Deep Dive Android Cocon
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This comprehensive training workshop at c0c0n 2013 provides a deep dive into Android security, covering the platform architecture, application development, Android Tamer toolkit, mobile security issues, penetration testing methodology, and using Android devices as pentesting platforms.
Key Topics Covered
Android Platform Overview:
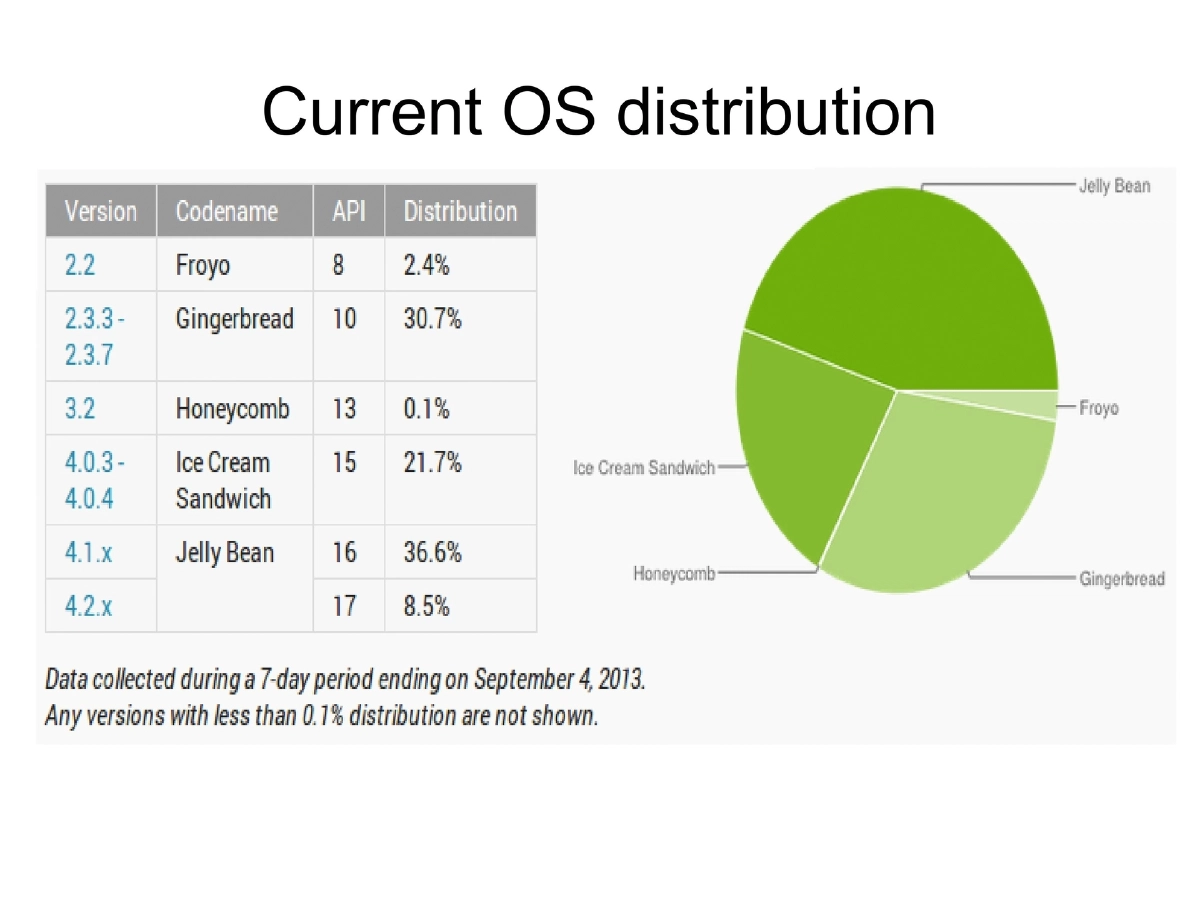
- 56% smartphone market share (Gartner May 2012), open source, minimal developer license cost ($25)
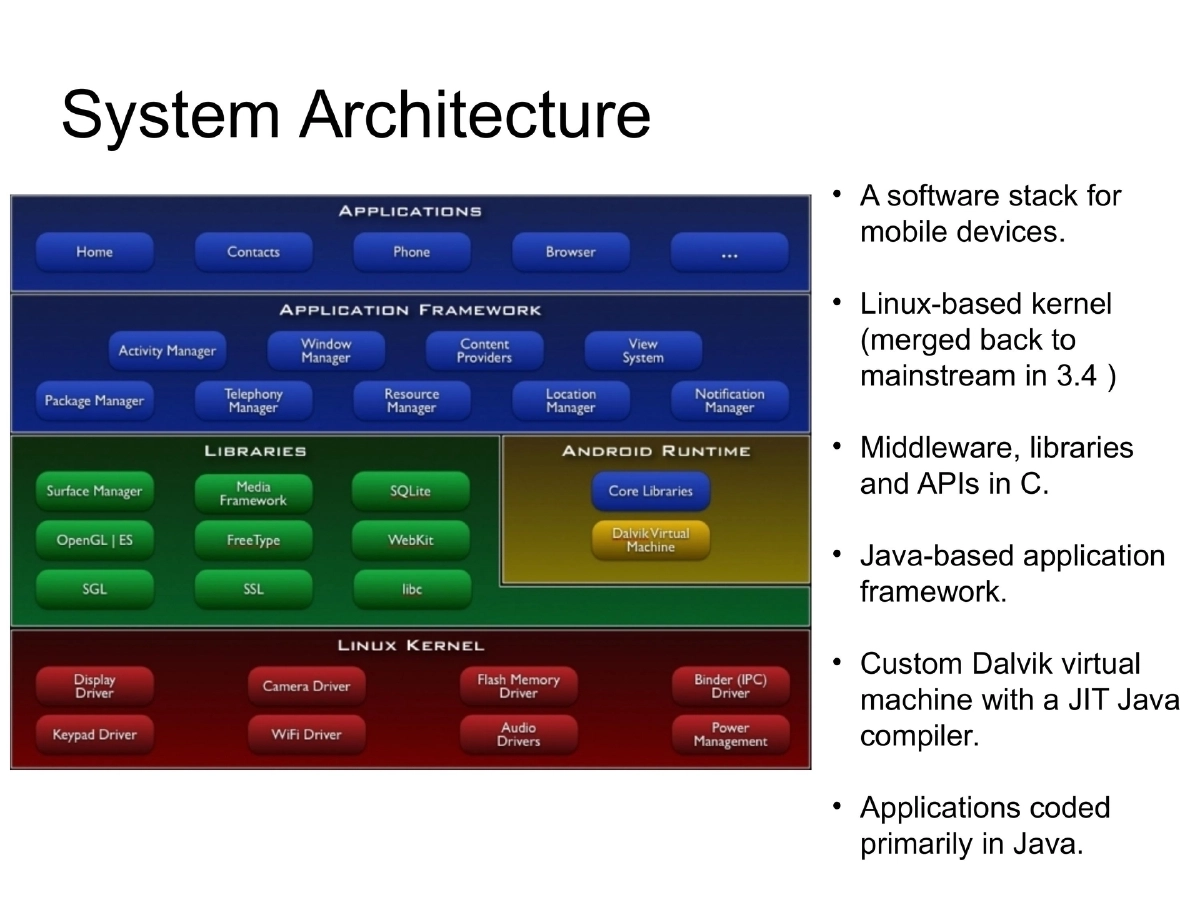
- Architecture: Linux kernel (merged back to mainstream in 3.4), C middleware, Java framework, Dalvik VM
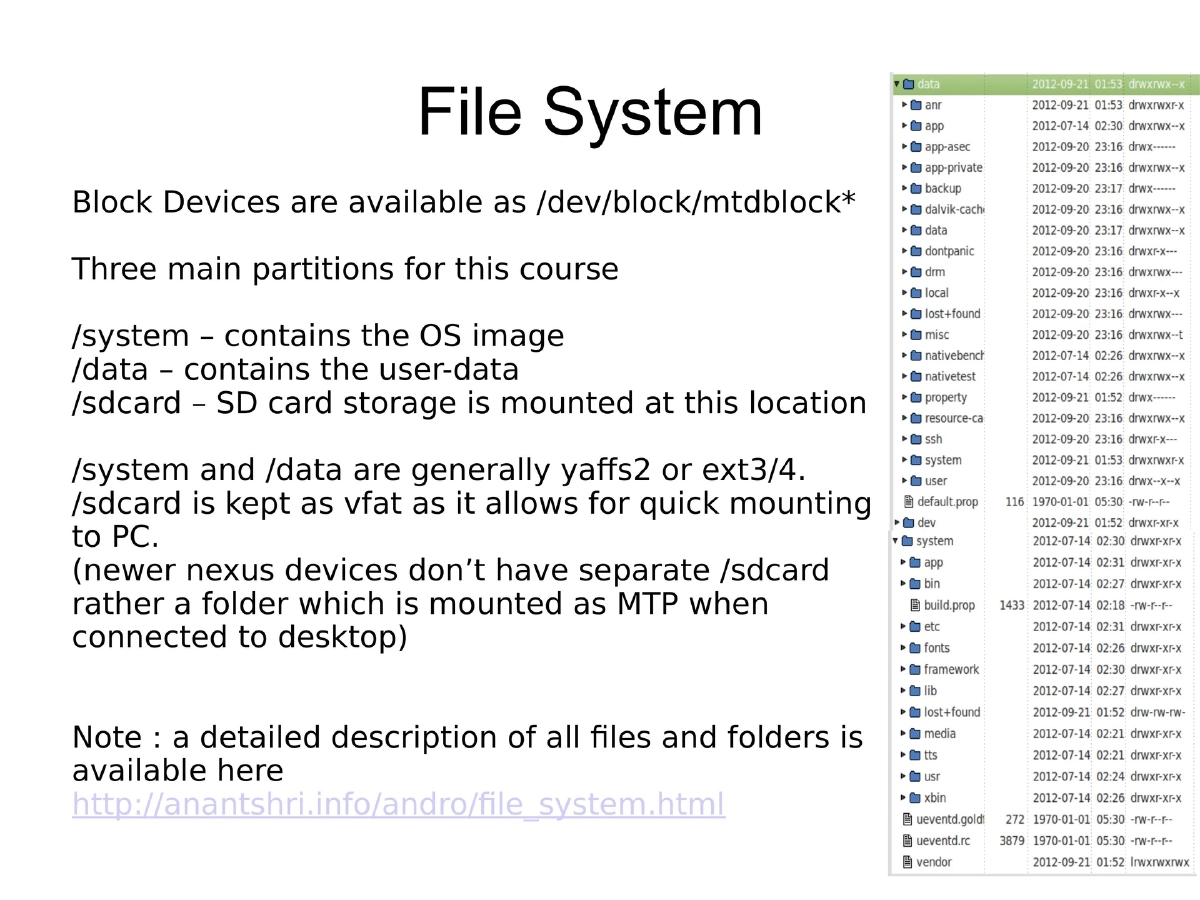
- Key partitions: /system (OS, yaffs2/ext3/4), /data (user data), /sdcard (vfat for PC compatibility)
Security Model:
- Unix permission-based restrictions with SELinux (4.3 onwards, permissive; enforced in 4.4)
- Application sandboxing with unique UIDs per app
- Permission model requiring first-time approval
- AppOps (hidden feature) for fine-tuning permission control
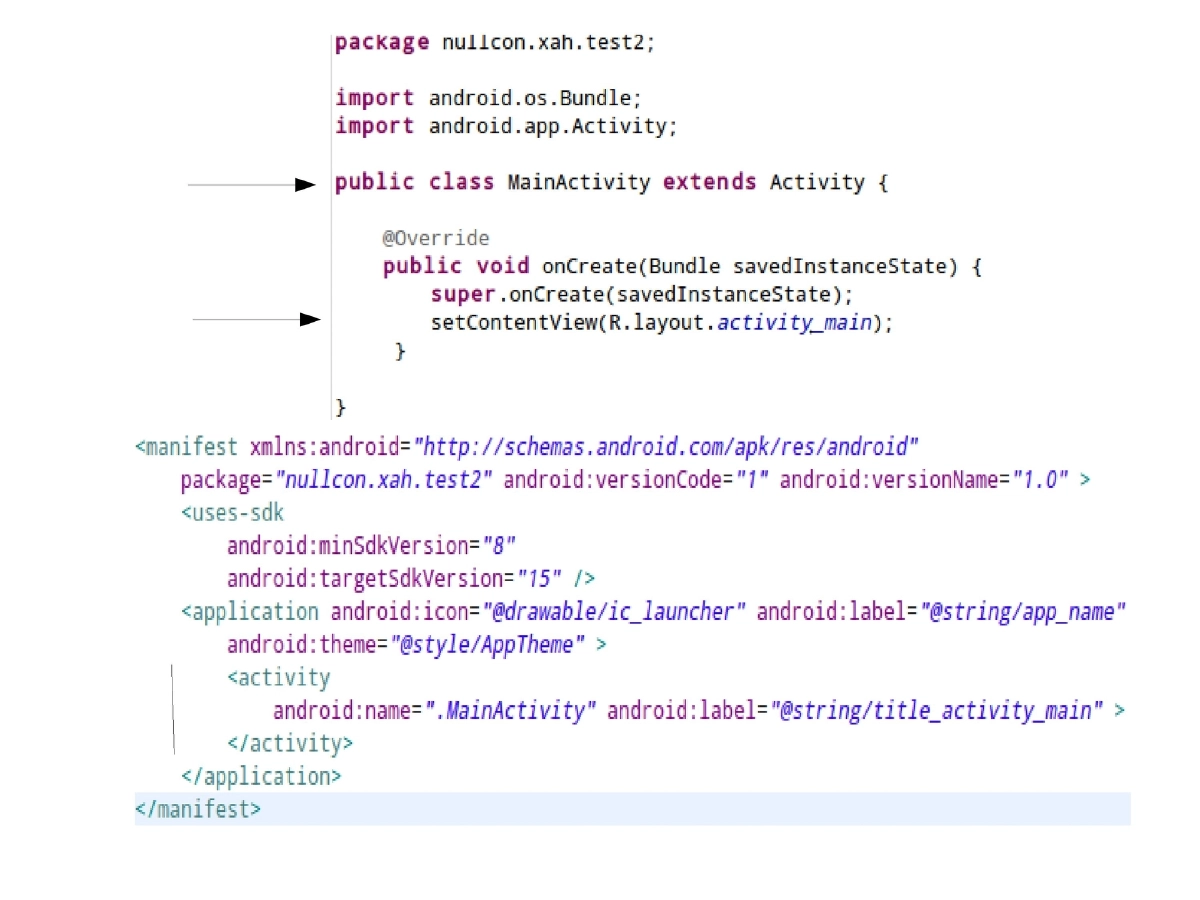
Application Architecture:
- Dalvik Virtual Machine: register-based (vs. Java’s stack-based), optimized for memory and performance constraints
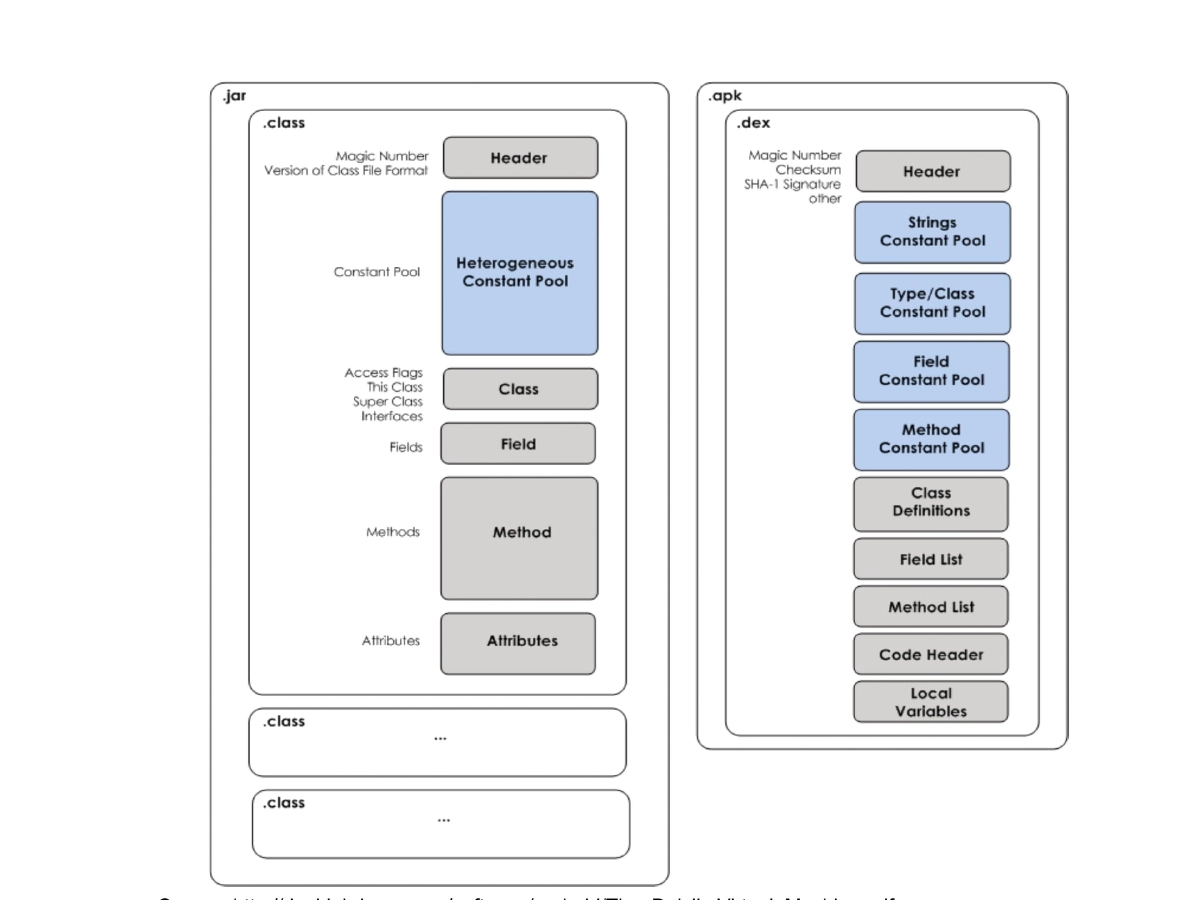
- DEX format: multiple classes per file, shared type-specific constant pools for minimal memory footprint
- Zygote process: boots at startup, initializes core libraries, forks new VM instances for each app
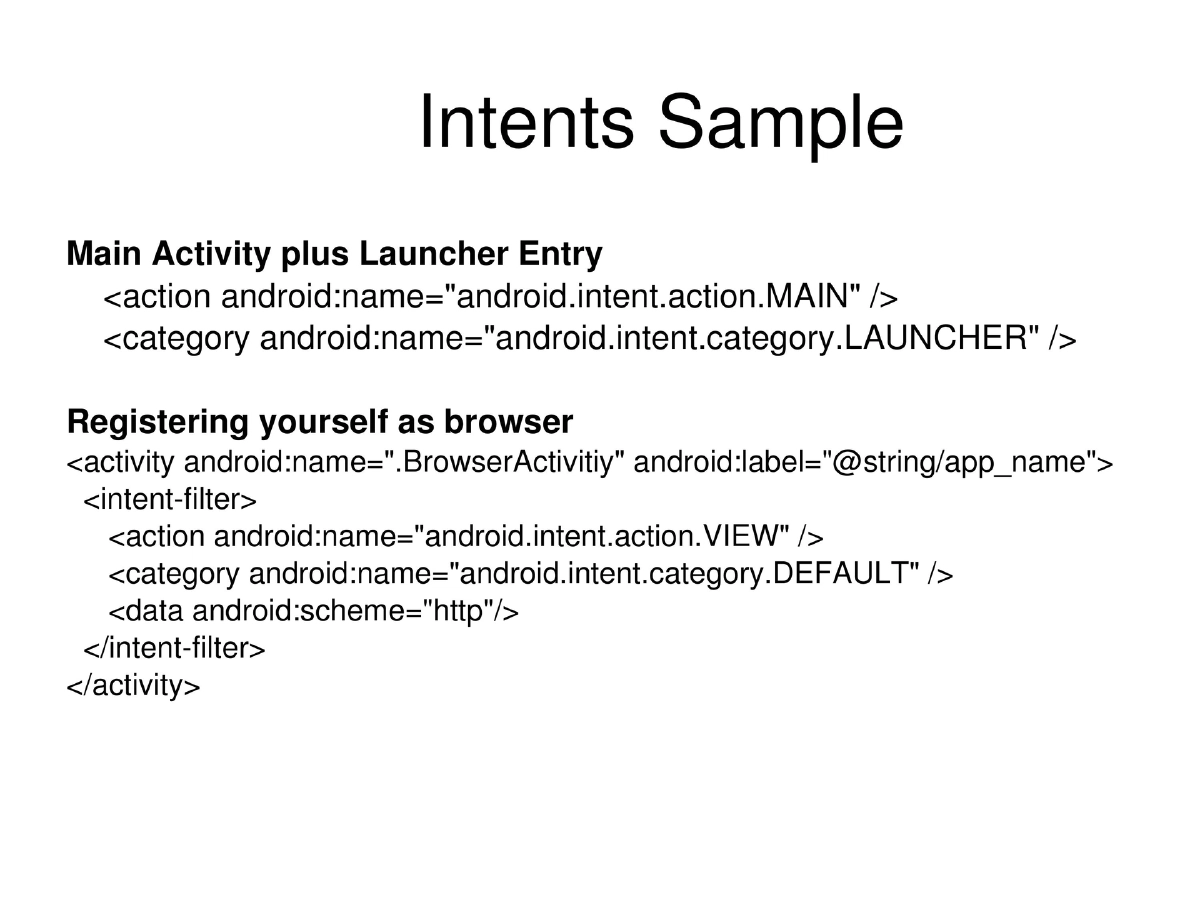
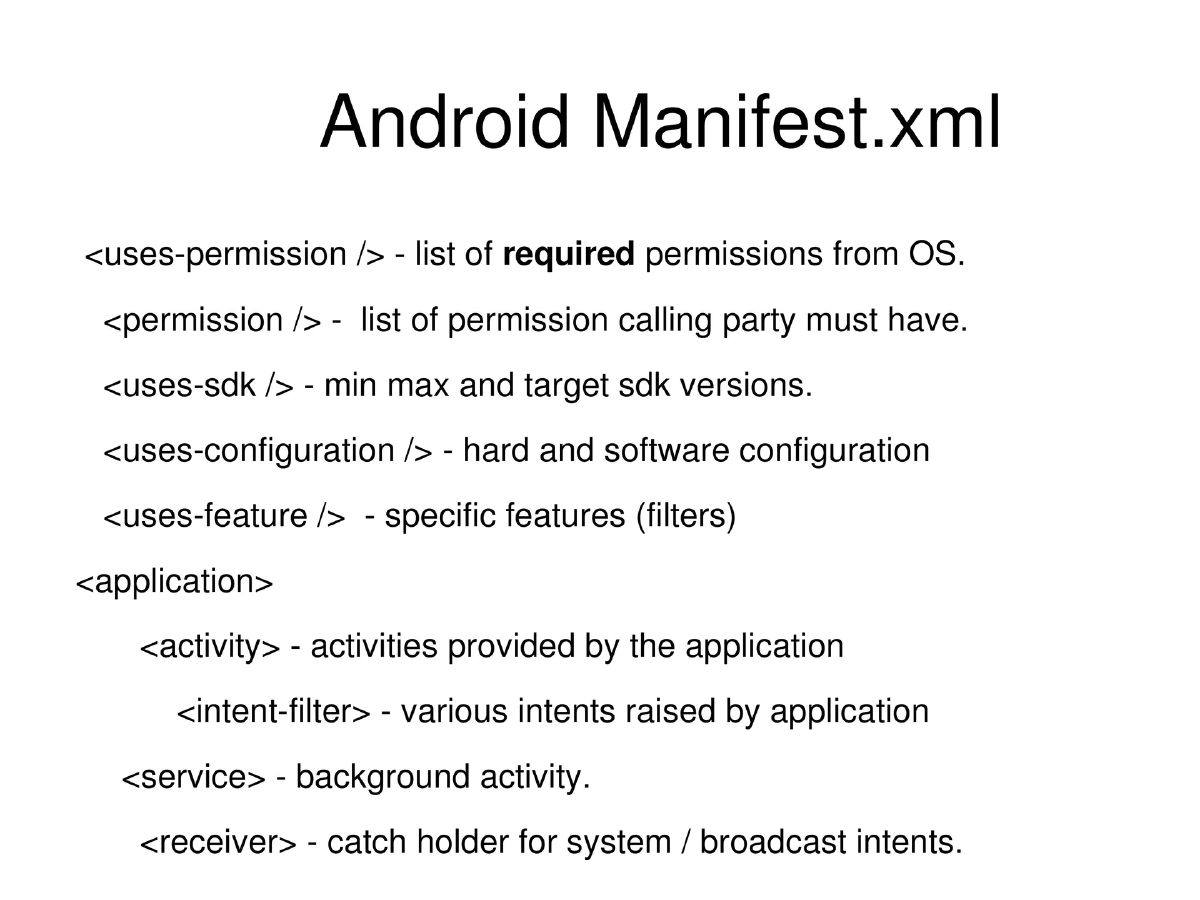
- Components: Activities (UI), Services (background), Intents (IPC), Content Providers (data sharing)
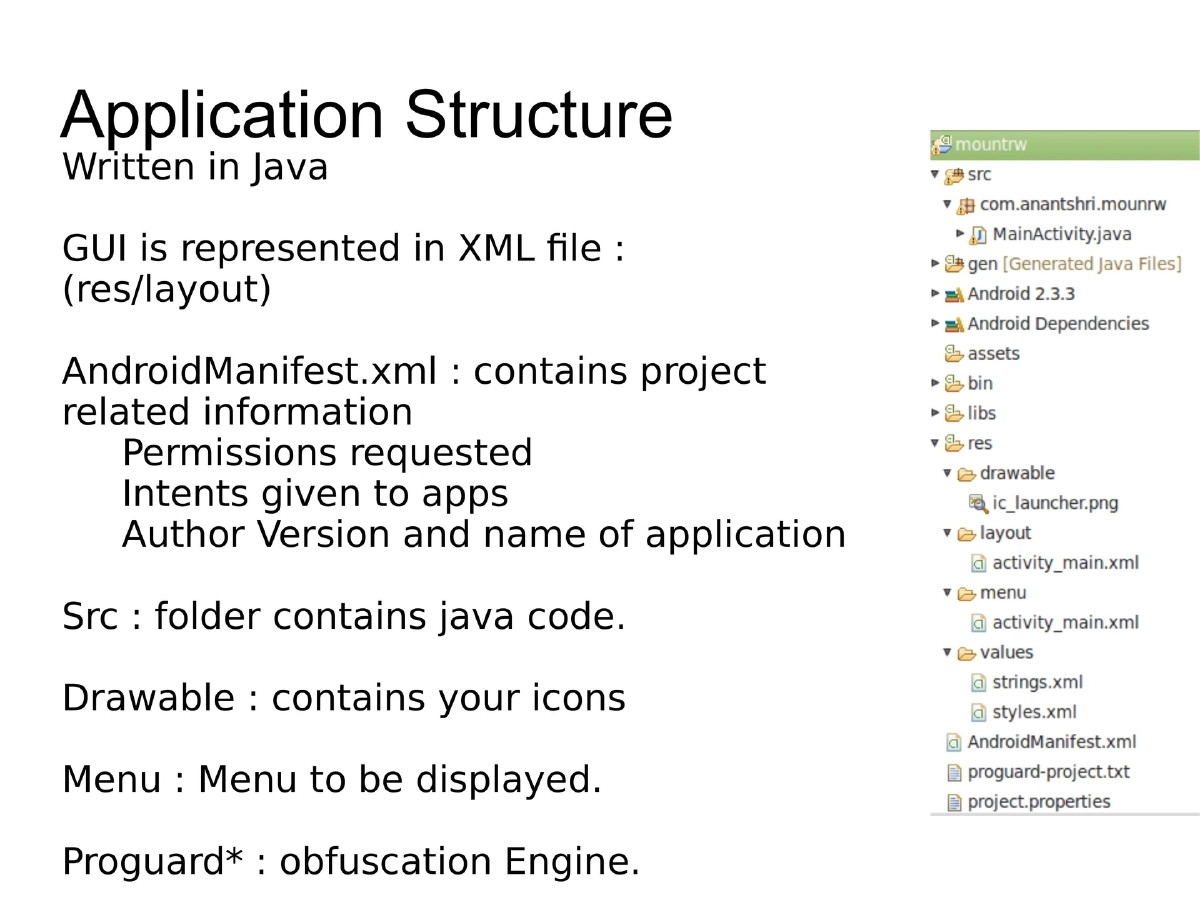
- AndroidManifest.xml: permissions, intents, SDK versions, features, receivers
Android Tamer Toolkit (v2):
- VM/Live ISO/Installable environment focused on Android security (first launched ClubHack 2011)
- Based on Ubuntu 12.04 / Linux Mint 13 (supported till 2017)
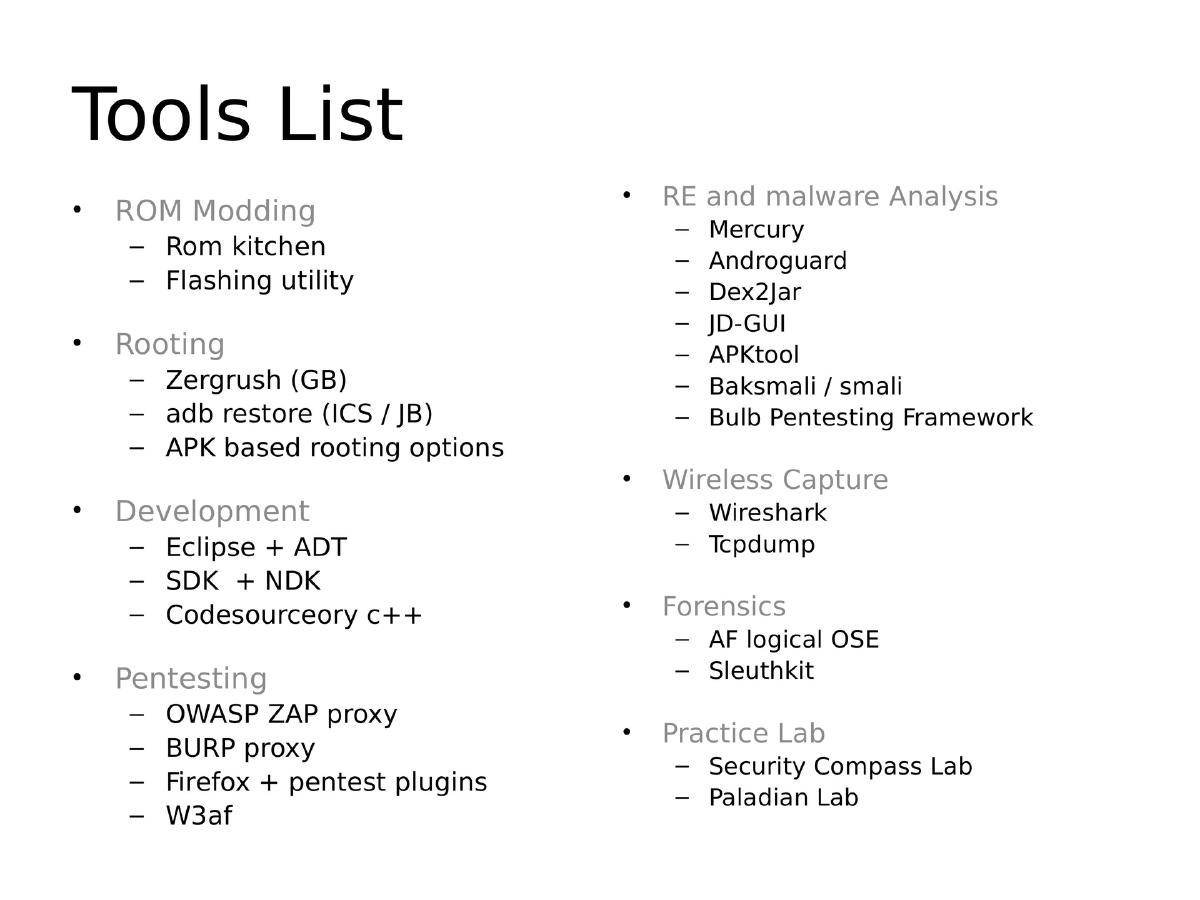
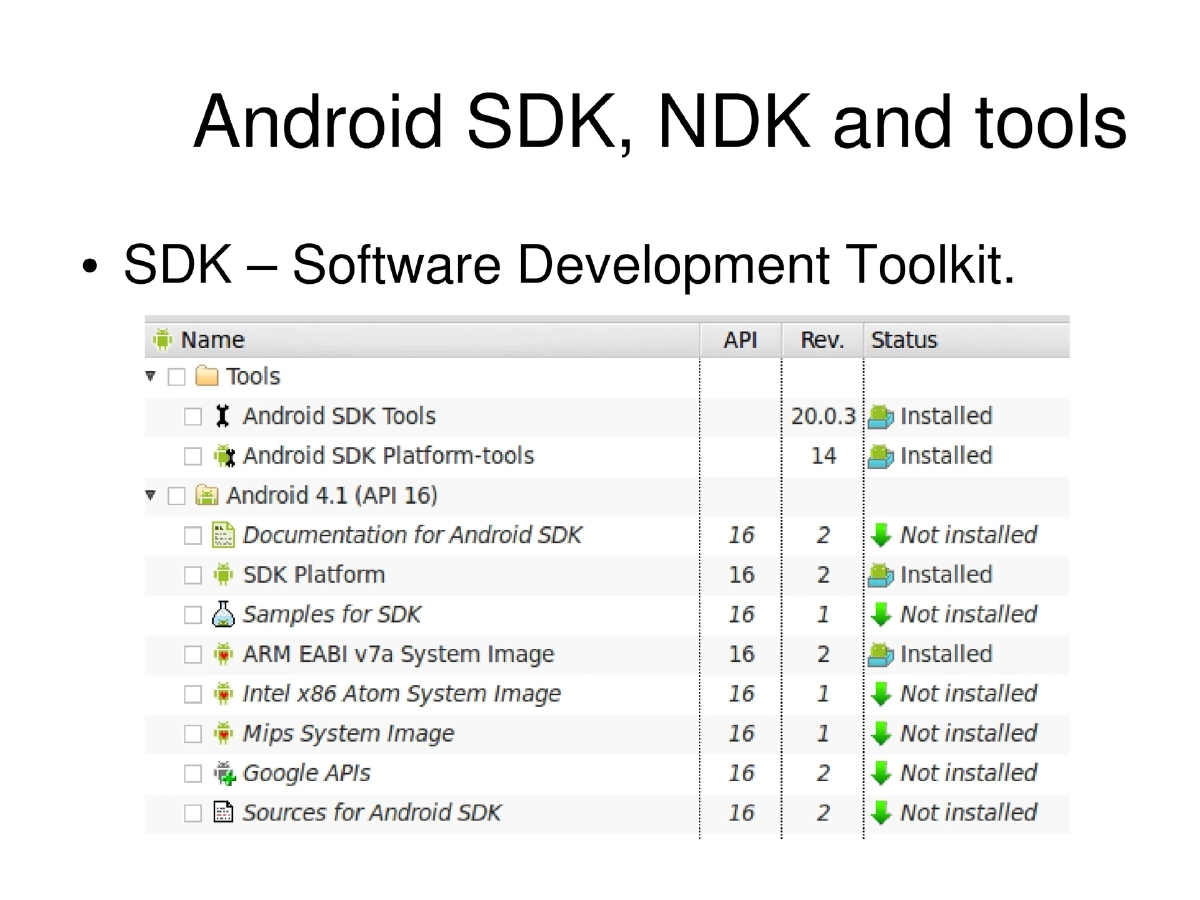
- Tools: ROM kitchen, flashing utilities, rooting kits, Eclipse + ADT + SDK + NDK, OWASP ZAP, Burp, Firefox pentest plugins, w3af, Drozer/Mercury, Androguard, Dex2Jar, JD-GUI, APKtool, Baksmali/Smali, Wireshark, AF Logical OSE, Sleuthkit, Security Compass Lab, Paladian Lab
Mobile Security Issues:
- Data/activity sniffing (SMS, audio, video, location, contacts, browsing history)
- Unauthorized telephony access (premium SMS/calls, USSD purchases)
- Unsafe data in transit (HTTP, FTP, unsigned XML) and at rest (SQLite, XML)
- Hardcoded values (DB connection strings, API keys)
- Side-channel data leakage through cache, temp files
- Information disclosure via reverse engineering
- Logic/time bombs, UI impersonation, rooting vulnerabilities
- SQL injection on backend servers, click/tap jacking, JavaScript attacks
Pentesting Methodology:
- Static analysis: APK reverse engineering via Dex2jar + JD-GUI/JAD, Smali, APKtool
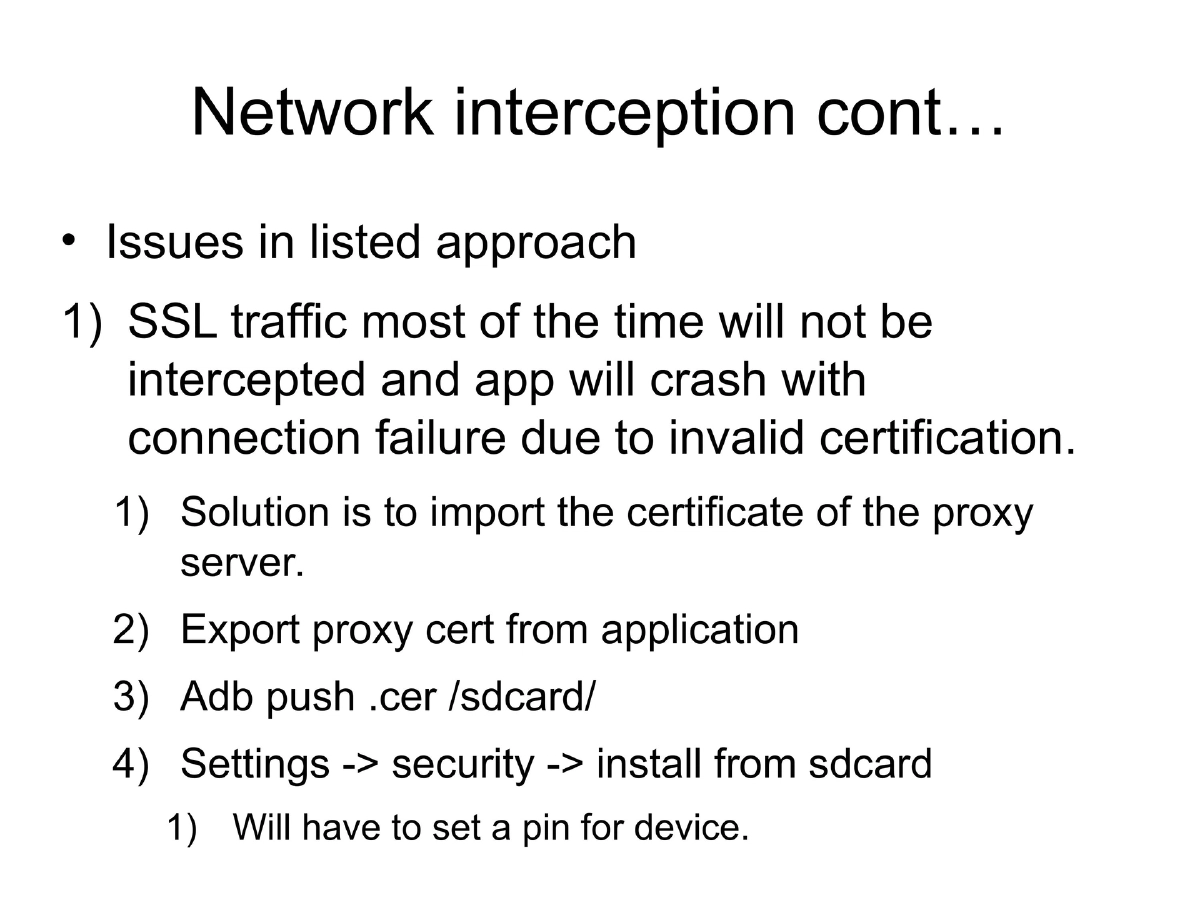
- Network traffic interception: Proxy configuration for emulator/device, SSL certificate import for intercepting HTTPS
- IPTables-based per-app traffic interception using Android’s per-app unique UIDs
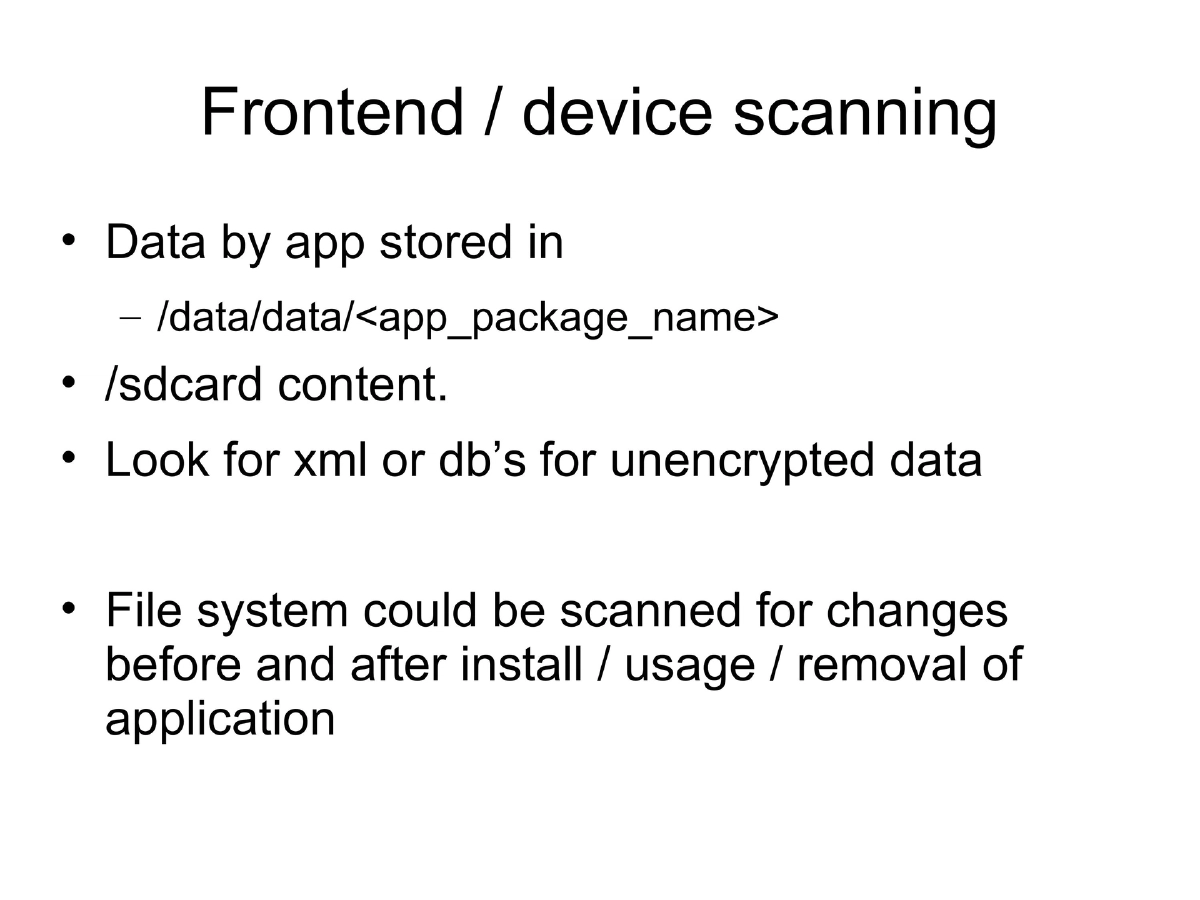
- Device-level tests: /data/data inspection, sdcard content, filesystem change analysis
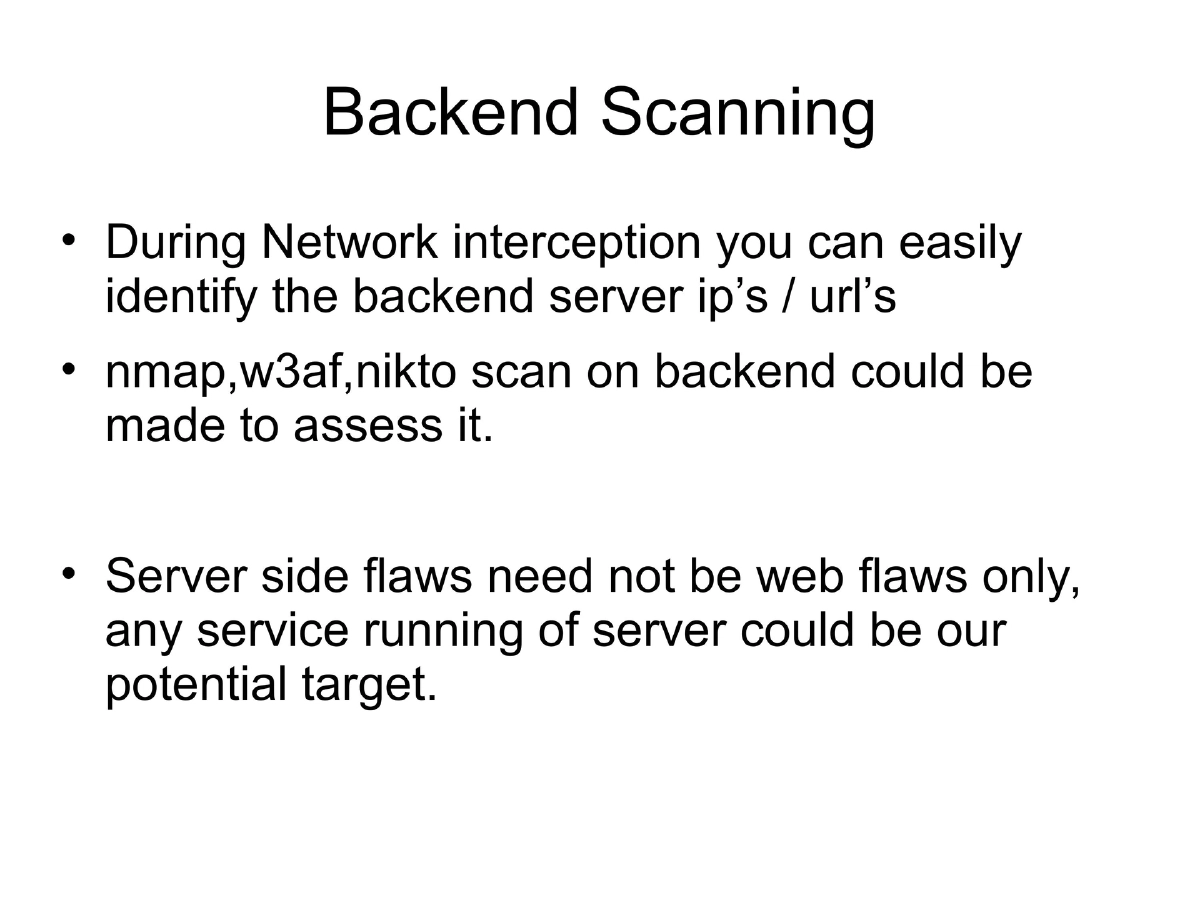
- Backend scanning: nmap, w3af, nikto on identified backend servers
- Pentesting frameworks: Drozer, AFE, Smartphone Pentest Framework
Pentesting Through Android:
- Mobile tools: DroidSheep, Dsploit, Interceptor, Network Discovery, Shark, zAnti
- Scripting environment: SL4A with Python (Py4a), Perl (Pl4a)
- Custom tool development: brute force attacks, task automation, WordPress enumeration
Actionable Takeaways
- Android pentesting requires understanding both the platform internals and application layer
- Static analysis through decompilation reveals hardcoded secrets and business logic
- SSL certificate installation is essential for intercepting encrypted application traffic
- IPTables enables granular per-application network interception on rooted devices
- Android devices themselves can serve as portable pentesting platforms with scripting frameworks