Snake Bytes C0c0n
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation introduces Python as a practical scripting language for web penetration testers, covering essential modules, demonstrating real-world security tool development, and showcasing Python’s integration with existing security tools.
Key Topics Covered
Why Python for Pentesting:
- Easy, flexible language with massive module ecosystem
- Built-in scripting support in tools like Burp and IRONWASP
- API support from OWASP ZAP
- Enables custom application logic and rapid tool development
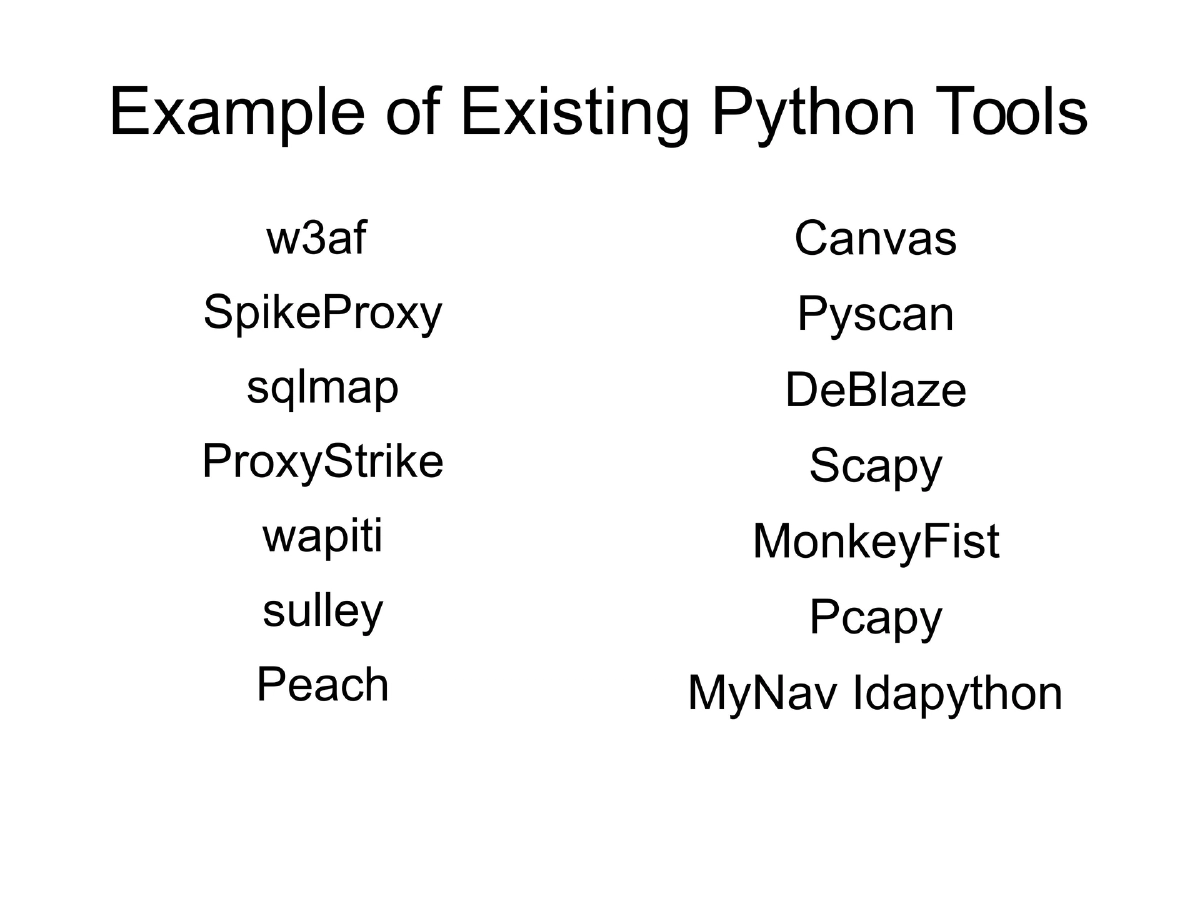
- Large existing toolbase: w3af, sqlmap, Scapy, Canvas, Sulley, Peach, and many more
Python Variations:
- CPython, Jython, IronPython
- Important distinction between Python 2.x and 3.x
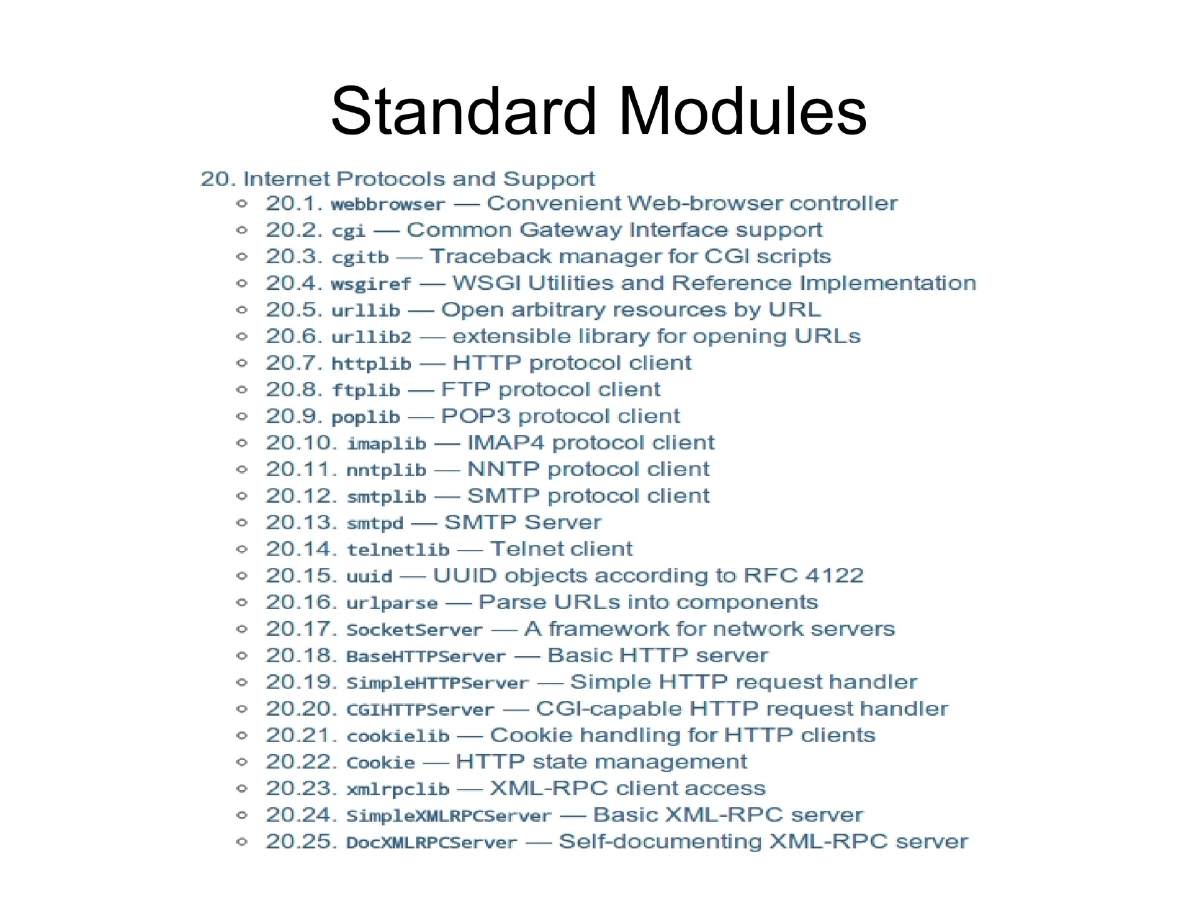
Essential Modules for Pentesters:
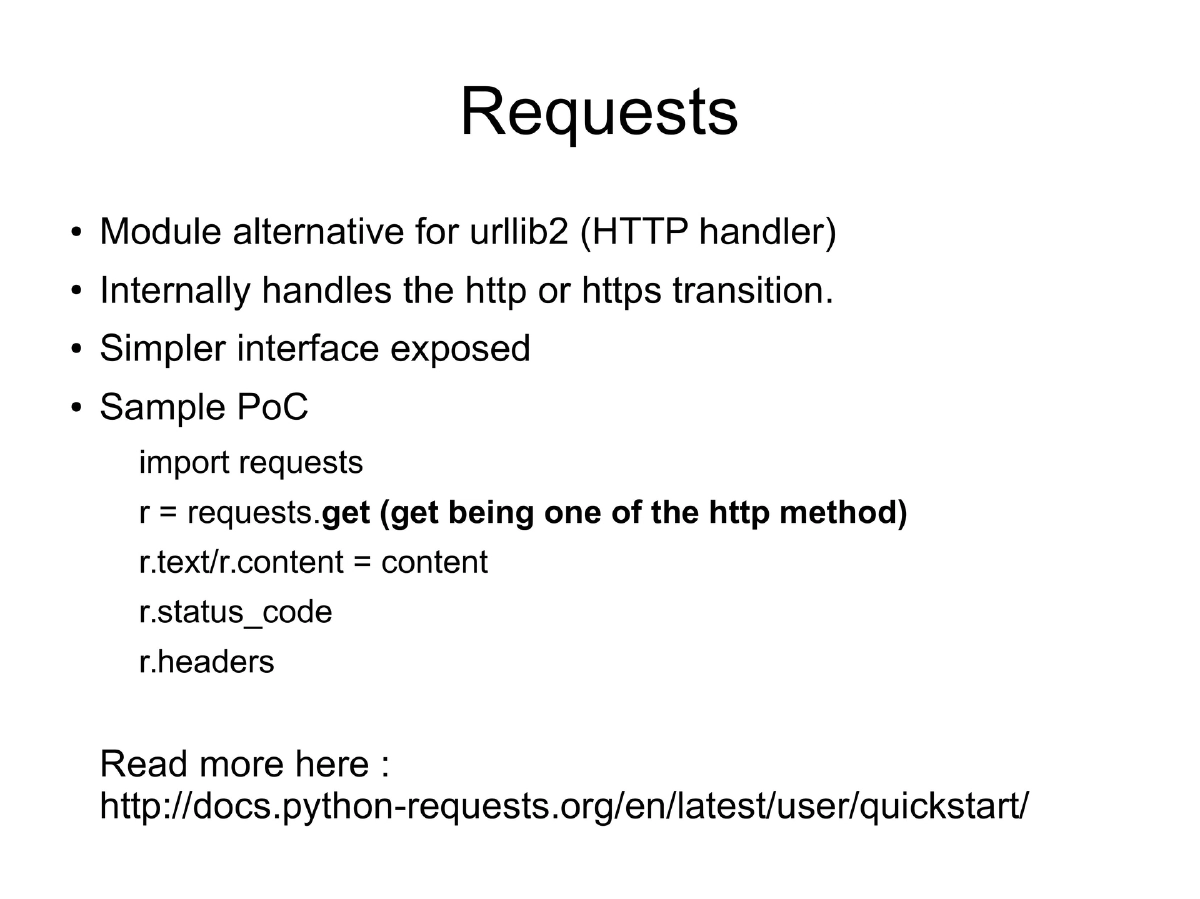
Requests:
- Alternative to urllib2 for HTTP handling
- Internally handles HTTP/HTTPS transitions
- Simple interface: requests.get(), r.text, r.status_code, r.headers
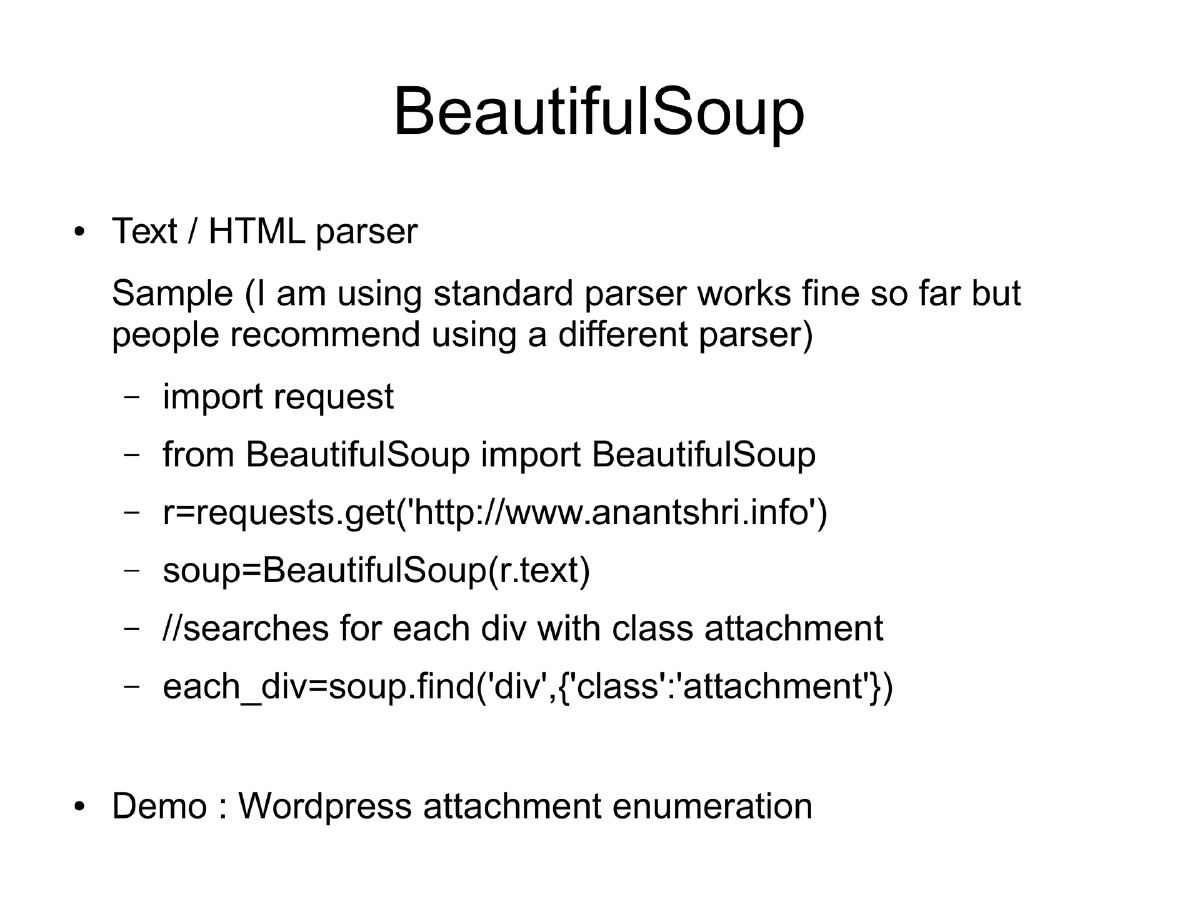
BeautifulSoup:
- HTML/text parser for extracting data from web responses
- Useful for finding specific elements by tag, class, or ID
- Demonstrated with WordPress attachment enumeration
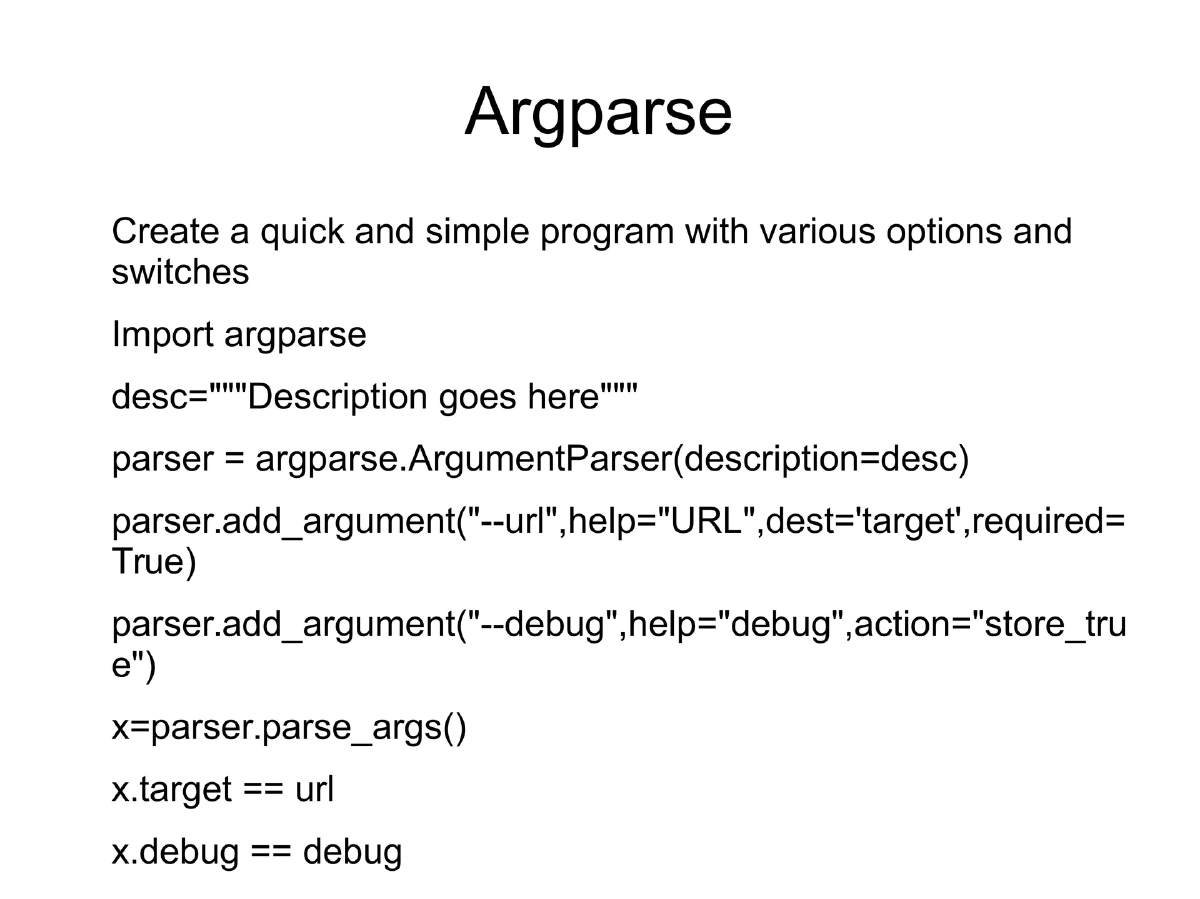
Argparse:
- Creates command-line tools with switches and options
- Supports required arguments, boolean flags, and help text
Practical Demonstrations:
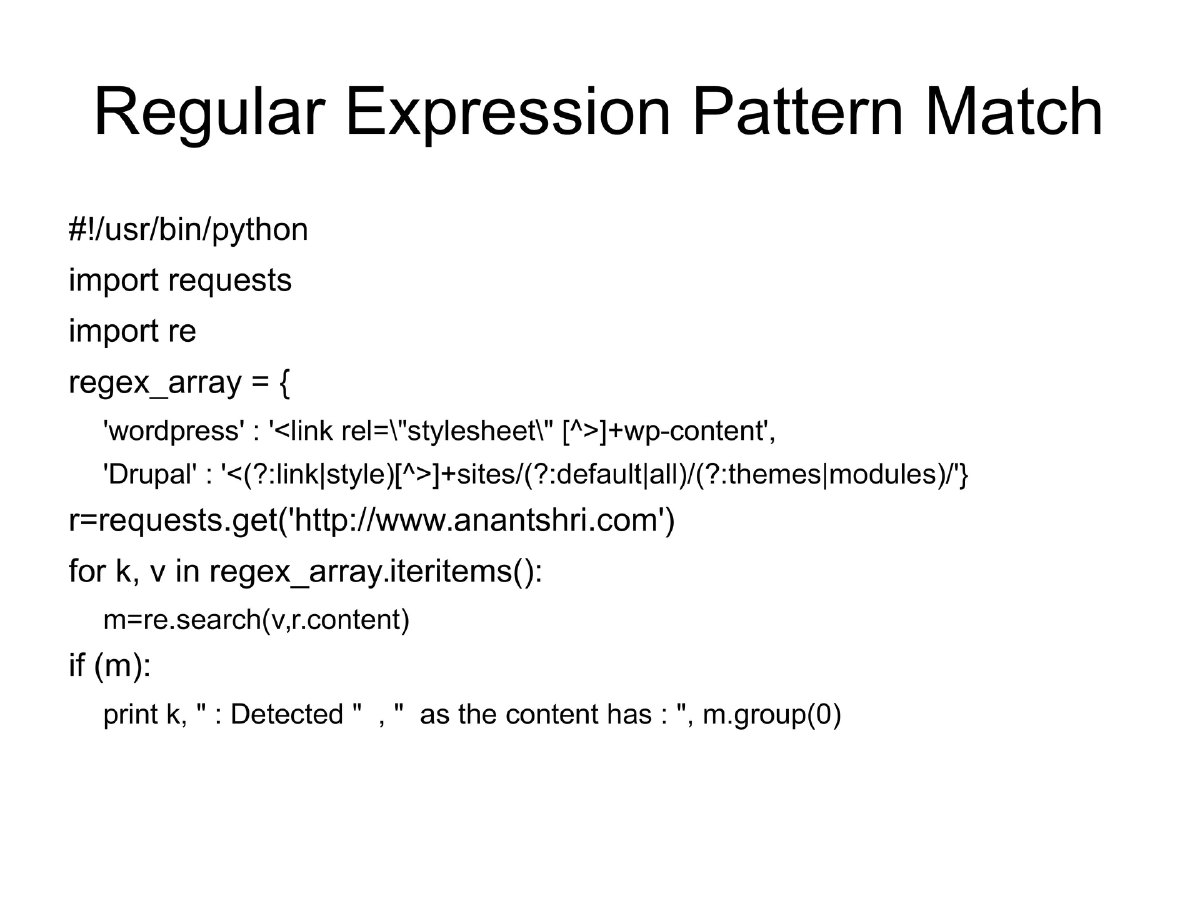
Regular Expression Pattern Matching:
- CMS fingerprinting using regex patterns against page content
- Identifying WordPress (wp-content in stylesheets) and Drupal (sites/default/themes patterns)
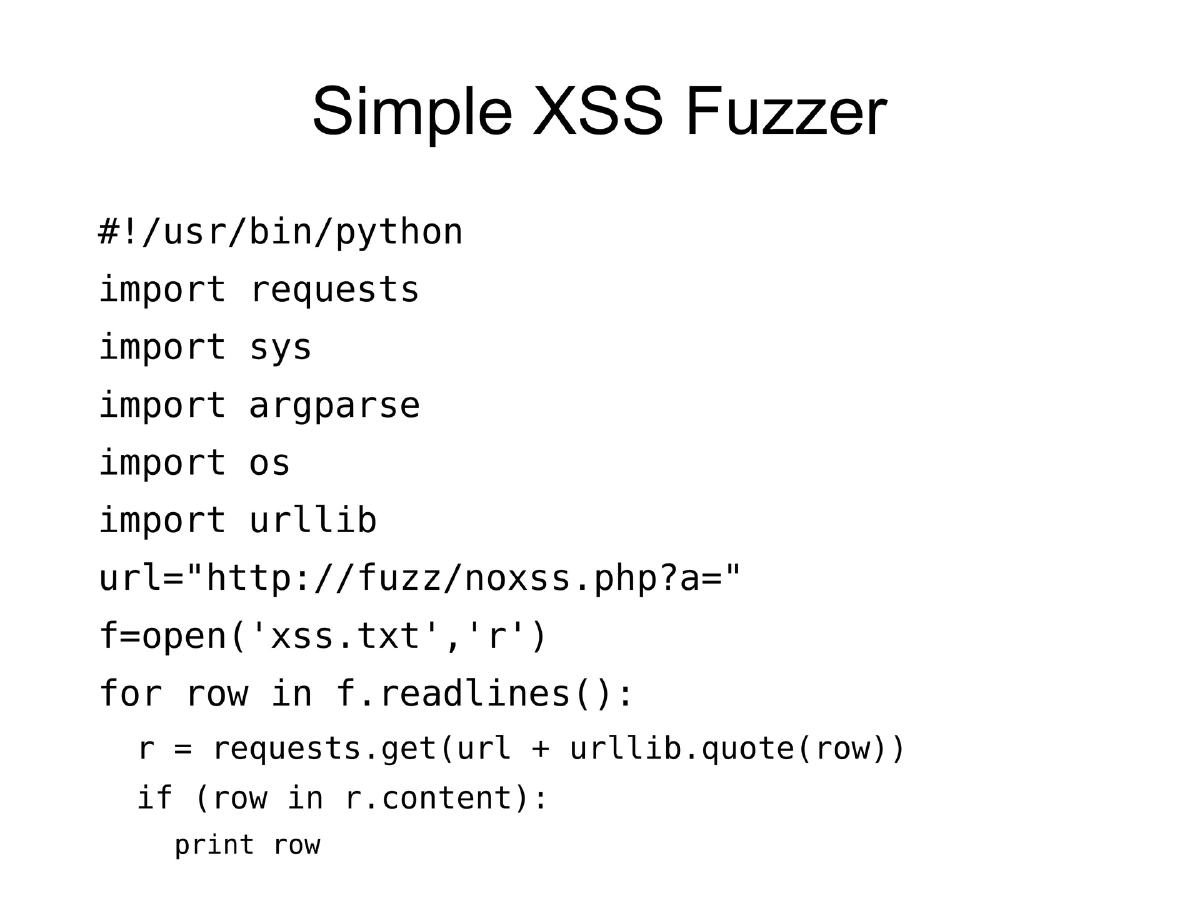
Simple XSS Fuzzer:
- Reads XSS payloads from file, injects into URL parameters
- Checks if payload reflects in response to identify XSS vulnerabilities
SVN Extractor:
- Tool to extract web resources from exposed .SVN folders
- Published at github.com/anantshri/svn-extractor
Distribution and Packaging:
- PyInstaller packages Python scripts with all dependencies into standalone executables
- Python for Android via SL4A enables running Python scripts on mobile devices
Learning Resources:
- Learn Python the Hard Way, Dive into Python
- SPSE certification courses
- Violent Python, Grey-hat Python
- Practice with IRONWASP inline scripting and Burp extensions
Actionable Takeaways
- Python’s requests and BeautifulSoup modules form the foundation for web security tools
- Regex-based fingerprinting can identify CMS platforms and technologies
- Custom fuzzers can be built in minimal code using Python’s HTTP libraries
- Exposed version control systems (.svn) are a common finding that Python automates exploiting
- PyInstaller enables distributing Python tools to team members without Python dependency