Nullcon Extreme Android
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This is a comprehensive two-day training workshop titled “Xtreme Android Exploitation Lab” delivered by Anant Shrivastava and Anto Joseph at Nullcon 2017. The training takes a hands-on, scenario-based approach to Android security — covering the full spectrum from APK reverse engineering, traffic interception, SSL pinning bypass, and root detection evasion on Day 1, through dynamic analysis, instrumentation frameworks (Xposed and Frida), and Android fuzzing on Day 2. The lab uses Android Tamer as the base environment with Genymotion emulator, and maps exercises against the OWASP Mobile Top 10 risks.
Key Topics Covered
-
Workshop Setup and Philosophy: The training uses VirtualBox with two VMs: Android Tamer (Nullcon Edition) and a Genymotion Android emulator. The philosophy prioritizes hands-on exercises over theory, using real-world attack scenarios that security professionals encounter. Credentials: username
android, passwordtamer. -
Day 1: Static Analysis and Traffic Interception
-
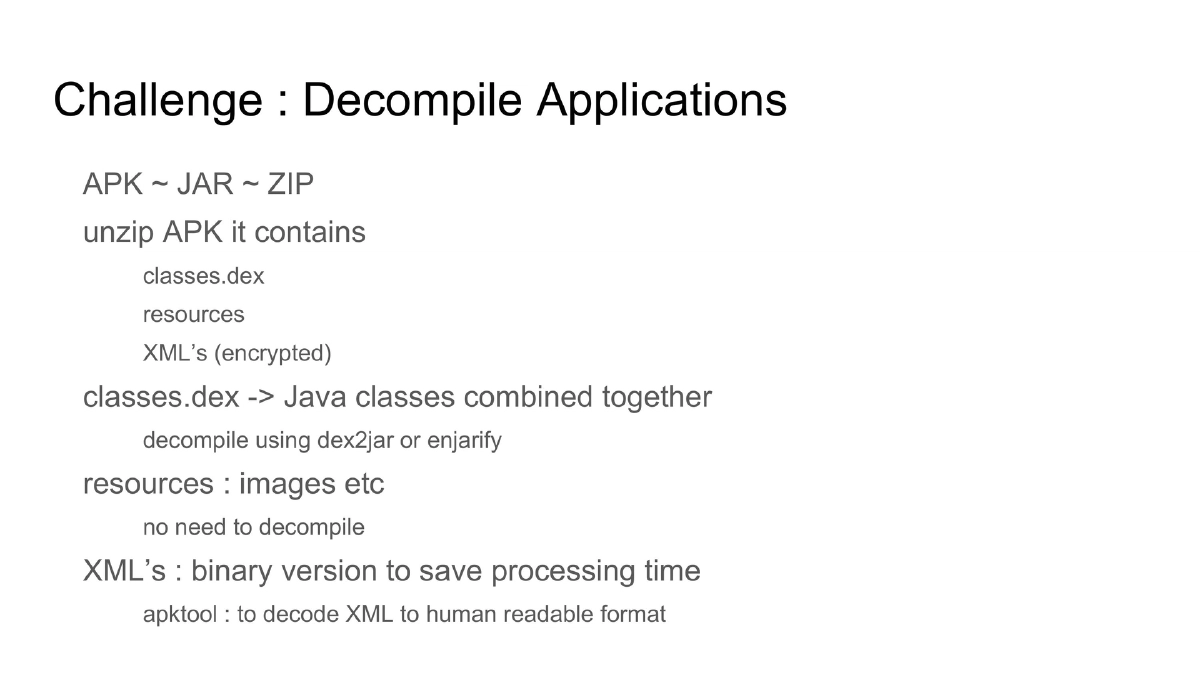
Understanding Android Application Code: APK files are modified Java code packages that can be decompiled to human-readable Java (easier to read but may lose accuracy) or Smali (bytecode representation that preserves accuracy). An APK is structurally similar to a ZIP/JAR file containing
classes.dex, resources, and binary-encoded XML files. -
Decompilation Techniques: Using
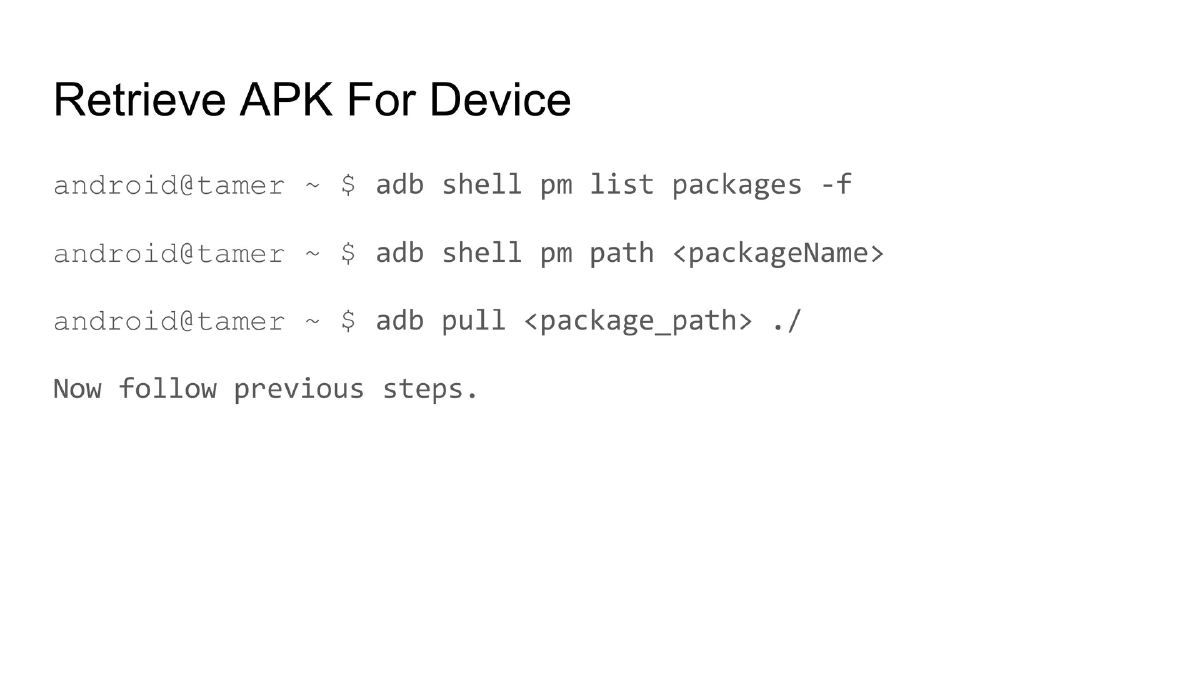
dex2jarorenjarifyto convert DEX to JAR files,apktoolto decode binary XML to human-readable format, and Android Tamer’s customapk2javascript that automates the full pipeline — decrypting XML files and producing Java code from two different decompilers (jad and jadx) simultaneously. APKs can be retrieved from devices usingadb shell pm list packages -fandadb pull. -
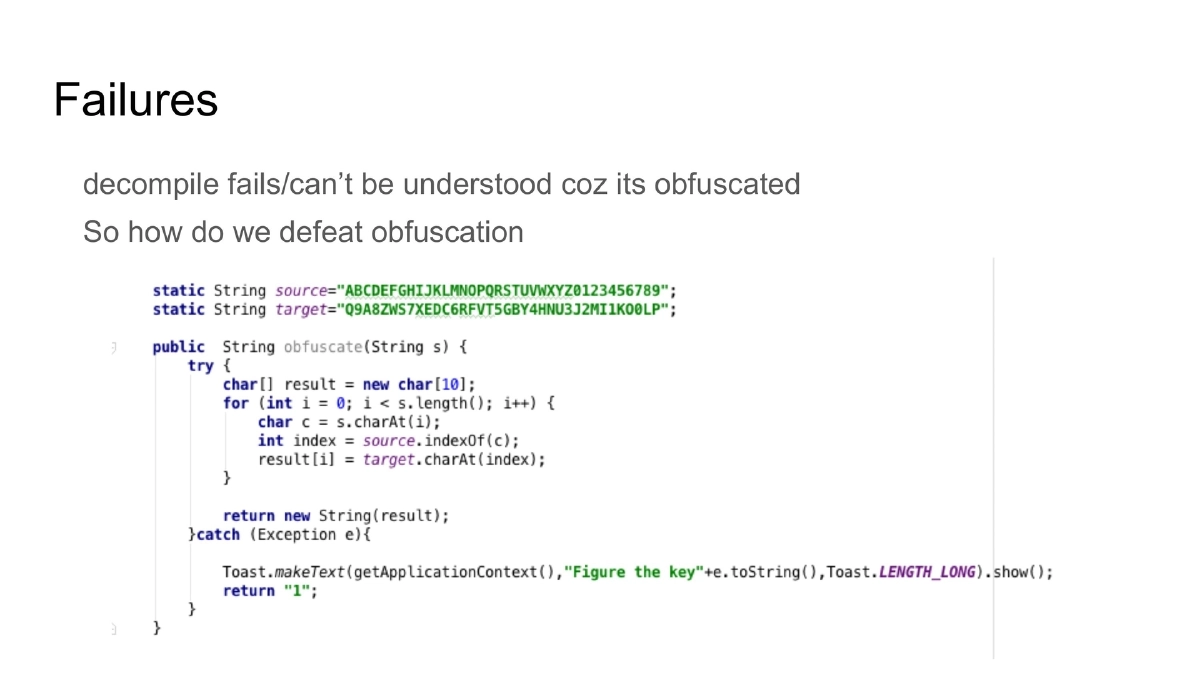
Handling Obfuscated Code: Common obfuscation techniques include control flow manipulation, string encryption, class and method renaming, and Java reflection to hide method calls. De-obfuscation tools covered include Simplify (generic de-obfuscation) and JEB with custom modules. The training emphasizes that obfuscation defers analysis but should never replace secure coding practices.
-
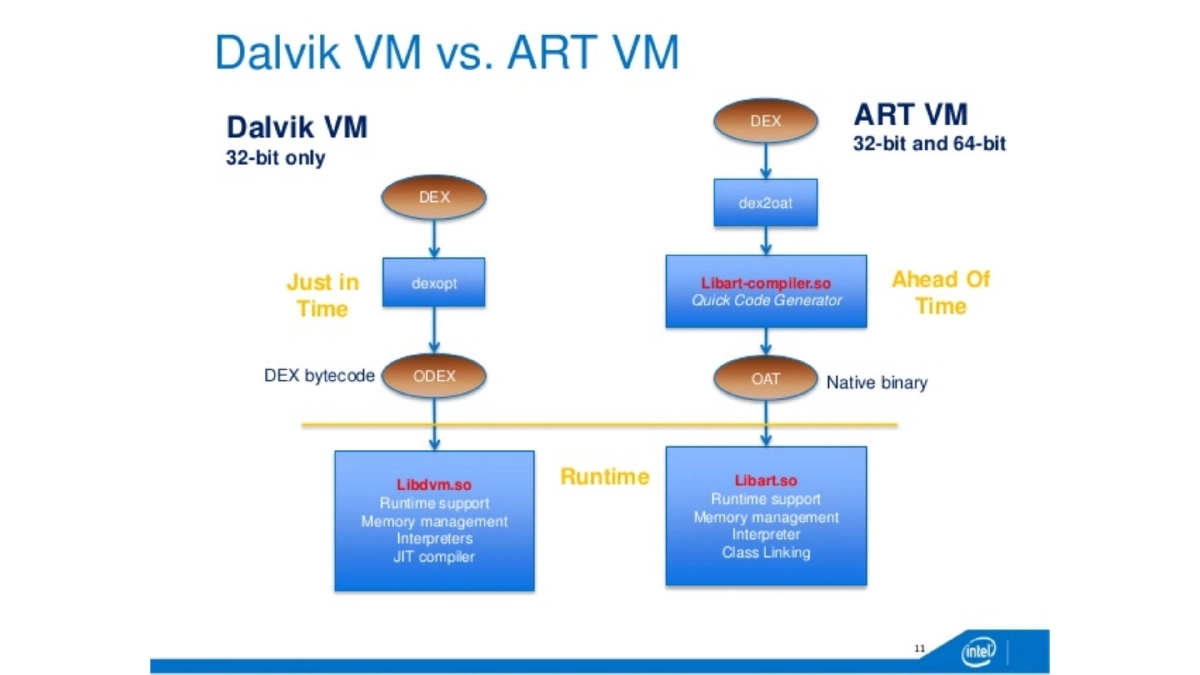
Dalvik and ART VM Internals: The Android runtime uses register-based bytecode. DEX files are device-independent code while ODEX/OAT files are device-optimized. Dalvik uses
dexoptfor optimization and stores files in dalvik-cache, while ART eliminates JIT compilation.Oat2dexconverter is used for decrypting Lollipop-era apps and JARs. System apps typically ship as ODEX/OAT files. -
Traffic Interception: Configuring proxy tools (Burp Suite, Charles, OWASP ZAP) by setting up the proxy in Android Tamer, configuring proxy settings in the device’s WiFi settings, and verifying interception for HTTP traffic.
-
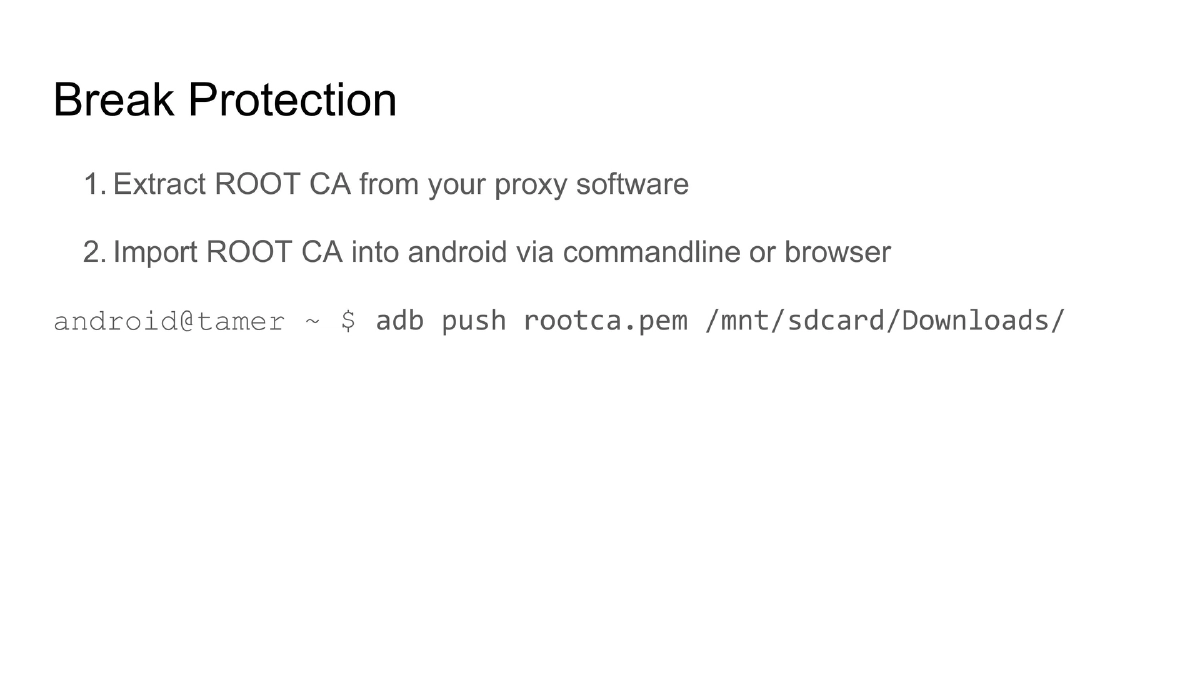
HTTPS Traffic Interception and PKI Weaknesses: The PKI system has inherent weaknesses — the system trusts all CAs in the trust store, any CA can issue certificates for any website (citing Diginotar, Trustwave, NIC incidents), and stolen certificates create “revocation hell.” Breaking HTTPS interception involves extracting the proxy’s root CA and importing it into the Android device via
adb pushor browser import. -
Certificate Pinning and Bypass: Certificate pinning validates certificates against hardcoded pins rather than the OS trust store. Implementation approaches include default platform code, frameworks, or custom code. Bypass methods: decompile the APK and modify the pinning code, or use the Xposed framework with the JustTrustMe module (root device, install Xposed, install and enable JustTrustMe, reboot).
-
Root Detection and Bypass: Applications detect root to protect data integrity and prevent tampering. Detection techniques are mainly blacklist-based: checking for binary presence (
/usr/bin/su), command availability (which), and superuser controller apps (superuser.apk). Bypass approaches: hide root binaries or overload system calls that check for them. -
HTML5 Hybrid Application Analysis: Cross-platform apps built with HTML/CSS/JS (using frameworks like PhoneGap, Titanium). Common issues include source code disclosure in
assets/www, DOM-based XSS, SSL misconfigurations, local storage data leakage, framework-specific vulnerabilities, and easy repackaging. -
Static Analysis Tools: Using Android Tamer’s built-in tools including Mobilizer and
droidscan.shfor identifying flaws without running the application. -
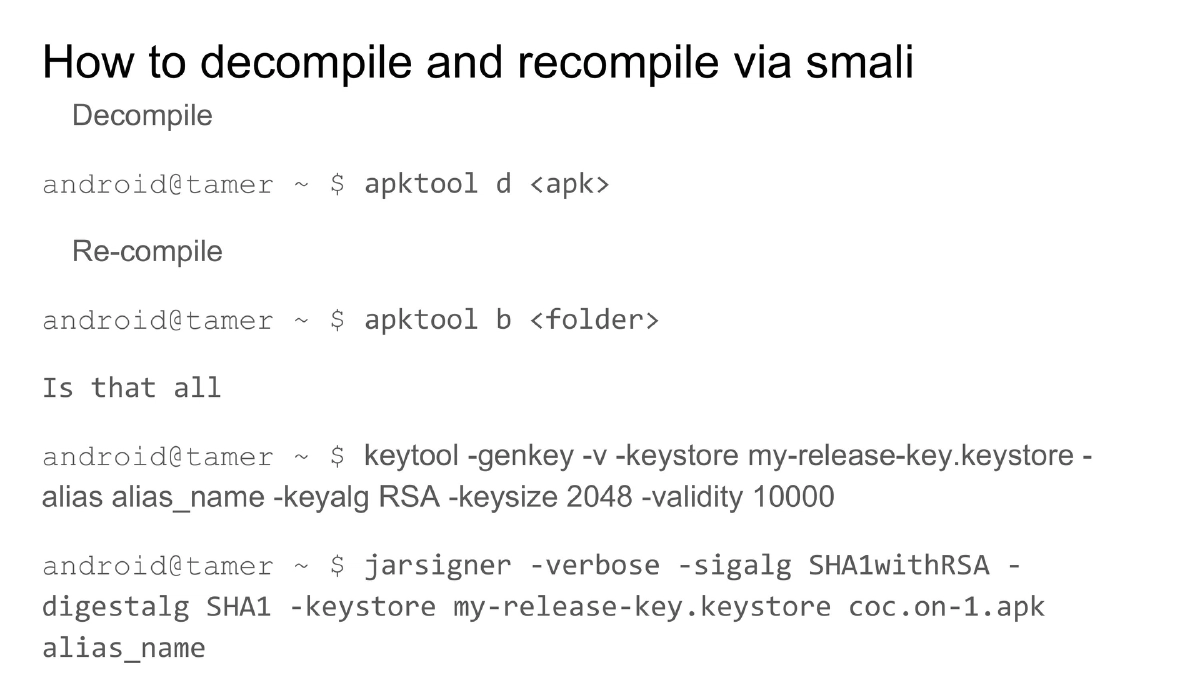
Decompile-Modify-Recompile Workflow: Using
apktool dto decompile, modifying Smali code, recompiling withapktool b, then signing withkeytool(generate keystore) andjarsigner(sign the APK).
-
-
Day 2: Dynamic Analysis, Instrumentation, and Fuzzing
-
Manual Dynamic Analysis: Runtime analysis using
adb,ddms/Android Monitor, andpidcatfor log monitoring. Key locations to inspect:/data/data/<app>/,/sdcard/, and/sdcard1/for data leakage. -
Automated Analysis Frameworks: MobSF (by Ajin), Marvin, Cuckoo-Droid, drozer, and Qark — tools for automated static and dynamic analysis of Android applications.
-
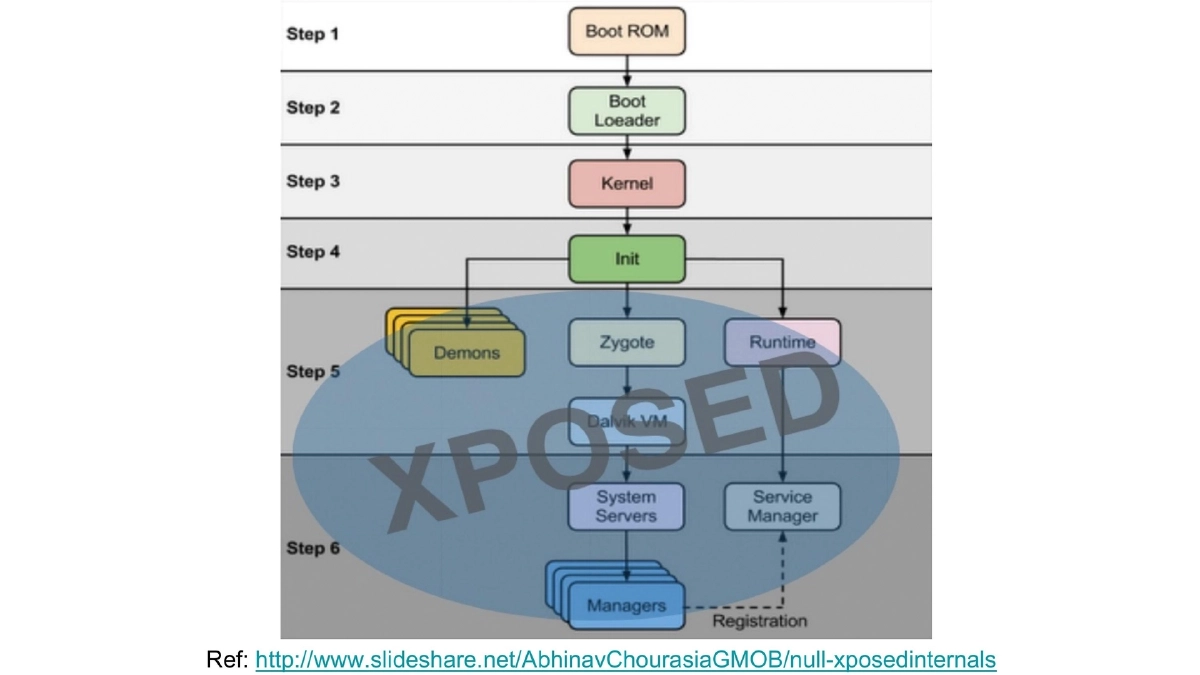
Xposed Framework — Hooking and Dynamic Instrumentation: Runtime behavior modification without recompilation. The training includes writing custom Xposed modules to hook into application methods at runtime.
-
Frida — Dynamic Code Instrumentation: A cross-platform instrumentation toolkit that injects JavaScript snippets into native apps on Windows, Mac, Linux, iOS, and Android, with Python and Node.js API bindings. Hands-on exercises using
frida-android-hooks(by Anto Joseph) covering: root detection bypass, debugger check bypass, WebView logging, device ID spoofing, certificate pinning bypass, and login screen brute-force. -
Fuzzing Android: Introduction to fuzzing concepts and their application to Android security — including intent fuzzing, C binary fuzzing, and finding vulnerabilities in Android’s core (referencing how to find the “next Stagefright”). The lab covers setting up a fuzzing environment, generating datasets, running datasets against targets, writing glue scripts, and writing log collection scripts using DroidFuzzer.
-
-
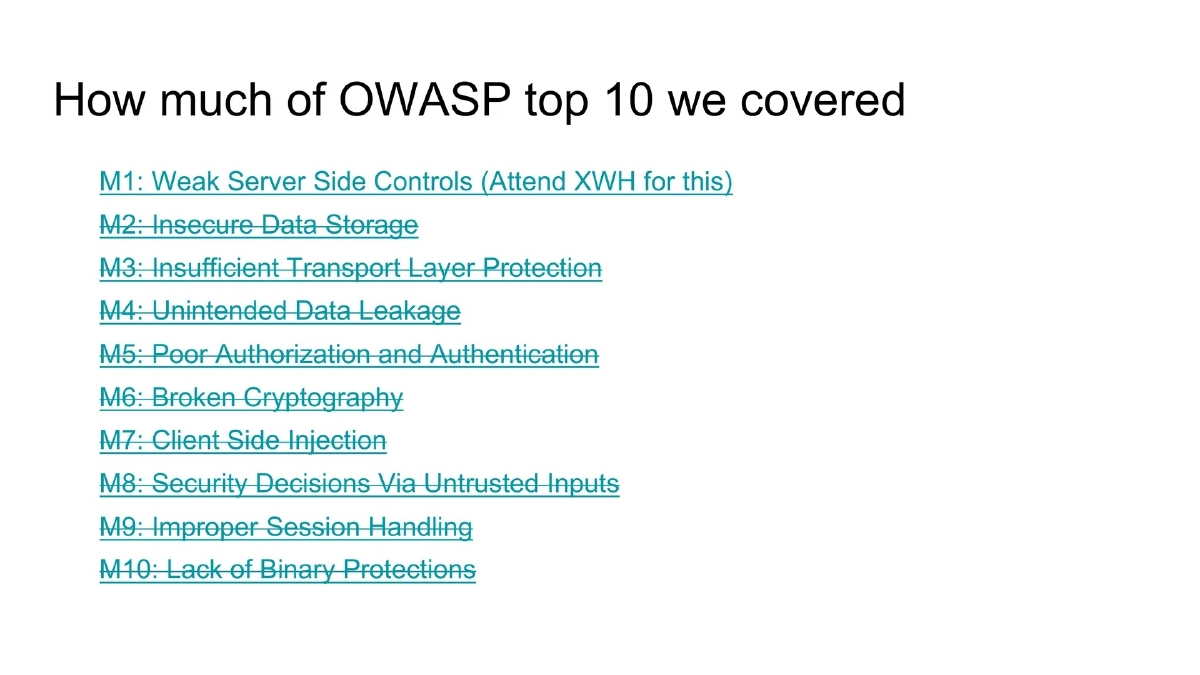
OWASP Mobile Top 10 Coverage: The training maps its exercises against the OWASP Mobile Top 10 (2014 edition), covering M2 (Insecure Data Storage), M3 (Insufficient Transport Layer Protection), M4 (Unintended Data Leakage), M5 (Poor Authorization and Authentication), M6 (Broken Cryptography), M7 (Client Side Injection), M8 (Security Decisions Via Untrusted Inputs), M9 (Improper Session Handling), and M10 (Lack of Binary Protections). M1 (Weak Server Side Controls) is noted as covered in a separate Xtreme Web Hacking course.
Actionable Takeaways
- Set up Android Tamer with Genymotion as a standardized Android security testing lab — use
apk2javafor rapid decompilation and always cross-reference output from multiple decompilers (jad and jadx) for accuracy. - For traffic interception, follow the escalation path: configure proxy for HTTP first, import proxy root CA for HTTPS, then use Xposed with JustTrustMe or Frida scripts for certificate pinning bypass — this systematic approach covers progressively hardened applications.
- Learn Frida as your primary dynamic instrumentation tool — its JavaScript injection capability and Python/Node.js bindings make it the most versatile tool for runtime behavior modification, covering root detection bypass, certificate pinning bypass, and custom hooking scenarios.
- When facing obfuscated code, use the Simplify de-obfuscation tool first, then fall back to Smali-level analysis if Java decompilation fails — remember that obfuscation defers but doesn’t prevent analysis.
- Include fuzzing in your Android assessment methodology — use DroidFuzzer for intent fuzzing and C binary fuzzing to discover vulnerabilities beyond what static and dynamic analysis tools typically find, especially in Android’s media processing and core framework components.
- Always check
/data/data/<app>/,/sdcard/, and/sdcard1/during dynamic analysis for insecure data storage — many applications leak sensitive data to these locations. - Master the decompile-modify-recompile workflow (
apktool d→ edit Smali →apktool b→keytool→jarsigner) as it is essential for bypassing client-side controls and modifying application behavior during assessments.