BlackHat Webcast
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation, delivered as a Black Hat WebCast in 2021, provides a comprehensive overview of cloud security from an offensive perspective. Anant Shrivastava covers the current state of cloud adoption, the shared responsibility model, security tooling options, and then maps real-world cloud attack techniques to the MITRE ATT&CK framework — focusing on storage services, Azure blob exploitation, AWS Elastic Beanstalk SSRF chains, IAM privilege escalation via shadow admin accounts, and Cognito misconfigurations.
Key Topics Covered
Cloud Adoption Landscape:
- Cloud computing has become essential, accelerated by the shift to remote work in 2020
- Traditional data centers and physical network boundaries are aging concepts
- Organizations fall into two categories: cloud-native (startups, SaaS providers, cloud aggregators) and those migrating from existing infrastructure
- Five cloud migration strategies: Rehost (lift and shift), Refactor (modernize for IaaS), Rearchitect (monolith to microservices/containers), Rebuild (rewrite as cloud-native), and Replace (adopt SaaS alternatives)
Cloud Security Concerns:
- Cloud represents a paradigm shift where conventional security controls are insufficient
- Top concerns: misconfigurations (the biggest), insecure APIs and interfaces, unauthorized access via credential leakage, unintended public data exposure, and data loss/sovereignty issues (GDPR and similar)
- Reference to NotSoSecure’s security architecture review methodology for cloud-native environments
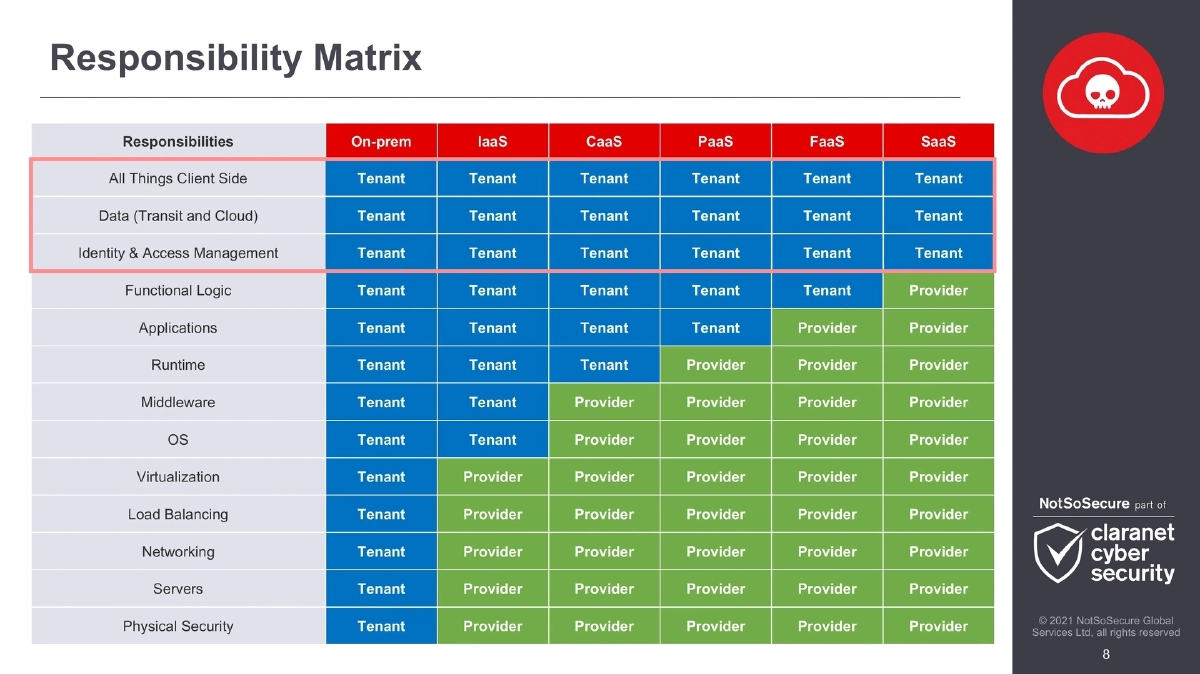
Shared Responsibility Matrix:
- Detailed breakdown across On-prem, IaaS, CaaS, PaaS, FaaS, and SaaS models
- Tenant always responsible for: client-side security, data protection (transit and cloud), and identity & access management
- Provider responsibilities increase from IaaS (virtualization and below) through to SaaS (everything except client-side, data, and IAM)
- Understanding where responsibilities shift is critical for identifying security gaps
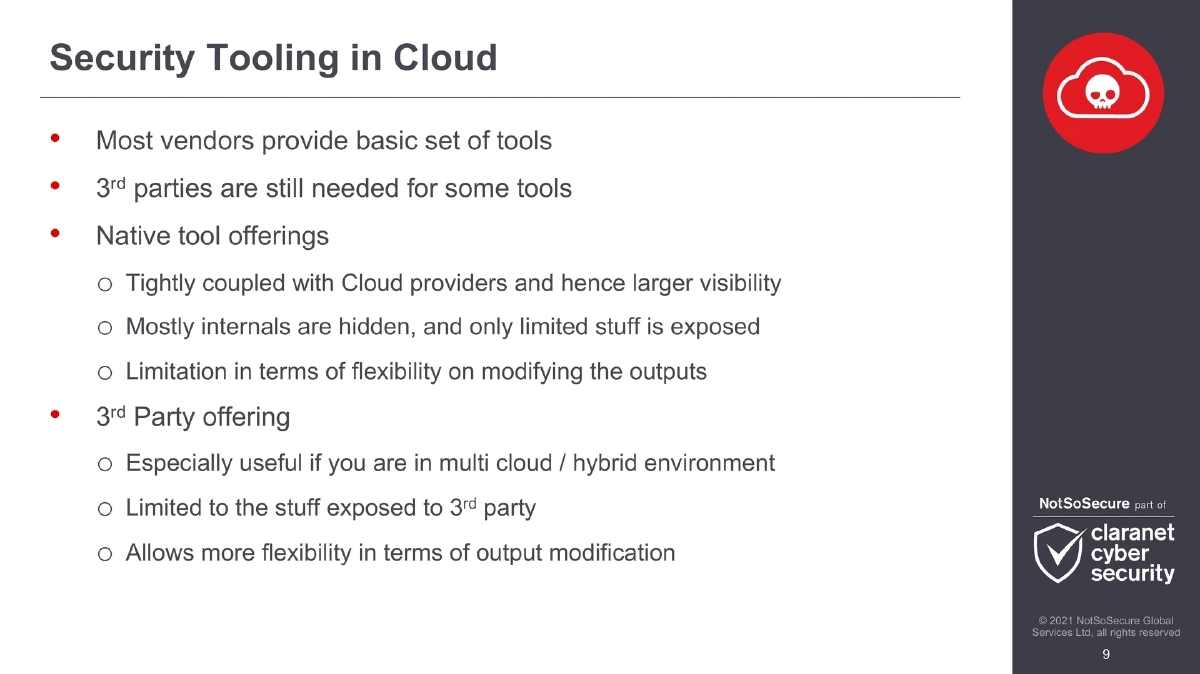
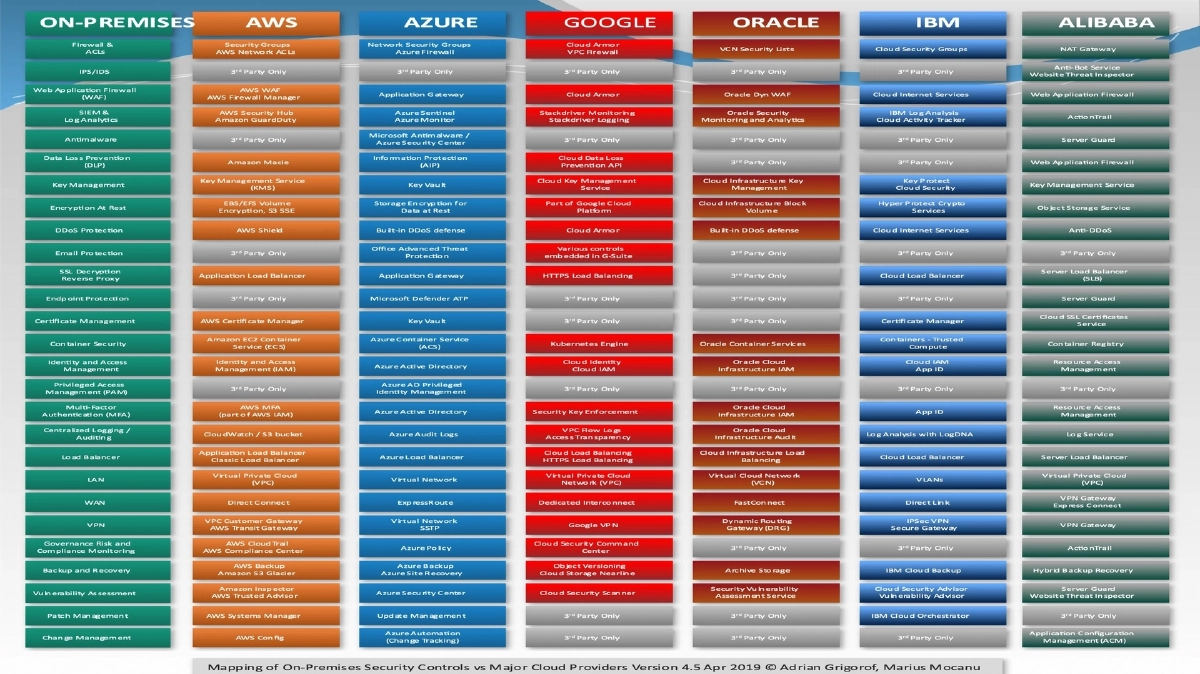
Security Tooling in the Cloud:
- Native vendor tools: tightly coupled with providers for greater visibility, but limited in flexibility and transparency of internals
- Third-party tools: especially valuable for multi-cloud and hybrid environments, more flexibility in output customization but limited to externally exposed data
- Both categories needed for comprehensive coverage
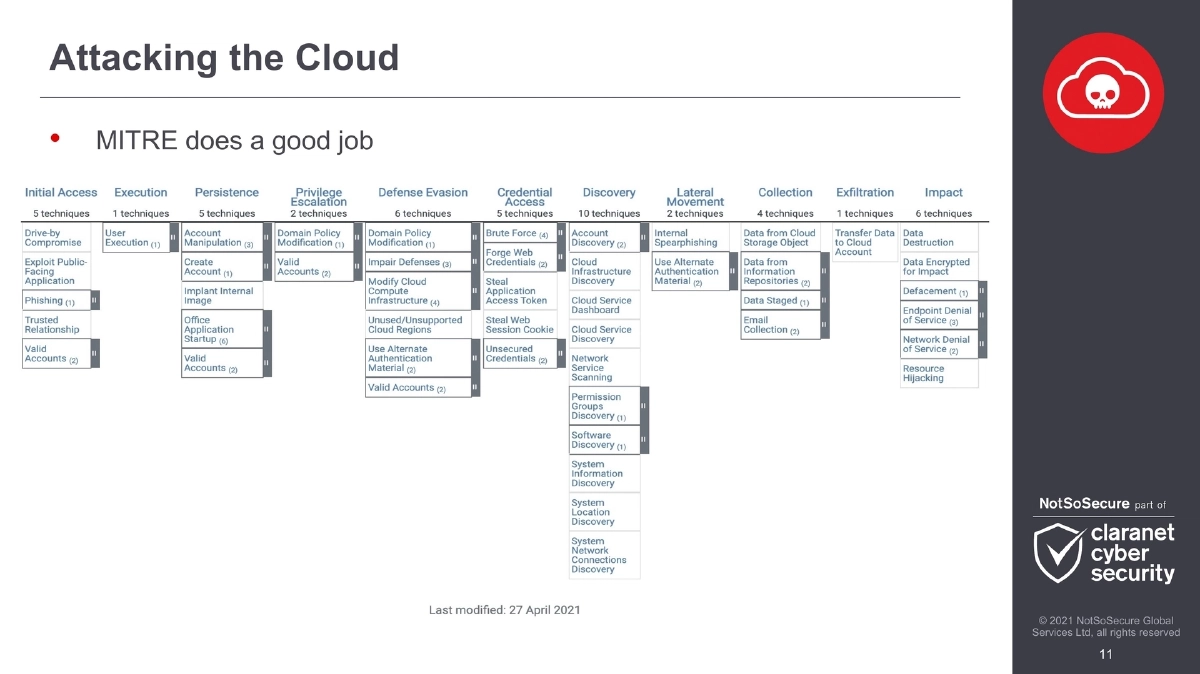
Attack Techniques Mapped to MITRE ATT&CK:
- MITRE ATT&CK framework used to structure cloud attack methodology
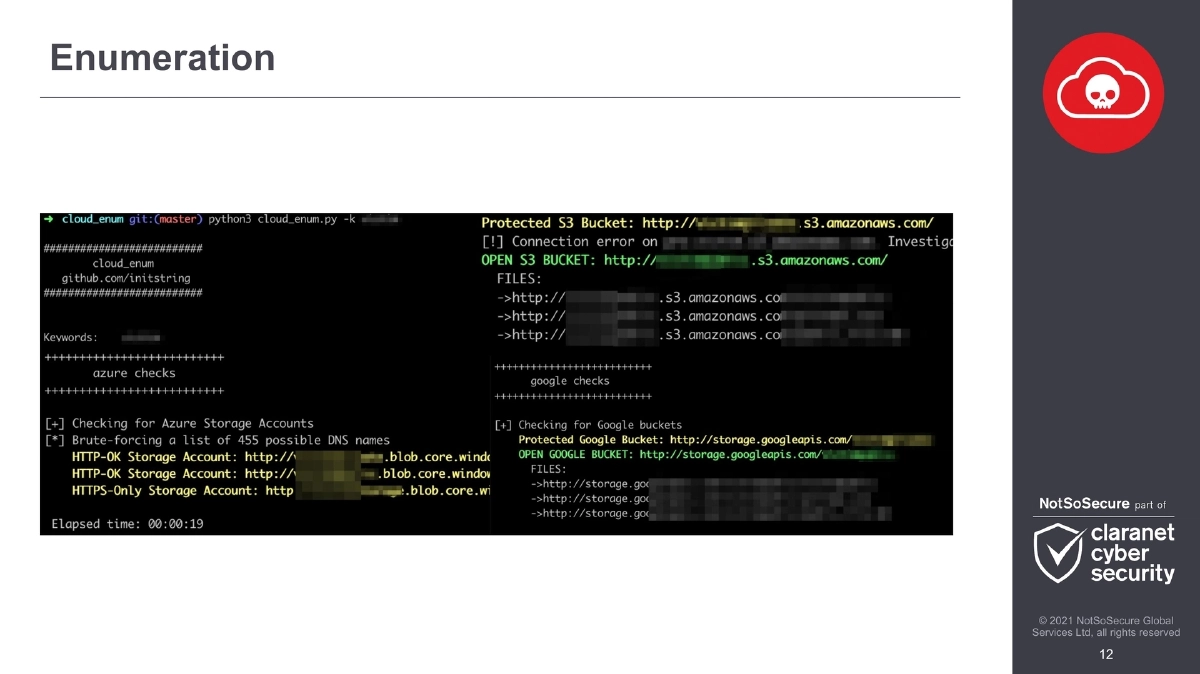
- Enumeration phase covers discovery of cloud assets and services
- Storage accounts identified as the “lynchpin” of cloud existence — enumeration, attack, exploit, and post-exploit phases
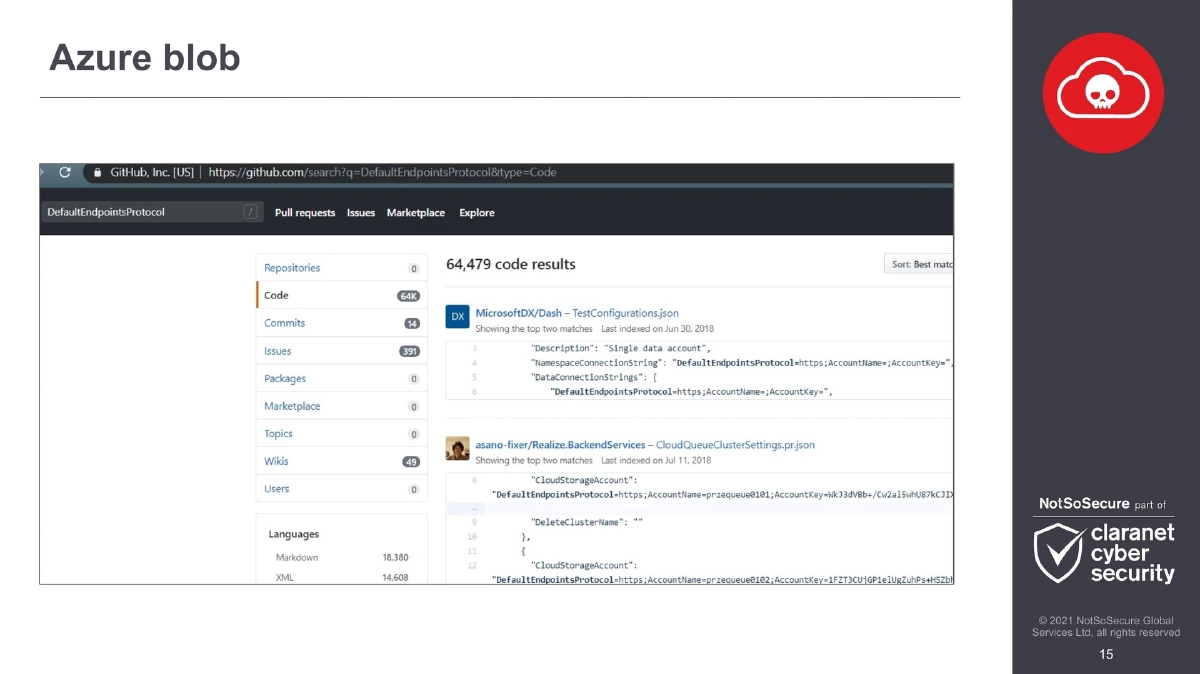
AWS S3 and Azure Blob Storage Attacks:
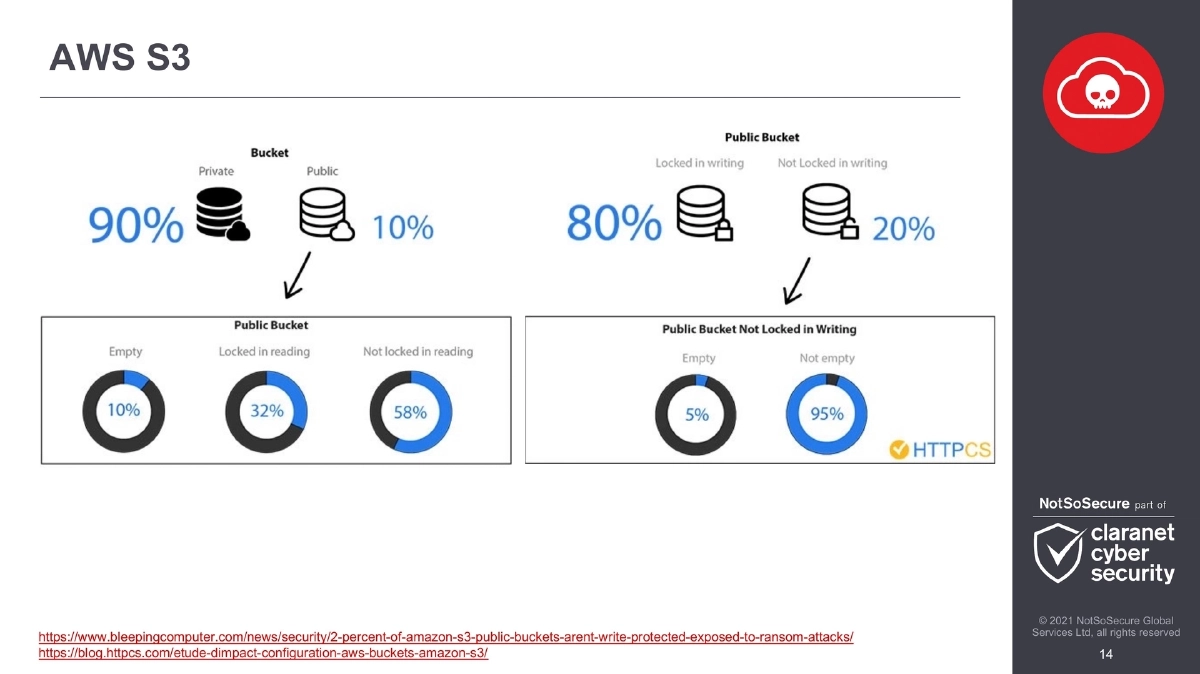
- Statistics showing 2% of Amazon S3 public buckets lack write protection, exposing them to ransom attacks
- Azure blob storage enumeration and exploitation techniques
- Case study: leaked Azure Storage SAS URL exploitation — loading in Azure Storage Explorer, accessing source code of Azure Functions, planting and hiding backdoors
AWS Elastic Beanstalk Attack Chain:
- Starting from SSRF vulnerability on Beanstalk-hosted application
- Metadata harvesting for account ID, region, and security credentials
- Bucket name enumeration using predictable naming patterns from account ID and region
- Source code access via AWS S3 CLI, then CI/CD pipeline abuse to deploy backdoor shells
- Additional predictable naming patterns identified by Summit Route
IAM Privilege Escalation — Shadow Admins:
- Cloud shadow admins are accounts with permissions attackers can abuse for privilege escalation
- These accounts are typically overlooked because they are not members of privileged groups like Domain Admin
- Case study: AWS managed policy
AmazonElasticTranscoderFullAccessincludediam:PutRolePolicypermission, allowing inline policy attachment to any role — effectively granting root admin access - AWS fixed this by creating replacement policy
AmazonElasticTranscoder_FullAccess
AWS Cognito Misconfigurations:
- Cognito supports unauthenticated and authenticated credential types
- Building on Andres Riancho’s BlackHat 2019 research on unauthenticated credentials
- Extended research around authenticated credentials revealed ways to leverage hidden signup features to gain elevated access
- Reference: NotSoSecure’s “Hacking AWS Cognito Misconfigurations” research
Actionable Takeaways
- Map your organization’s cloud deployment model (IaaS through SaaS) against the shared responsibility matrix to identify exactly which security controls are your responsibility versus the provider’s.
- Combine native vendor security tools with third-party solutions for comprehensive coverage, especially in multi-cloud or hybrid environments where native tools lack cross-platform visibility.
- Target cloud storage services early in engagements — they are the foundational dependency for nearly all other cloud services and frequently contain secrets, source code, and sensitive data.
- Hunt for shadow admin accounts in AWS by auditing managed policies for dangerous permissions like
iam:PutRolePolicythat enable privilege escalation without being members of obvious admin groups. - Test AWS Cognito configurations for both unauthenticated and authenticated credential abuse, including hidden signup features that may grant unexpected access levels.
- Chain SSRF vulnerabilities with cloud metadata services and predictable resource naming patterns (Elastic Beanstalk, S3) to achieve full application compromise through CI/CD pipeline abuse.
- Audit Azure SAS URLs for overly permissive access scopes and validate that leaked storage keys are not present in public repositories.