Diversec Keynote
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This keynote presentation, delivered at DiverSecCon 2021, shares Anant Shrivastava’s perspectives on the state of the information security industry. Through a series of thought-provoking themes, the talk distinguishes infosec as a profession from hacking as a passion, highlights the breadth of roles in the security industry beyond pentesting, discusses the post-COVID-19 shift in the threat landscape, and emphasizes the importance of collaboration and standing on the shoulders of those who came before.
Key Topics Covered
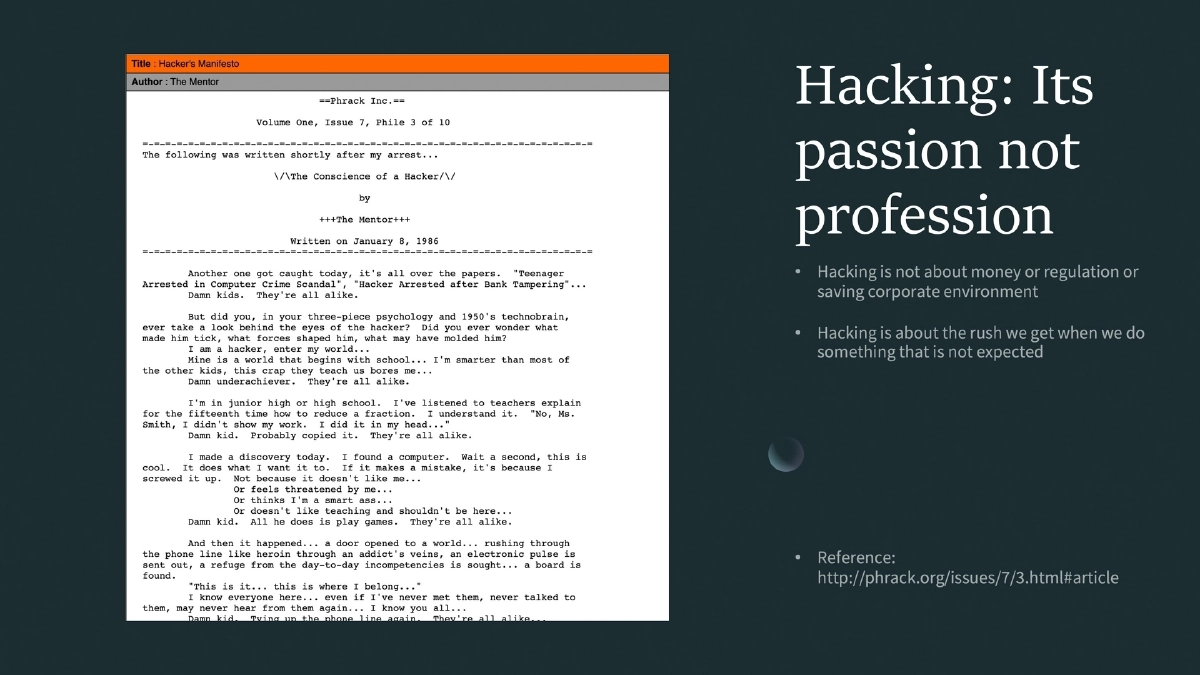
Infosec is Not Hacking:
- A clear distinction between information security as a professional discipline and hacking as a passion-driven pursuit
- Hacking is about exploration and curiosity; infosec is about providing security services to organizations
- Conflating the two leads to unrealistic expectations for both practitioners and employers
The Breadth of the Infosec Industry:
- The security field extends far beyond penetration testing and offensive work
- Reference to Kiersten Brager’s framework: “Security is not just hacking” — covering governance, risk, compliance, architecture, operations, incident response, and more
- The industry needs diverse skill sets and mindsets, not just offensive specialists
Hiring Practices:
- Organizations should hire for the work that needs to be done, not for trendy titles or flashy skill sets
- Practical capability and job-fit matter more than certifications or conference fame
- The emphasis should be on building well-rounded teams that cover the full spectrum of security needs
Post-COVID-19 World:
- The pandemic fundamentally changed the security landscape with the shift to remote work
- New attack surfaces emerged as organizations rapidly adopted cloud services and remote access solutions
- The perimeter dissolved, requiring a rethinking of traditional security boundaries and controls
Offensive Perspective — Dig Deep but Don’t Forget the Old:
- Attackers should pursue deep specialization in modern technologies while remembering that classic vulnerabilities and attack vectors remain relevant
- Reference to XKCD comic 2176 illustrating how old vulnerabilities persist alongside new ones
- Legacy systems and forgotten infrastructure often provide the easiest entry points
Defenders Must Assemble:
- A call for the defensive side of security to organize and collaborate more effectively
- Defense requires teamwork across disciplines — detection, response, architecture, and operations working in concert
- The defensive community needs the same energy and collaboration that offensive researchers bring to conferences and communities
Standing on Shoulders of Giants:
- Acknowledging the contributions of predecessors in the field
- The infosec community’s strength lies in building upon shared knowledge and open research
- New practitioners should study the foundational work that made current techniques possible
Actionable Takeaways
- Distinguish between hacking (passion and exploration) and information security (professional practice) when building your career or hiring for your team — they require different mindsets and skill sets.
- Recognize the full spectrum of infosec roles beyond pentesting: governance, architecture, incident response, DevSecOps, compliance, and more — and build teams that cover this breadth.
- Hire based on practical skills and job requirements rather than chasing trendy titles or certification collections.
- Reassess your security posture for the post-pandemic reality where remote work is permanent, cloud adoption is accelerated, and traditional perimeter-based defenses are insufficient.
- Balance deep specialization in modern attack techniques with knowledge of classic vulnerabilities — legacy systems and forgotten infrastructure remain high-value targets.
- Invest in defensive collaboration with the same intensity as offensive research — assemble cross-functional security teams and participate in community knowledge sharing.