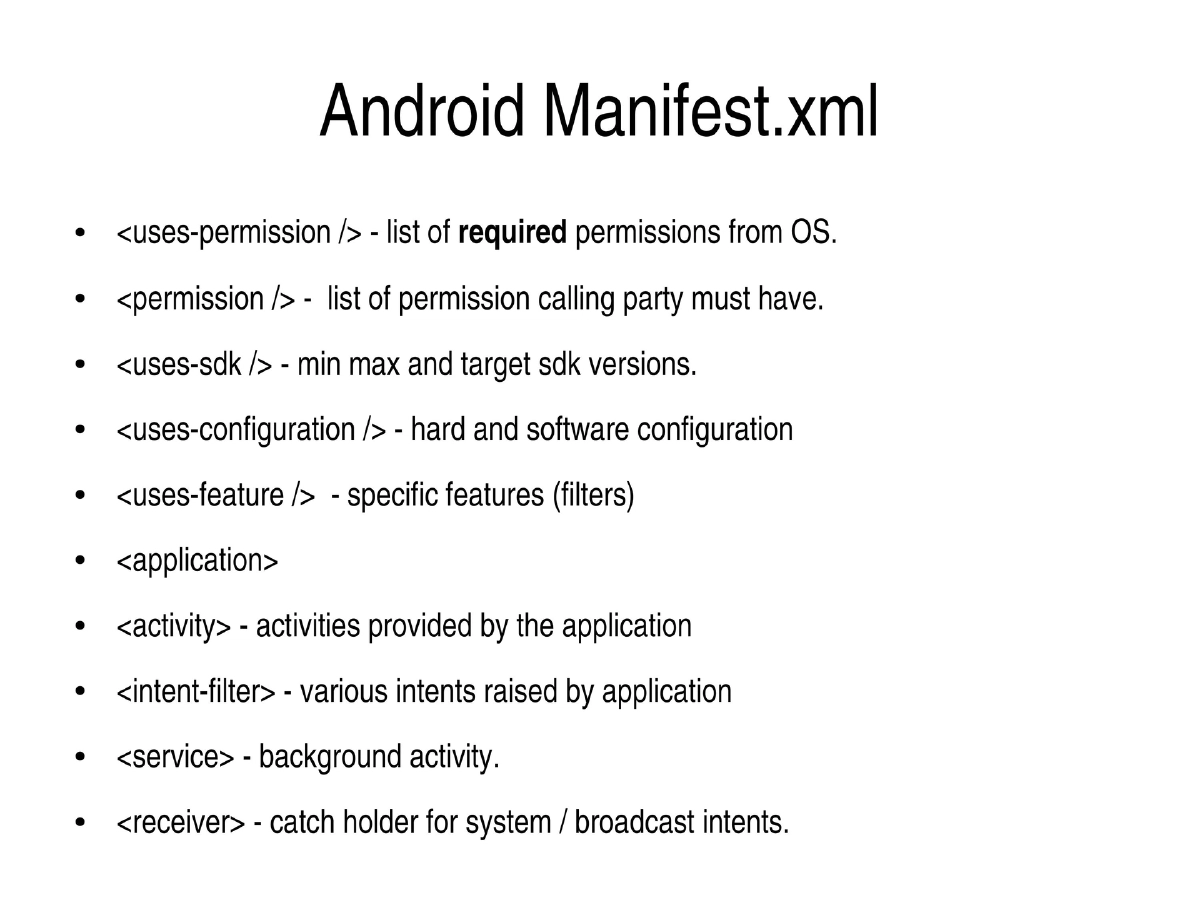
- AndroidManifest.xml defines permissions, intents, SDK versions, and component declarations
Android Tamer:
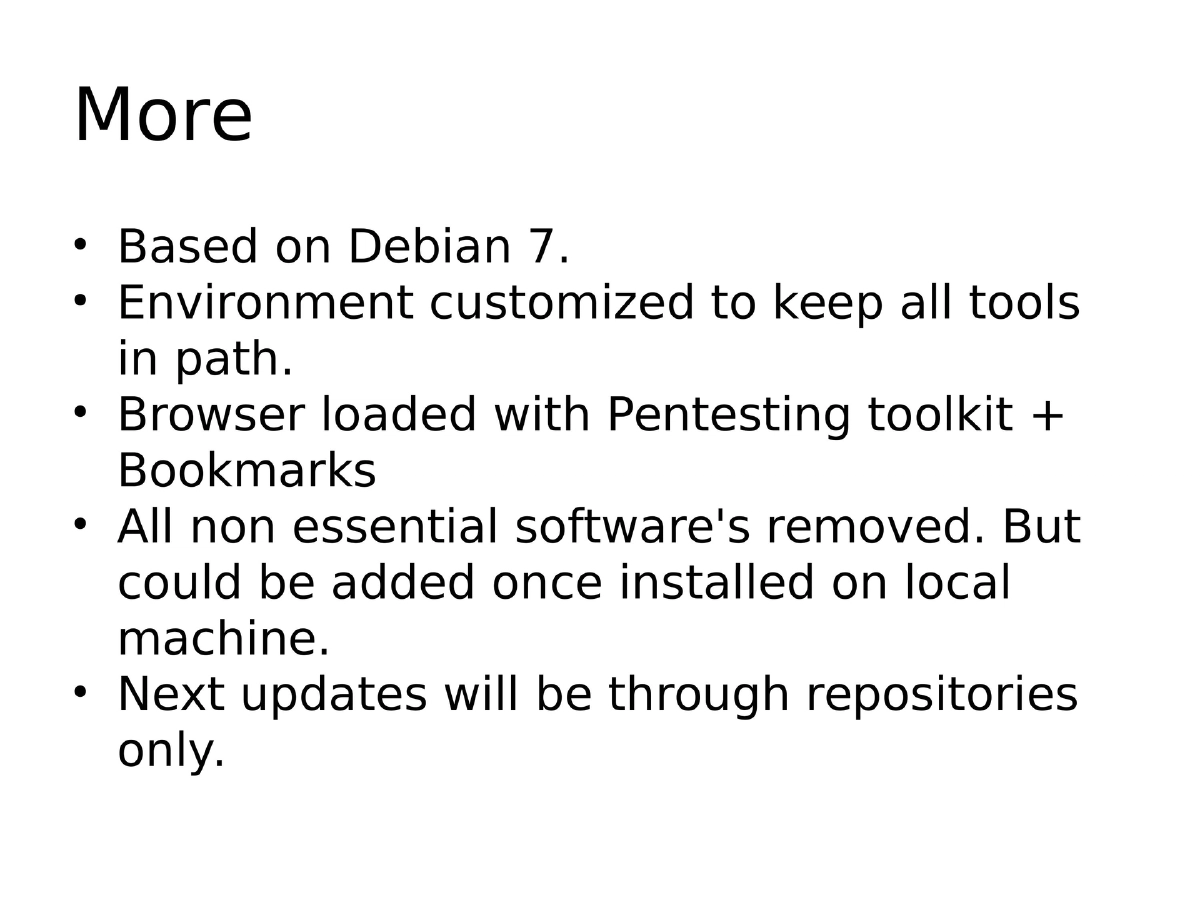
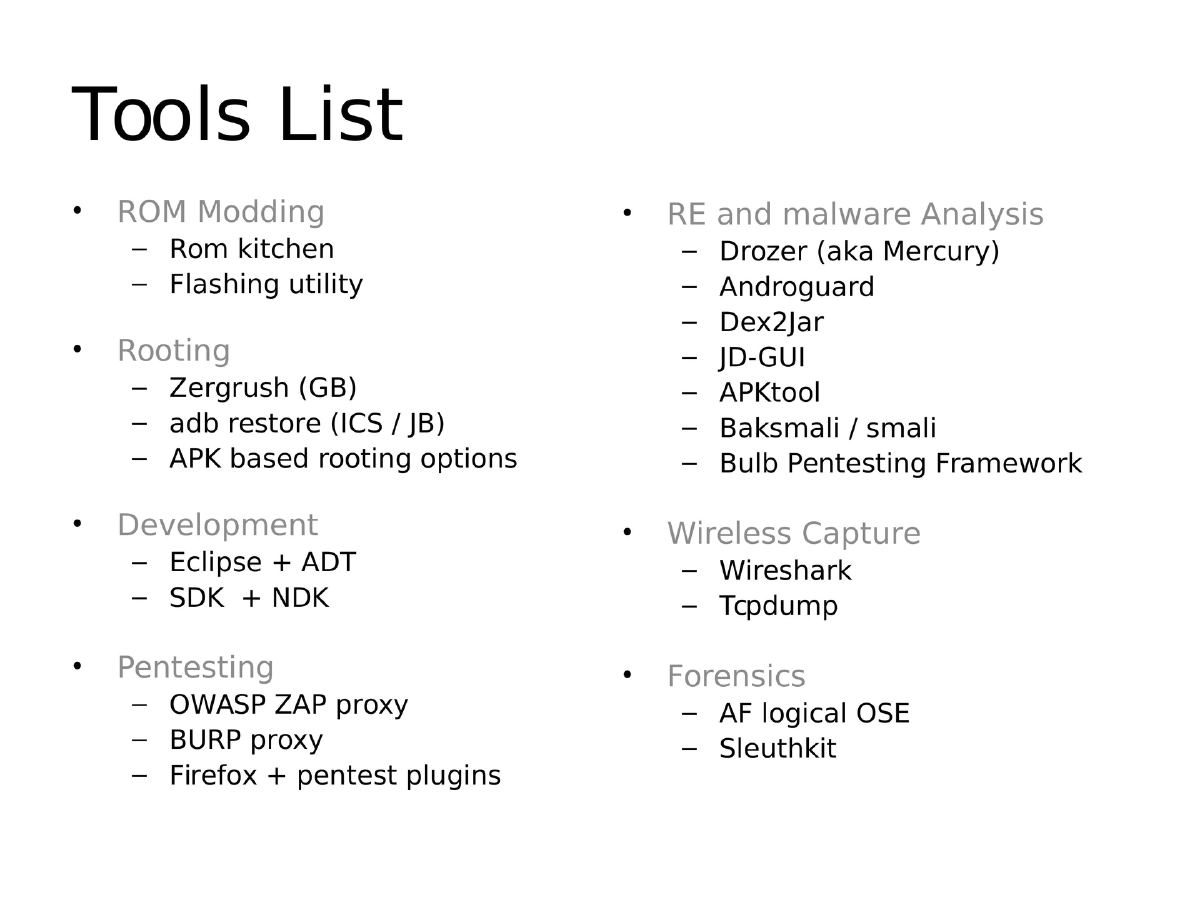
- VM/Live ISO environment for Android security (Debian 7 based)
- Comprehensive toolset: OWASP ZAP, Burp, Drozer, Androguard, Dex2Jar, JD-GUI, APKtool, Wireshark, AF Logical OSE, Sleuthkit
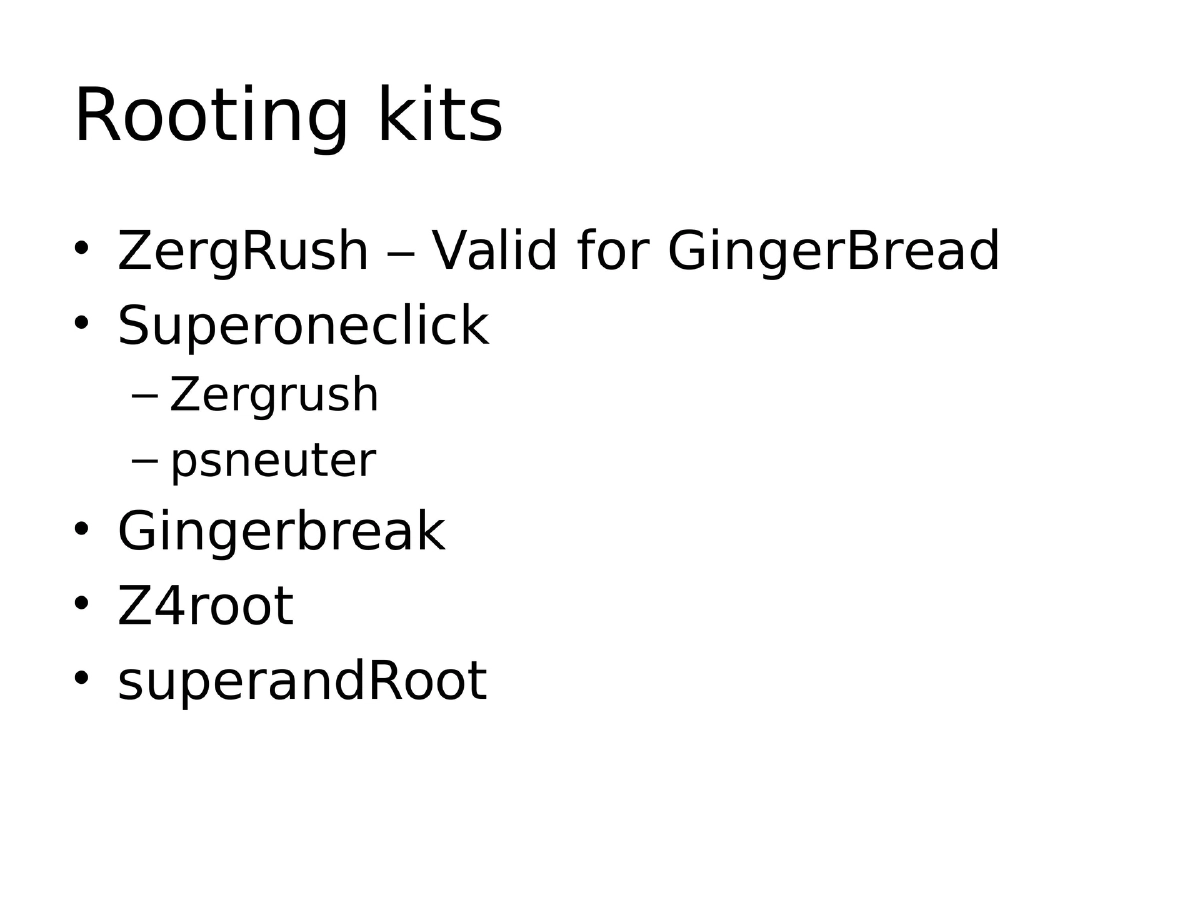
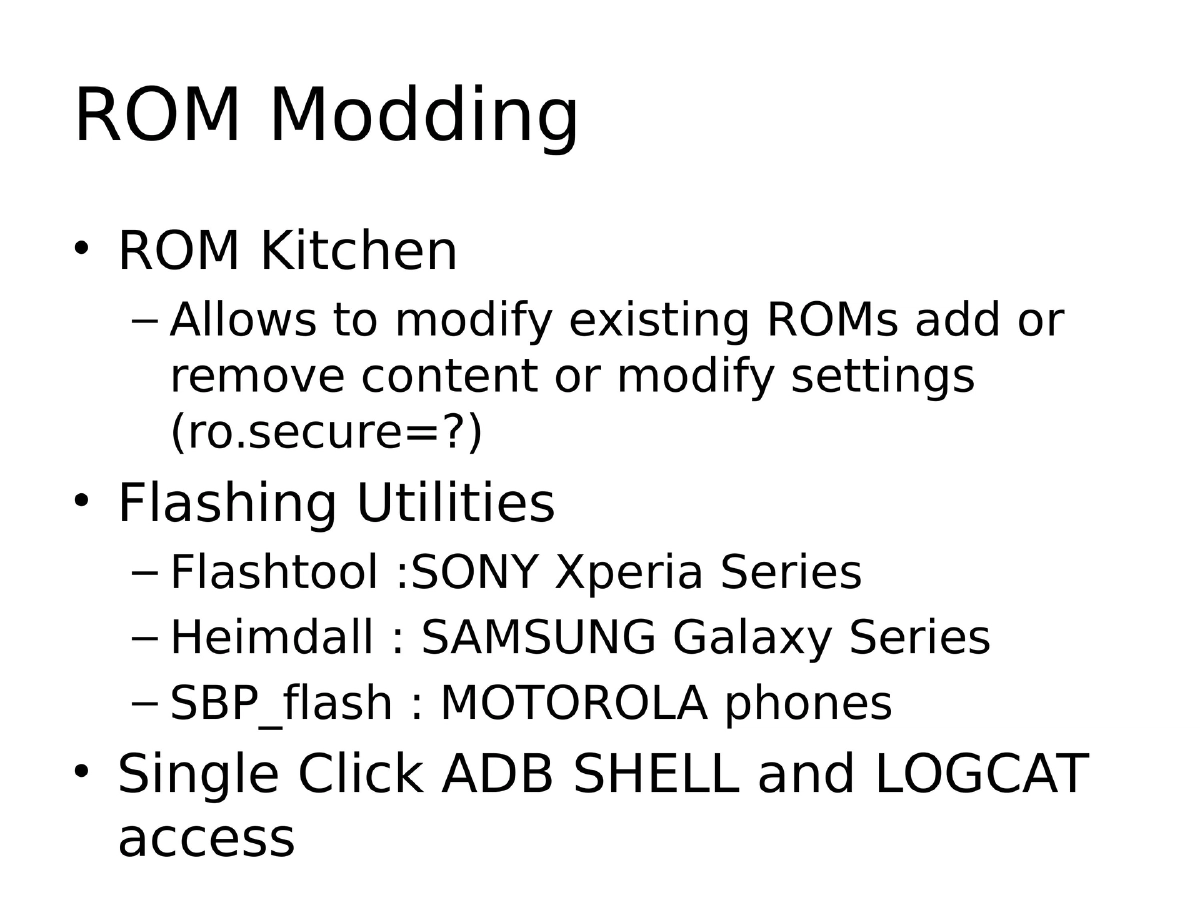
- ROM modding tools, flashing utilities, rooting kits
Mobile Security Issues:
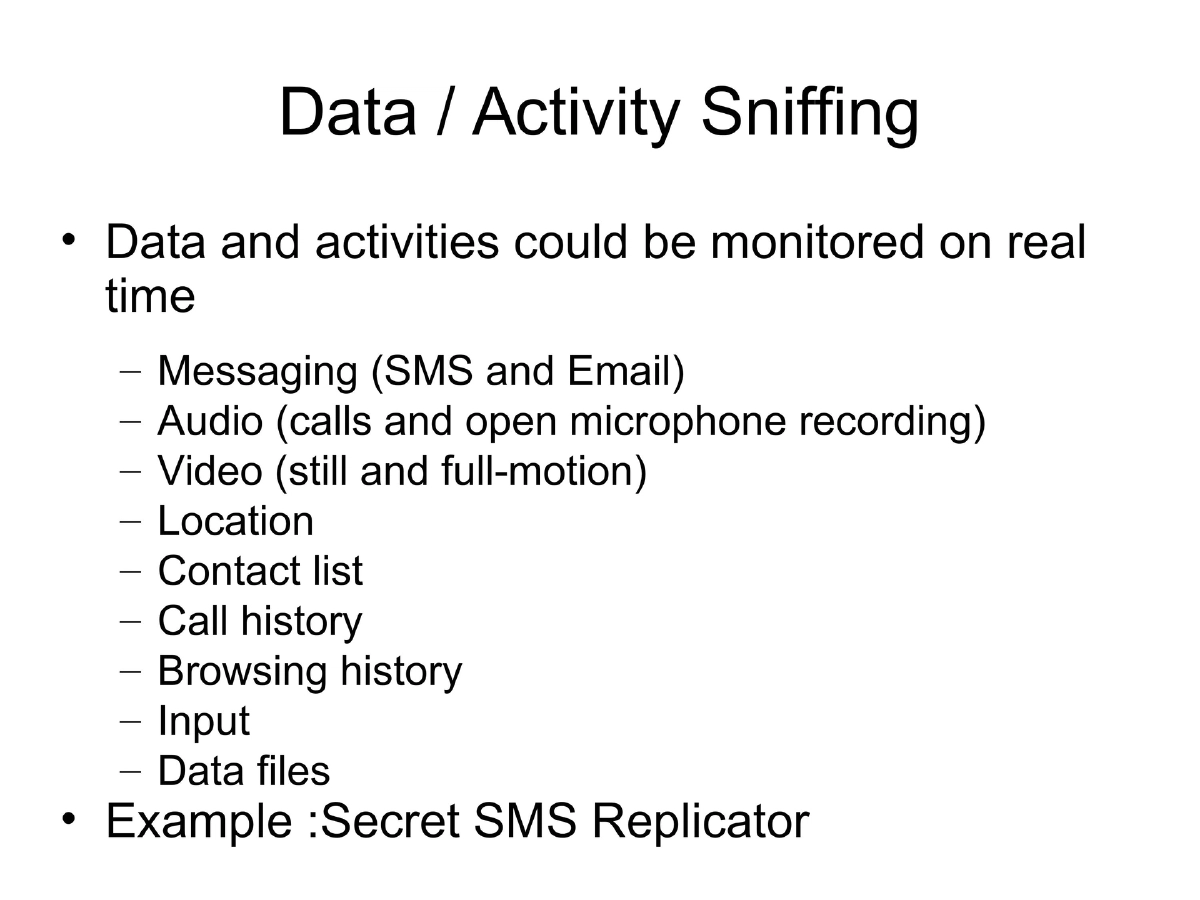
- Data sniffing (SMS, audio, video, location, contacts)
- Telephony abuse (premium SMS, USSD), unsafe data transit/storage
- Hardcoded credentials and API keys
- Side-channel leakage, information disclosure through reverse engineering
- Logic bombs, UI impersonation, SQL injection, tap jacking
Pentesting Methodology:
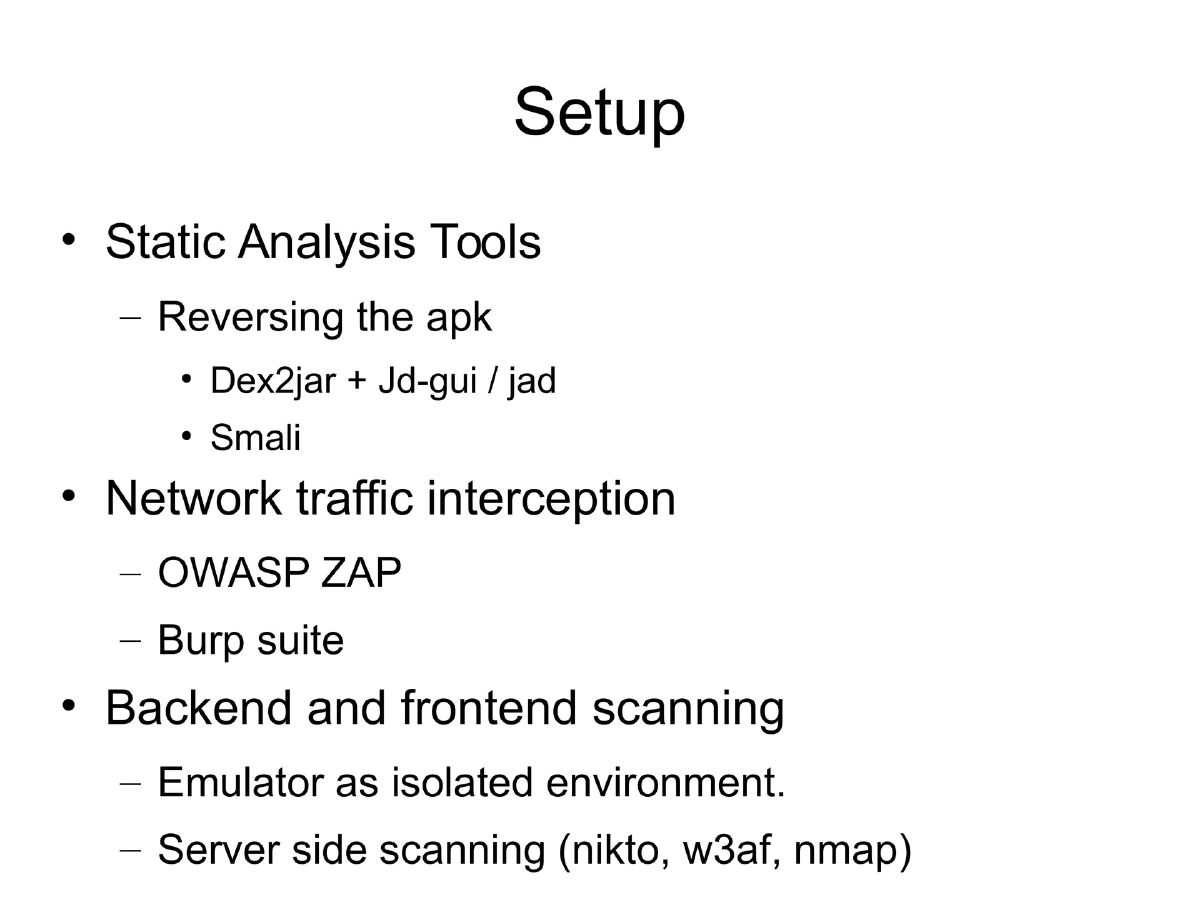
- Static analysis: Dex2jar + JD-GUI for decompilation, APKtool for resource extraction
- Dynamic analysis: Proxy setup, SSL certificate import, traffic interception
- IPTables-based per-app interception using unique Android UIDs
- Backend server scanning with nmap, w3af, nikto
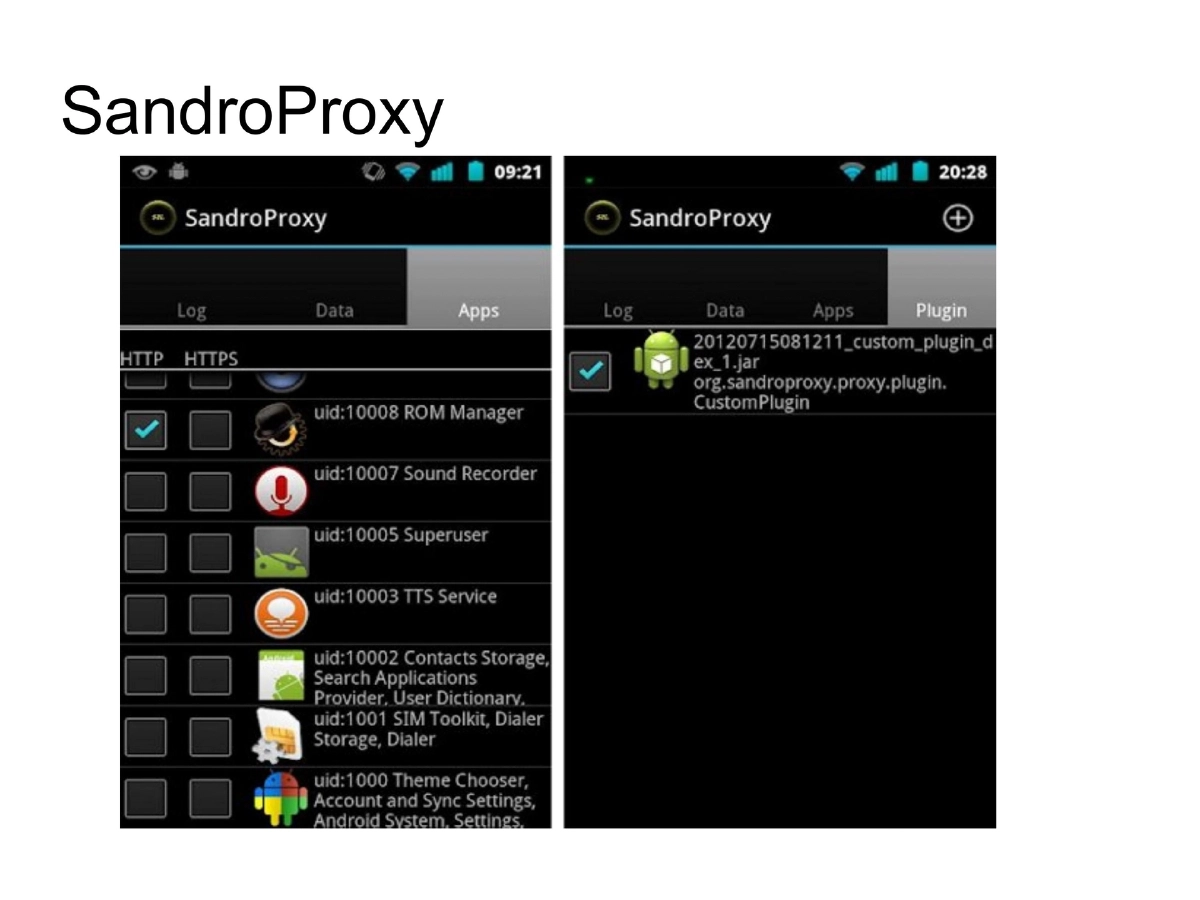
- SandroProxy for on-device traffic analysis
Using Android as a Pentesting Platform:
- Available tools: DroidSheep, Dsploit, Interceptor, zAnti
- Scripting via SL4A with Python/Perl
- Custom script development for brute force, enumeration, and automation
Actionable Takeaways
- Understanding Android internals (Dalvik, Zygote, permissions) is foundational for security testing
- Multiple decompilation paths exist for different analysis needs
- SSL interception requires certificate installation on the testing device
- Per-app UID architecture enables granular network monitoring via IPTables
- Android devices serve dual purpose as both testing targets and portable pentesting platforms