Owtf
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation introduces OWASP OWTF (Offensive Web Testing Framework), a Python-based automated penetration testing framework that organizes security testing operations according to standards like OWASP, NIST, and others. Presented at an OWASP Bangalore meetup, Anant Shrivastava demonstrates OWTF’s capabilities through live demos against test applications, covering its architecture, unique selling points, setup process, and contribution opportunities.
Key Topics Covered
-
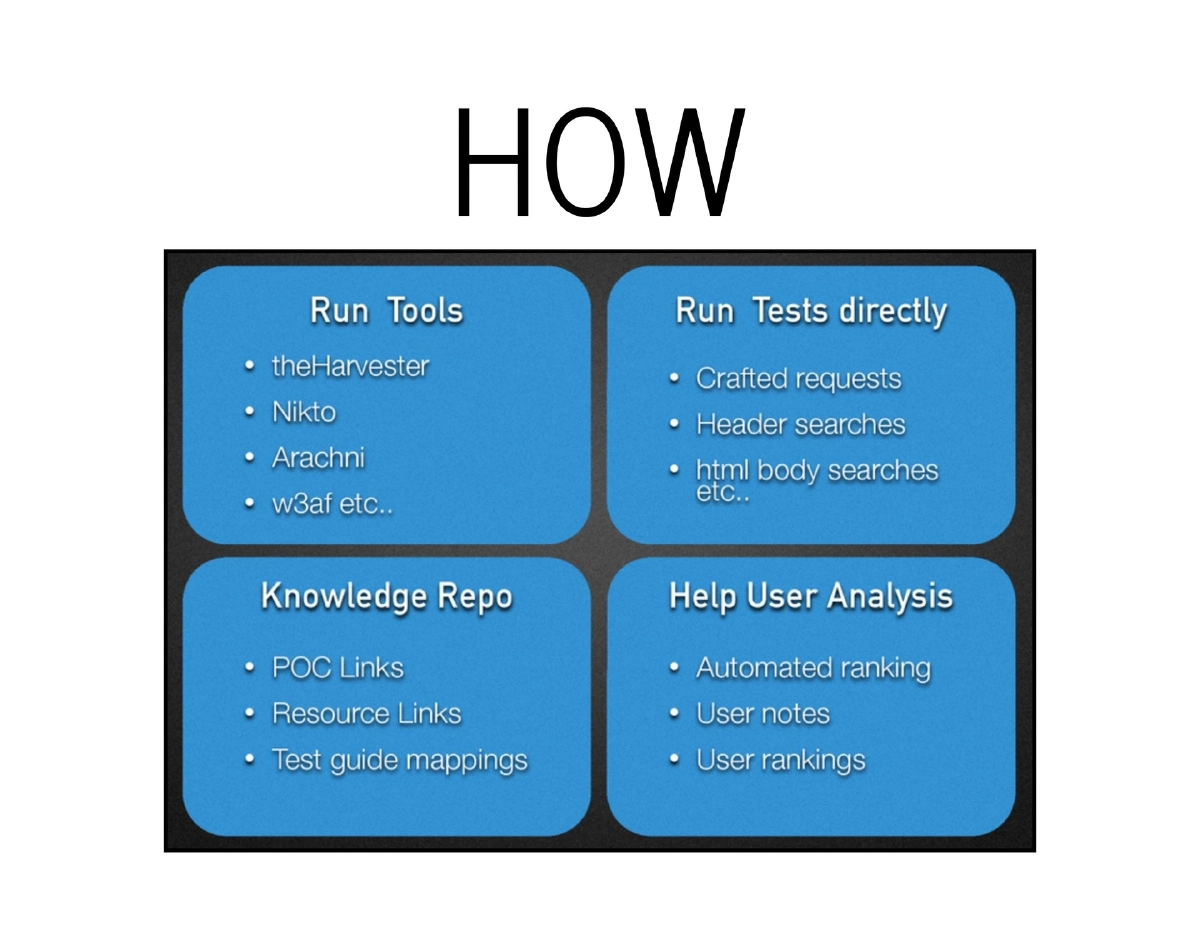
What is OWTF: The Offensive Web Testing Framework is one of the most active OWASP projects (alongside ZAP and the Testing Guide). Originally created by Abraham Aranguren (@7a_) in Python, OWTF began as a way to run OWASP tests passively — without directly accessing the target website — and evolved into a comprehensive automated pentesting platform.
-
Core Capabilities and USP: OWTF provides automated task execution with a single dashboard, result aggregation with plans for future correlation, raw tool output availability, and the ability to pause and resume tasks. It serves as a single point of access for all penetration testing data and findings.
-
Standards Compliance: Tests are organized according to established standards including OWASP Testing Guide, NIST, and custom frameworks. Results can be ranked with custom notes and categorized by execution type (passive or active testing).
-
Platform Support: Officially supported on Kali Linux and Samurai WTF distributions. Setup involves cloning the repository from GitHub (
github.com/owtf/owtf) and running the Python installation script. -
Demo Environment: Live demonstrations were conducted against
demo.testfire.netandtestasp.vulnweb.comrunning on a Kali Linux machine with OWTF configured. -
Advanced Features Not Covered: OWTF botnet mode for distributed scanning, built-in proxy functionality, PlugnHack support for browser integration, and the WAF Bypasser along with other extensible plugins.
-
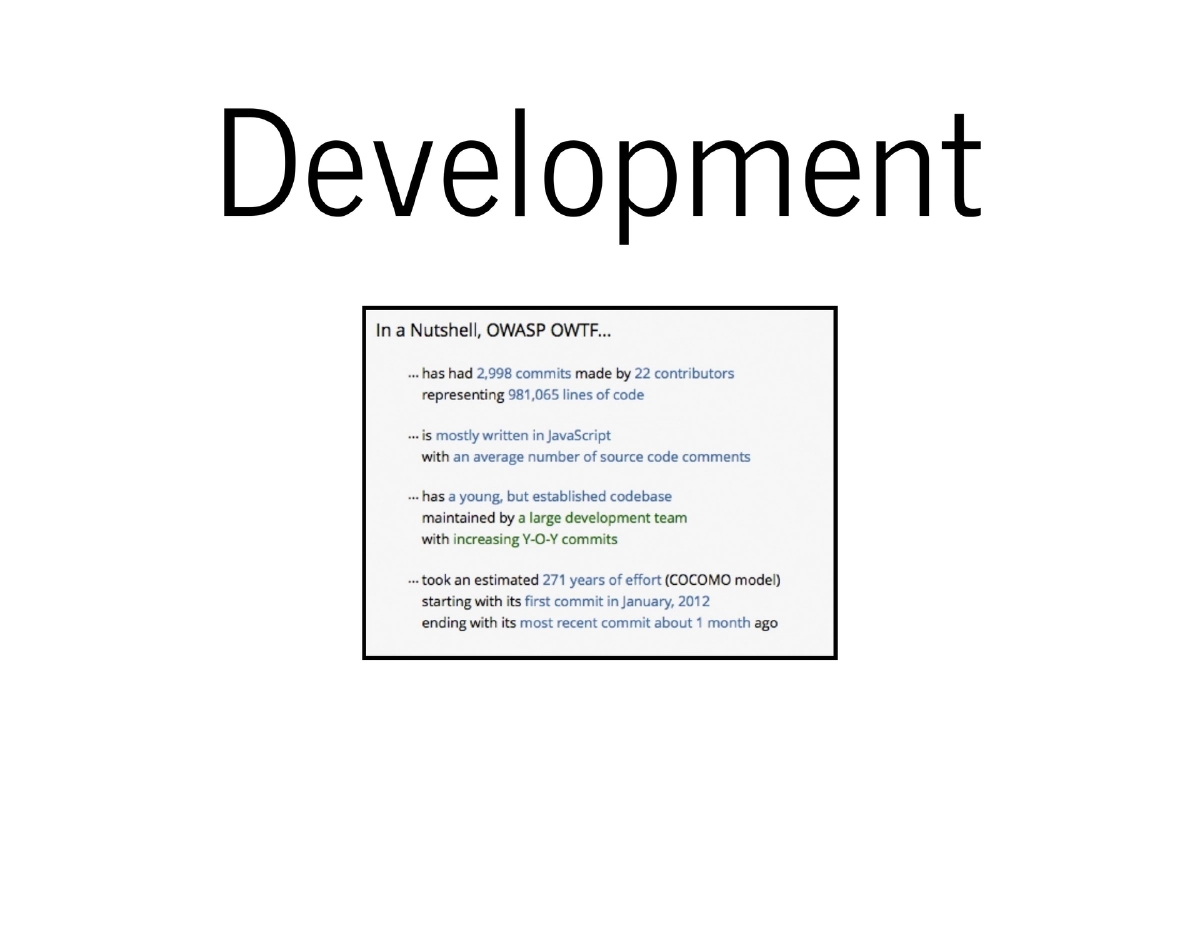
Contributing to OWTF: Opportunities include Google Summer of Code (GSoC), Winter of Code programs, direct code contributions, and issue tracker participation on the GitHub page.
Actionable Takeaways
- Use OWTF as an aggregation layer for penetration testing to organize findings by standard (OWASP, NIST) and manage both passive and active test execution from a single dashboard.
- Set up OWTF on Kali Linux or Samurai WTF for the best out-of-the-box experience, using the simple three-step installation (git clone, cd, python install).
- Leverage OWTF’s pause and resume functionality for long-running assessments where continuous testing is impractical.
- Contribute to the OWTF project through GSoC, code contributions, or issue tracker participation to help advance this community-driven security testing framework.
- Explore OWTF’s advanced features like botnet mode for distributed scanning and the WAF Bypasser for testing against protected applications.