Cocon Security Issues In Android Custom Roms
AI Generated Summary
AI Generated Content Disclaimer
Note: This summary is AI-generated and may contain inaccuracies, errors, or omissions. If you spot any issues, please contact the site owner for corrections. Errors or omissions are unintended.
This presentation examines the security risks inherent in Android custom ROMs, covering common misconfigurations found in aftermarket firmware and demonstrating a proof-of-concept data theft tool.
Key Topics Covered
Custom ROM Ecosystem:
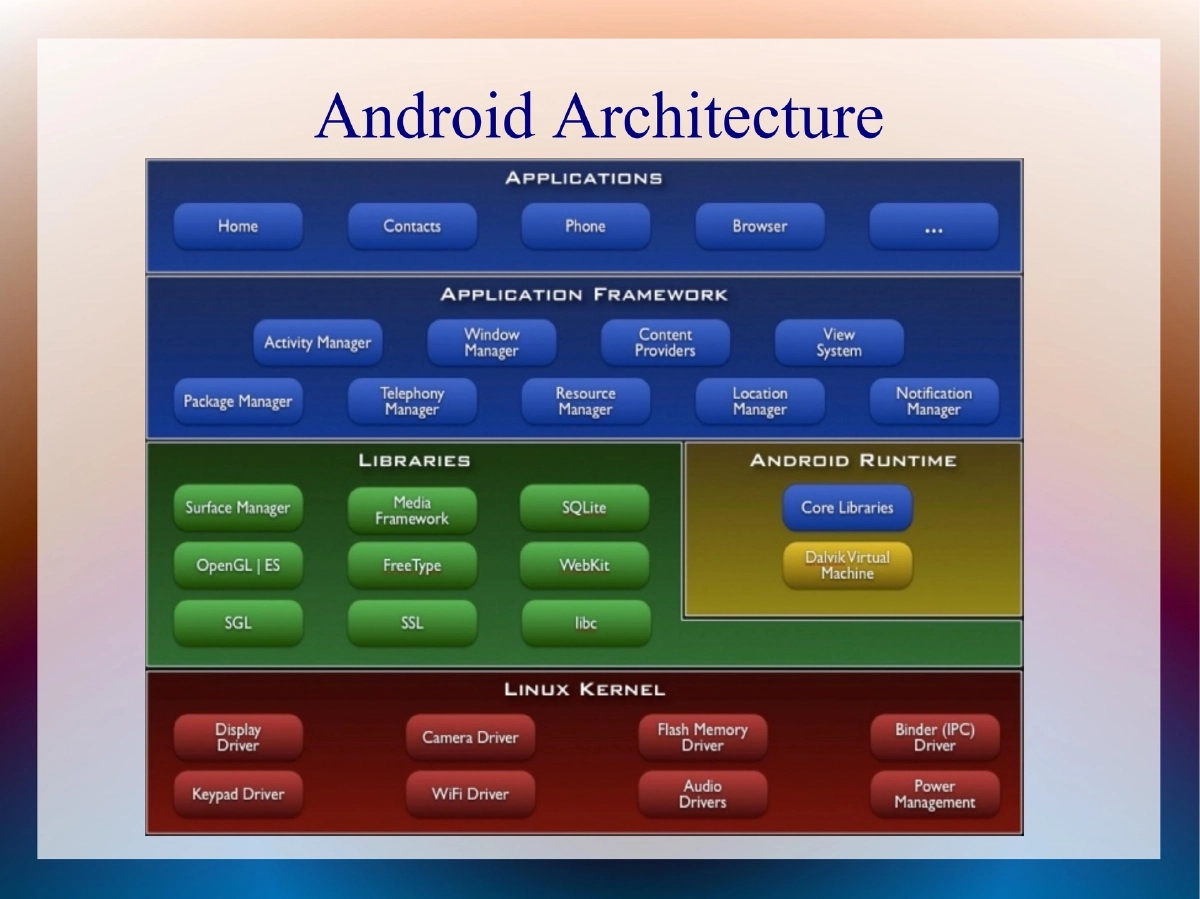
- Android ROM is the OS firmware layer consisting of kernel, Dalvik, libraries, framework, and vendor applications
- Stock ROMs are pre-installed by manufacturers; custom ROMs are aftermarket versions not officially supported
- Popular custom ROMs include CyanogenMod, MIUI (Chinese origin, mimics iPhone), and OMFGB
- Sources include cyanogenmod.com, miui.org, XDA Developers, and various underground forums
- ROM cookers create custom versions for fun, profit, or the “they can” attitude
Why Security Review is Needed:
- Android malware and exploits are increasing rapidly
- Employees pressure organizations to integrate Android into corporate infrastructure
- CyanogenMod is considered a viable corporate alternative, but security has not been thoroughly evaluated
- Custom ROMs may contain undisclosed modifications
Security Issues Identified:
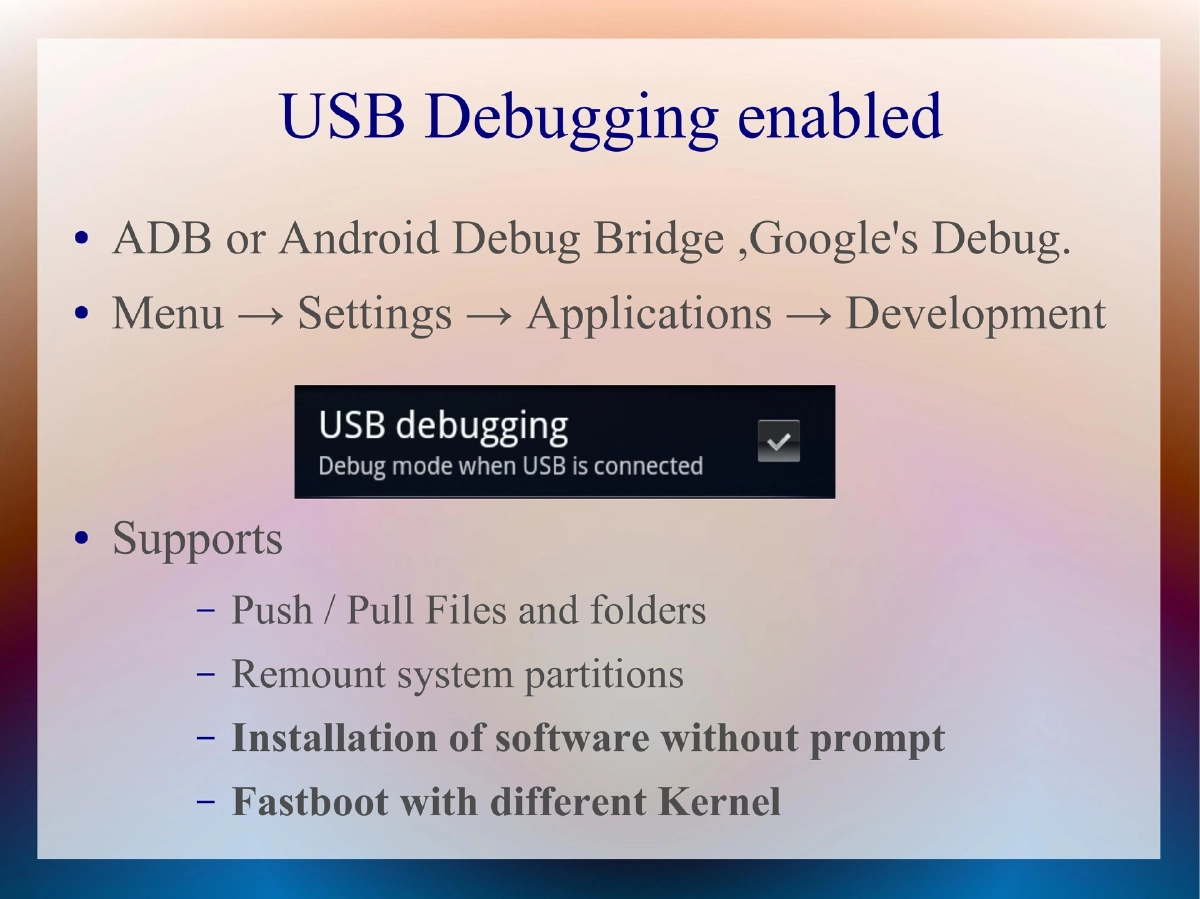
- USB Debugging Enabled: ADB allows file push/pull, system partition remount, silent software installation, and fastboot with different kernels
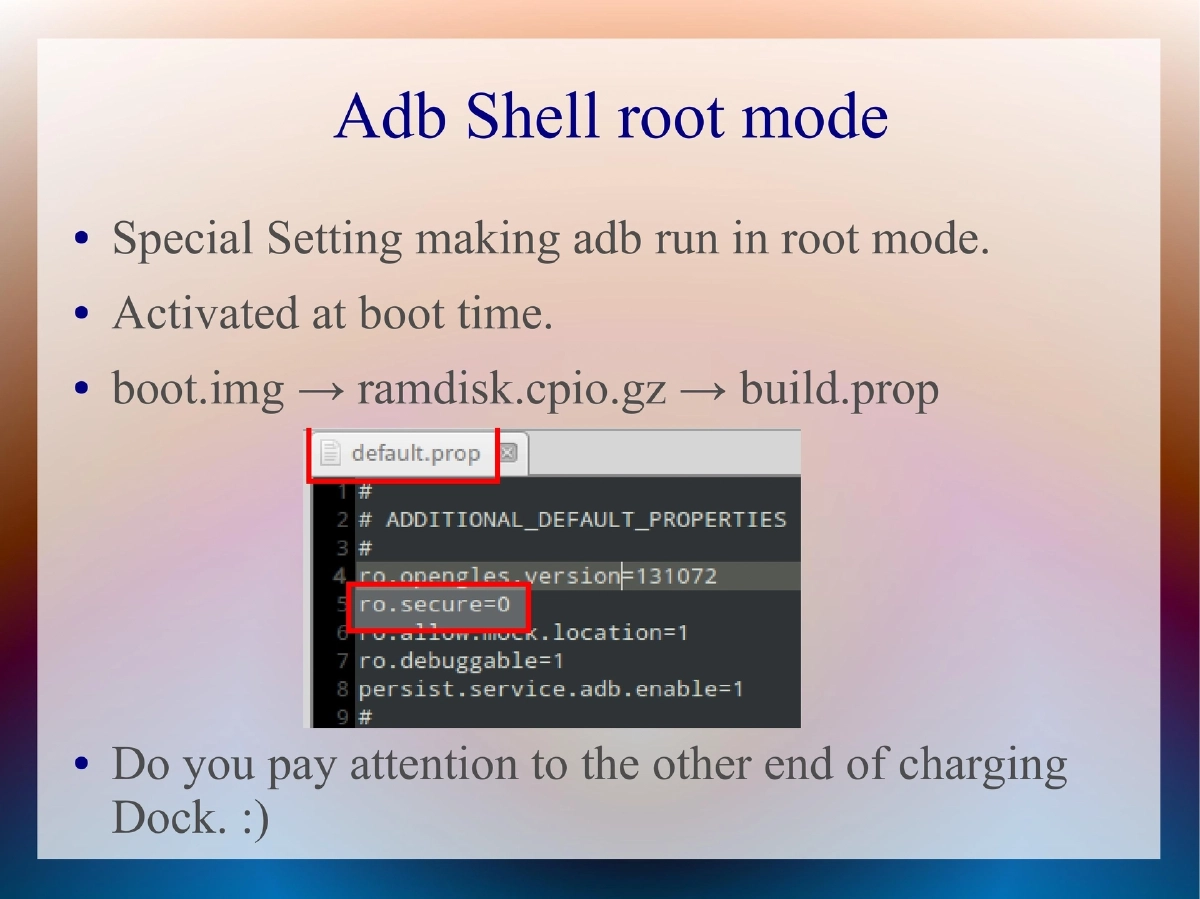
- ADB Shell Root Mode: Special setting making ADB run as root, activated at boot time via build.prop in boot image ramdisk
- ADB Shell over WiFi: Allows ADB access over wireless network, combining with root mode effectively hands over the device
- System Permissions: /system should be read-only, but many ROM cookers set 777 permissions, opening doors for rootkits, trojans, and malware
- Unknown Source Installation: Custom ROM forums encourage enabling unknown sources, bypassing Android Market restrictions
- SU Access: Switch user binary indicates rooted device; default protection from unauthorized execution is limited to Superuser.apk
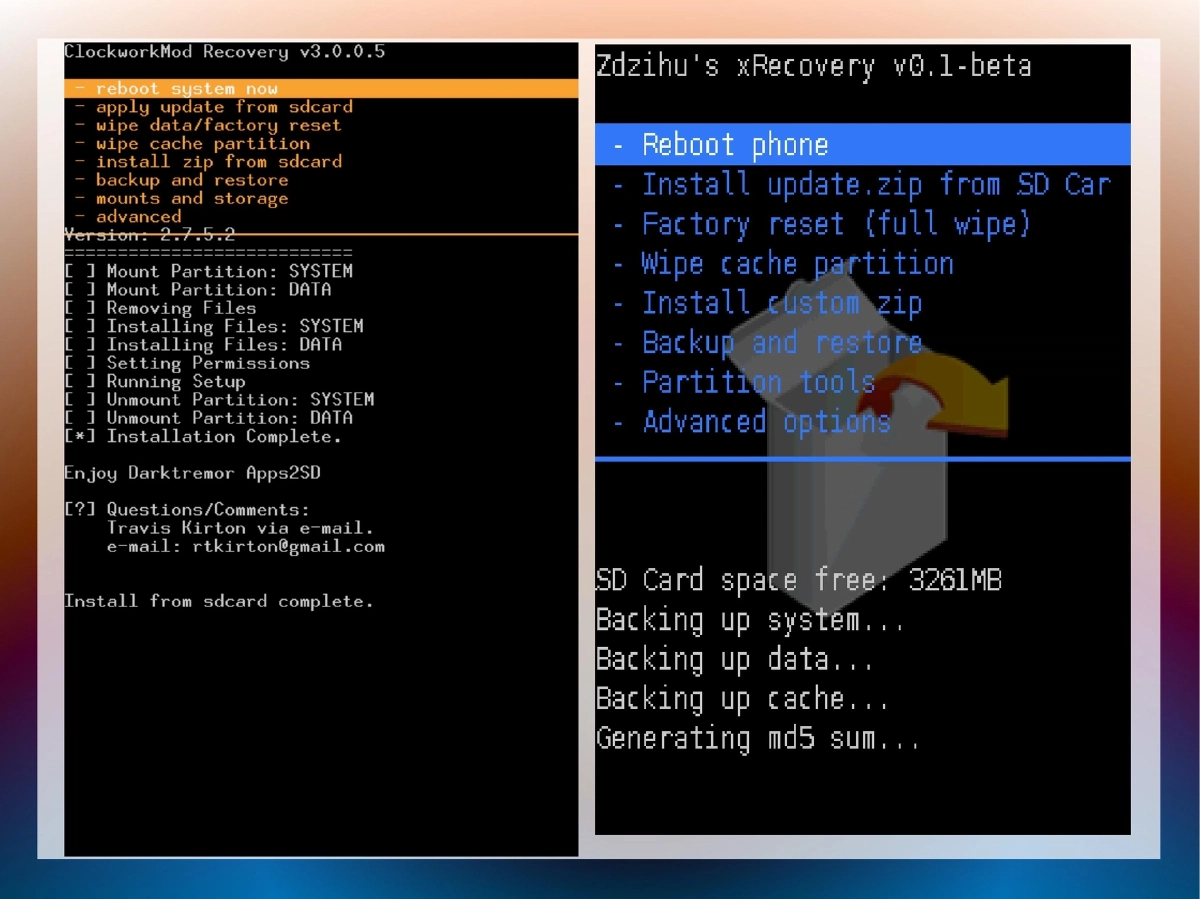
- Custom Recovery Images: Provide unrestricted root access by default; entering recovery mode is trivially easy
Proof-of-Concept Tool:
- Demonstrated a data theft tool targeting these vulnerabilities
- Intentionally not developed to full extent to avoid script kiddie misuse
Protection Recommendations:
- Developers: Avoid unnecessary settings for normal users, recommend closing unknown source settings
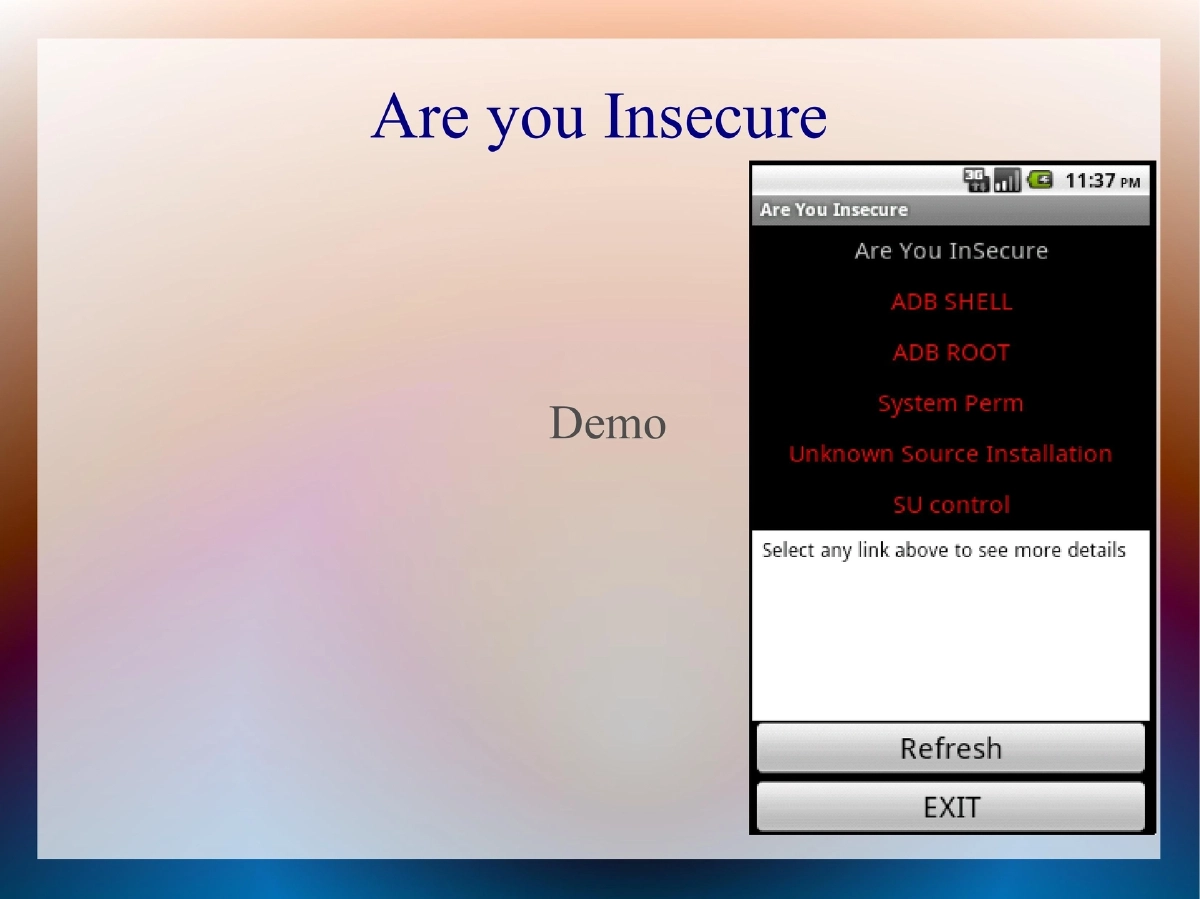
- Users: Examine development processes, ask questions, run security audit tools (“Are You Insecure” tool demonstrated)
Actionable Takeaways
- Custom ROMs introduce multiple security risks through misconfigurations
- Root mode via ADB combined with WiFi access creates critical attack surface
- Permissive file system permissions on /system enable persistent malware
- Organizations should perform security audits before approving custom ROMs for corporate use
- Users should verify ROM security settings before installation