Exploiting Version Control Systems
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation covers the exploitation of publicly exposed version control system (VCS) directories on web servers, demonstrating how developers who deploy code via Git, SVN, or Mercurial can inadvertently expose their entire source code repository. Anant Shrivastava walks through VCS directory structures, predictable file paths for detection, available extraction tools, and live demos of extracting source code both with and without directory listing enabled.
Key Topics Covered
-
What is VCS Exploitation: Version control systems (Git, SVN, Mercurial) are the standard developer workflow for code deployment, often with auto-deployment on commit. When VCS metadata directories are left accessible on production web servers, attackers can reconstruct the entire source code repository, making it a high-value target — described as “a golden ticket” especially when auto-deployment is available.
-
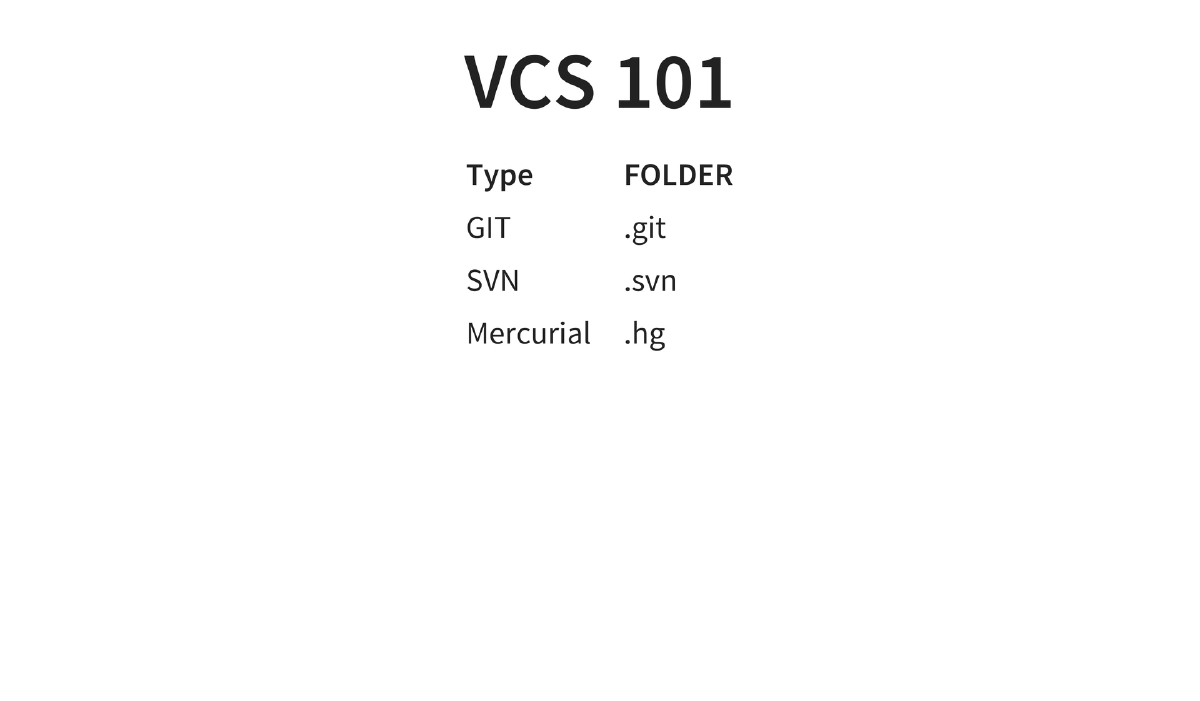
VCS Directory Signatures: Each version control system creates a characteristic hidden directory — Git uses
.git, SVN uses.svn, and Mercurial uses.hg. The.bzrdirectory (Bazaar) is also mentioned. These directories contain the complete repository history and metadata. -
Predictable Detection Files: Specific files can be probed to confirm VCS exposure —
.git/HEADfor Git repositories,.hg/requiresfor Mercurial, and.bzr/READMEfor Bazaar. The.gitignorefile is described as the “robots.txt of VCS” since it reveals file and directory names the developer wanted to exclude. -
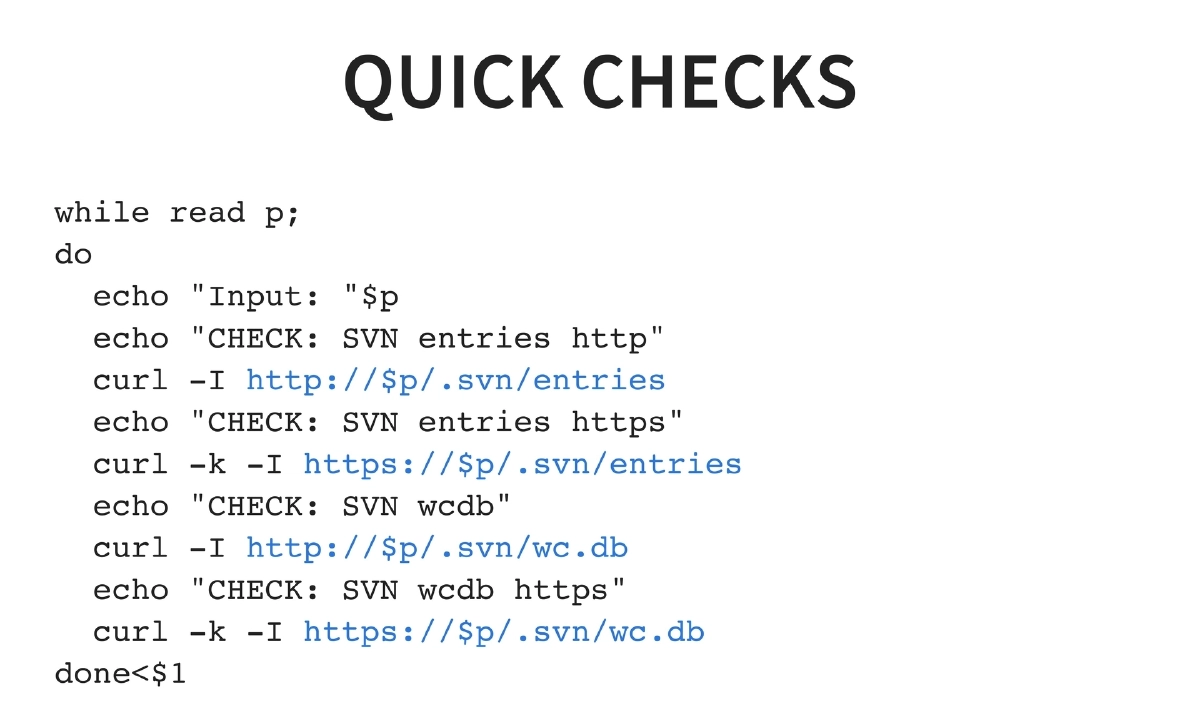
SVN-Specific Detection: A shell script demonstrates bulk checking of targets by probing for
.svn/entriesand.svn/wc.dbover both HTTP and HTTPS, enabling rapid identification of exposed SVN repositories across multiple domains. -
Extraction Tools:
- SVN-extractor: Written by Anant Shrivastava, focused specifically on SVN repository extraction.
- DVCS-pillage: Handles Git and Mercurial but lacks SVN support.
- dvcs-ripper: An alternative implementation that covers SVN, Git, and Mercurial.
-
Demo Scenarios: Live demonstrations covering two common configurations — exploitation when directory listing is enabled on the web server (straightforward directory browsing and download), and exploitation when directory listing is disabled (requiring knowledge of predictable file paths and tool-based reconstruction).
Actionable Takeaways
- Never deploy VCS metadata directories (
.git,.svn,.hg) to production web servers — add explicit deny rules in your web server configuration to block access to these directories. - During penetration tests, always probe for VCS directories by checking predictable paths like
.git/HEAD,.svn/entries,.svn/wc.db, and.hg/requireson target web servers. - Use automated tools like svn-extractor, DVCS-pillage, or dvcs-ripper to reconstruct source code from exposed VCS directories, even when directory listing is disabled.
- Check
.gitignorefiles when discovered, as they reveal the names of files and directories the developer considered sensitive enough to exclude from version control. - If using auto-deployment from VCS, ensure the deployment process strips VCS metadata or that web server rules prevent access to hidden directories.
- Include VCS directory exposure checks in your standard security scanning and CI/CD pipeline to catch accidental deployments before they reach production.