Sbomplay Arsenal BH EU
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
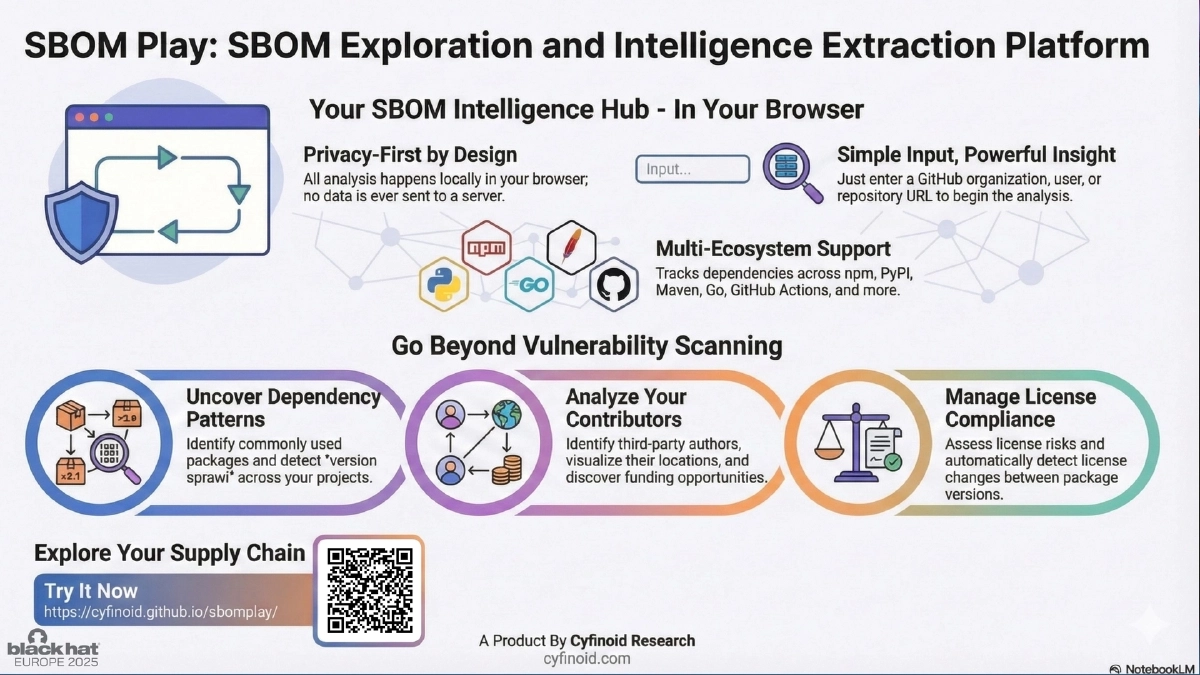
This Black Hat Europe 2025 Arsenal presentation introduces SBoM Play, an open-source, fully client-side SBoM exploration and intelligence extraction platform. Anant Shrivastava demonstrates how the tool transforms raw Software Bill of Materials data into actionable visual dashboards — covering dependency analysis, vulnerability tracking, license compliance, author attribution, geographical mapping, and version sprawl detection — all running entirely in the browser with no backend required.
Key Topics Covered
Tool Philosophy and Design:
- SBoM is fundamentally an inventory — SBoM Play focuses on extracting intelligence from that inventory
- Designed to demonstrate SBoM value in non-infosec scenarios, proving that “showing is better than talking”
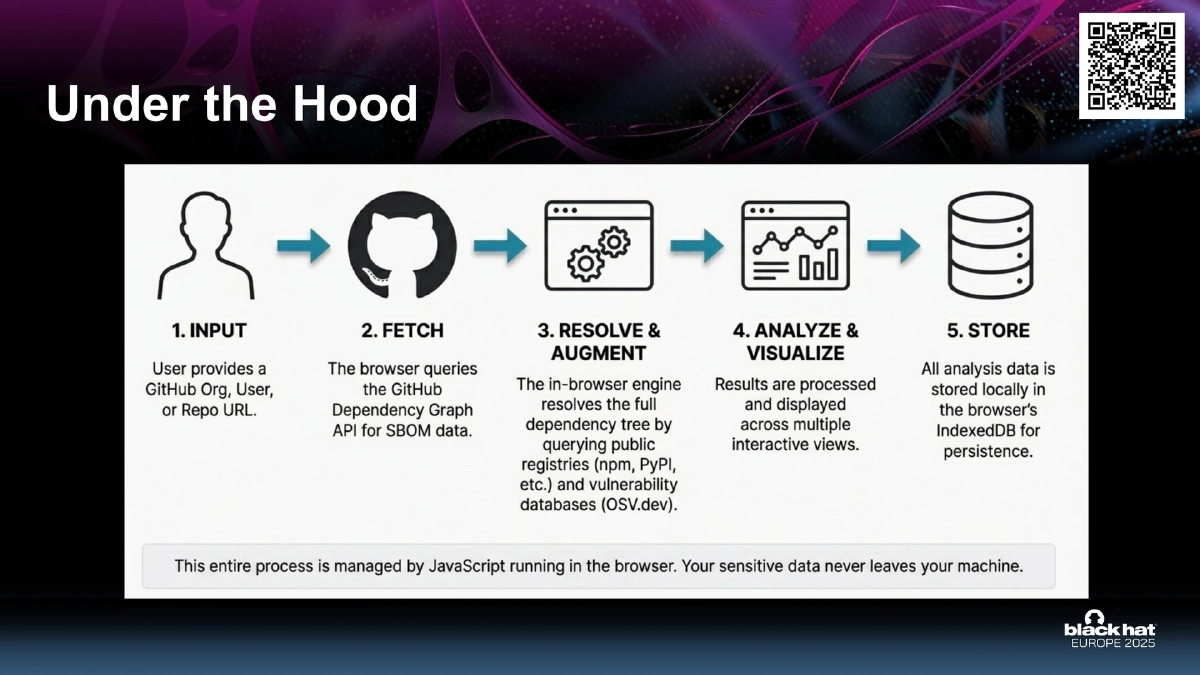
- Fully client-side architecture: runs entirely in the browser with no server or backend, ensuring privacy and zero data leakage
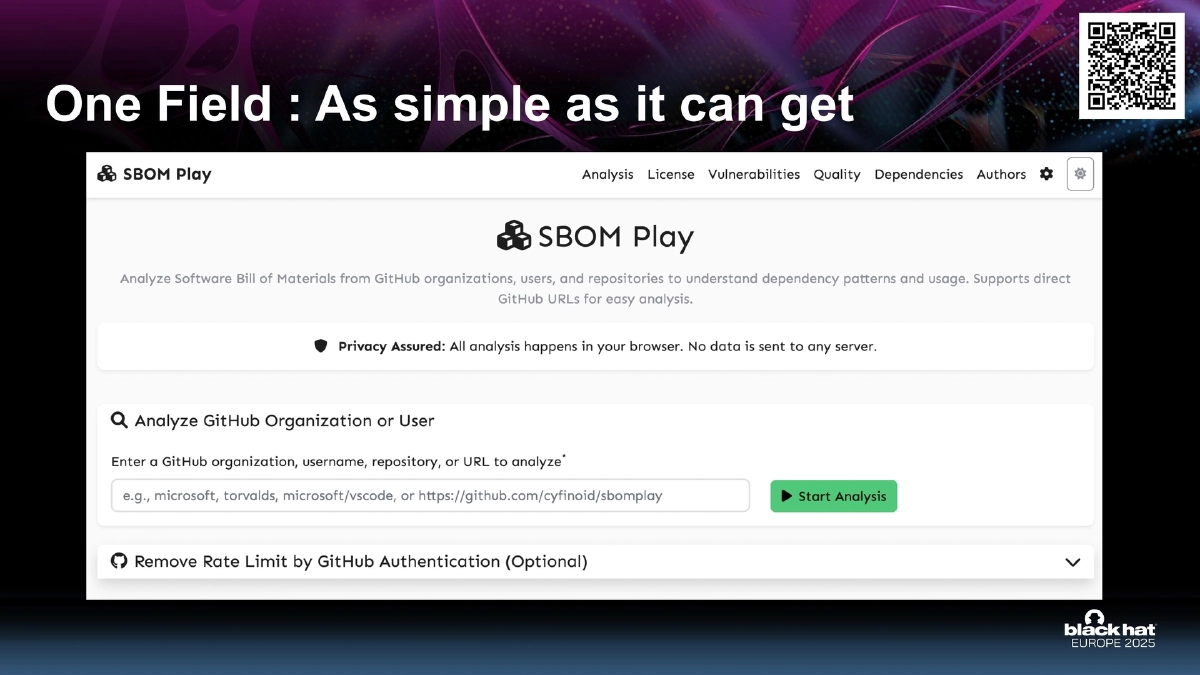
Simple Input Model:
- Accepts a GitHub organization, user, or repository as input
- Supports shortform notation (user/repo, org/repo, username, org) or full GitHub URLs
- Only requires GitHub’s Dependency Graph to be enabled on target repositories
Core Architecture:
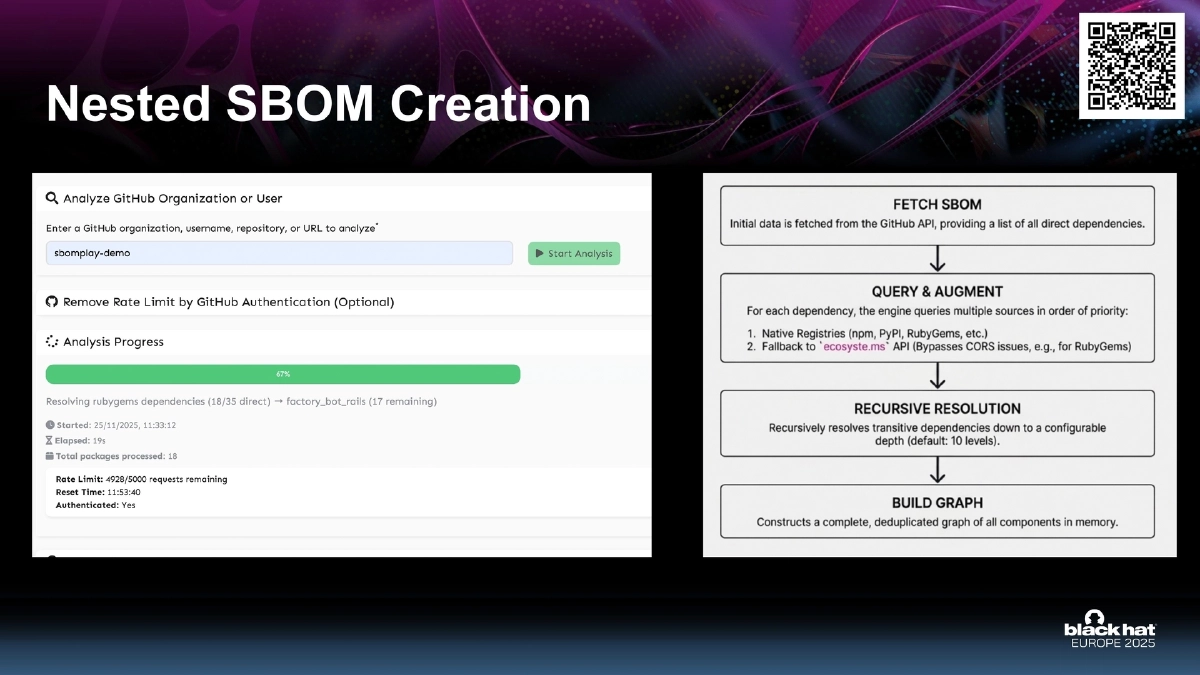
- Fetches SBoM data via GitHub’s dependency graph API
- Performs nested SBoM creation by recursively resolving transitive dependencies
- Processes and visualizes data entirely on the client side
Dashboard and Visualization Features:
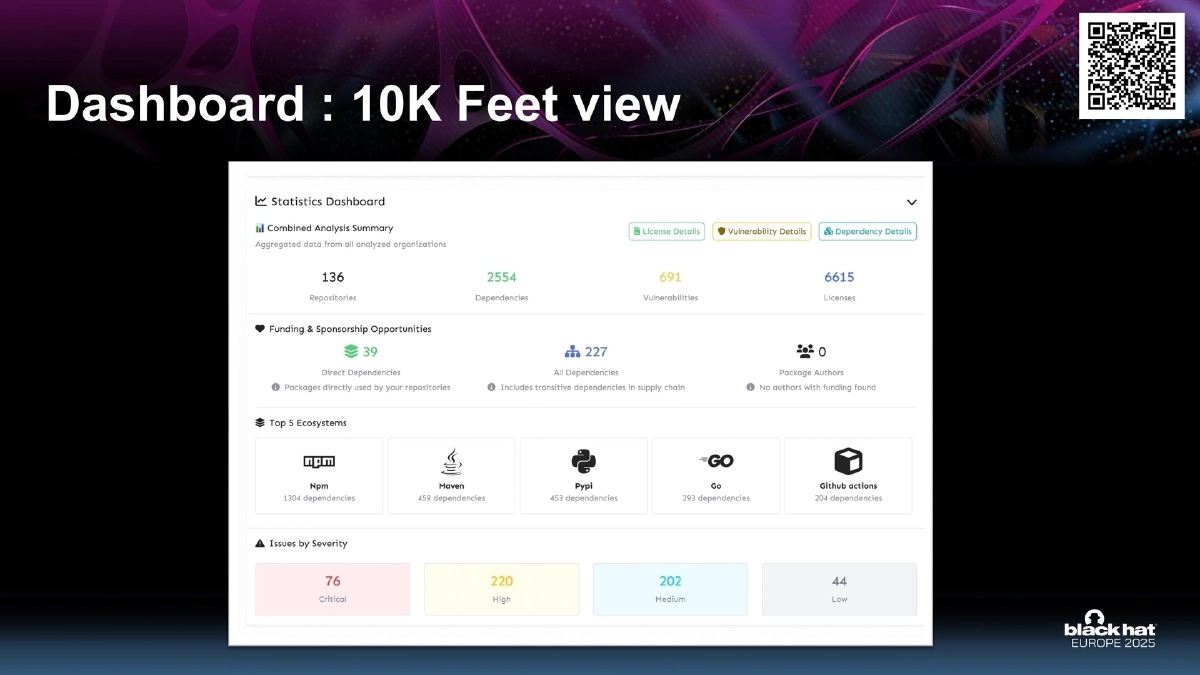
- 10K-foot dashboard view providing a high-level summary of the entire organization’s dependency landscape
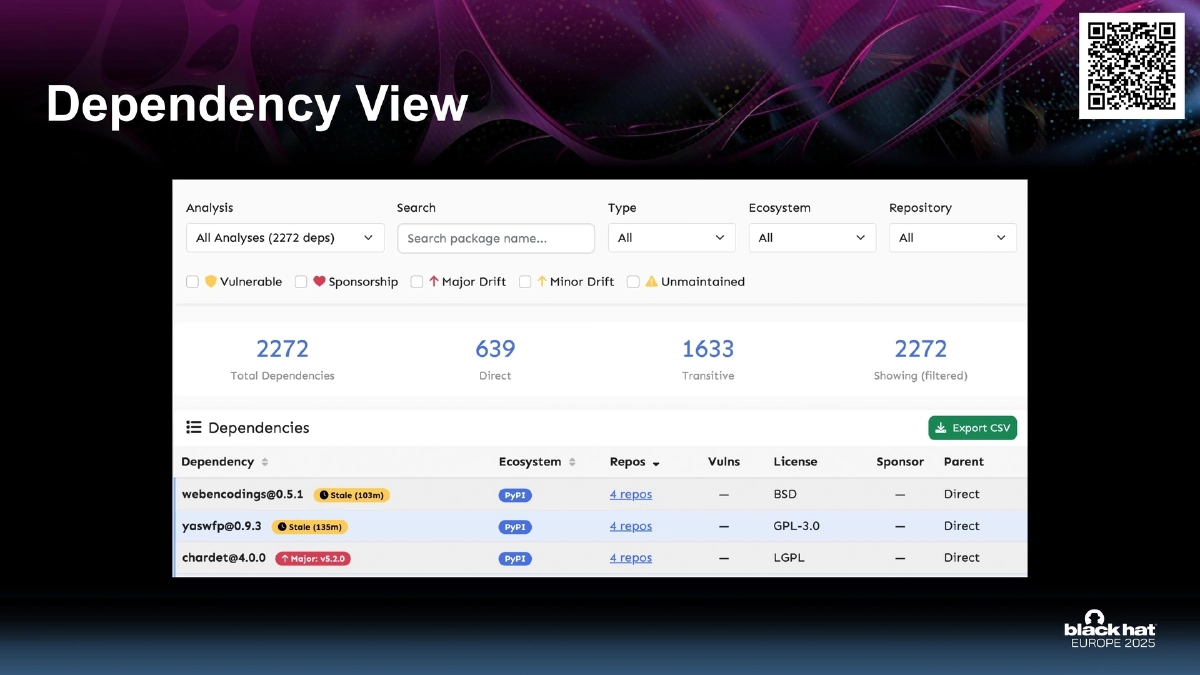
- Dependency view: detailed breakdown of all direct and transitive dependencies across repositories
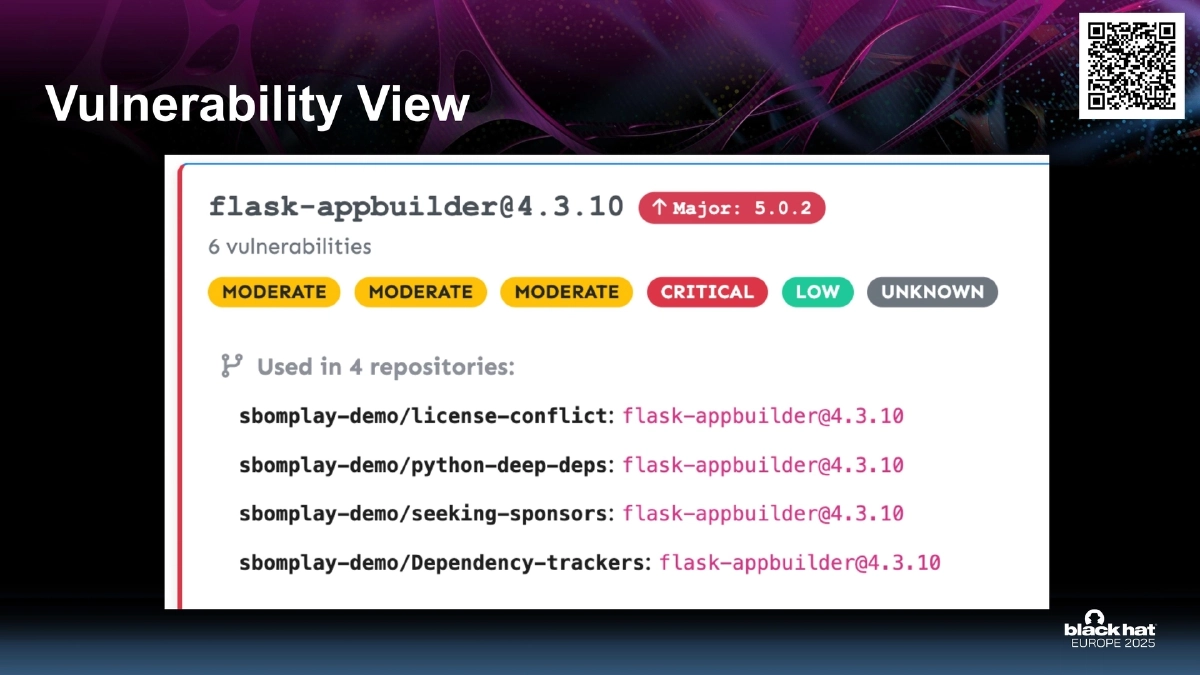
- Vulnerability view: aggregated vulnerability data mapped to specific dependencies and repositories
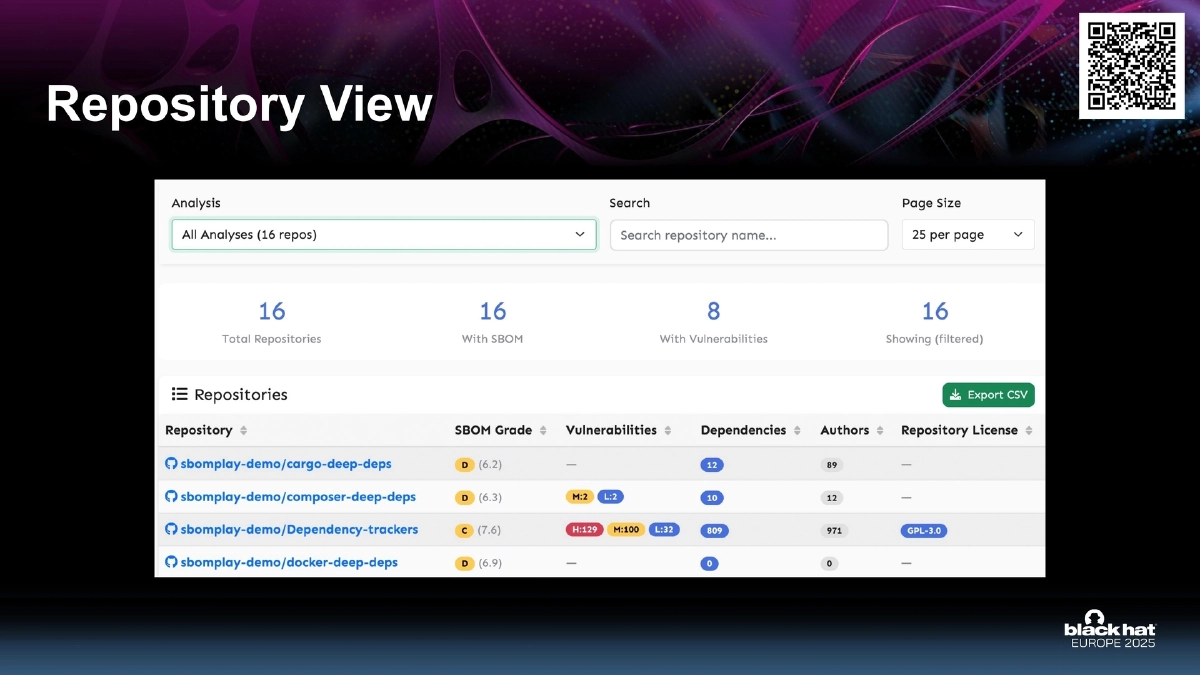
- Repository view: per-repository analysis of dependencies, risks, and compliance status
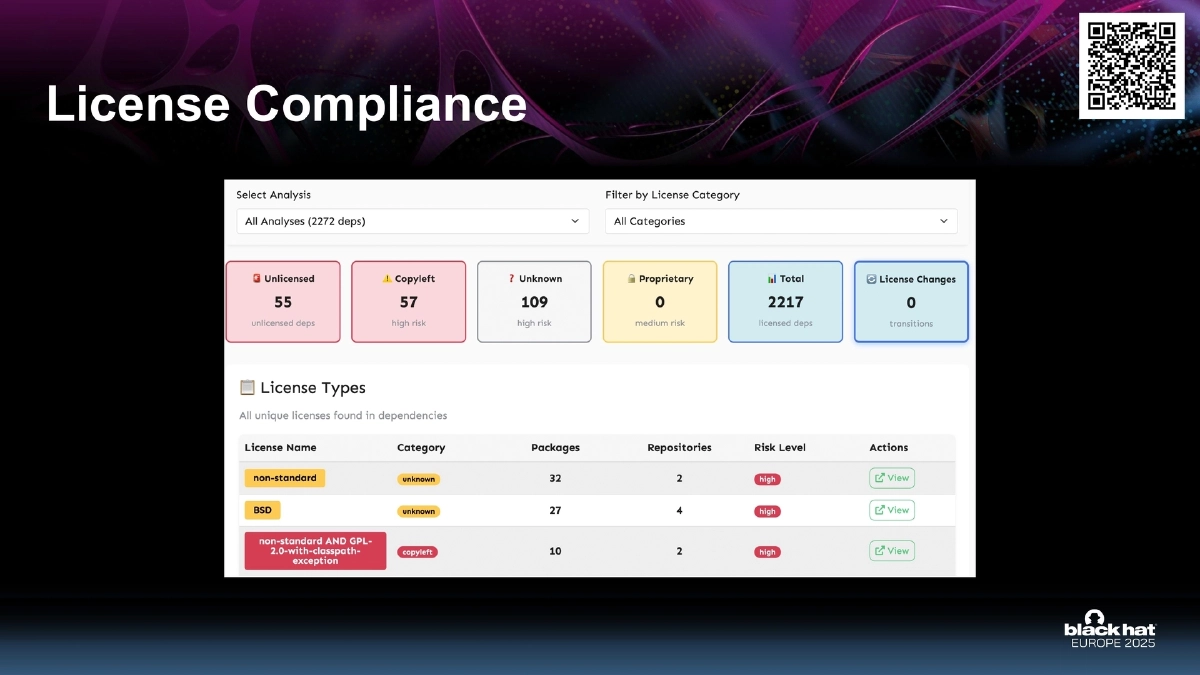
- License compliance view: identification of license types across the dependency tree with policy violation detection
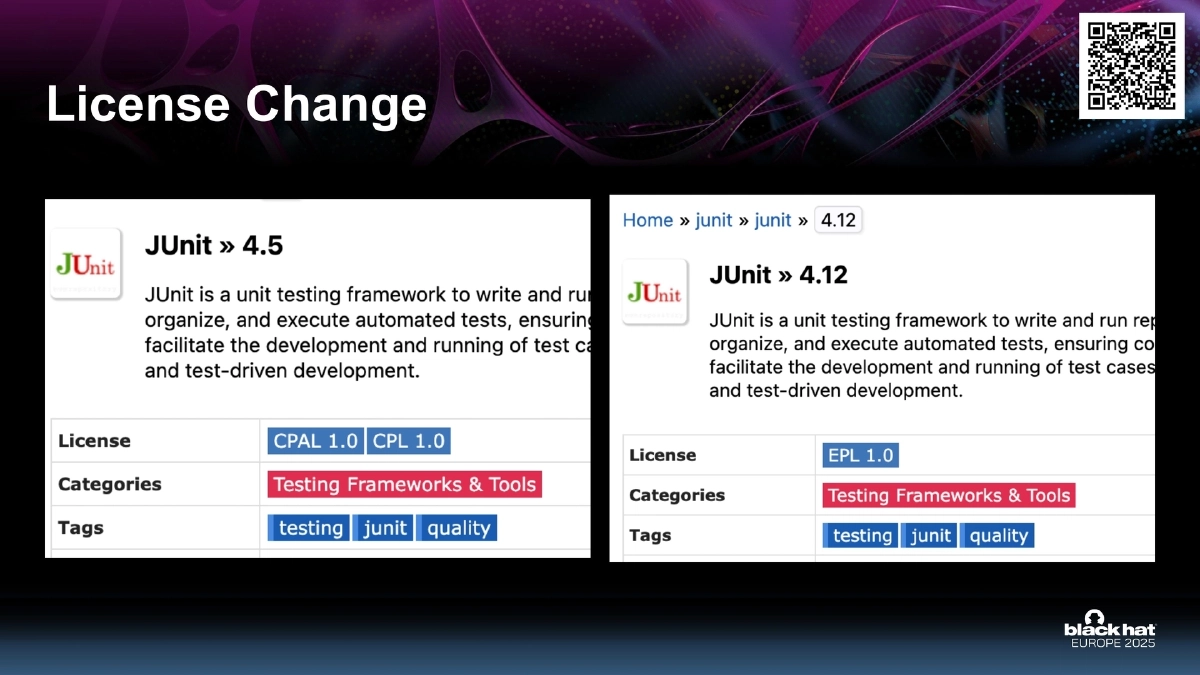
- License change tracking: monitoring for license changes in dependencies between versions
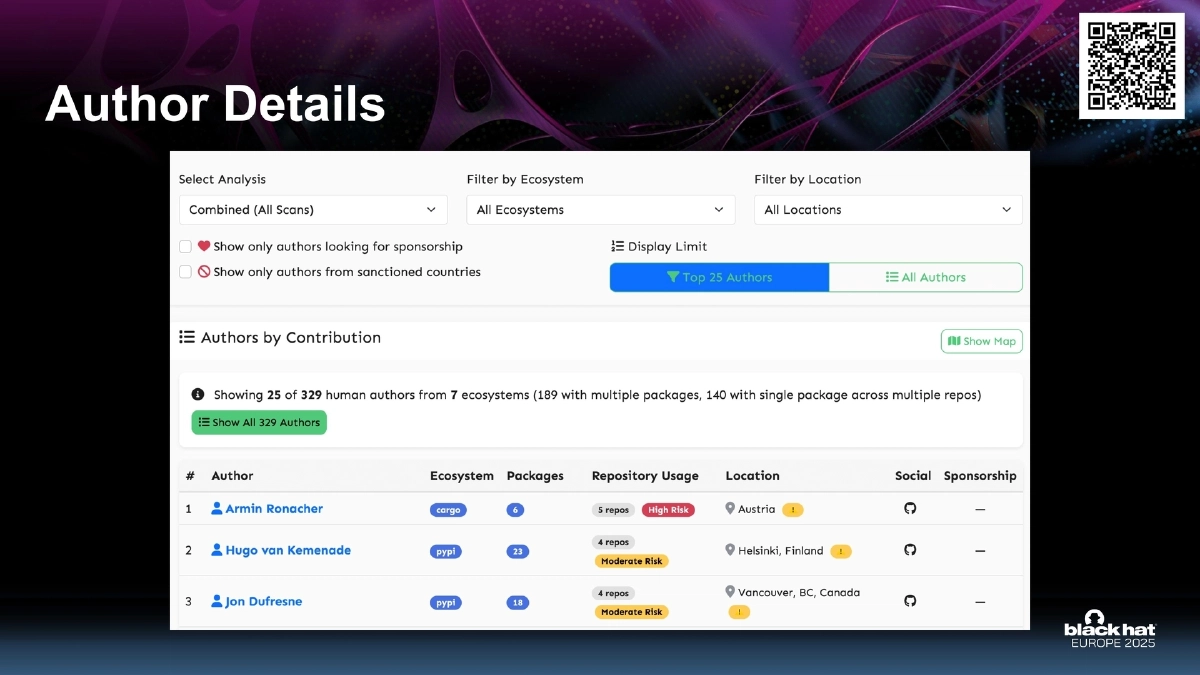
- Author details: attribution data showing who maintains the dependencies being consumed
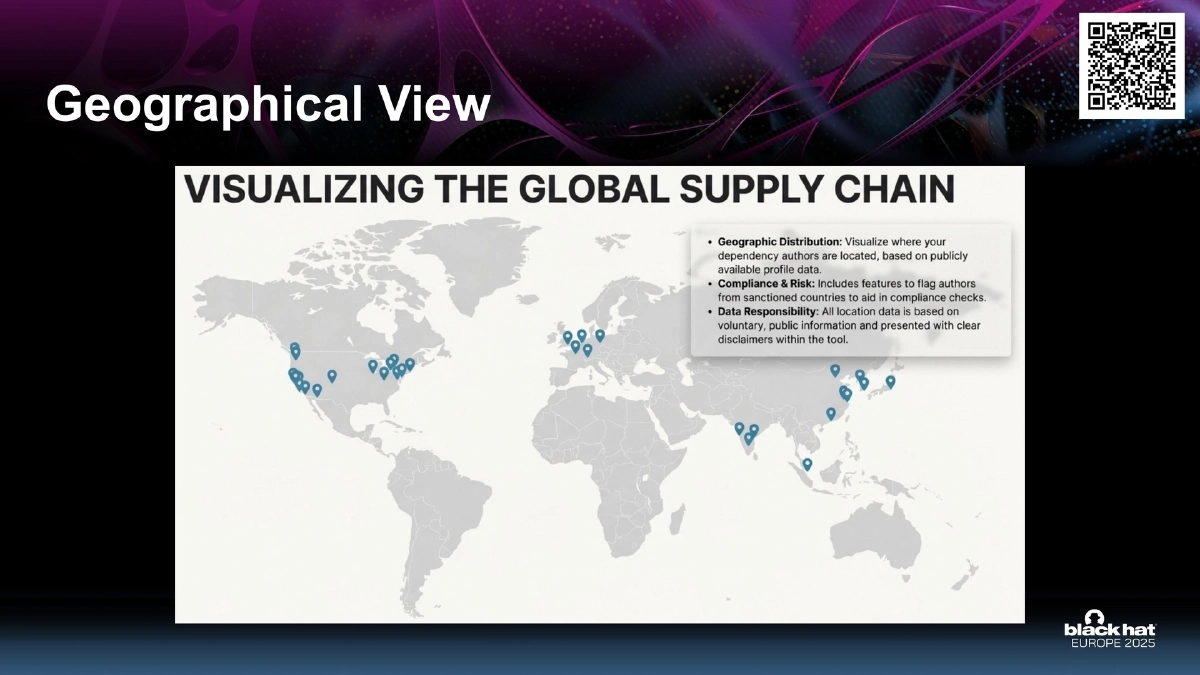
- Geographical view: mapping dependency maintainers and origins by geographic location
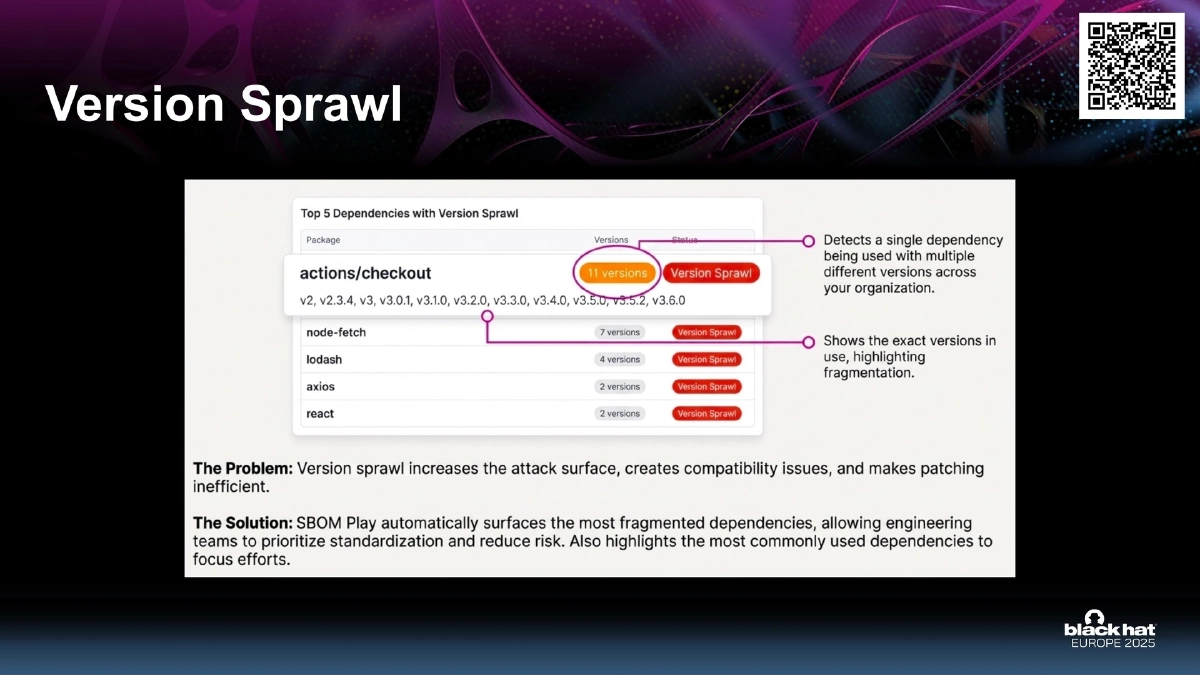
- Version sprawl detection: identifying cases where multiple versions of the same package are used across an organization
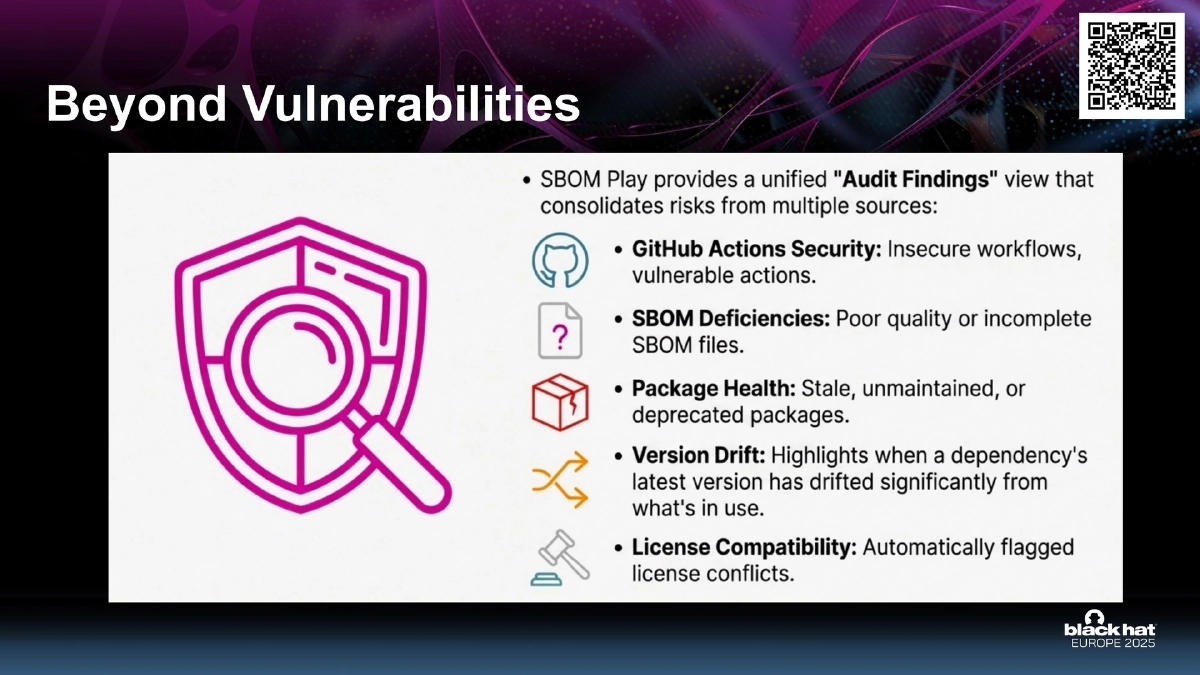
Beyond Vulnerabilities:
- SBoM Play goes beyond traditional vulnerability scanning to surface broader supply chain intelligence
- License compliance, maintainer trust, geographic risk, and version consolidation opportunities are all surfaced as actionable insights
Actionable Takeaways
- Try SBoM Play at cyfinoid.github.io/sbomplay to explore your GitHub organization’s dependency landscape without any data leaving your browser.
- Use the version sprawl view to identify consolidation opportunities where multiple versions of the same dependency exist across your repositories.
- Leverage the license compliance view to proactively detect license policy violations before they become legal liabilities.
- Monitor license changes between dependency versions to catch unexpected license shifts (e.g., from permissive to copyleft) early.
- Use the geographical and author views to assess concentration risk — understanding who maintains your critical dependencies and where they are located.