Reducing Attack Surface Security Days Japan
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation at Security Days Tokyo argues that reducing the attack surface is no longer optional in an era where AI amplifies both offensive and defensive capabilities, supply chains are opaque, and cloud/CI-CD systems control everything. Anant Shrivastava introduces the Attack Surface Reduction (ASR) Manifesto — a philosophy-first approach that advocates for building systems that are simpler, smaller, and inherently less attackable through subtraction rather than accumulation. The talk covers reduction strategies across four domains: software, identity and access management, infrastructure, and data.
Key Topics Covered
The Evolving Developer Workflow and AI’s Impact:
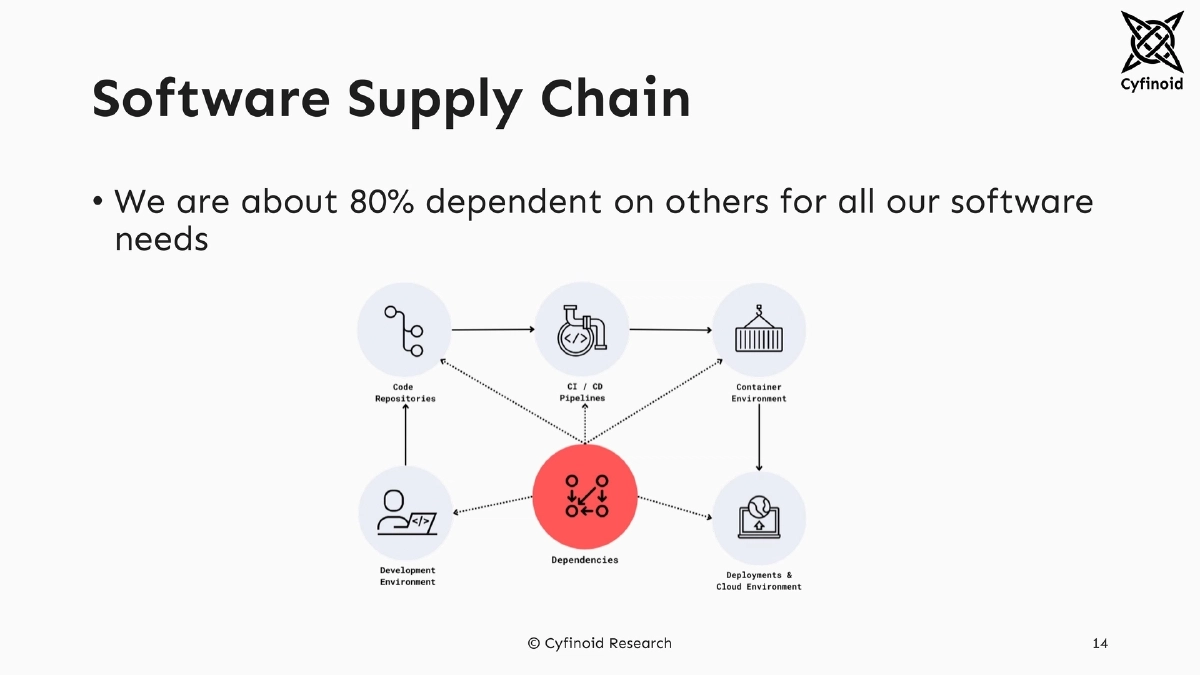
- The modern developer workflow involves Chrome extensions, AI-driven code completion in VS Code, GitHub Actions for CI/CD, Docker containers on Kubernetes/EC2 — each link a potential supply chain attack vector
- AI agents are now writing code autonomously with full command-line access, fundamentally changing the trust model
- Shadow IT risk: non-technical staff (BizDev, HR, Finance) are using AI IDEs like Cursor/Windsurf to build and deploy applications on personal Vercel/Railway accounts, creating unmonitored attack surfaces
AI as a Force Multiplier:
- “If you’re a +1 programmer, AI can make you a +10. But if you’re at -1, you’re just amplifying bad decisions at scale.”
- AI accelerates development speed but reduces testing time allocation, creating a cycle of more features, more bugs, more AI-assisted fixes, and repeat
- AI code tools hallucinate package names, potentially introducing non-existent or malicious dependencies
- Defensively, AI shows promise — DARPA’s AIxCC competition demonstrated AI capabilities in finding and fixing vulnerabilities
Why Current Approaches Fail:
- The industry’s default response is reactive: patch after compromise, add another scanner, deploy more layers, buy another dashboard, monitor more alerts
- This accumulation-based approach increases complexity rather than reducing risk
- Misconfigurations at abstraction layers bypass traditional defenses entirely
The Attack Surface Reduction Manifesto:
- Core philosophy: “Build less. Expose less. Trust less.”
- Rather than chasing visibility across growing complexity, build systems that are simpler, smaller, and inherently less attackable
- Available at reducetheattacksurface.com
Software Reduction:
- Minimize features, APIs, and endpoints
- Prioritize internal reuse over external dependence
- Shrink build and toolchain footprint
- Limit codebase blast radius through modular architecture
- Harden through simplicity
IAM (Identity and Access Management) Reduction:
- Apply the principle of least privilege rigorously
- Enforce human account hygiene and service identity discipline
- Discover and eliminate shadow access
- Control role explosion and federated identity risks
- Manage secret lifecycles and reduce SaaS/vendor identity exposure
Infrastructure Reduction:
- Expose nothing by default
- Reduce control plane and runtime complexity
- Enforce minimalism at the image and execution level
- Prune zombie infrastructure and orphaned services
- Reduce lateral movement paths
- Implement runtime cleanup and reboot culture
- Enforce infrastructure-as-code and deployment discipline
Data Reduction:
- Collect less data by default
- Reduce data retention periods
- Limit data propagation and transformation chains
- Avoid over-engineering analytics
Convincing Management:
- Quantify outcomes in monetary terms
- Reduced assets directly lower costs for ongoing operations, security compliance, electricity, data traffic, per-device licensing, and storage
Actionable Takeaways
- Adopt the ASR Manifesto mindset — prioritize subtraction over accumulation by systematically removing unnecessary features, endpoints, accounts, infrastructure, and data.
- Audit your organization’s AI-driven development practices: inventory which AI tools are in use, what access they have, and whether non-technical staff are independently deploying AI-built applications.
- Apply reduction strategies across all four domains (software, IAM, infrastructure, data) rather than focusing solely on code-level security.
- Quantify the cost savings of attack surface reduction to build management buy-in — reduced assets mean reduced operational, compliance, licensing, and storage costs.
- Explore your environment to identify unused or unnecessary assets, then systematically reduce the attack surface starting with the highest-risk, lowest-value components.
- Visit reducetheattacksurface.com to review the full manifesto and begin implementing its principles in your security strategy.