Rootconf Heartbleed
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation, delivered at RootConf 2014, provides a comprehensive analysis of the Heartbleed vulnerability alongside other major SSL/TLS bugs that collectively demonstrated that most security protocols were fundamentally broken. Anant Shrivastava covers Heartbleed, GnuTLS, Apple’s goto fail, Lucky13, BEAST, and CRIME — explaining what each means for developers and administrators, and providing both technical and policy-based solutions for securing infrastructure.
Key Topics Covered
-
Overview of SSL/TLS Vulnerabilities: A panoramic view of multiple critical bugs — Heartbleed (OpenSSL), GnuTLS bug, Apple’s goto fail bug, Lucky13, BEAST, and CRIME — that collectively undermined trust in SSL/TLS implementations. The core thesis: “SSL == inSecure Socket Layer” given the state of affairs in 2014.
-
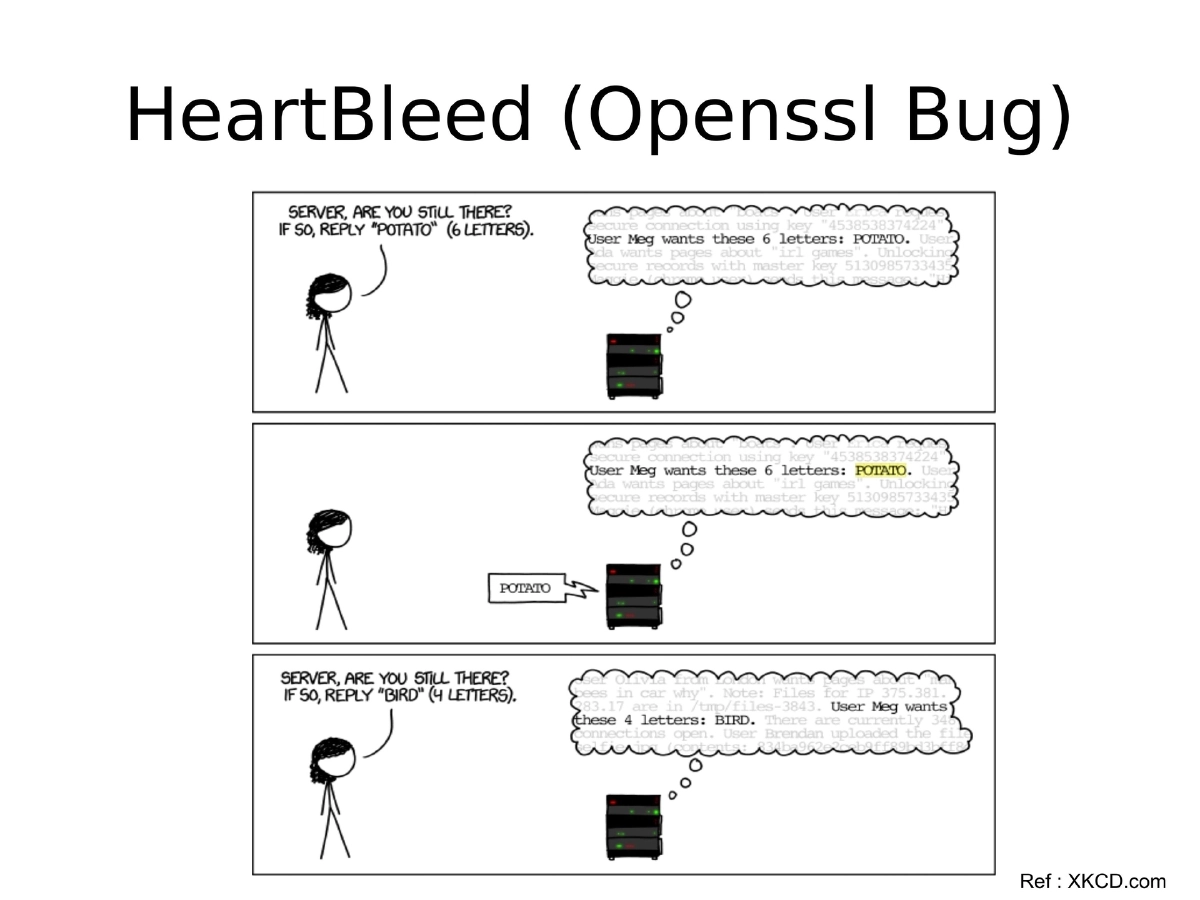
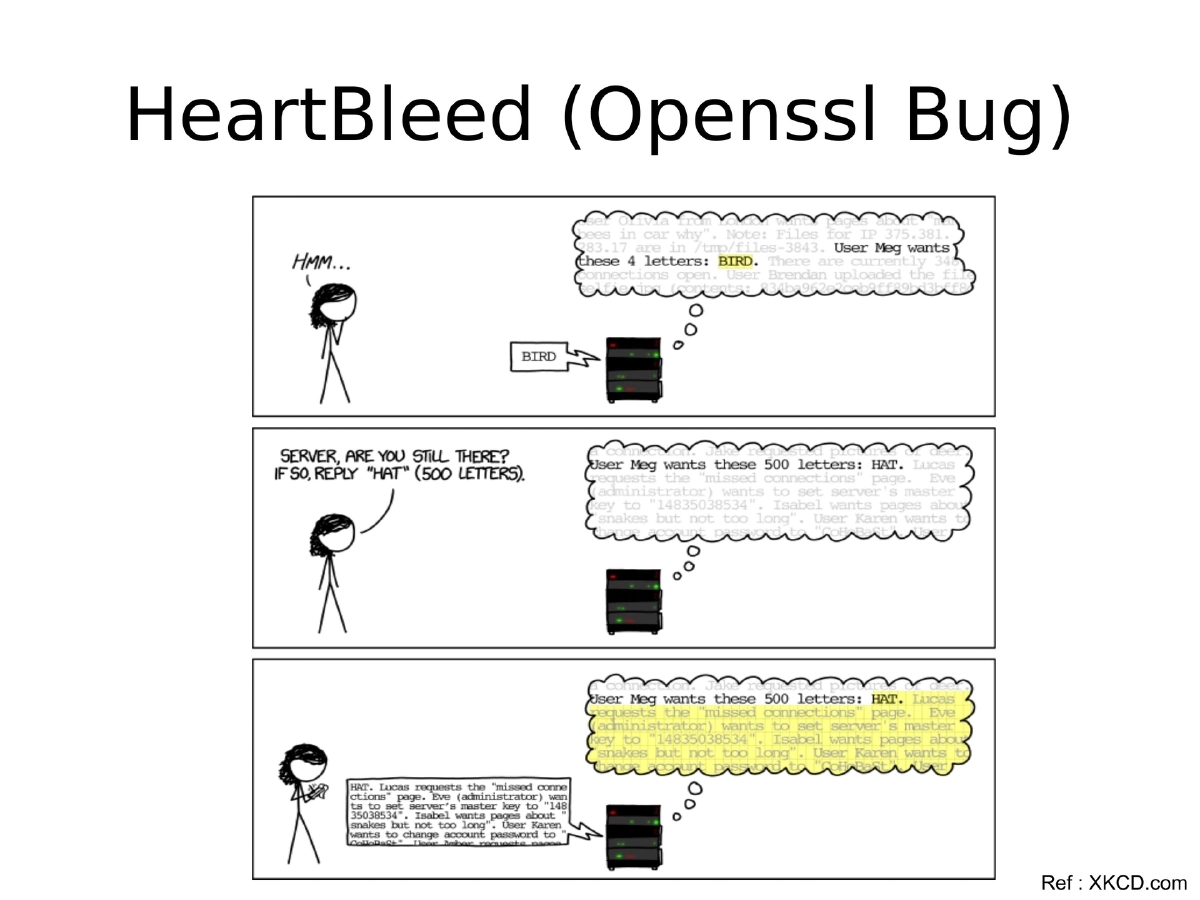
Heartbleed (CVE-2014-0160): A memory disclosure vulnerability in OpenSSL (versions 1.0.1 through 1.0.1f) that allowed attackers to read up to 64KB of server memory per request. Key trivia: three independent researchers found the same issue within a week; early exploit scripts only checked TLS 1.1 (missing 1.0 and 1.2), causing many servers to be incorrectly marked safe; the original discoverer did not expect private key disclosure; Akamai’s open-sourced key safety solution was bypassed within hours.
-
Impact Statistics: 75 Cisco products were affected, Tor was among affected products, GlobalSign’s CRL grew from 22KB to 4.9MB, and revoked certificates jumped from 1,492 to 133,243 — demonstrating the massive scale of certificate revocation required.
-
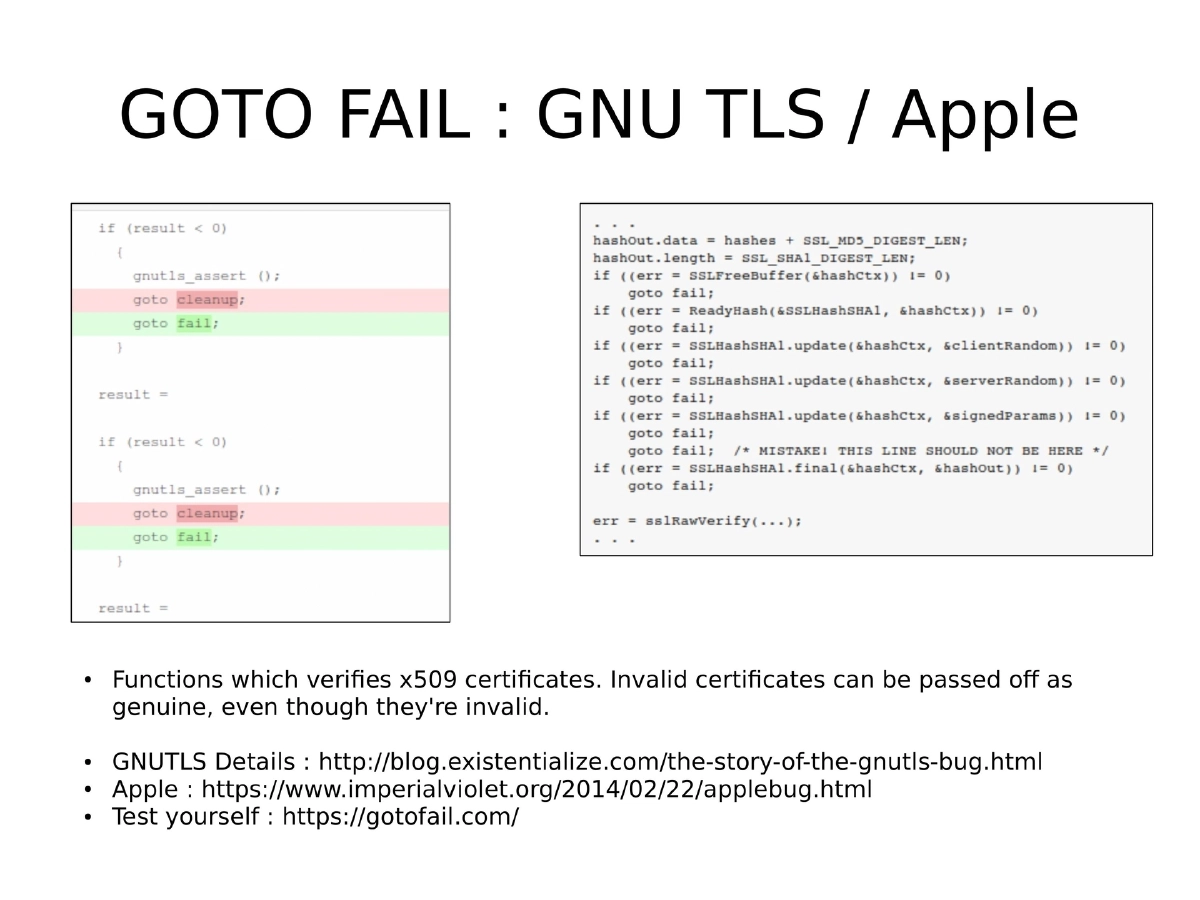
GnuTLS and Apple goto fail: Both were certificate validation bypass bugs where the x509 verification functions could accept invalid certificates as genuine. These were implementation flaws in the verification logic rather than protocol-level weaknesses.
-
BEAST, CRIME, and Lucky13: BEAST exploited CBC ciphers to retrieve encrypted data through key guessing; CRIME exploited TLS compression (SPDY) to extract data; Lucky13 was a cryptographic timing attack. A critical catch-22 existed: protecting against BEAST made systems vulnerable to Lucky13 and vice versa.
-
Reverse Heartbleed: A client-side variant of the attack using tools like Pacemaker that could exploit vulnerable OpenSSL clients connecting to malicious servers.
-
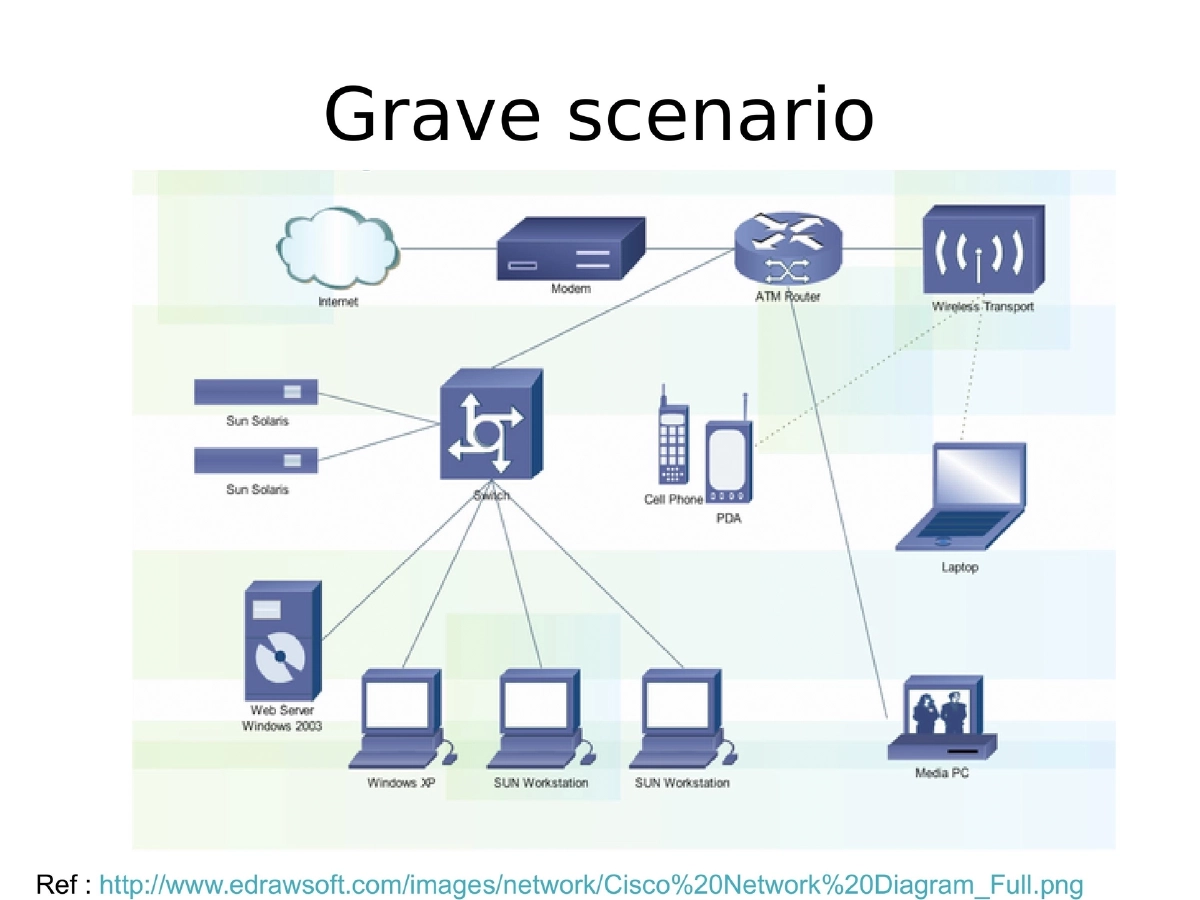
Status Quo: SSL 3.0 / TLS 1.0 was broken at nearly all algorithm and protection levels, with either reasonable exploits or conceptual exploitation available for most configurations.
-
Technical Solutions: Enable TLS 1.1 and 1.2, implement Perfect Forward Secrecy (random public keys per session using non-deterministic algorithms so that compromising one session does not affect others), change SSL certificates post-breach, and accept that security only holds until the next flaw is found.
-
Policy-Based Solutions: Fail hard and fail early with established emergency processes; inform customers of suspected breaches; force password resets rather than merely requesting them; do not forget to rotate API keys and other secrets alongside certificates; maintain hardware support subscriptions for timely patches.
-
Advice for Developers and Administrators: Administrators must patch meticulously, monitor religiously, and leverage big data to identify anomalies. Developers must care about older library versions, avoid bundling dependencies without maintaining updates, and recognize that more eyes on open-source code does not automatically mean fewer security bugs.
Actionable Takeaways
- Enable TLS 1.1 and 1.2 and implement Perfect Forward Secrecy to ensure that compromise of one session does not expose data from other sessions.
- When a major vulnerability like Heartbleed is disclosed, assume credentials and keys are compromised — force password resets, rotate API keys, and replace SSL certificates rather than just patching the software.
- Establish emergency response processes that inform customers proactively and block logins if breach is suspected — fail hard and fail early.
- Developers should stop bundling dependencies without maintaining update pipelines; treat third-party libraries as ongoing maintenance obligations, not one-time imports.
- Do not rely on initial exploit scripts or scanner results during major vulnerability disclosures — early tools often miss variant configurations (as seen with Heartbleed scripts checking only TLS 1.1).
- Maintain hardware and software support subscriptions to ensure timely access to security patches, especially for network infrastructure devices.